0x01 工具介绍
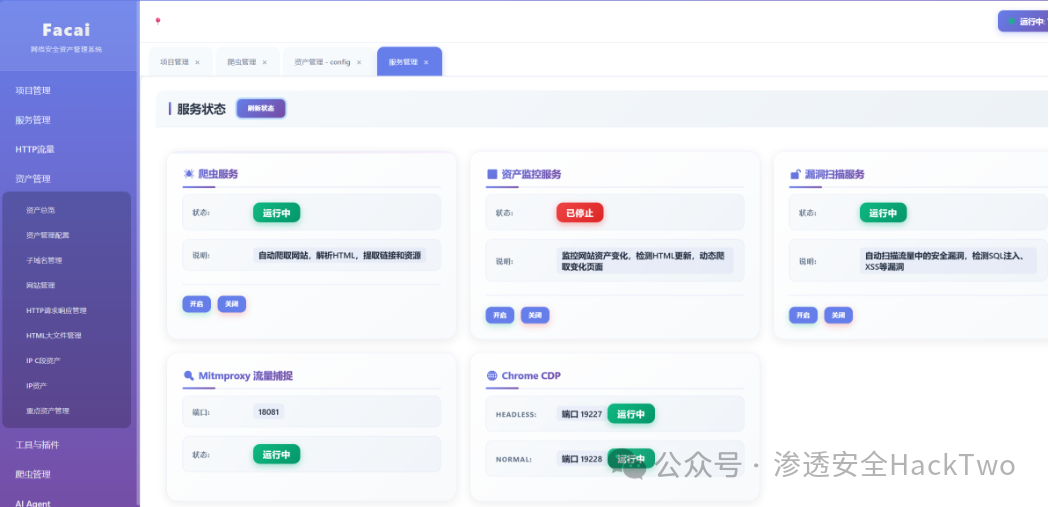
Facai 是一款全新 AI 赋能的轻量化网安平台,基于 Mitmproxy 实现全量 HTTP 流量捕获与深度分析,集成资产测绘、被动爬虫与无害化漏洞检测能力。可自动抓取浏览器及应用流量,智能分离站点、子域名与请求数据,完成资产梳理与漏洞初筛(XSS/SQL/SSRF/RCE)。内置端口扫描、请求重放、编码解码等实用工具,支持 DNSlog 盲打与自定义 payload,适配红队日常与自动化运营场景。系统低依赖、易部署,全程可视化操作,让安全测试更高效便捷。
发财网安工具,都发财,谁用谁发财,你只负责点点点,其他都交给它。
注意:现在只对常读和星标的才展示大图推送,建议大家把渗透安全HackTwo "设为 星标**⭐️****** "否 则可能就看不到了啦!
下载地址在末尾 #渗透安全HackTwo
0x02 功能介绍
✨主要功能
如今已然迈入 AI 时代,传统安全的运作模式早已跟不上发展节奏,这已是行业现状。正如过往内容所表达的核心观点:当下数字化环境里,核心服务对象只有两类 ------ 人类与 AI。
因此在工具设计层面,必须兼顾双向适配,做到人机可读、人机通用。
而 JSON 作为通用轻量化数据格式,兼容性极强,既能被人类快速阅读理解,也完美适配 AI-Agent 自动化调度标准。
本工具便以此为核心设计理念,全程围绕 HTTP 请求处理,统一采用 JSON 标准化格式进行数据交互与流转。
{
"url": "https://a.molun.com/auth/getAuthCodeInfoByCode",
"headers": {
