登录服务器,发现root的用户名和密码登录不上去,去机房搞,还要花费一些时间,用了普通用户账号密码,可以登录进去了,赶紧改了root的密码,可以登录了。一看负载,之前是20多,现在变成了70多,肯定又进挖矿病毒了。
上一次是我frp暴露的登录密码太弱了,改了强密码后没想到这么快又被攻破了。
一,处理挖矿病毒
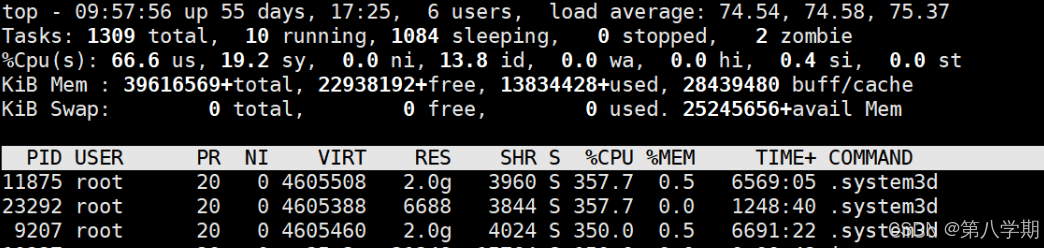
1、top看了进程高的command,是system3d挖矿病毒
2、看定时任务,有一些/tmp下的定时任务,都清理掉!
[root@baidu01 /tmp]# crontab -l
@daily /tmp/.est1/./.b4nd1d0
@reboot /tmp/.est1/./.b4nd1d0 > /dev/null 2>&1 & disown
* * * * * /tmp/.est1/./.b4nd1d0 > /dev/null 2>&1 & disown
@monthly /tmp/.est1/./.b4nd1d0 > /dev/null 2>&1 & disown
0 2 * * * /data/lib/etcd/backup/etcd_backup.sh &> /dev/null
# 删除异常的定时任务
[root@baidu01 ~]# crontab -e
crontab: installing new crontab
[root@baidu01 ~]# crontab -l
0 2 * * * /data/lib/etcd/backup/etcd_backup.sh &> /dev/null3、根据进程ID查找病毒文件位置
4、停止进程并删除病毒文件
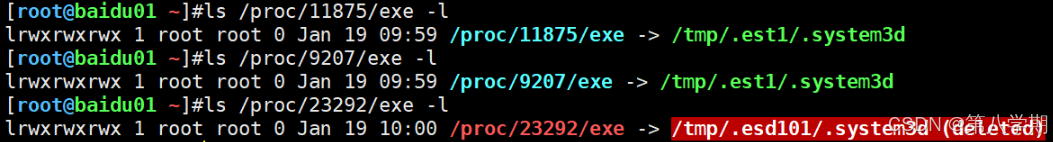
[root@baidu01 ~]# ls /proc/11875/exe -l
lrwxrwxrwx 1 root root 0 Jan 19 09:59 /proc/11875/exe -> /tmp/.est1/.system3d
[root@baidu01 ~]# ls /proc/9207/exe -l
lrwxrwxrwx 1 root root 0 Jan 19 09:59 /proc/9207/exe -> /tmp/.est1/.system3d
[root@baidu01 ~]# ls /proc/23292/exe -l
lrwxrwxrwx 1 root root 0 Jan 19 10:00 /proc/23292/exe -> /tmp/.esd101/.system3d (deleted)
[root@baidu01 ~]# kill -9 11875
[root@baidu01 ~]# kill -9 9207
[root@baidu01 ~]# kill -9 23292
[root@baidu01 ~]# ls -a /tmp/
./ ../ .esd101/ .est1/ .font-unix/ .ICE-unix/ .temp/ .Test-unix/ .X11-unix/ .XIM-unix/
[root@baidu01 ~]# ls /tmp/.est1/
.b4nd1d0 config.json .pidsclip .system3d
[root@baidu01 ~]# rm -rf /tmp/.est1/
[root@baidu01 ~]# ls /tmp/.esd101/
.b4nd1d0 config.json .system3d
[root@baidu01 ~]# rm -rf /tmp/.esd101/5、此时处理完负载会减少一些
6、排查是否有异常用户,uid,gid都是0
(1)发现一个dubai用户,是刚创建的,删除掉
[root@baidu01 ~]# grep "0" /etc/passwd
root:x:0:0:root:/root:/bin/bash
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
dubai:x:0:0::/home/dubai:/bin/bash
user:x:1000:1000::/home/user:/bin/bash
[root@baidu01 ~]# ls -lrth /home/
total 0
drwxr-xr-x. 3 root root 26 Nov 1 17:13 disk11
drwxr-xr-x. 2 root root 10 Nov 1 17:13 data
drwxr-xr-x. 2 root root 10 Nov 2 16:15 opt
drwx------ 2 clamav clamav 78 Dec 1 10:04 clamav
drwxr-xr-x 3 root root 26 Dec 6 14:55 baidu
