前言:
稍微讲述一下本文的输出顺序,首先会部署一个k8s常用的管理面板,然后针对于该面板展开讲解RBAC是如何正确创建用户以及使用的,以及如何正确使用对应的权限等等,话不多说,直接进入主题
Dashboard
参考文档
官方地址
https://github.com/kubernetes/dashboard
资源配置
https://raw.githubusercontent.com/kubernetes/dashboard/v2.0.4/aio/deploy/recommended.yaml
部署流程
1、执行dashboard文件
注意:由于dashboard下载的文件当中service是clusterip类型的,所有我们外部是访问不到的,因此需要给它创建一个ingress,但此处由于我的电脑原因,不能修改/etc/hosts文件,于是这里我是修改了下载文件当中的service服务的,改为了nodeport
# Copyright 2017 The Kubernetes Authors.
#
# Licensed under the Apache License, Version 2.0 (the "License");
# you may not use this file except in compliance with the License.
# You may obtain a copy of the License at
#
# http://www.apache.org/licenses/LICENSE-2.0
#
# Unless required by applicable law or agreed to in writing, software
# distributed under the License is distributed on an "AS IS" BASIS,
# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
# See the License for the specific language governing permissions and
# limitations under the License.
apiVersion: v1
kind: Namespace
metadata:
name: kubernetes-dashboard
---
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kubernetes-dashboard
---
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kubernetes-dashboard
spec:
ports:
- port: 443
targetPort: 8443
nodePort: 30445
selector:
k8s-app: kubernetes-dashboard
type: NodePort
---
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-certs
namespace: kubernetes-dashboard
type: Opaque
---
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-csrf
namespace: kubernetes-dashboard
type: Opaque
data:
csrf: ""
---
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-key-holder
namespace: kubernetes-dashboard
type: Opaque
---
kind: ConfigMap
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-settings
namespace: kubernetes-dashboard
---
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kubernetes-dashboard
rules:
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs", "kubernetes-dashboard-csrf"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster", "dashboard-metrics-scraper"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:", "dashboard-metrics-scraper", "http:dashboard-metrics-scraper"]
verbs: ["get"]
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
rules:
# Allow Metrics Scraper to get metrics from the Metrics server
- apiGroups: ["metrics.k8s.io"]
resources: ["pods", "nodes"]
verbs: ["get", "list", "watch"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kubernetes-dashboard
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kubernetes-dashboard
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: kubernetes-dashboard
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: kubernetes-dashboard
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kubernetes-dashboard
---
kind: Deployment
apiVersion: apps/v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kubernetes-dashboard
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
spec:
containers:
- name: kubernetes-dashboard