"accept": "application/json, text/plain, */*",
"content-type": "application/x-www-form-urlencoded",
"user-agent": "Mozilla/5.0...",
"cookie": "auth_sid=20000"
},
"method": "POST",
"body": "code=1&client_id=65407",
"time": "2025-11-14 17:20:26",
"website": "http://a.molun.com/",
"status": 0,
"scaner_status":0,
"source": 0 // 0=流量捕捉, 1=url生成
}平台以HTTP 请求处理为核心标准,通过抓取全网流量数据,自动解析拆分站点、子域名等关键资产;同步完成子域名 DNS 解析、请求响应抓取,深度采集 HTML、JS、接口报文等各类资源数据,实现全维度业务信息沉淀与结构化梳理。

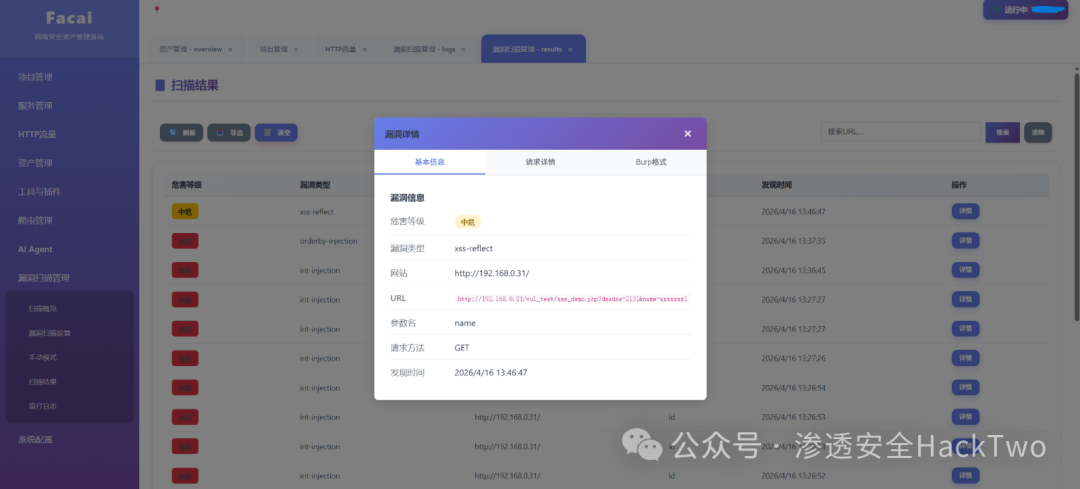
支持对http请求进行处理分离,并且处理读取html,还会对http进行漏洞扫描,并且扫描是无害化,不打任何payload,虽然有不少误报,但将就能用。
-
资产管理工具
-
被动漏洞扫描器
0x03 更新介绍
Full Changelog0x04 使用介绍
📦基础使用流程
安装依赖
pip install -r requirements.txt配置文件config.json
{
"flask_port":5001,
"chrome_path": "C:\\Program Files\\Google\\Chrome\\Application\\chrome.exe",
"burp_path": "D:\\hack_tools\\burp\\",
"chrome_cdp_port": 19227,
"chrome_spider_cdp_port": 19228,
"mitmproxy_port": 18081,
"burp_port":8080,
"mongodb": {
"ip": "127.0.0.1",
"port": 27017,
"dbname": "facai",
"username": "",
"password": ""
},
"AI_model":{
"model_name":"",
"API":"",
"API_KEY": ""
}
}这里的burp_path有个前提,我burp是破解版的,如果你不是,你可以不用填写,burp_path、burp_port。
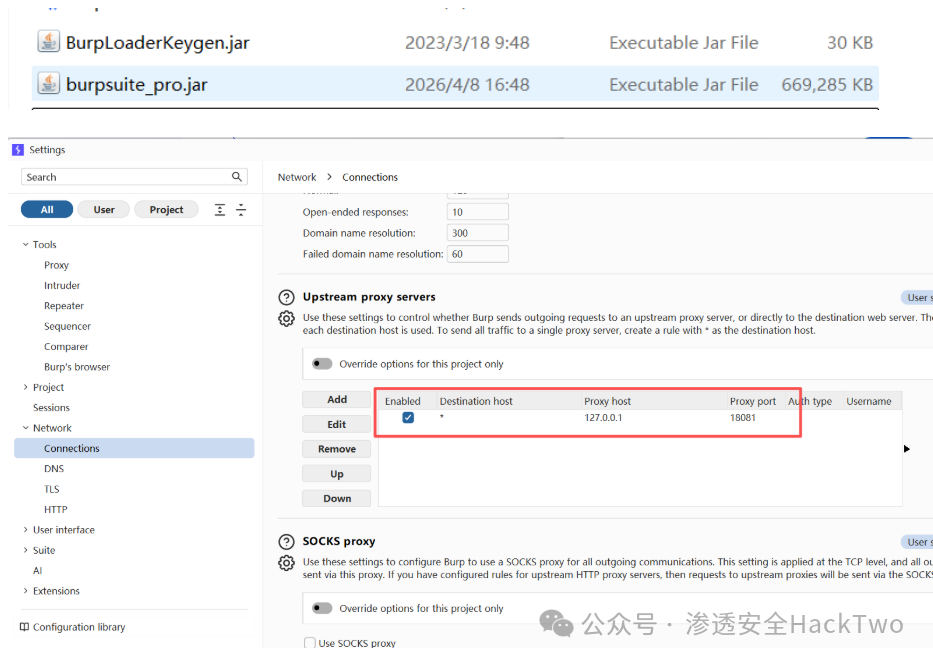
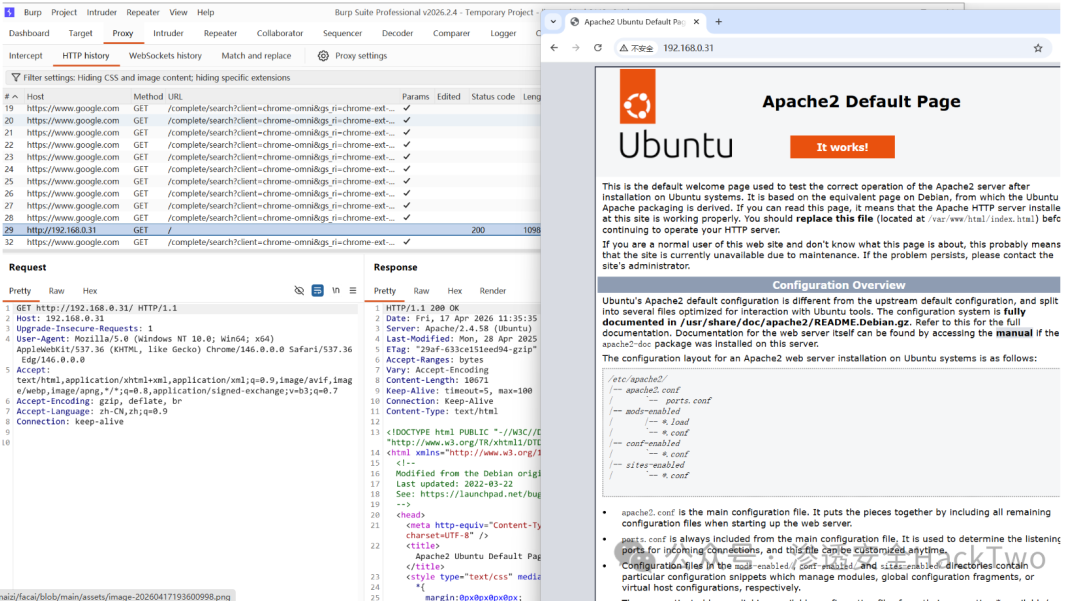
如图自行打开,然后设置burp转发端口,指向为mitmproxy_port端口。
启动
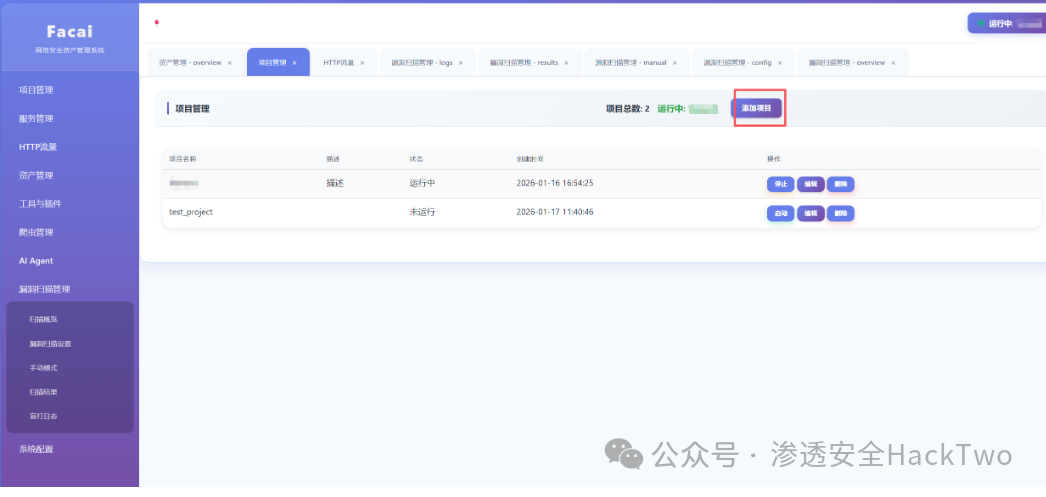
start.bat添加项目
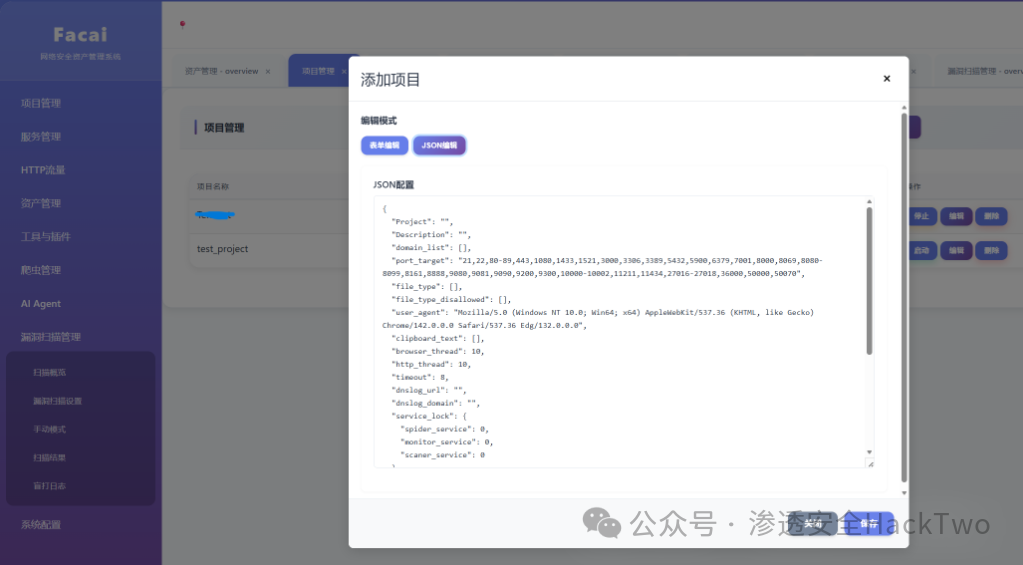
{
"Project": "test",
"Project_Name": "molun",
"Description": "描述",
"domain_list": [
"lulun.com",
"molun.com"
],
