1. 本地主机访问公有云vpc内网(单向访问)
1.1 关键说明
腾讯云提供基于 IPSec 和 SSL 两种协议类型的 V P N 组网方案,其中 IPSec 协议需配置对端网关 IP,而 SSL 协议无需涉及对端网关。
IPSec V P N:用于实现本地数据中心与公有云 VPC 私网互通,要求本地侧与 VPC 侧均具备公网地址,需在两侧分别配置网关,实现双向互通。(V P N网关+对端网关)
SSL V P N:用于实现本地终端访问公有云 VPC 私网,仅需 VPC 侧配置公网网关,本地侧只需具备公网访问能力即可,无需配置公网网关,支持本地到公有云 VPC 私网的单向访问(本文所述方案)。
1.2 关键步骤
一、公有云侧:创建 SSL V P N 网关 → 创建 SSL 服务端 → 生成 SSL 客户端 → 新增路由策略
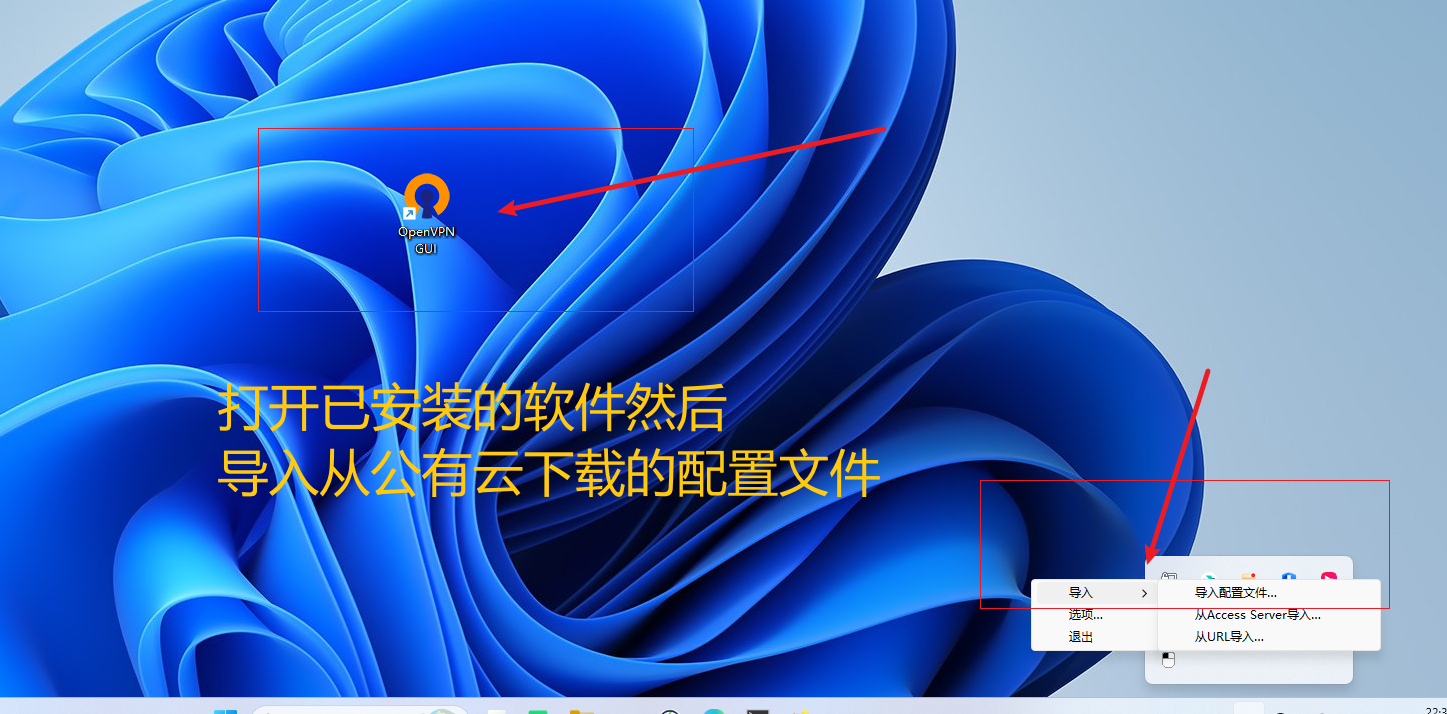
二、本地侧:安装 OpenV P N 客户端,客户端配置文件从公有云 SSL 客户端处下载获取。