image: kubernetesui/dashboard:v2.0.4
imagePullPolicy: Always
ports:
- containerPort: 8443
protocol: TCP
args:
- --auto-generate-certificates
- --namespace=kubernetes-dashboard
# Uncomment the following line to manually specify Kubernetes API server Host
# If not specified, Dashboard will attempt to auto discover the API server and connect
# to it. Uncomment only if the default does not work.
# - --apiserver-host=http://my-address:port
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
# Create on-disk volume to store exec logs
- mountPath: /tmp
name: tmp-volume
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
securityContext:
allowPrivilegeEscalation: false
readOnlyRootFilesystem: true
runAsUser: 1001
runAsGroup: 2001
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {}
serviceAccountName: kubernetes-dashboard
nodeSelector:
"kubernetes.io/os": linux
# Comment the following tolerations if Dashboard must not be deployed on master
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
---
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: dashboard-metrics-scraper
name: dashboard-metrics-scraper
namespace: kubernetes-dashboard
spec:
ports:
- port: 8000
targetPort: 8000
selector:
k8s-app: dashboard-metrics-scraper
---
kind: Deployment
apiVersion: apps/v1
metadata:
labels:
k8s-app: dashboard-metrics-scraper
name: dashboard-metrics-scraper
namespace: kubernetes-dashboard
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: dashboard-metrics-scraper
template:
metadata:
labels:
k8s-app: dashboard-metrics-scraper
annotations:
seccomp.security.alpha.kubernetes.io/pod: 'runtime/default'
spec:
containers:
- name: dashboard-metrics-scraper
image: kubernetesui/metrics-scraper:v1.0.4
ports:
- containerPort: 8000
protocol: TCP
livenessProbe:
httpGet:
scheme: HTTP
path: /
port: 8000
initialDelaySeconds: 30
timeoutSeconds: 30
volumeMounts:
- mountPath: /tmp
name: tmp-volume
securityContext:
allowPrivilegeEscalation: false
readOnlyRootFilesystem: true
runAsUser: 1001
runAsGroup: 2001
serviceAccountName: kubernetes-dashboard
nodeSelector:
"kubernetes.io/os": linux
# Comment the following tolerations if Dashboard must not be deployed on master
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
volumes:
- name: tmp-volume
emptyDir: {}
#执行yaml文件即可
kubectl apply -f dash-board.yaml2、创建ingress(如果是直接下载的资源清单则需要执行此步骤)
cat > dashboard-ingress.yml << 'EOF'
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: kubernetes-dashboard-ingress
namespace: kubernetes-dashboard
annotations:
kubernetes.io/ingress.class: "nginx"
ingress.kubernetes.io/ssl-passthrough: "true"
nginx.ingress.kubernetes.io/backend-protocol: "HTTPS"
nginx.ingress.kubernetes.io/rewrite-target: /
spec:
rules:
- host: "dashboard.k8s.com"
http:
paths:
- path: /
pathType: ImplementationSpecific
backend:
service:
name: kubernetes-dashboard
port:
number: 443
EOF
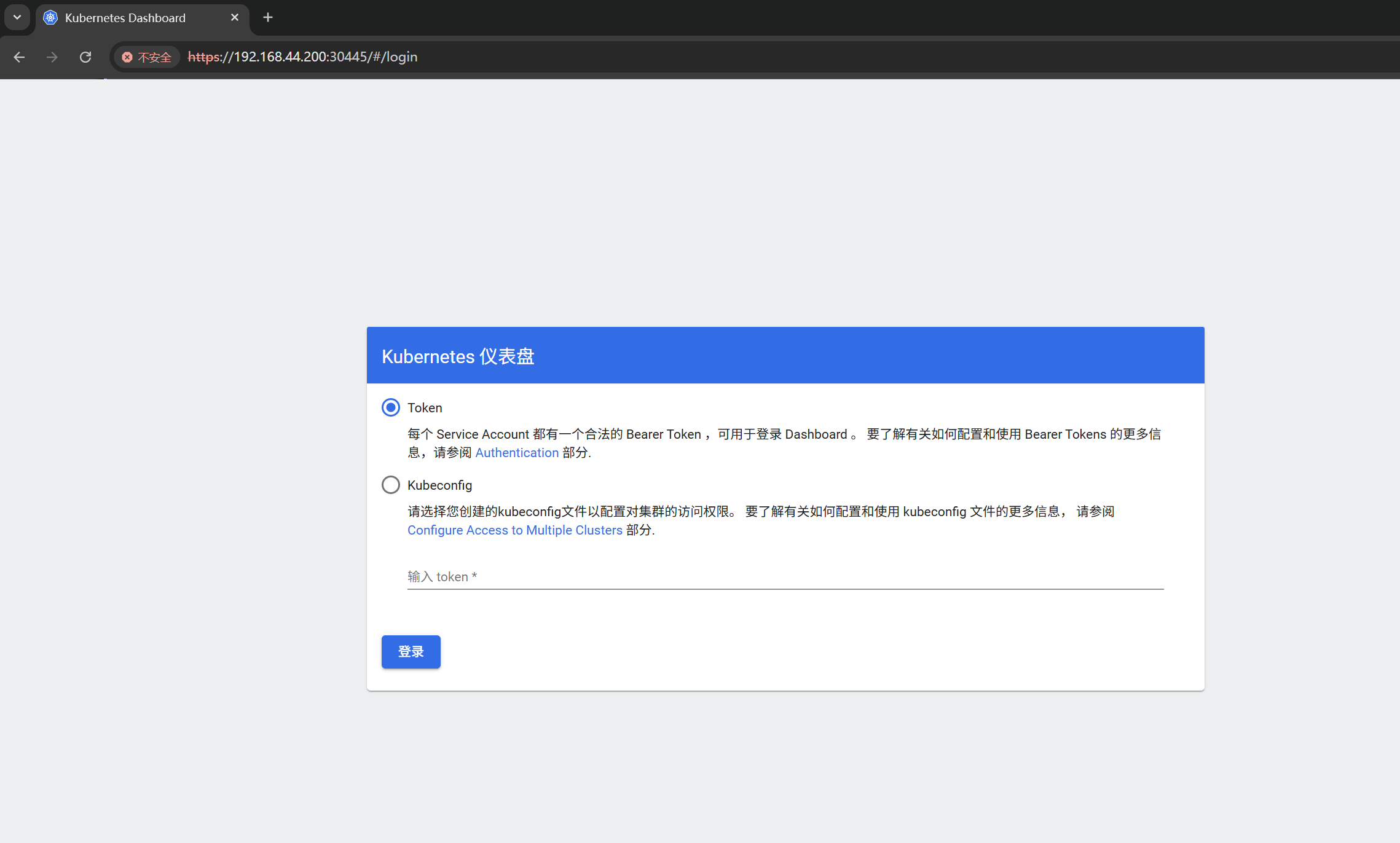
kubectl apply -f dashboard-ingress.yml如下界面访问成功!!!
