一、准备工作:同步系统和网络配置
1. 配置主机名和Hosts解析
操作目的:让Master和Node能通过主机名互相通信。
在Master节点执行
hostnamectl set-hostname master 在Node节点执行
hostnamectl set-hostname node1 两台机器均修改hosts文件(替换实际IP)
vi /etc/hosts
10.10.75.182 master
10.10.75.284 node 注意:IP地址需替换为你的服务器实际IP,使用ifconfig查看 。
2. 关闭防火墙和SELinux
关闭防火墙
systemctl stop firewalld
systemctl disable firewalld 关闭SELinux
# 临时生效
setenforce 0
# 永久关闭
sed -i 's/SELINUX=enforcing/SELINUX=disabled/g' /etc/selinux/config注意:需重启服务器使配置永久生效
3. 禁用Swap分区
# 临时关闭
swapoff -a
# 永久关闭
sed -i '/ swap / s/^\(.*\)$/#\1/g' /etc/fstab
# 验证关闭结果执行 free -m 查看Swap行是否全为0
free -m4. 配置内核参数和IPVS
原理:Linux内核需支持容器网络桥接和流量转发。
# 创建模块加载配置文件
cat > /etc/modules-load.d/k8s.conf << EOF
br_netfilter
ip_vs
ip_vs_rr
ip_vs_sh
nf_conntrack
EOF
# 立即加载所有模块
modprobe --all br_netfilter ip_vs ip_vs_rr ip_vs_sh nf_conntrack
# 验证模块是否加载成功(输出模块名称即表示成功)
lsmod | grep -e br_netfilter -e ip_vs -e nf_conntrack
# 创建 sysctl 配置文件
cat > /etc/sysctl.d/k8s.conf << EOF
net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1
net.ipv4.ip_forward = 1
EOF
sed -i 's/net.ipv4.ip_forward=0/net.ipv4.ip_forward=1/' /etc/sysctl.conf
# 生效配置(无需重启,立即应用)
sysctl --system
# 验证参数是否生效(输出 1 即表示成功)
sysctl net.bridge.bridge-nf-call-ip6tables net.bridge.bridge-nf-call-iptables net.ipv4.ip_forward
lsmod | grep br_netfilter 5. 同步服务器时间
原理:Kubernetes证书依赖时间一致性。
# 安装NTP服务
yum install -y ntp
# 启动并同步时间
systemctl start ntpd
systemctl enable ntpd
# 设置NTP同步时间源
ntpdate time.windows.com 6. 安装K8S运行时containerd
# 安装K8S运行时containerd
yum install containerd
# 查看 containerd 服务状态
systemctl status containerd
# 若状态为 inactive(dead)或 failed,启动服务
systemctl start containerd
# 设置开机自启
systemctl enable containerd
# 再次确认状态(需显示 Active: active (running))
systemctl status containerd
# 初始化配置
containerd config default > /etc/containerd/config.toml
grep -i sandbox /etc/containerd/config.toml
# 将UOS容器镜像仓库修改成阿里云容器镜像仓库
sed -i 's|registry.uniontech.com/uos-app/pause:3.9|registry.aliyuncs.com/google_containers/pause:3.9|' /etc/containerd/config.toml
# 重启 containerd 使配置生效
systemctl restart containerd二、安装Kubernetes组件(kubeadm/kubelet/kubectl)
1. 直接执行命令创建仓库文件
cat > /etc/yum.repos.d/kubernetes.repo << EOF
[kubernetes]
name=Kubernetes
baseurl=https://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64
enabled=1
gpgcheck=0
EOF2. 验证仓库是否创建成功
# 查看仓库文件内容,确认配置正确
cat /etc/yum.repos.d/kubernetes.repo
# 刷新 YUM 缓存,使新仓库生效
yum clean all3.安装 Kubernetes 核心组件
配置完阿里云仓库后,即可安装 Kubernetes 集群依赖的 kubeadm(集群初始化工具)、kubelet(节点代理)、kubectl(命令行工具)
# 安装 v1.28.2 版本
yum install -y kubelet-1.28.2 kubeadm-1.28.2 kubectl-1.28.2
# 冻结版本(防止自动升级)
systemctl enable --now kubelet4.初始化 Kubernetes 控制平面节点
# 提前拉取镜像,避免初始化因为拉取镜像超时造成初始化失败
kubeadm config images pull --kubernetes-version=v1.28.2 --image-repository=registry.aliyuncs.com/google_containers
# 设置 kubelet 开机自启并启动
kubelet 是每个节点(Master/Worker)必须运行的组件,需确保其开机启动
kubeadm init --apiserver-advertise-address=10.10.14.103 --image-repository registry.aliyuncs.com/google_containers --kubernetes-version v1.28.2 --service-cidr=10.96.0.0/12 --pod-network-cidr=192.168.0.0/16
# 设置开机自启
systemctl enable kubelet
# 启动 kubelet(此时可能处于 "activating" 状态,初始化集群后会正常运行)
systemctl start kubelet
# 查看 kubelet 状态(确认无报错)
systemctl status kubelet
# 查看 kubeadm 版本
kubeadm version
# 查看 kubectl 客户端版本
kubectl version --client
# 将cni二进制文件拷贝到/usr/libexec/cni/目录下 原因是kubeadm / kubelet 安装时会把 CNI 二进制释放到 /opt/cni/bin,并在 /etc/cni/net.d 下生成网络配置。系统级 containerd 编译时把默认插件目录写死为 /usr/libexec/cni,不再读取 kubelet 的 --cni-bin-dir。
cp /opt/cni/bin/* /usr/libexec/cni/
# 检查集群初始化的核心凭证文件是否存在
ls -l /etc/kubernetes/admin.conf
# 配置 kubectl(worker节点也使用master节点的admin.conf配置文件)
export KUBECONFIG=/etc/kubernetes/admin.conf