2. 公有云侧操作步骤
2.1 创建 SSL V P N 网关(规格按实际需求写)



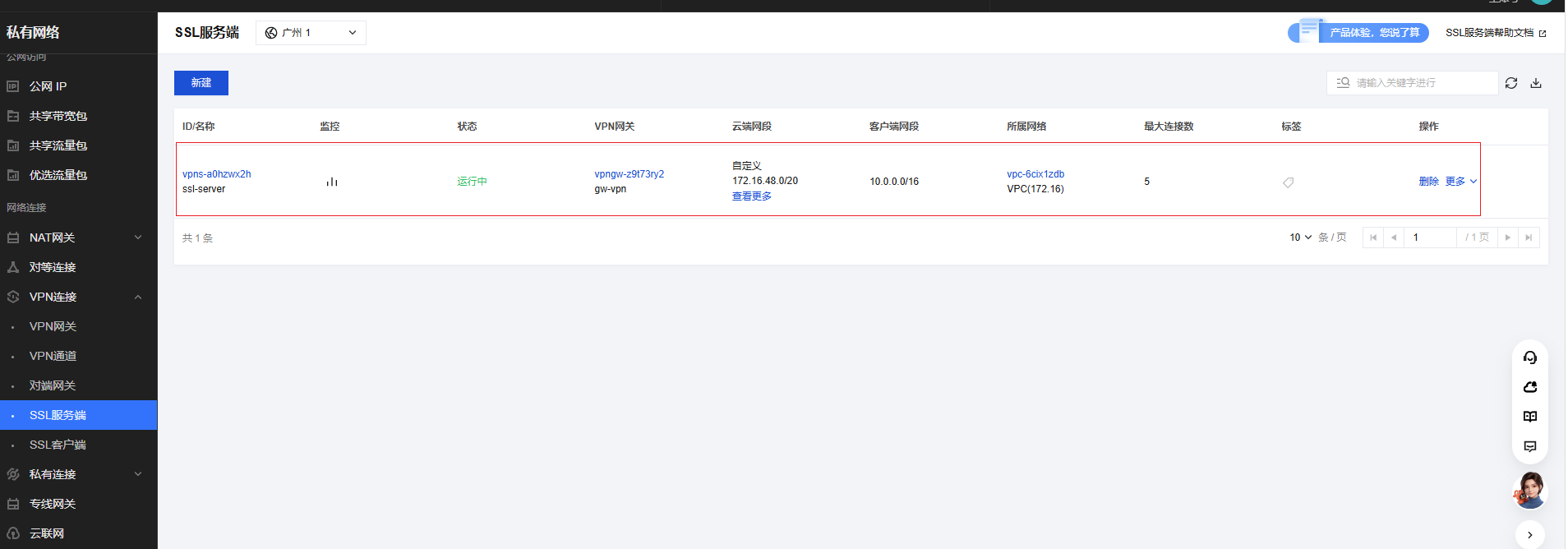
2.2 创建SSL服务端
创建 SSL 服务端时,需与上一步创建的 SSL VPN 网关绑定,并关联公有云侧的 VPC 地址或多个子网地址,同时关联本地侧的内网网段地址。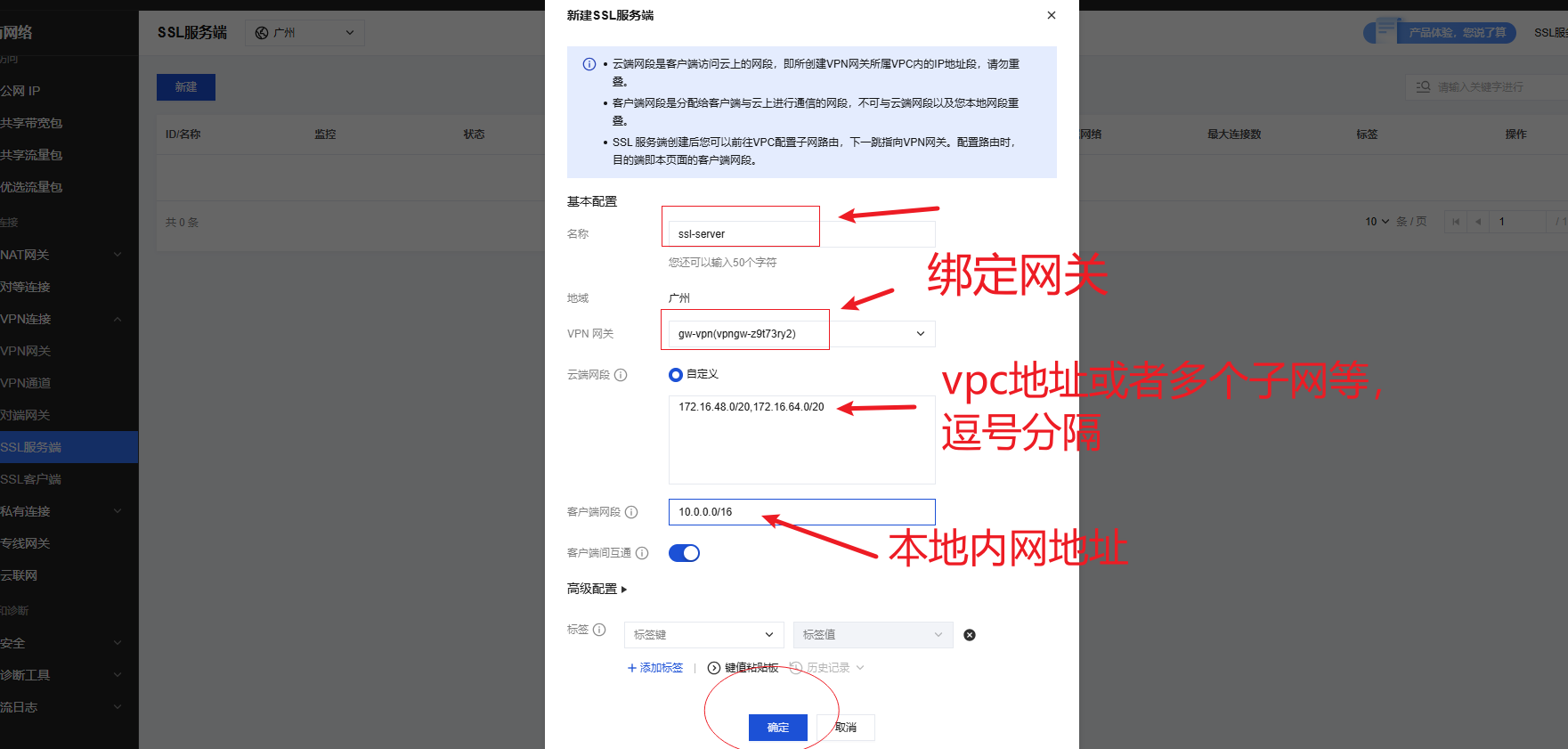
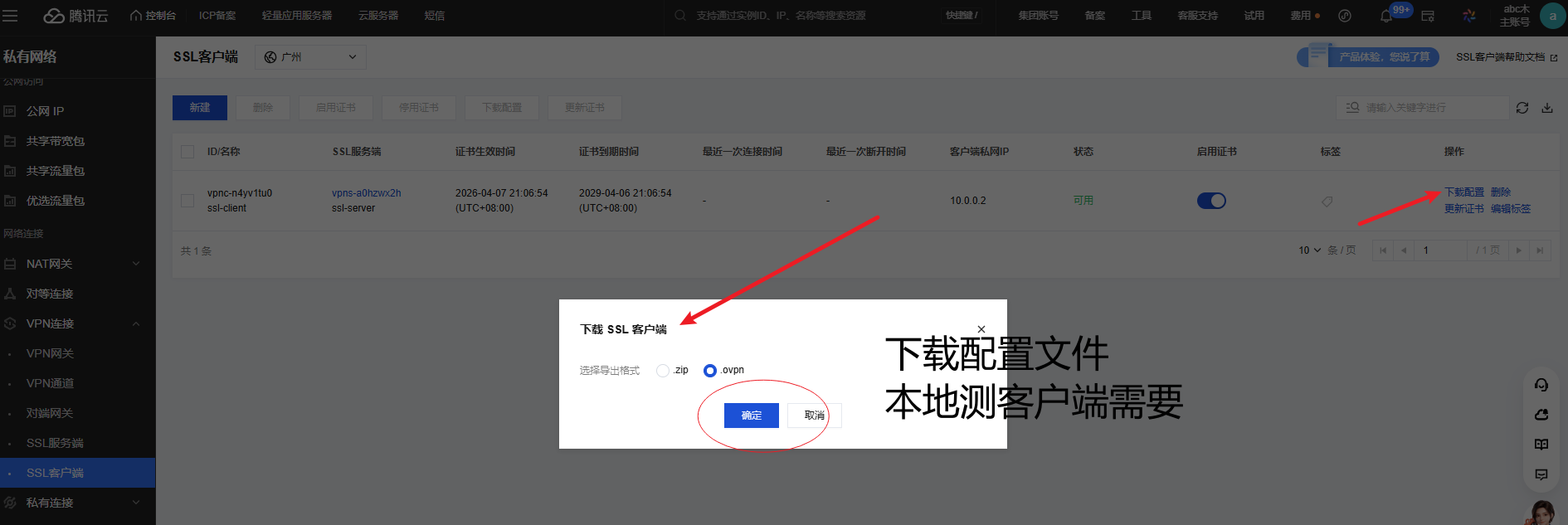
2.3 创建SSL客户端
SSL客户端需要和SSL服务端绑定,创建SSL客户端并绑定SSL服务端后,需要下载配置复制到本地客户端用。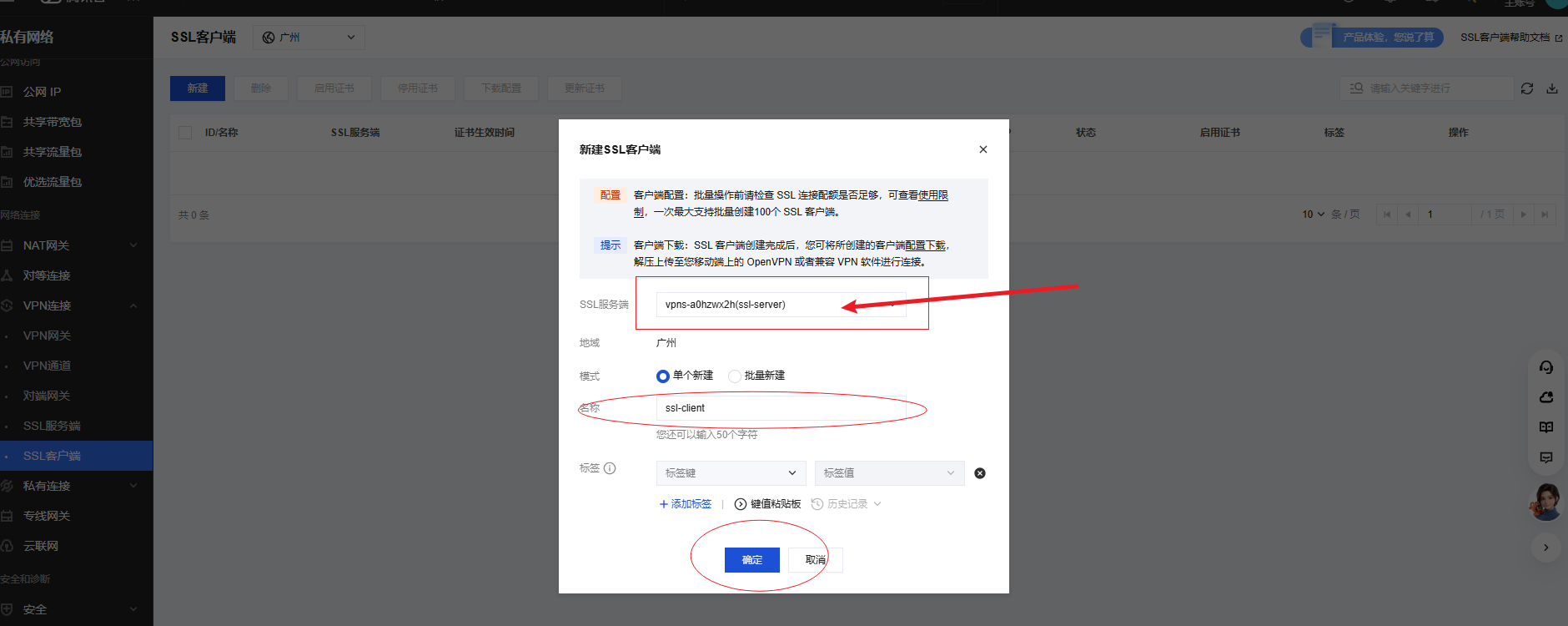
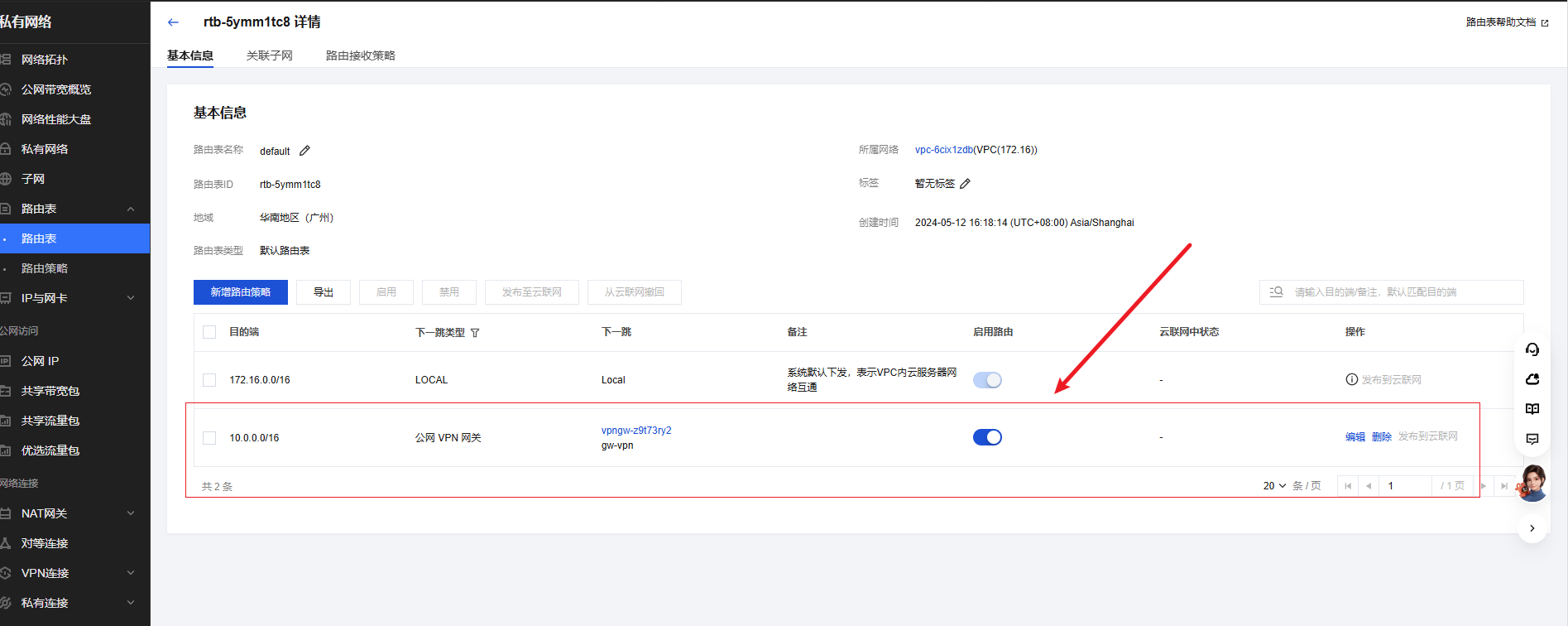
2.3 设置路由策略