3、生成token
#创建特权用户
cat > dashboard-admin.yaml<<EOF
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin-user
namespace: kubernetes-dashboard
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: admin-user
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: admin-user
namespace: kubernetes-dashboard
EOF
kubectl apply -f dashboard-admin.yaml
#生成期限为7天的token,注意admin-user为sa名称
root@k8s-master:~/k8s/dashborad# kubectl -n kubernetes-dashboard create token admin-user --duration=168h
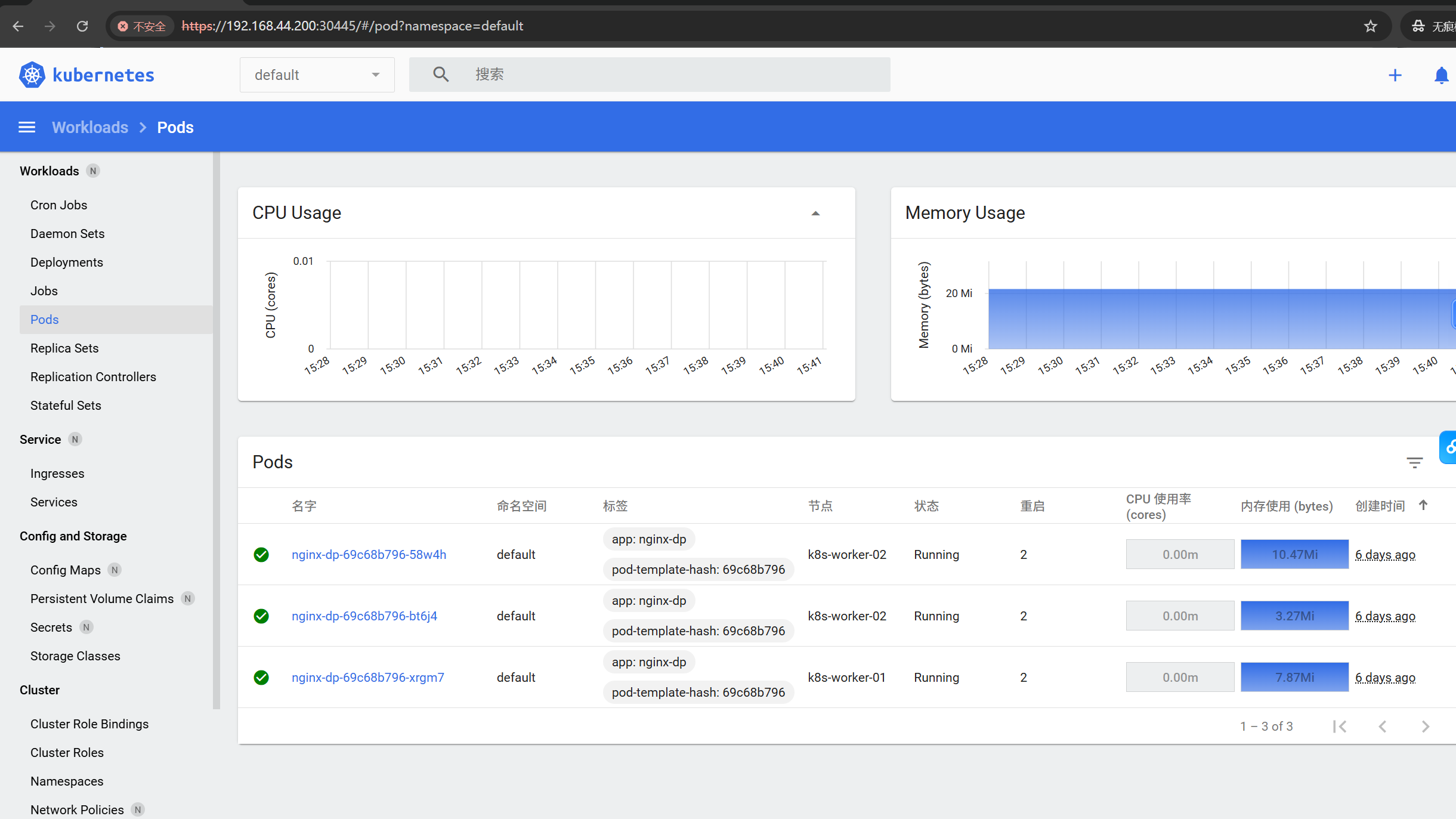
eyJhbGciOiJSUzI1NiIsImtpZCI6IkE1ek9BbTJTaTBtbVNJaUx0TWFZX2RlX05YZDlYRXhxcW9ZNV9ZVEhwVmMifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXjYWwiXSwiZXhwIjoxNzc0NjgyODgwLCJpYXQiOjE3NzQwNzgwODAsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwianRpIjoiYTc0Y2IyNDQtY2ZhWI5NGEtYjIzMzdhNjYxODk0Iiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJrdWJlcm5ldGVzLWRhc2hib2FyZCIsInNlcnZpY2VhY2NvdW50Ijp7Im5hbWUiOiJhZG1pbi11c2VyIiwidW0Nzk1YzItMzdkNi00MmM3LTkyNjEtZTZkYTkyMjk5ZDQ5In19LCJuYmYiOjE3NzQwNzgwODAsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlcm5ldGVzLWRhc2hib2FyZDphZG1pbi11-tohR0iYAgdfPBwH9l-nEzT4xiXLpE8foM3sl16oMTIH_7MKJ41Bkr370wKrOuqyRFuhcMIRuiI2DixqvpR6uH97wiE949Ui-DAHRI22dPrN_Mik1L5koZwdD_31Kw2LBZqoTX5eWyYYnqtKbHmxSMekR_jTmQf_6H8VqjcOAjv8jCfCtP4paU-GqDBhb37KP6wUvaaMVN9bG8w1L1v6bWlkKal0jqQuZbzHRiC9Y6J8BWO6kxLEXggqB9GGKla3551-DRFtlzPNJfFi4Rk15FvglgxsxzPzs978BTUCxC5fzGBHJXmn1WAzVk4sQMvanOQ正常访问界面!!!
RBAC
RBAC框架图(重点):
https://kubernetes.io/zh-cn/docs/reference/access-authn-authz/rbac/
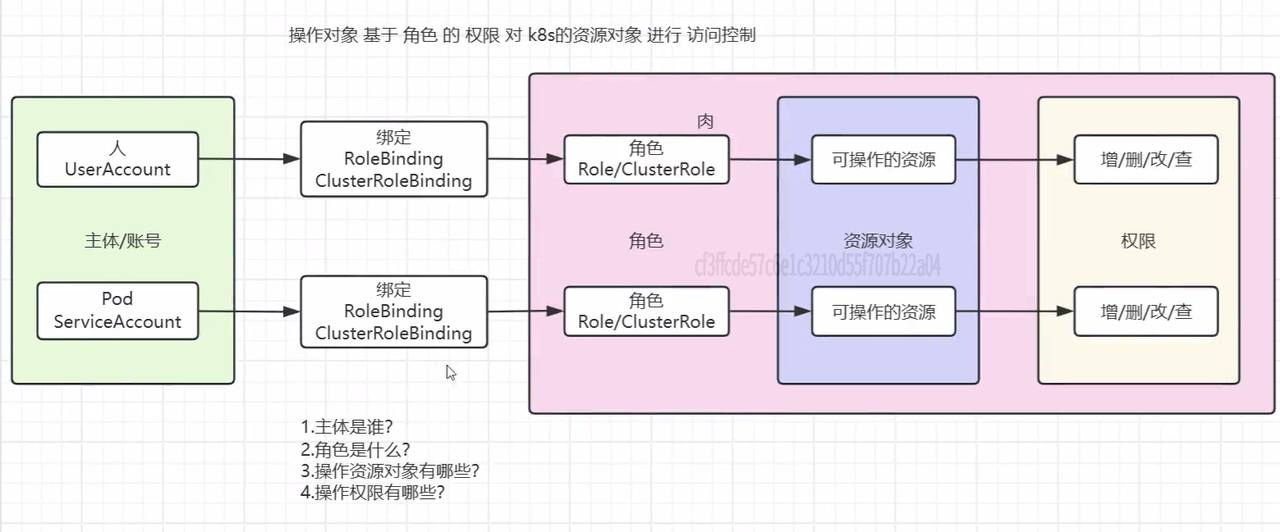
创建RBAC要搞清楚上述四点,账号给谁用(人还是pod),作用域在哪,可以操作的资源有哪些,分别给它什么权限
API资源组
1、什么是API资源组(API Group)?