"port_target": "21,22,80-89,443,1080,1433,1521,3000,3306,3389,5432,5900,6379,7001,8000,8069,8080-8099,8161,8888,9080,9081,9090,9200,9300,10000-10002,11211,11434,27016-27018,36000,50000,50070",
"clipboard_text": [
"'\"","javascript:alert``//",""
],
"dnslog_domain":"{hash}.www.dnslog.com",
"dnslog_url":"http://www.dnslog.com/{hash}",
"browser_thread": 10,
"http_thread": 10,
"user_agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/146.0.0.0 Safari/537.36 Edg/146.0.0.0",
"timeout": 8,
"service_lock": {
"spider_service": 1,
"monitor_service": 0,
"scaner_service": 1
},
"dns_server": [
[
"119.29.29.29",
"119.28.28.28"
],
[
"180.76.76.76",
"180.76.76.76"
],
[
"180.184.1.1",
"180.184.2.2"
],
[
"114.114.114.114",
"114.114.115.115"
],
[
"223.5.5.5",
"223.6.6.6"
]
],
"file_type": [".php", ".asp", ".aspx", ".asa", ".assh", ".jsp", ".jspx", ".do", ".action", ".py", ".cgi", ".htm", ".html", ".fcg", ".fcgi", ".xhtml", ".shtml", ".shtm", ".rhtml", ".rhtm", ".jhtml", ".jhtm", ".pl", ".php3", ".php4", ".php5", ".phtml", ".pht", ".phar", ".phpt", ".phs", ".ph7"],
"file_type_disallowed": [".3g2", ".3gp", ".7z", ".aac", ".abw", ".aif", ".aifc", ".aiff", ".arc", ".au", ".avi", ".azw", ".bin", ".bmp", ".bz", ".bz2", ".cmx", ".cod", ".csh", ".css", ".csv", ".doc", ".docx", ".eot", ".epub", ".gif", ".gz", ".ico", ".ics", ".ief", ".jar", ".jfif", ".jpe", ".jpeg", ".jpg", ".m3u", ".mid", ".midi", ".mjs", ".mp2", ".mp3", ".mp4", ".mpa", ".mpe", ".mpeg", ".mpg", ".mpkg", ".mpp", ".mpv2", ".odp", ".ods", ".odt", ".oga