文章目录
- 一、Bridge网络
-
- [1.1 概述](#1.1 概述)
- [1.2 Docker实现Bridge网络的方式](#1.2 Docker实现Bridge网络的方式)
- [1.3 内置bridge网络和自定义一bridge网络的区别](#1.3 内置bridge网络和自定义一bridge网络的区别)
- 二、Host网络
-
- [2.1 概述](#2.1 概述)
- [2.2 操作演示](#2.2 操作演示)
- [2.3 host网络的优势](#2.3 host网络的优势)
- 三、Container网络
-
- [3.1 概述](#3.1 概述)
- [3.2 操纵演示](#3.2 操纵演示)
- 四、None网络
-
- [4.1 概述](#4.1 概述)
- [4.2 操作演示](#4.2 操作演示)
- [4.3 使用场景](#4.3 使用场景)
一、Bridge网络
1.1 概述
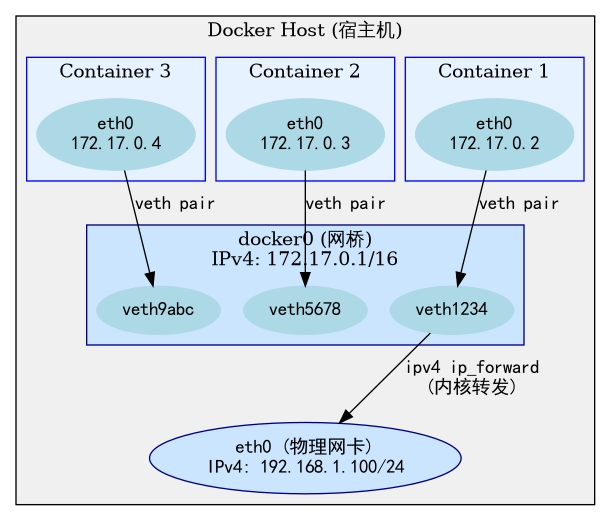
一个容器可以加入多个Bridge网络,同一个Bridge网络中,容器之间可以相互通信。也可通过docker和linux提供的虚拟技术(docker0+veth pair),与服务器外网通信;
docker中内置了一个默认的Bridge网络,启动容器,如果不设置网络连接,那么该容器默认加入内置bridge网络。也可以设置自定义的Bridge网络;
1.2 Docker实现Bridge网络的方式
安装docker,它会自动配置一个docker0网桥(用于内置Bridge网络):
bash
ip a
#本地回环接口
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
# 宿主机物理网卡
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:16:3e:10:f7:cb brd ff:ff:ff:ff:ff:ff
altname enp0s3
altname ens3
inet 172.16.42.42/18 metric 100 brd 172.16.63.255 scope global dynamic eth0
valid_lft 1891801668sec preferred_lft 1891801668sec
inet6 fe80::216:3eff:fe10:f7cb/64 scope link
valid_lft forever preferred_lft forever
# 虚拟网卡,用于容器的路由
4: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default
link/ether be:09:d4:9b:1f:1b brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::bc09:d4ff:fe9b:1f1b/64 scope link
valid_lft forever preferred_lft forever此外我们每创建一个Bridge网络,就会生成一个对应的网桥(linux看来,他是一个网卡):
bash
docker network create --driver bridge net1
4c154a2e61ab27756ba506d3ac36e3b05a43df84cdf3c95a5f4d3084ff8587a4
ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:16:3e:10:f7:cb brd ff:ff:ff:ff:ff:ff
altname enp0s3
altname ens3
inet 172.16.42.42/18 metric 100 brd 172.16.63.255 scope global dynamic eth0
valid_lft 1891801535sec preferred_lft 1891801535sec
inet6 fe80::216:3eff:fe10:f7cb/64 scope link
valid_lft forever preferred_lft forever
4: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default
link/ether be:09:d4:9b:1f:1b brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::bc09:d4ff:fe9b:1f1b/64 scope link
valid_lft forever preferred_lft forever
# 新增的虚拟网卡(本质是虚拟交换机)
478: br-4c154a2e61ab: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default
link/ether da:a2:52:16:4d:02 brd ff:ff:ff:ff:ff:ff
inet 172.18.0.1/16 brd 172.18.255.255 scope global br-4c154a2e61ab
valid_lft forever preferred_lft foreverDocker 容器通过 docker0 网桥通信示意图:
1.3 内置bridge网络和自定义一bridge网络的区别
自定义网络:
1、无法进行容器DNS解析
bash
docker run -itd --name c1 busybox:latest
2d39a5f6cc70af3e941f7001a76c88415bae85e905de520e51c5b12819252753
docker run -itd --name c2 busybox:latest
7c6be80a37b59f85f05ea310ea1a84d19bfda86f841752af3ab832438f21dc00
docker network ls
NETWORK ID NAME DRIVER SCOPE
4961851d7f3b bridge bridge local
a6be76bcbdde host host local
4c154a2e61ab net1 bridge local
f446ebf2ce52 none null local
docker network inspect bridge | awk '/"Containers": {/,/}/'
"Containers": {
"2d39a5f6cc70af3e941f7001a76c88415bae85e905de520e51c5b12819252753": {
"Name": "c1",
"EndpointID": "ac2b21ac7680c1459c090cf9f4c6b485d29f6ae2ff3aee86ae1ee0989b48b51c",
"MacAddress": "da:11:98:94:84:a4",
"IPv4Address": "172.17.0.2/16",
"IPv6Address": ""
},
root@iZ2ze8ve39i30yl0dhbqneZ:~# docker network inspect bridge | less -SN
root@iZ2ze8ve39i30yl0dhbqneZ:~# docker network inspect bridge | awk '/"Containers": {/,/}/'
"Containers": {
"2d39a5f6cc70af3e941f7001a76c88415bae85e905de520e51c5b12819252753": {
"Name": "c1",
"EndpointID": "ac2b21ac7680c1459c090cf9f4c6b485d29f6ae2ff3aee86ae1ee0989b48b51c",
"MacAddress": "da:11:98:94:84:a4",
"IPv4Address": "172.17.0.2/16",
"IPv6Address": ""
},
docker exec -it c1 sh
/ # ping c2
ping: bad address 'c2' #进入容器后无法通过容器名连接2、无法控制网段和网关
bash
# 对于内置Bridge网络,通过docker0路由,默认网关/网段只能是172.17.0.1/16,不可更改
ip a | grep docker0
4: docker0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker03、隔离性相对较差,因为所有未指定网络的容器都会加入内置Bridge网络
自定义Bridge网络:
1、可以使用容器域名解析
2、可以自定义网关、网段
3、隔离性较强
bash
docker network create --driver bridge --subnet 182.168.0.0/16 --gateway 182.168.0.1 my_net
docker network connect my_net c1
docker network connect my_net c2
docker exec -it c1 sh
/ # ping c2
PING c2 (182.168.0.3): 56 data bytes
64 bytes from 182.168.0.3: seq=0 ttl=64 time=0.139 ms
64 bytes from 182.168.0.3: seq=1 ttl=64 time=0.107 ms
...
^C
/ # exit
docker network disconnect my_net c1
docker exec -it c1 sh
/ # ping c2
ping: bad address 'c2'二、Host网络
2.1 概述
Docker 容器运行默认都会分配独立的 Network Namespace 隔离子系统, 但是如果基于 host 网络模式,容器将不会获得一个独立的 Network Namespace,而是和宿主机共用同一个 Network Namespace,容器将不会虚拟出自己的网卡,IP 等,而是直接使用宿主机的 IP 和端口
2.2 操作演示
- 启动c1(用内置Bridge网络)和c2容器(用host网络)
- 分别查看两个容器的网络配置
bash
docker run -itd --name c1 busybox:latest
0ae5db106d38d0a05eb3d0f64fbba3d60712f50843477448d3db1d5694588a14
docker run -itd --name c2 --network=host busybox:latest
6790ab1b071719d94f4da867e60bb5afdf741d8e0087efc6ca6602aacc434931
docker exec c1 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0@if486: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether 22:b4:cf:d9:a6:f6 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
docker exec c2 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel qlen 1000
link/ether 00:16:3e:10:f7:cb brd ff:ff:ff:ff:ff:ff
inet 172.16.42.42/18 brd 172.16.63.255 scope global dynamic eth0
valid_lft 1891742123sec preferred_lft 1891742123sec
inet6 fe80::216:3eff:fe10:f7cb/64 scope link
valid_lft forever preferred_lft forever
4: docker0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue
link/ether be:09:d4:9b:1f:1b brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::bc09:d4ff:fe9b:1f1b/64 scope link
valid_lft forever preferred_lft forever
481: br-68a1865b8bfb: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue
link/ether 52:fa:1b:5f:df:76 brd ff:ff:ff:ff:ff:ff
inet 182.168.0.1/16 brd 182.168.255.255 scope global br-68a1865b8bfb
valid_lft forever preferred_lft forever
inet6 fe80::50fa:1bff:fe5f:df76/64 scope link
valid_lft forever preferred_lft forever
486: veth525511d@eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master docker0
link/ether ce:a8:7b:9e:42:dc brd ff:ff:ff:ff:ff:ff
inet6 fe80::cca8:7bff:fe9e:42dc/64 scope link
valid_lft forever preferred_lft forever
# c2的网络配置和宿主机是一致的
ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:16:3e:10:f7:cb brd ff:ff:ff:ff:ff:ff
altname enp0s3
altname ens3
inet 172.16.42.42/18 metric 100 brd 172.16.63.255 scope global dynamic eth0
valid_lft 1891741976sec preferred_lft 1891741976sec
inet6 fe80::216:3eff:fe10:f7cb/64 scope link
valid_lft forever preferred_lft forever
4: docker0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether be:09:d4:9b:1f:1b brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::bc09:d4ff:fe9b:1f1b/64 scope link
valid_lft forever preferred_lft forever
481: br-68a1865b8bfb: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default
link/ether 52:fa:1b:5f:df:76 brd ff:ff:ff:ff:ff:ff
inet 182.168.0.1/16 brd 182.168.255.255 scope global br-68a1865b8bfb
valid_lft forever preferred_lft forever
inet6 fe80::50fa:1bff:fe5f:df76/64 scope link
valid_lft forever preferred_lft forever
486: veth525511d@if2: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master docker0 state UP group default