# 创建 .kube 目录(root 用户的目录是 /root/.kube)
mkdir -p /root/.kube
# 把集群的管理员凭证复制到 kubectl 默认读取的路径
cp -i /etc/kubernetes/admin.conf /root/.kube/config
# 赋予权限(否则 root 用户也可能读不了)
chown $(id -u):$(id -g) /root/.kube/config5.部署K8s 网络插件
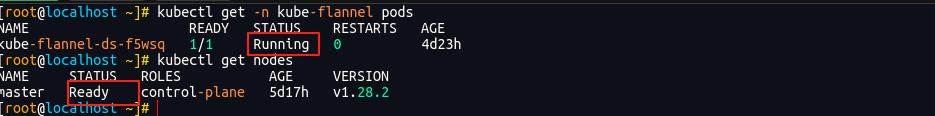
本文档K8s网络插件选择使用 Flannel 插件作为网络管理组件。
# 部署flannel插件
kubectl apply -f kube-flannel.yaml
#flannel 装到了 /opt/cni/bin 而kubelet 读取 CNI 插件的默认路径是 `/usr/libexec/cni`因此需要将/opt/cni/bin二进制文件复制到/usr/libexec/cni目录下
cp -rf /opt/cni/bin/* /usr/libexec/cni/kube-flannel.yaml内容如下:
注意:配置文件中net-conf.json参数的网络需要与k8s初始化的网络一致。
---
kind: Namespace
apiVersion: v1
metadata:
name: kube-flannel
labels:
k8s-app: flannel
pod-security.kubernetes.io/enforce: privileged
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1
metadata:
labels:
k8s-app: flannel
name: flannel
rules:
- apiGroups:
- ""
resources:
- pods
verbs:
- get
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- nodes/status
verbs:
- patch
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
labels:
k8s-app: flannel
name: flannel
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: flannel
subjects:
- kind: ServiceAccount
name: flannel
namespace: kube-flannel
---
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: flannel
name: flannel
namespace: kube-flannel
---
kind: ConfigMap
apiVersion: v1
metadata:
name: kube-flannel-cfg
namespace: kube-flannel
labels:
tier: node
k8s-app: flannel
app: flannel
data:
cni-conf.json: |
{
"name": "cbr0",
"cniVersion": "0.3.1",
"plugins": [
{
"type": "flannel",
"delegate": {
"hairpinMode": true,
"isDefaultGateway": true
}
},
{
"type": "portmap",
"capabilities": {
"portMappings": true
}
}
]
}
net-conf.json: |
{
"Network": "192.168.0.0/16",
"EnableNFTables": false,
"Backend": {
"Type": "vxlan"
}
}
---
apiVersion: apps/v1
kind: DaemonSet
metadata:
name: kube-flannel-ds
namespace: kube-flannel
labels:
tier: node
app: flannel
k8s-app: flannel
spec:
selector:
matchLabels:
app: flannel
template:
metadata:
labels:
tier: node
app: flannel
spec:
affinity:
nodeAffinity:
requiredDuringSchedulingIgnoredDuringExecution:
nodeSelectorTerms:
- matchExpressions:
- key: kubernetes.io/os
operator: In
values:
- linux
hostNetwork: true
priorityClassName: system-node-critical
tolerations:
- operator: Exists
effect: NoSchedule
serviceAccountName: flannel
initContainers:
- name: install-cni-plugin
image: ghcr.io/flannel-io/flannel-cni-plugin:v1.8.0-flannel1
command:
- cp
args:
- -f
- /flannel
- /opt/cni/bin/flannel
volumeMounts:
- name: cni-plugin
mountPath: /opt/cni/bin
- name: install-cni
image: ghcr.io/flannel-io/flannel:v0.27.4
command:
- cp
args:
- -f
- /etc/kube-flannel/cni-conf.json
- /etc/cni/net.d/10-flannel.conflist
volumeMounts:
- name: cni
mountPath: /etc/cni/net.d
- name: flannel-cfg
mountPath: /etc/kube-flannel/
containers:
- name: kube-flannel
image: ghcr.io/flannel-io/flannel:v0.27.4
command:
- /opt/bin/flanneld
args:
- --ip-masq
- --kube-subnet-mgr
resources:
requests:
cpu: "100m"
memory: "50Mi"
securityContext:
privileged: false
capabilities:
add: ["NET_ADMIN", "NET_RAW"]
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
- name: EVENT_QUEUE_DEPTH
value: "5000"
- name: CONT_WHEN_CACHE_NOT_READY
value: "false"
volumeMounts:
- name: run
mountPath: /run/flannel
- name: flannel-cfg
mountPath: /etc/kube-flannel/
- name: xtables-lock
mountPath: /run/xtables.lock
volumes:
- name: run
hostPath:
path: /run/flannel
- name: cni-plugin
hostPath:
path: /opt/cni/bin
- name: cni
hostPath:
path: /etc/cni/net.d
- name: flannel-cfg
configMap:
name: kube-flannel-cfg
- name: xtables-lock
hostPath:
path: /run/xtables.lock
type: FileOrCreate