API资源组是Kubernetes用于对相关API资源进行逻辑分组和版本管理的一种机制。
可以把它想象成编程语言中的包(Package) 或命名空间(Namespace)。它的主要目的有兩個:
-
组织性:将功能相似的API资源归类到一起。例如,所有与部署相关的资源(如
Deployment、DaemonSet、StatefulSet)都在apps这个组里。 -
演进与版本控制:允许Kubernetes API在未来引入新功能或更改时,不会破坏现有的客户端。一个API组可以拥有多个版本(如
v1、v1beta1、v2alpha1),不同版本代表着不同的稳定性和功能集。
2、核心组 (Core Group) 与 命名组 (Named Groups)
这是理解apiGroups如何填写的关键。
a. 核心组 (Core Group) / 遗留组 (Legacy Group)
-
是什么:这是Kubernetes最早期的一批API资源,它们非常基础且稳定。
-
包含资源:
pods,services,endpoints,persistentvolumes,nodes,namespaces,secrets,configmaps,serviceaccounts等。 -
特殊之处:它们在API路径中没有组名,使用的是
/api/v1/。 -
在RBAC中如何表示:为了在RBAC的
apiGroups字段中表示这些核心资源,你必须使用空字符串""。
b. 命名组 (Named Groups)
Kubernetes后期开发的所有新API资源都属于某个命名组。它们的组名是其完整API路径的一部分。
常见的命名组及其资源示例:
|---------------------------|--------------------------------------------------------|----------------|
| API 组名 | 包含的资源 | 说明 |
| apps | deployments, daemonsets, statefulsets, replicasets | 应用工作负载的核心组 |
| batch | jobs, cronjobs | 批处理任务 |
| networking.k8s.io | ingresses, networkpolicies | 网络相关资源 |
| rbac.authorization.k8s.io | roles, clusterroles, rolebindings, clusterrolebindings | RBAC权限本身 |
| autoscaling | horizontalpodautoscalers | 自动扩缩容 |
| storage.k8s.io | storageclasses | 存储相关 |
| apiextensions.k8s.io | customresourcedefinitions (CRDs) | 用于定义自定义资源(CRD) |
| certificates.k8s.io | certificatesigningrequests (CSRs) | 证书管理 |
3、在RBAC的Role/ClusterRole中如何编写 apiGroups
在Role或ClusterRole的规则(rules)中,apiGroups字段是一个字符串数组([]string),因为它可以同时指定多个API组。
编写规则与示例:
规则一:授权核心组的资源时,apiGroups 必须设为 [""](空字符串数组)。
rules:
- apiGroups: [""] # 核心组,双引号内无内容
resources: ["pods", "services", "secrets", "configmaps"]
verbs: ["get", "list", "watch"]规则二:授权命名组的资源时,apiGroups 设为对应的组名字符串
rules:
- apiGroups: ["apps"] # 命名组,组名是 "apps"
resources: ["deployments", "statefulsets"]
verbs: ["get", "list", "create", "update", "delete"]
- apiGroups: ["networking.k8s.io"] # 命名组,组名是 "networking.k8s.io"
resources: ["ingresses"]
verbs: ["get", "list"]4、查看资源组命令
查看资源组对象:
kubectl api-resources --api-group=""
kubectl api-resources --api-group="apps" 查看资源权限:
Kubernetes API Server 提供了标准的发现端点,让你可以找到所有可用的 API 组、版本和资源。
/apis:这是所有命名 API 组的根目录。核心组 (/api/v1) 不在此列表中。
/api:这是核心 API 组的根目录。
#列出所有可用的命名 API 组
kubectl get --raw /apis | jq '.groups[].name'
#查看资源权限
kubectl get --raw /api/v1|jq
kubectl get --raw /api/v1|jq '.resources[] | select(.name == "pods")'RBAC模板
如要创建一个RBAC用户,可参考下述模板
---
# RBAC 通用配置模板
# 使用方法:根据您的需求保留需要的部分,删除不需要的部分
# ======================
# 1. 服务账户 (ServiceAccount)
# ======================
apiVersion: v1
kind: ServiceAccount
metadata:
name: <service-account-name> # 修改为您的服务账户名称
namespace: <target-namespace> # 修改为目标命名空间
---
