本案例中所有内容仅供个人学习交流,抓包内容、敏感网址、数据接口均已做脱敏处理,严禁用于商业用途和非法用途,否则由此产生的一切后果均与作者无关。
请求分析
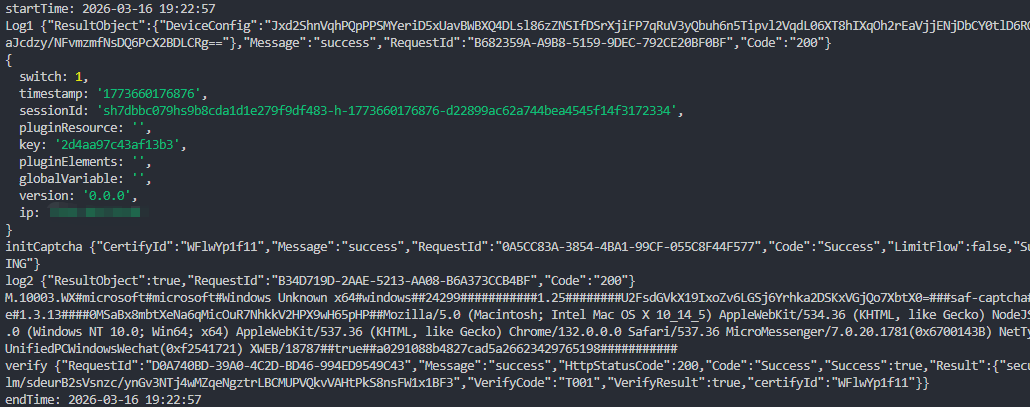
log1
javascript
let reqBody = {
"AccessKeyId": "LTAI5tGjnK9uu9GbT9GQw72p",
"Version": "2020-10-15",
"SignatureMethod": "HMAC-SHA1",
"SignatureVersion": "1.0",
"Format": "JSON",
"Action": "Log1",
"Data": log1Data,//可以固定
"SignatureNonce": Q(),
};
let signature = getSignature(reqBody, "fpOKzILEajkqgSpr9VvU98FwAgIRcX&");
reqBody["Signature"] = signature;InitCaptcha
javascript
let reqBody = {
"AccessKeyId": "LTAI5tSEBwYMwVKAQGpxmvTd",
"SignatureMethod": "HMAC-SHA1",
"SignatureVersion": "1.0",
"Format": "JSON",
"Timestamp": dayjs.utc().format('YYYY-MM-DDTHH:mm:ss[Z]'),
"Version": "2023-03-05",
"Action": "InitCaptchaV2",
"SceneId": SceneId,//固定值
"Language": "cn",
"SignatureNonce": Q(),//随机
};
let signature = getSignature(reqBody, "YSKfst7GaVkXwZYvVihJsKF9r89koz&");
reqBody["Signature"] = signature;log2
javascript
let data = getLog2Data(deviceConfig, fpList);
let reqBody = {
"AccessKeyId": "LTAI5tGjnK9uu9GbT9GQw72p",
"Version": "2020-10-15",
"SignatureMethod": "HMAC-SHA1",
"SignatureVersion": "1.0",
"Format": "JSON",
"Action": "Log2",
"Data": data,//环境数组重点
"SignatureNonce": Q(),
};
let signature = getSignature(reqBody, "fpOKzILEajkqgSpr9VvU98FwAgIRcX&");
reqBody["Signature"] = signature;VerifyCaptcha接口
javascript
let reqBody = {
"AccessKeyId": "LTAI5tSEBwYMwVKAQGpxmvTd",
"SignatureMethod": "HMAC-SHA1",
"SignatureVersion": "1.0",
"Format": "JSON",
"Timestamp": dayjs.utc().format('YYYY-MM-DDTHH:mm:ss[Z]'),
"Version": "2023-03-05",
"Action": "VerifyCaptchaV3",
"SceneId": SceneId,
"CertifyId": certifyId,
"CaptchaVerifyParam": JSON.stringify({
sceneId: SceneId,
certifyId,
deviceToken: getDeviceToken(deviceConfig, certifyId, fpList),
data: verifyData,//轨迹
}),
"SignatureNonce": Q(),
};
let signature = getSignature(reqBody, "YSKfst7GaVkXwZYvVihJsKF9r89koz&");
reqBody["Signature"] = signature;逆向分析
javascript
Log1的响应:ResultObject这个要解密非常关键
环境数组:第25位有个动态值,这个值通过Log1接口返回的ResultObject解密的sessionId和key运算而来
Log2的Data:这是阿里v系列的常用加密流程,整体来说就是b64+AES,和web版本对比有一个区别就是最外层的数组第三个值的key是WEB_AES_SECRET_KEY和ACCESS_SEC运算而来
DeviceToken:这个基本和web一致,也是b64+AES的反复折磨,会看到经典阿里的"daye,raolewoba!"
InitCaptcha:中返回的CertifyId很重要,会参与验证接口和最终提交接口
VerifyCaptcha:这个接口没啥好说的和基本和web一致,会简单一点没有那些绑定文件的值和vmp效果
咨询、沟通、合作
2227669390