drwx------ 6 user user 183 Dec 18 21:28 user
drwx------ 3 root root 94 Jan 19 09:51 dubai
#删除提示被进程1占用
[root@baidu01 ~]# userdel -r dubai
userdel: user dubai is currently used by process 1(2)使用vipw删除dubai的用户行;
(3)在/etc/shodow把dubai用户行删掉,把/home/dubai目录删掉,/var/spool/mail/dubai删掉
[root@baidu01 /home]#rm -rf dubai/
[root@baidu01 /home]#rm -rf /var/spool/mail/dubai二、处理暴力破解
进程处理好后,我们来处理下暴力破解问题,每次我登录都提示有多少次登录失败,比如下面信息,提示六千多次。
WARNING! The remote SSH server rejected X11 forwarding request.
Last failed login: Fri Jan 19 09:44:46 CST 2024 from localhost on ssh:notty
There were 6626 failed login attempts since the last successful login.
Last login: Thu Jan 18 18:10:58 2024 from 10.10.50.233通过lastb命令也可以看到不断有登陆请求去登陆我们的主机,所以我们要禁止重复登陆那么多次。
我们使用Fail2ban的软件防止被暴力破解。
1、安装软件
[root@baidu01 ~]# yum install epel-release -y
[root@baidu01 ~]# yum install fail2ban -y
[root@baidu01 ~]# fail2ban-server --version
Fail2Ban v0.11.22、编辑配置文件
[root@baidu01 ~]# cat /etc/fail2ban/jail.local
[sshd]
enabled = true
filter = sshd
port = 22
maxretry = 3
findtime = 60
bantime = -1
action = %(action_mwl)s3、重启服务后生效
[root@baidu01 ~]# systemctl restart fail2ban.service
[root@baidu01 ~]# systemctl enable fail2ban.service4、在其它主机连接该主机测试
root@serverai:~# ssh 10.10.50.67
root@10.10.50.67's password:
Permission denied, please try again.
root@10.10.50.67's password:
Permission denied, please try again.
root@10.10.50.67's password:
Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password).
# 失败3次后,服务端的主机禁止了该IP,即使输入正确的也会提示不能登陆
[root@baidu01 ~]# fail2ban-client status sshd
Status for the jail: sshd
|- Filter
| |- Currently failed: 1
| |- Total failed: 11
| `- Journal matches: _SYSTEMD_UNIT=sshd.service + _COMM=sshd
`- Actions
|- Currently banned: 1
|- Total banned: 1
`- Banned IP list: 10.10.50.20 #禁止IP列表5、封禁解除
[root@baidu01 ~]# fail2ban-client set sshd unbanip 10.10.50.20
1
[root@baidu01 ~]# fail2ban-client status sshd
Status for the jail: sshd
|- Filter
| |- Currently failed: 1
| |- Total failed: 14
| `- Journal matches: _SYSTEMD_UNIT=sshd.service + _COMM=sshd
`- Actions
|- Currently banned: 0
|- Total banned: 1
`- Banned IP list: