"Isn't it safe as long as I keep my assets in my own wallet?"
This is one of the most common assumptions in Web3---but it's only half true.
Self-custody eliminates reliance on centralized exchanges, reducing risks such as platform freezes or insolvency. However, from the moment a seed phrase is generated, every user action becomes part of the security boundary.
In April 2026 alone, the crypto industry experienced over 10 major security incidents, with losses exceeding $600 million. Notably, a significant portion of these losses did not come from protocol vulnerabilities, but from user mistakes and improper wallet usage. As a result, "wallet security" has once again become a core topic in Web3.
- Seed Phrase Security: The Weakest Link Is Often the User
A seed phrase (Mnemonic Phrase), based on the BIP-39 standard, is the root key of a hierarchical deterministic (HD) wallet. Whoever controls the seed phrase controls all associated assets.
In real-world cases, common mistakes include:
-
Storing seed phrases in cloud notes
-
Sending them via messaging apps
-
Taking screenshots or copying them into clipboard history
These actions expose the seed phrase to online environments, dramatically increasing the risk of leakage.
Best practices include:
-
Writing the seed phrase on physical media
-
Storing it offline in multiple secure locations
-
Never allowing it to touch internet-connected devices
For long-term durability, some users adopt metal backup solutions (such as UKey Ti), which provide resistance to fire, water, and corrosion.
- Software Wallet Security ≠ Private Key Security
Software wallets like MetaMask and Trust Wallet are widely used due to their convenience and ecosystem integration.
However, their private keys are ultimately stored on internet-connected devices.
This means:
→ If the device is compromised, the private key may also be at risk.
This is where hardware wallets come into play.
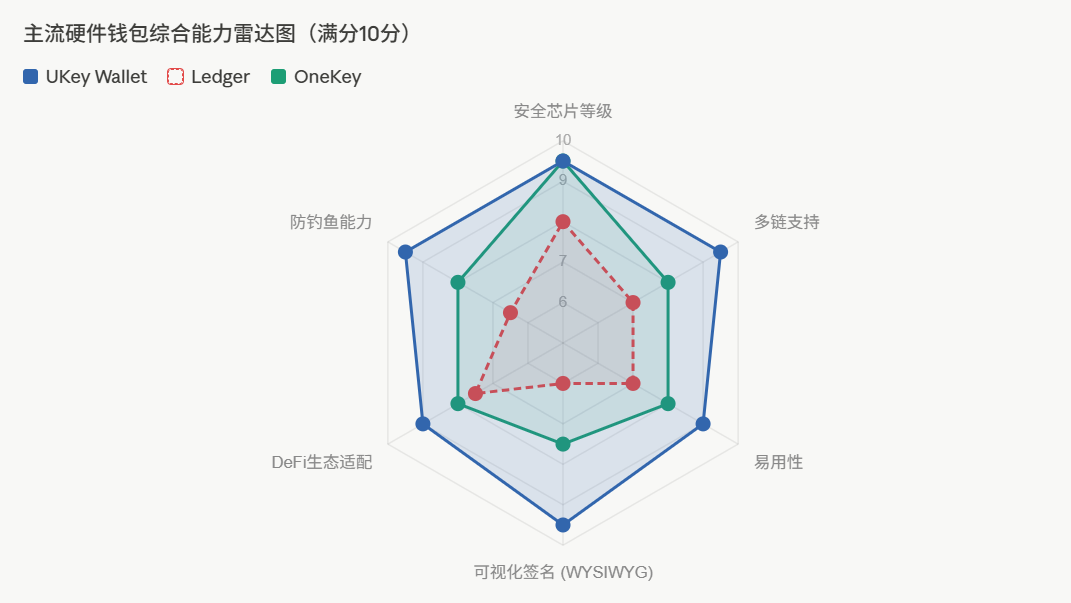
Devices from Ledger and OneKey isolate private keys within secure hardware environments. UKey Wallet's flagship device, UKey Core, adopts an EAL 6+ secure element---offering a higher level of protection against physical and side-channel attacks compared to common EAL 5+ implementations.
- Blind Signing: The Most Overlooked Critical Risk
One of the most dangerous threats in Web3 today is "blind signing."
Blind signing occurs when:
→ The information displayed to the user ≠ the actual transaction executed on-chain
This risk becomes especially prominent in complex DeFi interactions.
The industry is increasingly converging on a new standard:
→ WYSIWYG (What You See Is What You Sign)
UKey Wallet addresses this issue through its hardware device UKey Core, which independently parses raw transaction data and displays structured, human-readable information directly on the device screen, including:
-
Approval amounts
-
Contract addresses
-
Permission scopes
This eliminates reliance on potentially compromised front-end interfaces and significantly reduces manipulation risks.
- On-Chain Approvals: The Hidden Long-Term Risk
Every interaction with DeFi protocols or NFT platforms involves granting token approvals.
To save time, many users choose "Unlimited Approval." While convenient, this creates long-term vulnerabilities.
If a protocol is later exploited:
→ Approved assets may be drained without requiring access to the private key
This means:
Even a perfectly secure hardware wallet cannot protect against poor authorization management.
Best practices include:
-
Regularly reviewing approval history
-
Revoking unnecessary permissions
-
Avoiding unlimited approvals when possible
At the tool level, solutions like UKey Wallet integrate approval management and risk alerts, helping users identify malicious addresses and risky permissions before signing transactions.
Final Thoughts: Security Is Shifting Toward User Awareness
Web3 security is evolving---from preventing hacks to preventing mistakes.
A truly secure wallet today must not only ensure:
Private key isolation
Offline signing
But also:
Clear transaction understanding
Risk awareness at the user level
In this context, UKey Wallet's approach---combining secure architecture with user-centric design---reflects a broader industry trend: making security not just stronger, but more understandable.
As multi-chain ecosystems continue to expand, solutions that balance security and usability are increasingly becoming the preferred choice for Web3 users.