# ======================
# 2. 命名空间范围的权限 (Role + RoleBinding)
# ======================
# 适用场景:授予在特定命名空间内的权限
# Role 定义权限规则
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
namespace: <target-namespace> # 授权生效的命名空间
name: <role-name> # Role 名称
rules:
# 规则 1: 核心API组资源 (Pod, Service, ConfigMap, Secret, PVC等)
- apiGroups: [""] # 空字符串表示核心API组
resources:
- "pods" # 可以操作Pod
- "services" # 可以操作Service
- "configmaps" # 可以操作ConfigMap
- "secrets" # 可以操作Secret
- "persistentvolumeclaims" # 可以操作PVC
verbs:
- "get" # 查看
- "list" # 列表
- "watch" # 监听
- "create" # 创建
- "update" # 更新
- "patch" # 部分更新
- "delete" # 删除
# 规则 2: Apps API组资源 (Deployment, StatefulSet, DaemonSet, ReplicaSet)
- apiGroups: ["apps"]
resources:
- "deployments"
- "statefulsets"
- "daemonsets"
- "replicasets"
verbs: ["get", "list", "watch", "create", "update", "patch", "delete"]
---
# RoleBinding 将Role绑定到服务账户
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: <rolebinding-name> # RoleBinding 名称
namespace: <target-namespace> # 必须与Role在同一命名空间
subjects:
# 绑定到服务账户
- kind: ServiceAccount
name: <service-account-name> # 修改为服务账户名称
namespace: <service-account-namespace> # 服务账户所在命名空间
# 也可以绑定到用户或组
#- kind: User
# name: <username> # 用户名
# apiGroup: rbac.authorization.k8s.io
#- kind: Group
# name: <groupname> # 组名
# apiGroup: rbac.authorization.k8s.io
roleRef:
kind: Role
name: <role-name> # 引用的Role名称
apiGroup: rbac.authorization.k8s.io
---
# ======================
# 3. 集群范围的权限 (ClusterRole + ClusterRoleBinding)
# ======================
# 适用场景:授予跨所有命名空间的权限
# ClusterRole 定义集群范围的权限规则
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: <clusterrole-name> # ClusterRole 名称
rules:
# 规则 1: 集群范围资源 (Nodes, PersistentVolumes, Namespaces等)
- apiGroups: [""]
resources:
- "nodes" # 访问节点
- "persistentvolumes" # 访问PV
- "namespaces" # 访问命名空间
verbs: ["get", "list", "watch"]
# 规则 4: 访问所有命名空间中的特定资源
- apiGroups: [""]
resources:
- "pods"
- "services"
verbs: ["get", "list", "watch"]
# 不需要指定namespace,因为ClusterRole是集群范围的
---
# ClusterRoleBinding 将ClusterRole绑定到主体
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: <clusterrolebinding-name> # ClusterRoleBinding 名称
subjects:
# 绑定到服务账户 (需要指定命名空间)
- kind: ServiceAccount
name: <service-account-name>
namespace: <service-account-namespace>
# 也可以绑定到用户或组
#- kind: User
# name: <username>
# apiGroup: rbac.authorization.k8s.io
#- kind: Group
# name: <groupname>
# apiGroup: rbac.authorization.k8s.io
roleRef:
kind: ClusterRole
name: <clusterrole-name> # 引用的ClusterRole名称
apiGroup: rbac.authorization.k8s.io
---
# ======================
# 4. 使用现有集群角色
# ======================
# Kubernetes提供了一些预定义的ClusterRole,可以直接使用
# 示例:将view角色绑定到服务账户 (只读权限)
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: read-only-binding
namespace: <target-namespace>