注意:需要更新对应vpc对应的路由表策略。目的端写本地侧网段地址,下一跳类型为公网v p n 网关,选择正确的下一条网关。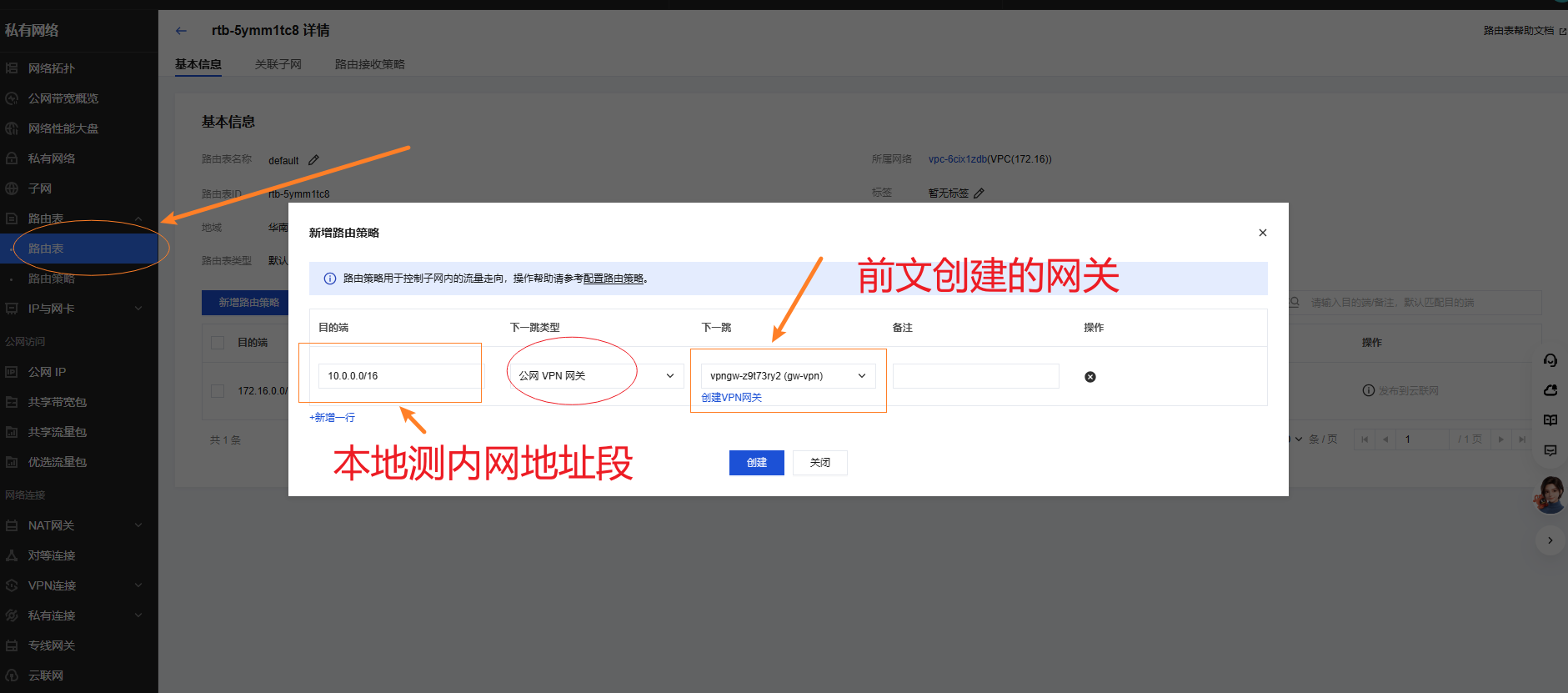
3. 本地侧操作步骤
3.1 本地侧部署客户端软件
为了更方便在客户端服务器部署客户端软件,l在本地linux服务器上使用 docker 运行 openv p n 软件
bash
mkdir -p /docker/openvpn && cd /docker/openvpn
cat > docker-compose.yml<<EOF
services:
openvpn-client:
#image: kylemanna/openvpn:latest
image: swr.cn-north-4.myhuaweicloud.com/ddn-k8s/docker.io/kylemanna/openvpn:latest
container_name: openvpn-client
cap_add:
- NET_ADMIN
network_mode: host
devices:
- /dev/net/tun
volumes:
- ./SSLVpnClientConfiguration.ovpn:/etc/openvpn/client.ovpn
command: openvpn --config /etc/openvpn/client.ovpn
restart: always
EOF
bash
# SSLVpnClientConfiguration.ovpn 是在公有云下载的配置
cd /docker/openvpn
ls -l
[root@VM-12-10-centos openvpn]#
[root@VM-12-10-centos openvpn]# pwd
/docker/openvpn
[root@VM-12-10-centos openvpn]# ls -al
total 20
drwxr-xr-x 2 root root 4096 Apr 7 21:50 .