link/ether ce:a8:7b:9e:42:dc brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet6 fe80::cca8:7bff:fe9e:42dc/64 scope link
valid_lft forever preferred_lft forever2.3 host网络的优势
host网络直接和宿主机公用同一套network namespace,省去了bridge网络需要进行虚拟网卡模拟,虚拟网卡路由、NAT转换的步骤 ,因此host网络最大优势是性能会好很多 。
反之,这也是它的缺点所在,由于和宿主机公用同一个局域网,可能出现端口冲突的问题 (容器内设置的端口,自动和宿主机端口绑定)。

三、Container网络
3.1 概述
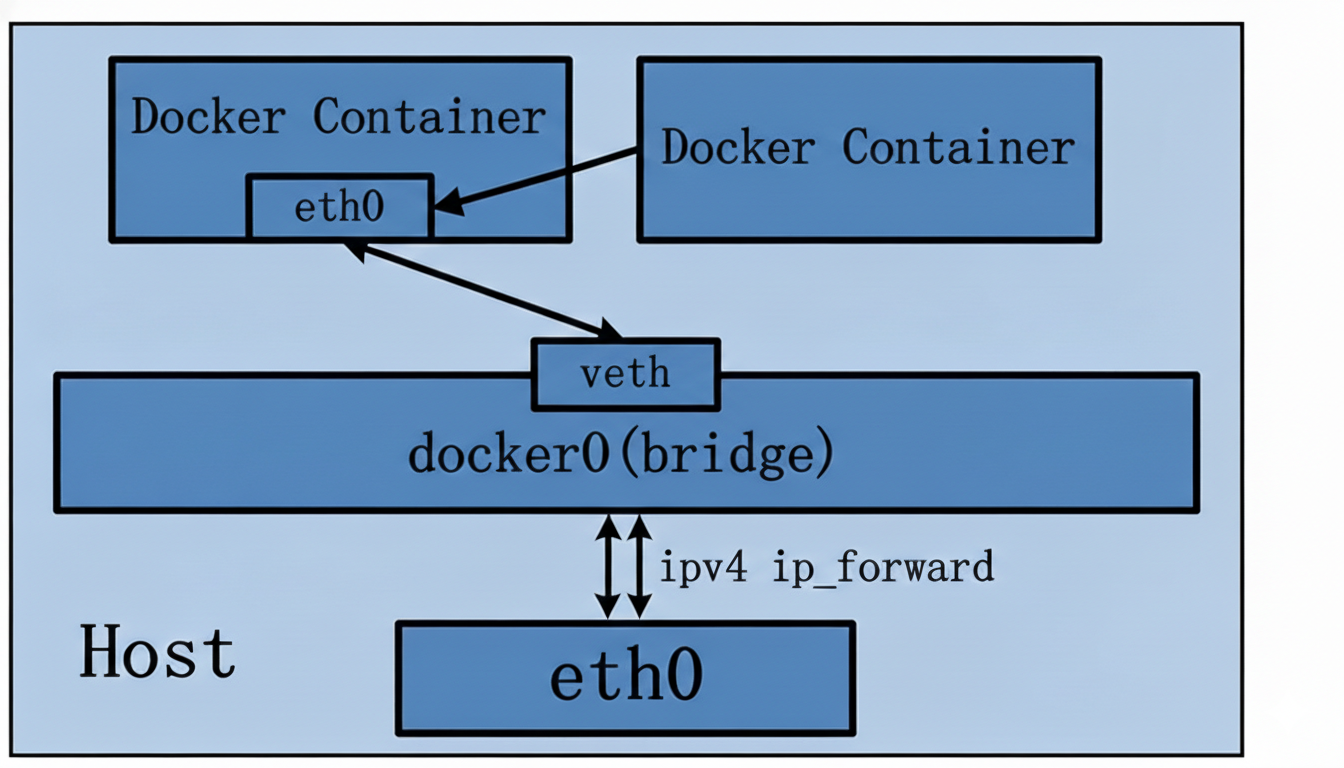
同一个容器网络下,多个容器相互联系,但是它们的网卡共享同一个容器的网卡;它和host网络类似,但是host网络共享宿主机的网络,而Container网络共享指定容器的网络;
工作模式如图:
3.2 操纵演示
- 启动c1容器(加入默认网络)启动c2容器加入c1的容器网络;
- 查看c1 c2的网络;
- 停止c1网络,查看c2网络;
- 重启c1网络查看c2网络;
- 重启c2网络,查看c2网络;
bash
# 1. 启动c1容器(加入默认网络)启动c2容器加入c1的容器网络
docker run -idt --name c1 busybox:latest
a17bd8893477d5e01a13d4aaffbf63c41cd19023c3348a7cdc17ff54c12b467a
docker run -itd --name c2 --network container:c1 busybox:latest
4dd1287d9595ca242704c0392ade3f8213de0abec234583586f9b4022246d505
# 2. 查看c1 c2的网络
docker exec -it c1 sh
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0@if488: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether a6:71:07:f1:ec:cc brd ff:ff:ff:ff:ff:ff
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
/ # exit
docker exec -it c2 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0@if488: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether a6:71:07:f1:ec:cc brd ff:ff:ff:ff:ff:ff
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
# 3. 停止c1网络,查看c2网络
docker stop c1
c1
docker exec -it c2 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
# 4. 重启c1网络查看c2网络
docker restart c1
c1
root@iZ2ze8ve39i30yl0dhbqneZ:~# docker exec -it c2 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
# 5. 重启c2网络,查看c2网络
docker restart c2
c2
docker exec -it c2 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0@if490: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue
link/ether be:5f:65:38:e7:31 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever我们可以发现一旦依赖的网络挂掉,那么该容器(例中的c2,它的网卡消失)的网络就不可用,必须依赖和被依赖的容器都重启才可恢复。
四、None网络
4.1 概述
顾名思义,没有任何网络,容器中只含有lo回环接口,不与任何容器或宿主机进行网络通信
4.2 操作演示
none网络的容器,只有lo接口:
bash
docker run --name c1 --network none -itd busybox:latest
fbc360ef49688553fc8452c38a43103a552b916fe3e6ac78d6e89f1a6674c388
docker exec -it c1 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever4.3 使用场景
- 用于安全级别较高,且不需要网络通信的应用比如随机密码
- 一些第三方应用可能需要docker创建没有网络的容器,网络由第三方应用配置