subjects:
- kind: ServiceAccount
name: <service-account-name>
namespace: <service-account-namespace>
roleRef:
kind: ClusterRole # 注意这里引用的是ClusterRole
name: view # 使用预定义的view角色
apiGroup: rbac.authorization.k8s.io
# 其他有用的预定义ClusterRole:
# - "view": 只读权限,可以查看大多数资源
# - "edit": 编辑权限,可以修改大多数资源,但不能查看或修改RBAC权限
# - "admin": 管理权限,可以管理命名空间内所有资源,包括RBAC权限
# - "cluster-admin": 超级用户权限,可以执行任何操作 on any resource案例:
serviceaccount(给pod用)
要求:
创建一个账号:pod-reader 命名空间:default 操作资源:deployment 操作权限:get watch list
---
apiVersion: v1
kind: Namespace
metadata:
labels:
kubernetes.io/metadata.name: serviceaccount
name: serviceaccount
spec:
finalizers:
- kubernetes
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin-user-serviceaccount
namespace: serviceaccount
---
# Role 定义权限规则
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
namespace: serviceaccount
name: admin-user-serviceaccount-role
rules:
- apiGroups: [""] # 空字符串表示核心API组
resources:
- "pods" # 可以操作Pod
verbs:
- "get" # 查看
- "list" # 列表
- "watch" # 监听
- apiGroups: ["/apis/apps/v1"]
resources:
- "deployments"
- "statefulsets"
verbs: ["get", "list", "watch"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: admin-user-serviceaccount-rolebinding
namespace: serviceaccount
subjects:
- kind: ServiceAccount
name: admin-user-serviceaccount
namespace: <eviceaccount
roleRef:
kind: Role
name: admin-user-serviceaccount-role
apiGroup: rbac.authorization.k8s.io
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin-user-serviceaccount
namespace: serviceaccount
---
# Role 定义权限规则
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
namespace: serviceaccount # 修正拼写
name: admin-user-serviceaccount-role
rules:
- apiGroups: [""] # 空字符串表示核心API组
resources:
- "pods" # 可以操作Pod
verbs:
- "get" # 查看
- "list" # 列表
- "watch" # 监听
- apiGroups: ["apps"]
resources:
- "deployments"
- "statefulsets"
verbs: ["get", "list", "watch"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: admin-user-serviceaccount-rolebinding
namespace: serviceaccount
subjects:
- kind: ServiceAccount
name: admin-user-serviceaccount
namespace: serviceaccount
roleRef:
kind: Role
name: admin-user-serviceaccount-role
apiGroup: rbac.authorization.k8s.io
root@k8s-master:~/k8s/RBAC# kubectl -n serviceaccount create token admin-user
admin-user admin-user-serviceaccount
root@k8s-master:~/k8s/RBAC# kubectl -n serviceaccount create token admin-user-serviceaccount
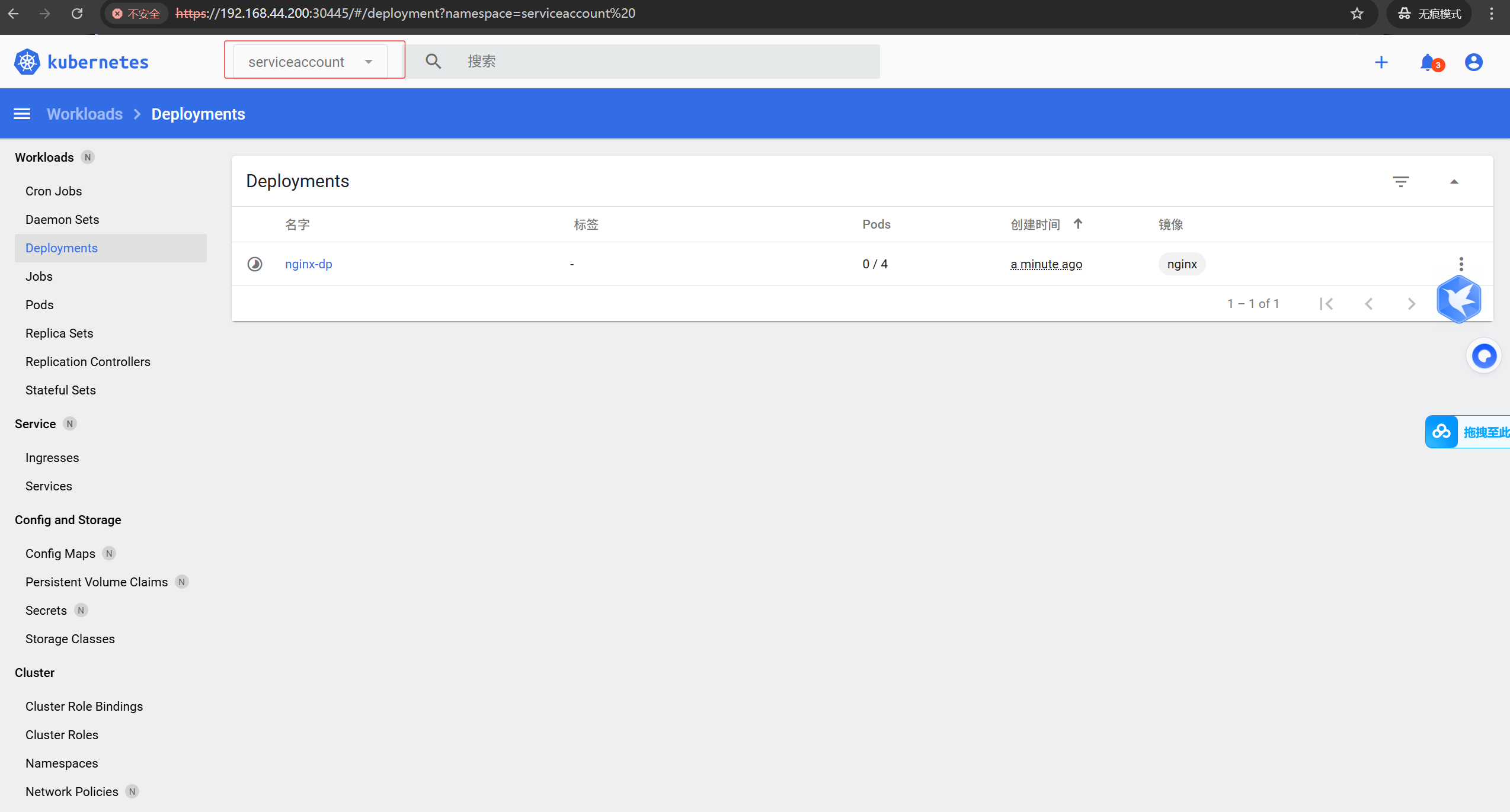