drwxr-xr-x 4 root root 4096 Apr 7 14:03 ..
-rw-r--r-- 1 root root 431 Apr 7 21:29 docker-compose.yml
-rw-r--r-- 1 root root 6601 Apr 7 21:26 SSLVpnClientConfiguration.ovpn
[root@VM-12-10-centos openvpn]#
bash
docker compose up -d
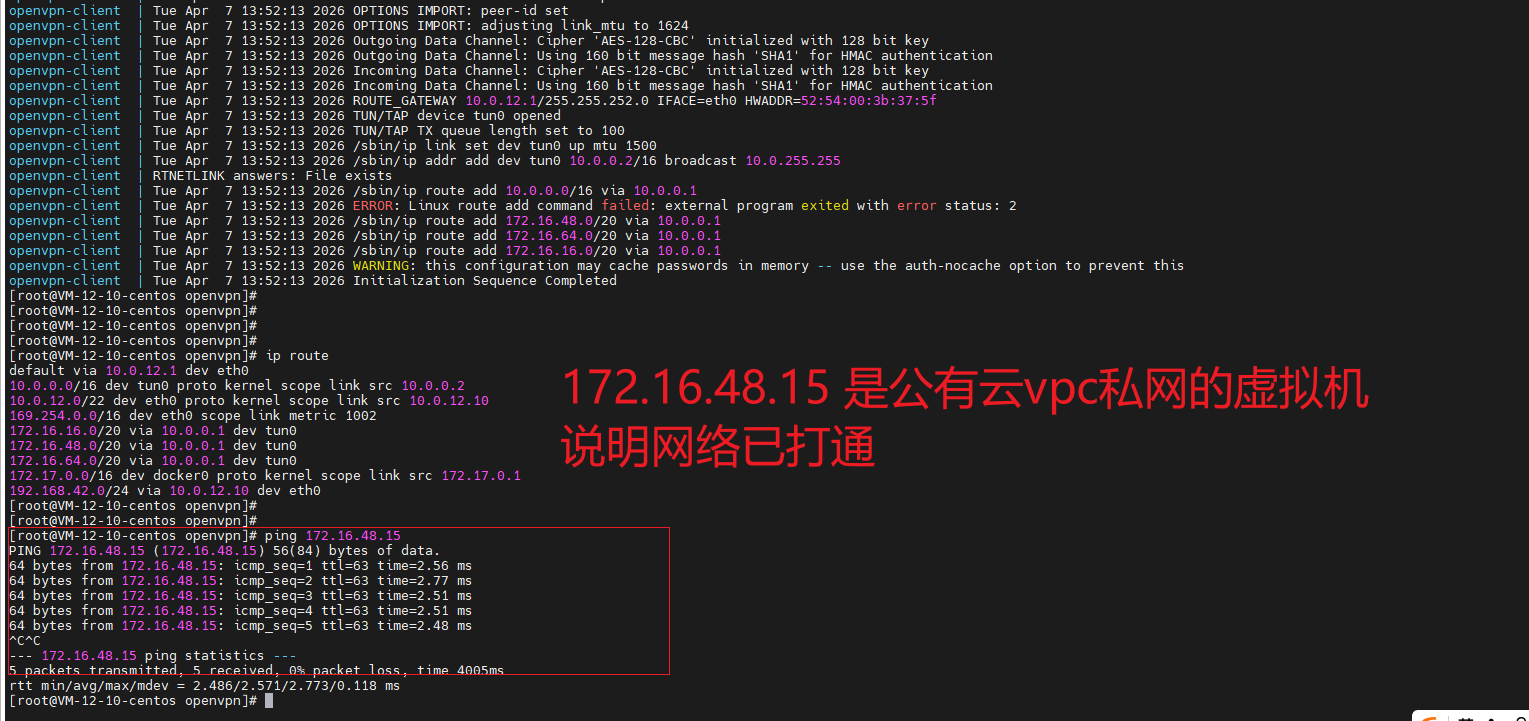
docker compose up logs3.2 本地侧验证访问公有云vpc私网资源
bash
[root@VM-12-10-centos openvpn]# pwd
/docker/openvpn
[root@VM-12-10-centos openvpn]# ls -al
total 20
drwxr-xr-x 2 root root 4096 Apr 7 21:50 .
drwxr-xr-x 4 root root 4096 Apr 7 14:03 ..