", ".ogv", ".ogx", ".otf", ".pbm", ".pdf", ".pgm", ".png", ".pnm", ".ppm", ".ppt", ".pptx", ".ra", ".ram", ".rar", ".ras", ".rgb", ".rmi", ".rtf", ".snd", ".svg", ".swf", ".tar", ".tif", ".tiff", ".ttf", ".vsd", ".wav", ".weba", ".webm", ".webp", ".woff", ".woff2", ".xbm", ".xls", ".xlsx", ".xpm", ".xul", ".xwd", ".zip", ".exe", ".apk", ".msi", ".dmg", ".rpm", ".deb", ".pkg", ".ios", ".iso", ".txt", ".m3u8", ".tgz", ".md", ".xml", ".dll"],
"personal_info":{"id_card_number":"110105199503151234","passport_number":"E12345678","marital_status":"未婚","account":"zhangsan_2024","password":"P@ssw0rd!2024","name":"张三","nickname":"三儿","gender":"男","age":28,"birthday":"1995-03-15","signature":"热爱编程与旅行","email":"zhangsan@example.com","phone":"13800138000","landline":"010-12345678","address":"北京市朝阳区建国路88号SOHO现代城A座1001室","postal_code":"100022","website_url":"https://zhangsan.github.io","emergency_contact":{"name":"张建国","relationship":"父亲","phone":"13900139000"},"school":"北京大学","education_level":"硕士","major":"计算机科学","graduation_time":"2019-07-01","company":"膜沦科技有限公司","occupation":"软件工程师","position":"高级开发工程师","industry":"互联网","work_experience_years":5,"country":"中国","province":"北京市","city":"北京市","district":"朝阳区","hobbies":["编程","旅行","摄影"],"languages":["中文","英语"],"avatar":"https://example.com/avatars/zhangsan.jpg","social_media":{"wechat":"zhangsan_2024","qq":"123456789","weibo":"@张三的微博","linkedin":"linkedin.com/in/zhangsan"},"agreed_to_terms":true,"subscription_preferences":{"receive_marketing_emails":false,"receive_sms_notifications":true}}
"status_code": 1,
"created_at": "2026-01-16 16:54:25",
"updated_at": "2026-02-25 16:21:12"
}-
Project为项目标识,必须纯英文。
-
domain_list为目标范围,必须域名。
-
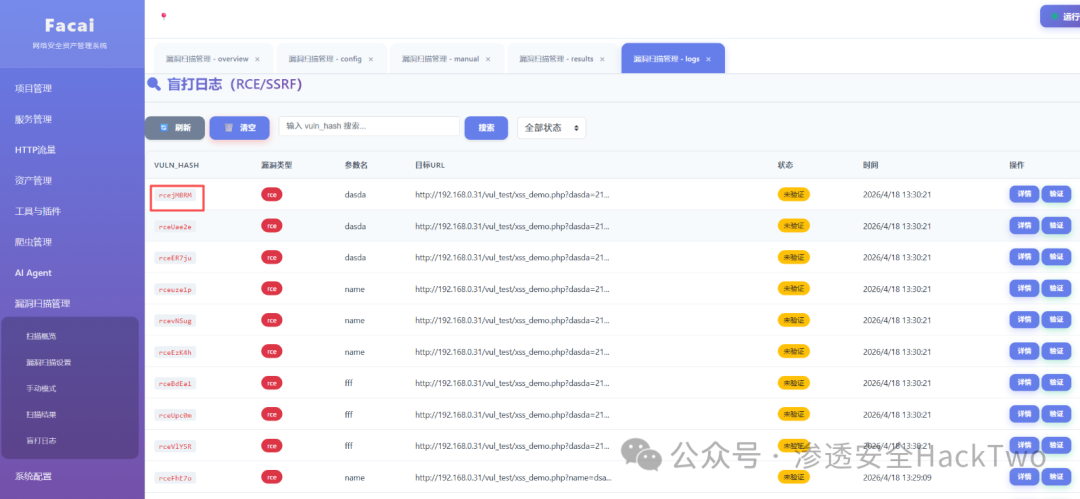
dnslog_domain、dnslog_url为rce与ssrf盲打的测试url,你可以自行填写,hash是标识符,方便到时候查询是哪个请求打的。
-
personal_info自行更改,之后爬虫会用到。
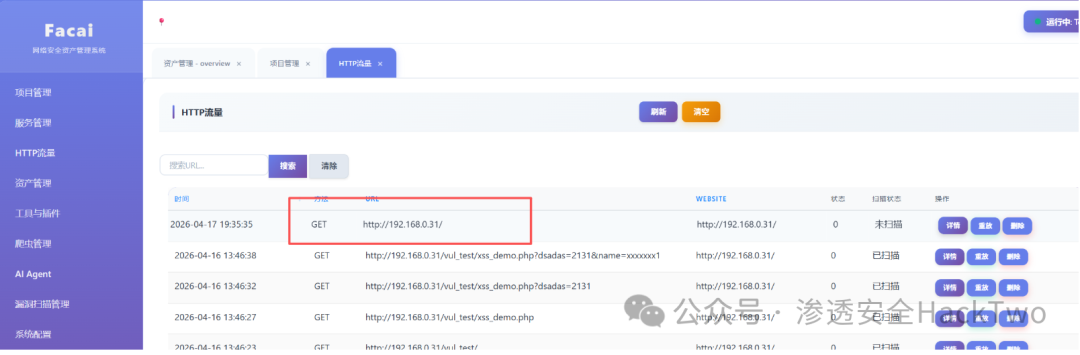
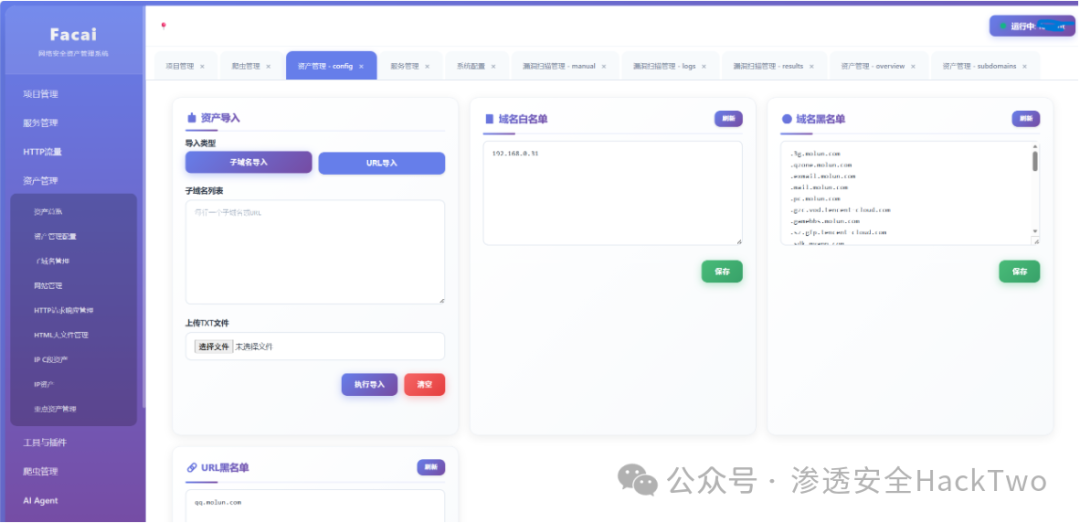
启动项目后则可用,因为流量表里没数据,得开浏览器代理指向代理端口往里面写数据,或者在资产管理、资产管理配置导入子域名或者url,写初始启动数据。
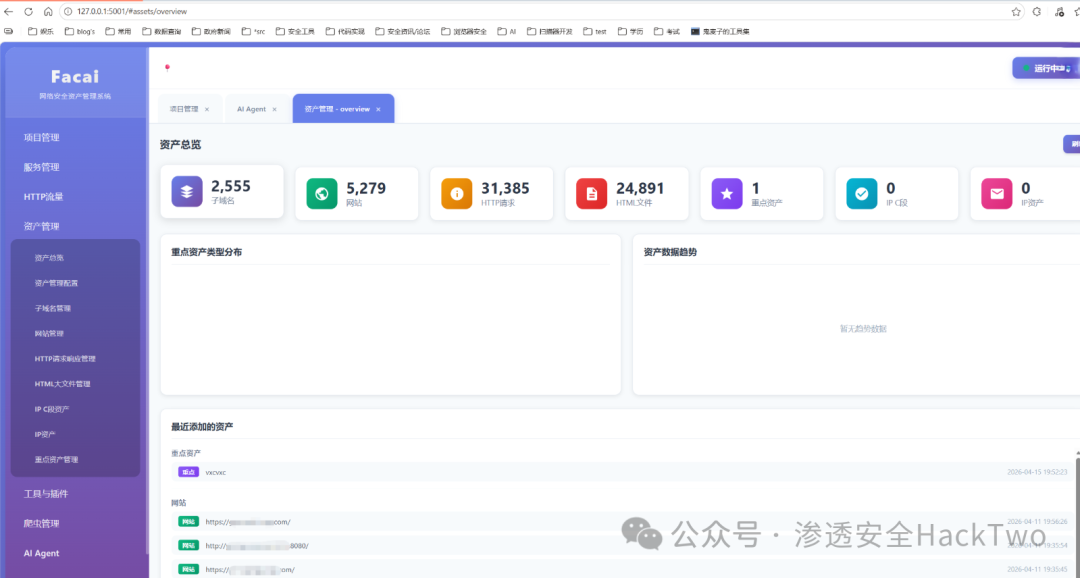
资产管理功能介绍
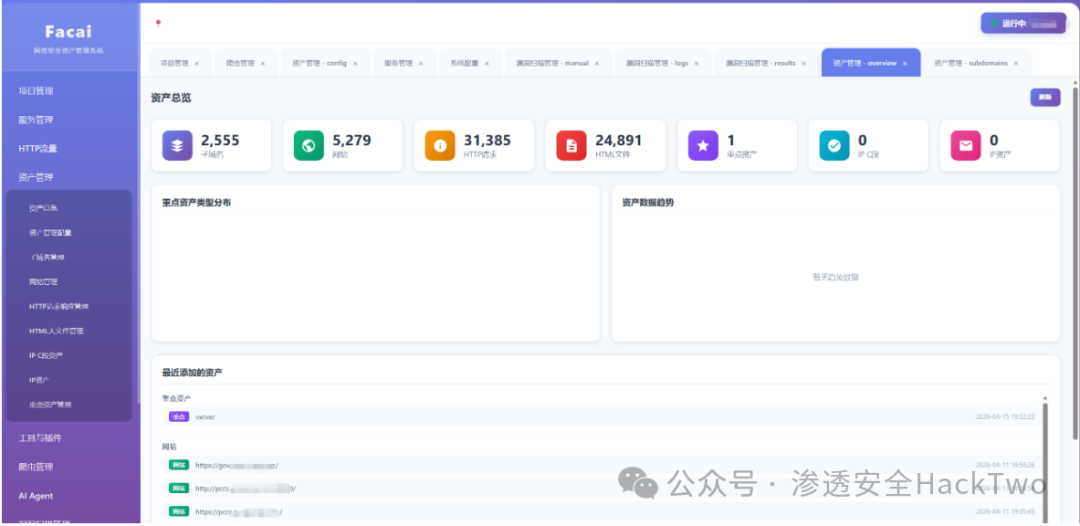
也就是子域名、网站、http请求、html文件、重点资产这些比较常规的显示。
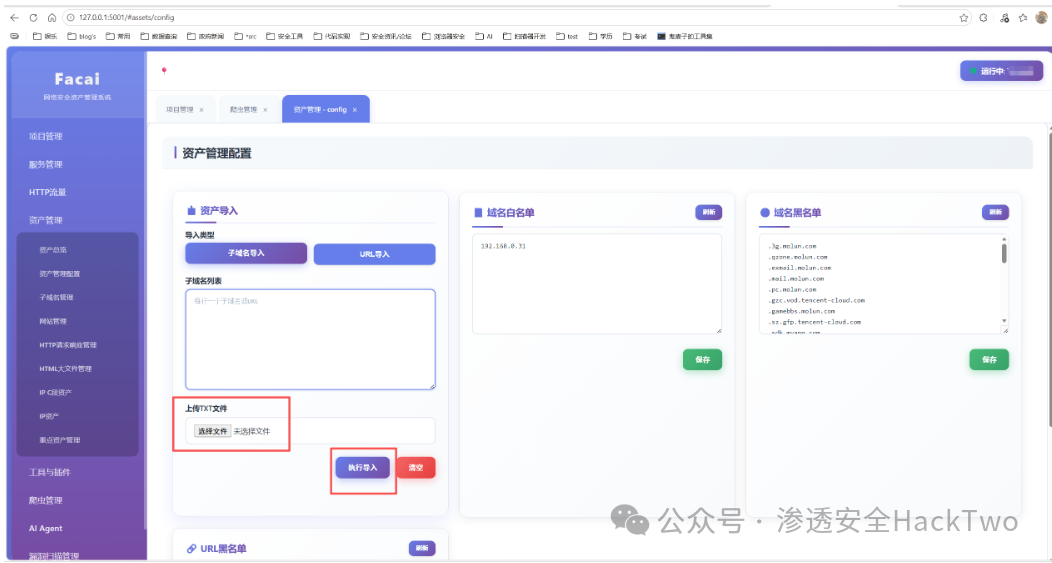
资产管理配置
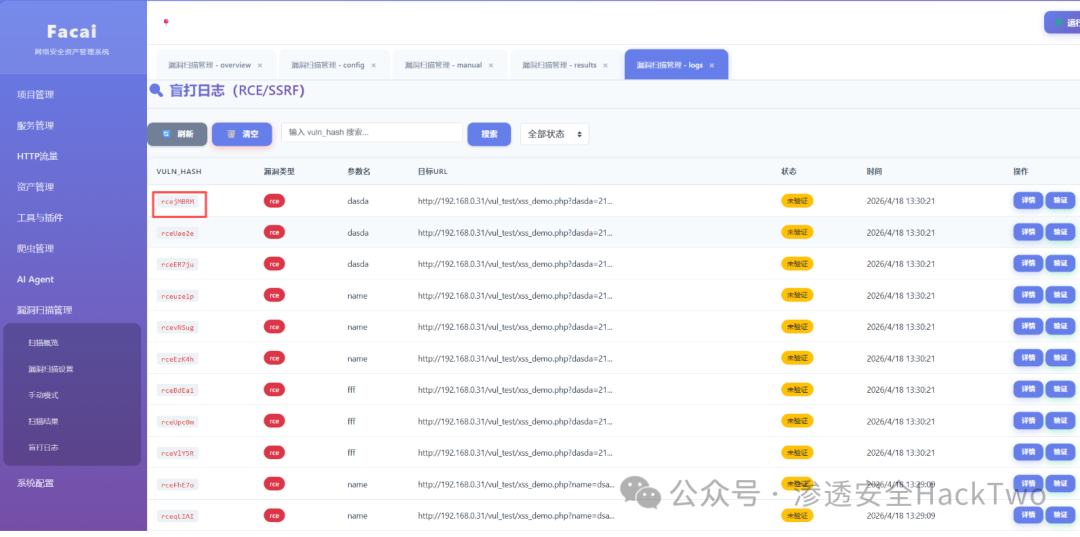
盲打日志
下载
⬇️回复20260428获取下载⬇️