eyJhbGciOiJSUzI1NiIsImtpZCI6IkE1ek9BbTJTaTBtbVNJaUx0TWFZX2RlX05YZDlYRXhxcW9ZNV9ZVEhwVmMifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiXSwiZXhwIjoxNzc0MDg5OTg0LCJpYXQiOjE3NzQwODYzODQsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwianRpIjoiNzk5ZGRlNTUtODU1Ny00YmY5LWE3OWEtNjAzZTQxN2M1NmQ5Iiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJzZXJ2aWNlYWNjb3VudCIsInNlcnZpY2VhY2NvdW50Ijp7Im5hbWUiOiJhZG1pbi11c2VyLXNlcnZpY2VhY2NvdW50IiwidWlkIjoiYjljYjZmMmQtNWU0MC00YjY3LWJlODEtYTdjNzkyNGM5ZGIxIn19LCJuYmYiOjE3NzQwODYzODQsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDpzZXJ2aWNlYWNjb3VudDphZG1pbi11c2VyLXNlcnZpY2VhY2NvdW50In0.JTTAqocF2yTasQ0FTd_7Cv9ULycC6IhL7ljzKkwSt-mtGxgbbTuUb01R2VAoJRnymfgDGHHxKObYdFKaQVIGmEUObBTDx3v-UX6uznlRw8hRETG6aHFixWRxfvkw9xZiQEQZmqqqSIt4AlP08BWJrfgBBXX5vNepql4mtTEnQghAZ7wYs7FhoR4T2cWvkGtXGOVWugcxbeV8D_dJGwHObXT7zr2LE-Ahf7-Px8K7Ygnj77q1wr-OKu5nKqSsfWiP0MDWqmFWnh6yaistQguG-gqZ0Tubyq0VBTNO1QOZHHT6D5CaCjsUc365Zt4_oWo5X-Mg_ejNotxPCtHWKUMTdQ此时浏览器登录dashboard如果只能查看serviceaccount当中的pod,dp,ss的数据即成功!!!
useraccount(给人用)
命名空间:wordpress 资源对象:service,deployment 操作权限:查看,创建,更新,不能删
#第1步:创建key
openssl genrsa -out luffy.key 2048
#第2步:使用key生成证书
openssl req -new -key luffy.key -out luffy.csr -subj "/CN=luffy/O=luffy"
#第3步:使用k8s自己的ca.crt和ca.key签发我们生成luffy.crt有效期300天
openssl x509 -req -in luffy.csr -CA /etc/kubernetes/pki/ca.crt -CAkey /etc/kubernetes/pki/ca.key -CAcreateserial -out luffy.crt -days 300
#第4步:生成集群配置
kubectl config set-cluster kubernetes --server=https://10.0.0.11:6443 --certificate-authority=/etc/kubernetes/pki/ca.crt --embed-certs=true --kubeconfig=luffy.config
#第5步:生成运行环境
kubectl config set-context luffy-context --cluster=kubernetes --user=luffy --namespace=wordpress --kubeconfig=luffy.config
、
#第6步:设置配置文件里的运行环境
kubectl config set current-context luffy-context --kubeconfig luffy.config
#第7步:指定用户的证书
kubectl config set-credentials luffy --client-certificate=luffy.crt --client-key=luffy.key --embed-certs=true --kubeconfig=luffy.config
#第8步:编写yaml配置文件
cat > user-role.yaml << EOF
# 创建 Role
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
namespace: wordpress
name: user-sa-role
rules:
- apiGroups: [""]
resources: ["events", "pods", "services"]
verbs: ["get", "watch", "list", "create", "update"]
- apiGroups: [""]
resources: ["pods/log"]
verbs: ["get"]
- apiGroups: [""]
resources: ["services/proxy"]
verbs: ["get", "create", "update"]
- apiGroups: ["apps"]
resources: ["replicasets", "deployments"]
verbs: ["get", "watch", "list", "create", "update"]
- apiGroups: ["apps"]
resources: ["deployments/scale"]
verbs: ["get", "update"]
---
# 创建 RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: user-sa-rolebinding
namespace: wordpress
subjects:
- kind: User
name: luffy
namespace: wordpress
roleRef:
kind: Role
name: user-sa-role
apiGroup: rbac.authorization.k8s.io
EOF
#将luffy.config文件发送到对应的客户端/root/.kube下更改名称为config
scp luffy.config root@192.168.200.211:/root/.kube/config
即可正常使用