-rw-r--r-- 1 root root 431 Apr 7 21:29 docker-compose.yml
-rw-r--r-- 1 root root 6601 Apr 7 21:26 SSLVpnClientConfiguration.ovpn
[root@VM-12-10-centos openvpn]#
[root@VM-12-10-centos openvpn]#
[root@VM-12-10-centos openvpn]# docker compose ps
NAME IMAGE COMMAND SERVICE CREATED STATUS PORTS
openvpn-client swr.cn-north-4.myhuaweicloud.com/ddn-k8s/docker.io/kylemanna/openvpn:latest "openvpn --config /e..." openvpn-client 18 minutes ago Up 18 minutes
[root@VM-12-10-centos openvpn]#
[root@VM-12-10-centos openvpn]#
[root@VM-12-10-centos openvpn]# docker compose logs
openvpn-client | Tue Apr 7 13:52:12 2026 Unrecognized option or missing or extra parameter(s) in /etc/openvpn/client.ovpn:21: data-ciphers (2.4.9)
openvpn-client | Tue Apr 7 13:52:12 2026 Unrecognized option or missing or extra parameter(s) in /etc/openvpn/client.ovpn:22: compat-mode (2.4.9)
openvpn-client | Tue Apr 7 13:52:12 2026 OpenVPN 2.4.9 x86_64-alpine-linux-musl [SSL (OpenSSL)] [LZO] [LZ4] [EPOLL] [MH/PKTINFO] [AEAD] built on Apr 20 2020
openvpn-client | Tue Apr 7 13:52:12 2026 library versions: OpenSSL 1.1.1g 21 Apr 2020, LZO 2.10
openvpn-client | Tue Apr 7 13:52:12 2026 Outgoing Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
openvpn-client | Tue Apr 7 13:52:12 2026 Incoming Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
openvpn-client | Tue Apr 7 13:52:12 2026 TCP/UDP: Preserving recently used remote address: [AF_INET]119.91.105.32:9798
openvpn-client | Tue Apr 7 13:52:12 2026 Socket Buffers: R=[212992->212992] S=[212992->212992]
openvpn-client | Tue Apr 7 13:52:12 2026 UDP link local: (not bound)
openvpn-client | Tue Apr 7 13:52:12 2026 UDP link remote: [AF_INET]119.91.105.32:9798
openvpn-client | Tue Apr 7 13:52:12 2026 TLS: Initial packet from [AF_INET]119.91.105.32:9798, sid=686ae7e7 de5f3074
openvpn-client | Tue Apr 7 13:52:12 2026 VERIFY OK: depth=1, C=CN, ST=GuangDong, L=ShenZhen, CN=Tencent Cloud VPN CA
openvpn-client | Tue Apr 7 13:52:12 2026 VERIFY KU OK
openvpn-client | Tue Apr 7 13:52:12 2026 Validating certificate extended key usage
openvpn-client | Tue Apr 7 13:52:12 2026 ++ Certificate has EKU (str) TLS Web Server Authentication, expects TLS Web Server Authentication
openvpn-client | Tue Apr 7 13:52:12 2026 VERIFY EKU OK
openvpn-client | Tue Apr 7 13:52:12 2026 VERIFY OK: depth=0, CN=vpns-a0hzwx2h
openvpn-client | Tue Apr 7 13:52:12 2026 Control Channel: TLSv1.2, cipher TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384, 2048 bit RSA
openvpn-client | Tue Apr 7 13:52:12 2026 [vpns-a0hzwx2h] Peer Connection Initiated with [AF_INET]119.91.105.32:9798
openvpn-client | Tue Apr 7 13:52:13 2026 SENT CONTROL [vpns-a0hzwx2h]: 'PUSH_REQUEST' (status=1)
openvpn-client | Tue Apr 7 13:52:13 2026 PUSH: Received control message: 'PUSH_REPLY,route 10.0.0.0 255.255.0.0,route-gateway 10.0.0.1,topology subnet,ping 3,ping-restart 18,route 172.16.48.0 255.255.240.0,route 172.16.64.0 255.255.240.0,route 172.16.16.0 255.255.240.0,ifconfig 10.0.0.2 255.255.0.0,peer-id 0'
openvpn-client | Tue Apr 7 13:52:13 2026 OPTIONS IMPORT: timers and/or timeouts modified
openvpn-client | Tue Apr 7 13:52:13 2026 OPTIONS IMPORT: --ifconfig/up options modified
openvpn-client | Tue Apr 7 13:52:13 2026 OPTIONS IMPORT: route options modified
openvpn-client | Tue Apr 7 13:52:13 2026 OPTIONS IMPORT: route-related options modified
openvpn-client | Tue Apr 7 13:52:13 2026 OPTIONS IMPORT: peer-id set
openvpn-client | Tue Apr 7 13:52:13 2026 OPTIONS IMPORT: adjusting link_mtu to 1624
openvpn-client | Tue Apr 7 13:52:13 2026 Outgoing Data Channel: Cipher 'AES-128-CBC' initialized with 128 bit key
openvpn-client | Tue Apr 7 13:52:13 2026 Outgoing Data Channel: Using 160 bit message hash 'SHA1' for HMAC authentication
openvpn-client | Tue Apr 7 13:52:13 2026 Incoming Data Channel: Cipher 'AES-128-CBC' initialized with 128 bit key
openvpn-client | Tue Apr 7 13:52:13 2026 Incoming Data Channel: Using 160 bit message hash 'SHA1' for HMAC authentication
openvpn-client | Tue Apr 7 13:52:13 2026 ROUTE_GATEWAY 10.0.12.1/255.255.252.0 IFACE=eth0 HWADDR=52:54:00:3b:37:5f
openvpn-client | Tue Apr 7 13:52:13 2026 TUN/TAP device tun0 opened
openvpn-client | Tue Apr 7 13:52:13 2026 TUN/TAP TX queue length set to 100
openvpn-client | Tue Apr 7 13:52:13 2026 /sbin/ip link set dev tun0 up mtu 1500
openvpn-client | Tue Apr 7 13:52:13 2026 /sbin/ip addr add dev tun0 10.0.0.2/16 broadcast 10.0.255.255
openvpn-client | RTNETLINK answers: File exists
openvpn-client | Tue Apr 7 13:52:13 2026 /sbin/ip route add 10.0.0.0/16 via 10.0.0.1
openvpn-client | Tue Apr 7 13:52:13 2026 ERROR: Linux route add command failed: external program exited with error status: 2
openvpn-client | Tue Apr 7 13:52:13 2026 /sbin/ip route add 172.16.48.0/20 via 10.0.0.1
openvpn-client | Tue Apr 7 13:52:13 2026 /sbin/ip route add 172.16.64.0/20 via 10.0.0.1
openvpn-client | Tue Apr 7 13:52:13 2026 /sbin/ip route add 172.16.16.0/20 via 10.0.0.1
openvpn-client | Tue Apr 7 13:52:13 2026 WARNING: this configuration may cache passwords in memory -- use the auth-nocache option to prevent this
openvpn-client | Tue Apr 7 13:52:13 2026 Initialization Sequence Completed
[root@VM-12-10-centos openvpn]#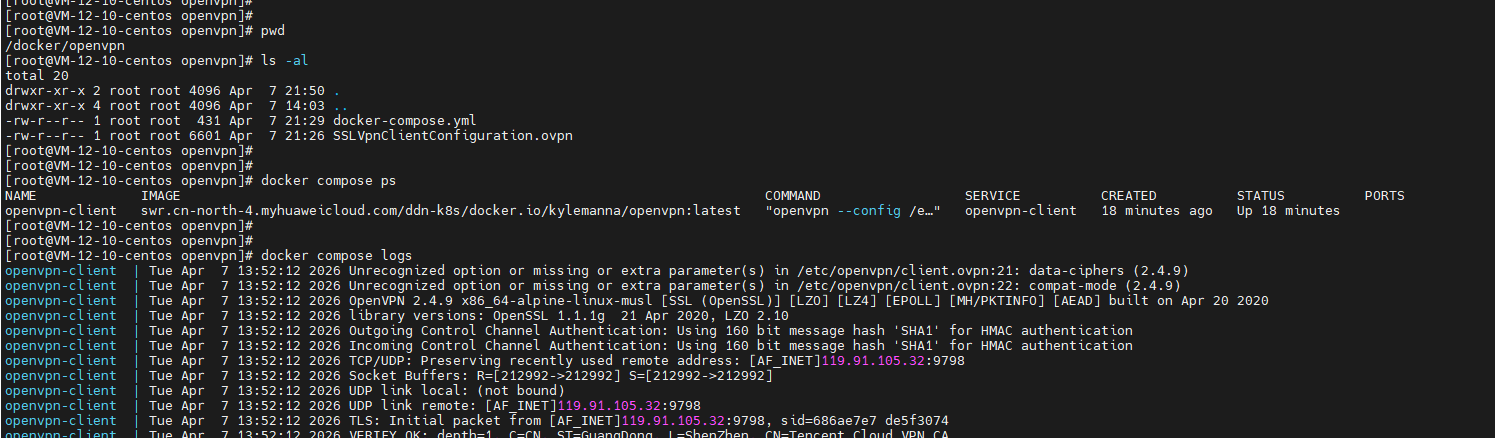
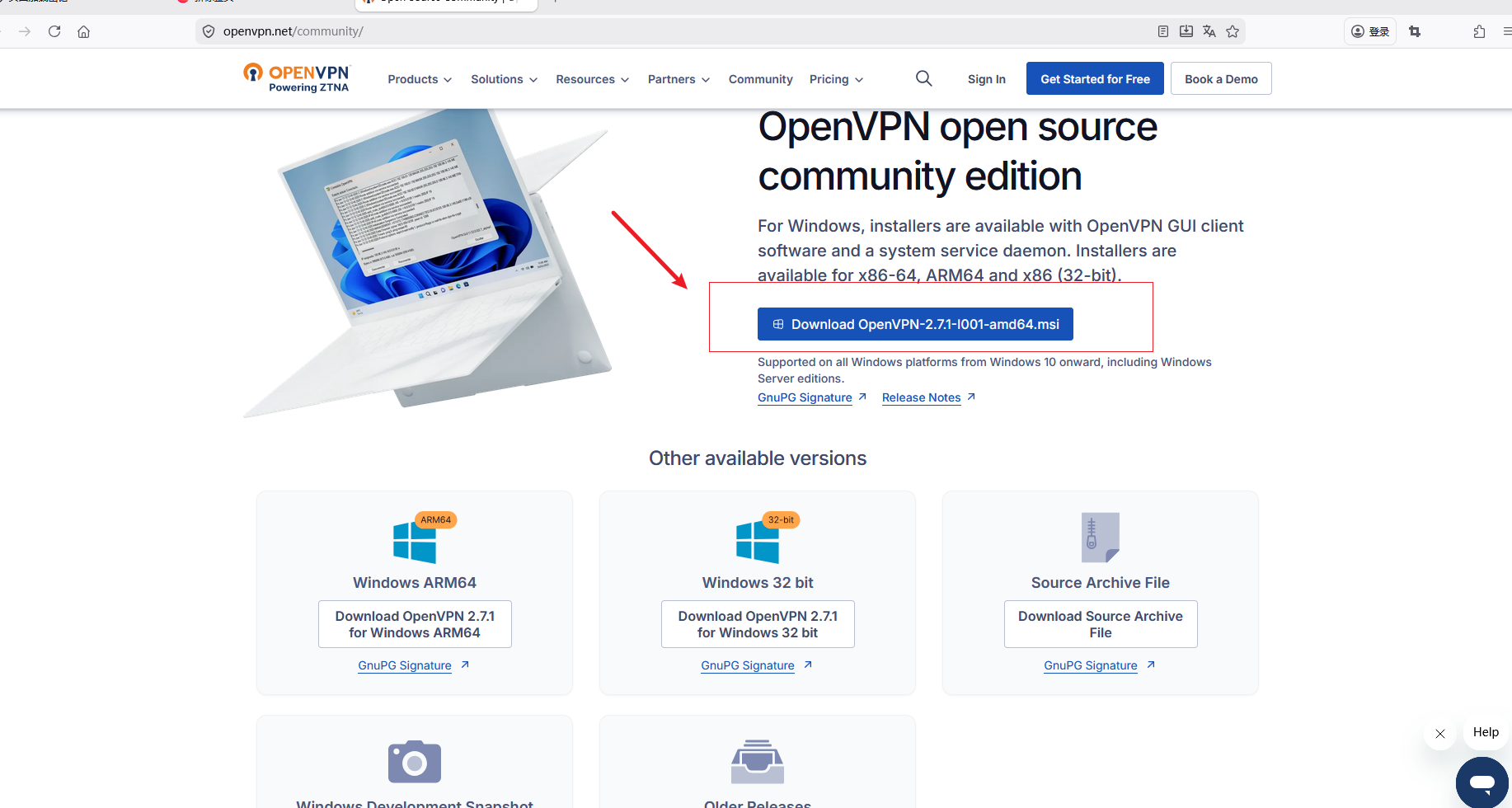
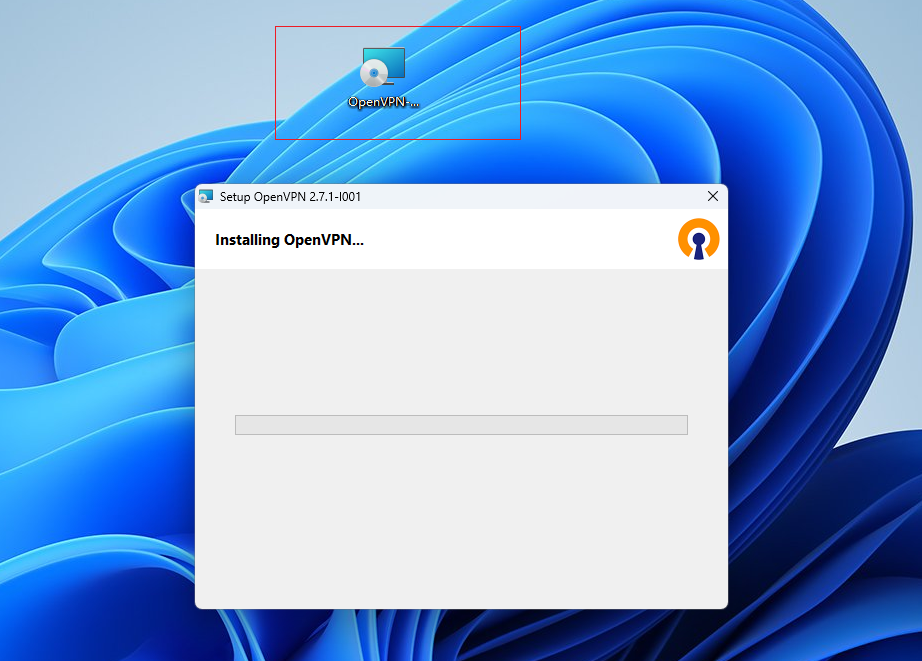
3.3 本地侧 Windows 安装 open v p n 软件
https://openvpn.net/community/
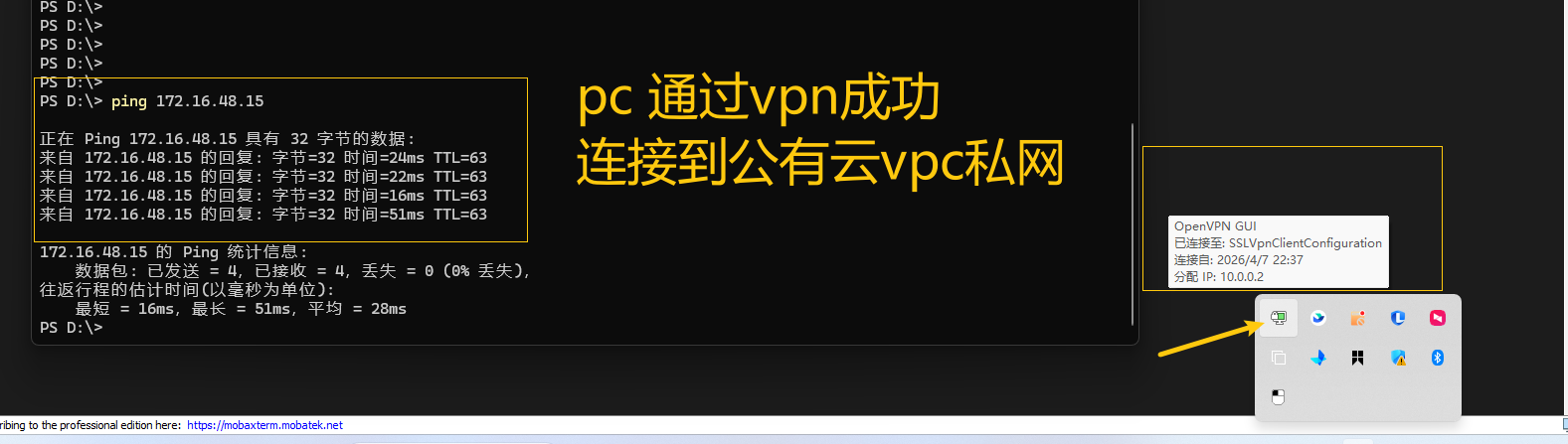
4. 验证结果
- 不管是本地的虚拟还是本地的PC 都能通过 v p n 安全访问到公有云vpc私网的资源。
5. 注意事项
- 如果按照步骤还访问不通需要检查防火墙,安全组以及网络ACL策略等。以及访问的子网是否在范围内等
- 一个客户端配置只能一个 openv p n 在线。